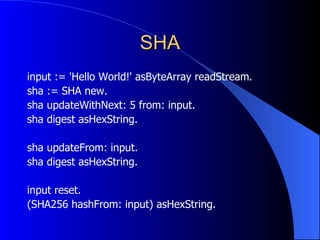
The document discusses various topics in public key cryptography including public key algorithms like RSA and Diffie-Hellman key exchange. It also covers hashing algorithms like MD5 and SHA, digital signatures using RSA and DSA, and applications like encryption, key establishment, and signing. Code examples are provided in Smalltalk to demonstrate encrypting, decrypting, signing and verifying messages using these cryptographic techniques.



![RSA (1977) RSA Security, PKCS #1 modulus n = product of 2 large primes p, q public: e = relatively prime to (p-1)(q-1) private: d = e -1 mod ((p-1)(q-1)) C = P e mod n [ P < n ] P = C d mod n small e => faster encryption](https://image.slidesharecdn.com/06esugcrypto2-12874629454595-phpapp02/85/Cryptography-for-Smalltalkers-2-ESUG-2006-5-320.jpg)










![MD5 (MD5 hash: 'Hello' asByteArray) asHexString (MD5 hash: #[1 2 3 4 5] from: 2 to: 4) asHexString input := #[1 2 3 4 5 6 7 8 9] readStream. (MD5 hashNext: 3 from: input) asHexString (MD5 hashFrom: input) asHexString](https://image.slidesharecdn.com/06esugcrypto2-12874629454595-phpapp02/85/Cryptography-for-Smalltalkers-2-ESUG-2006-17-320.jpg)






![Books [1] Anderson: Security Engineering [2] Ferguson, Schneier: Practical Cryptography [3] Kahn: The Codebreakers [4] Menezes, van Oorschot, Vanstone: Handbook of Applied Cryptography [5] Schneier: Applied Cryptography](https://image.slidesharecdn.com/06esugcrypto2-12874629454595-phpapp02/85/Cryptography-for-Smalltalkers-2-ESUG-2006-25-320.jpg)