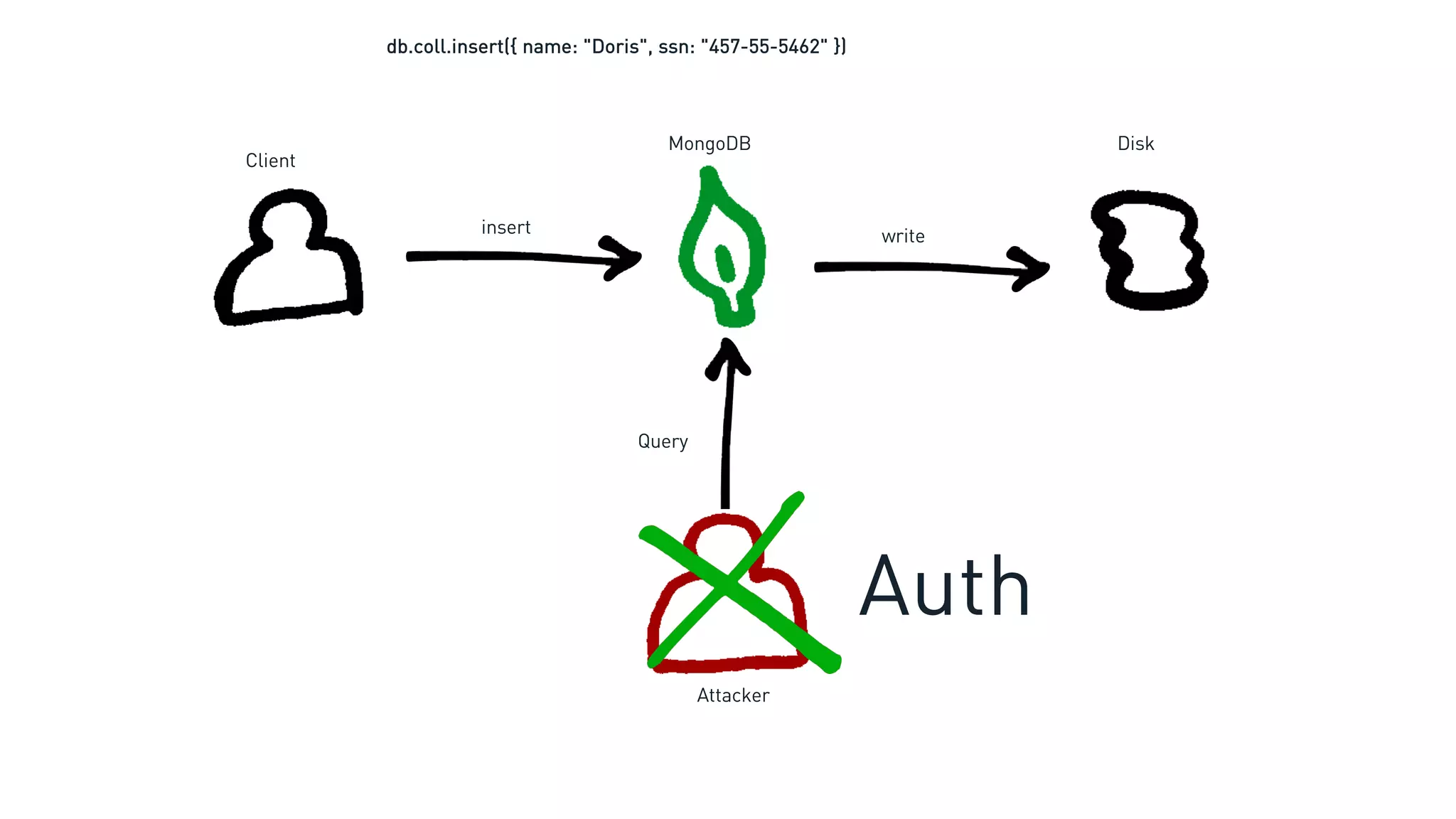
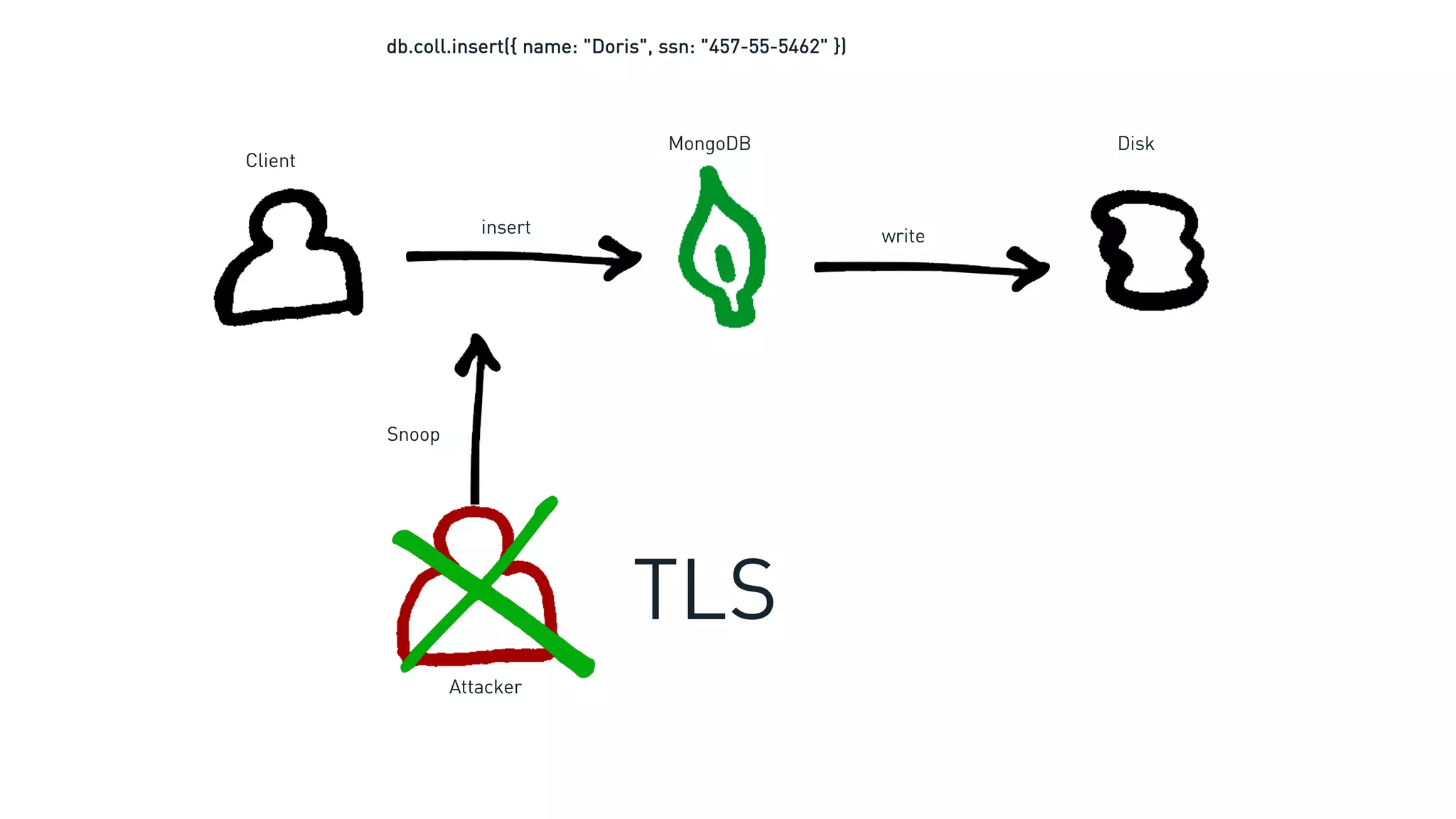
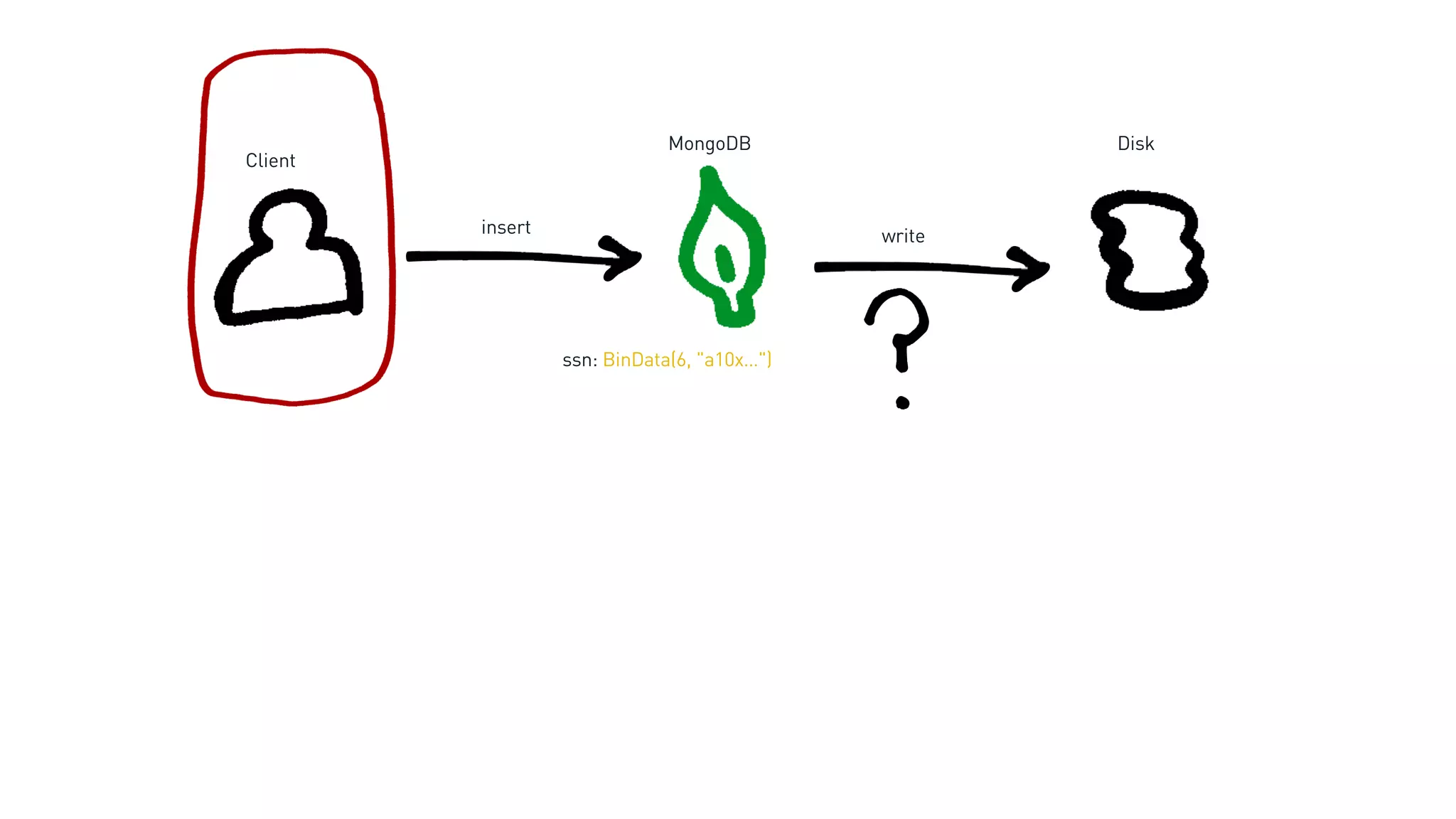
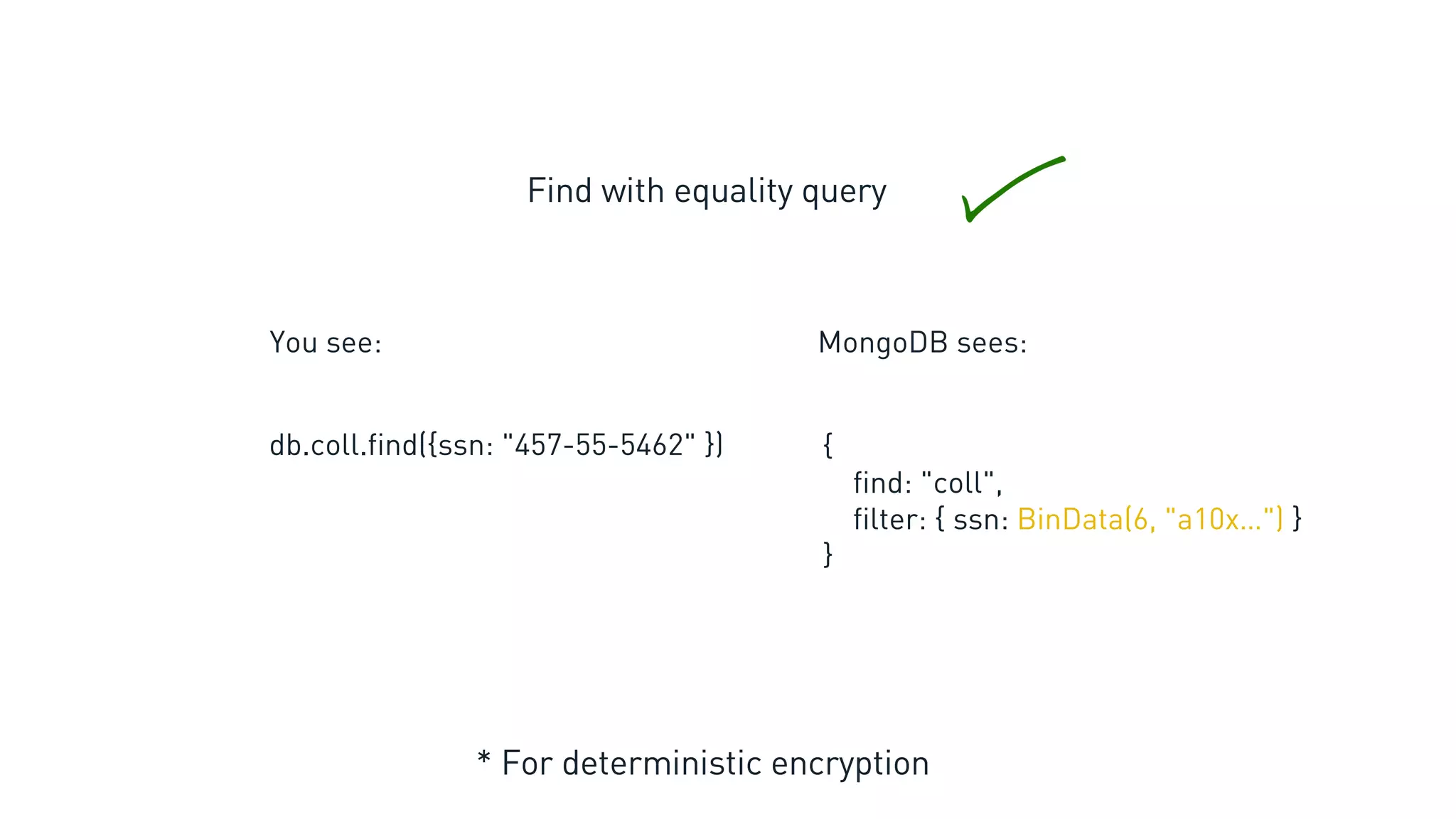
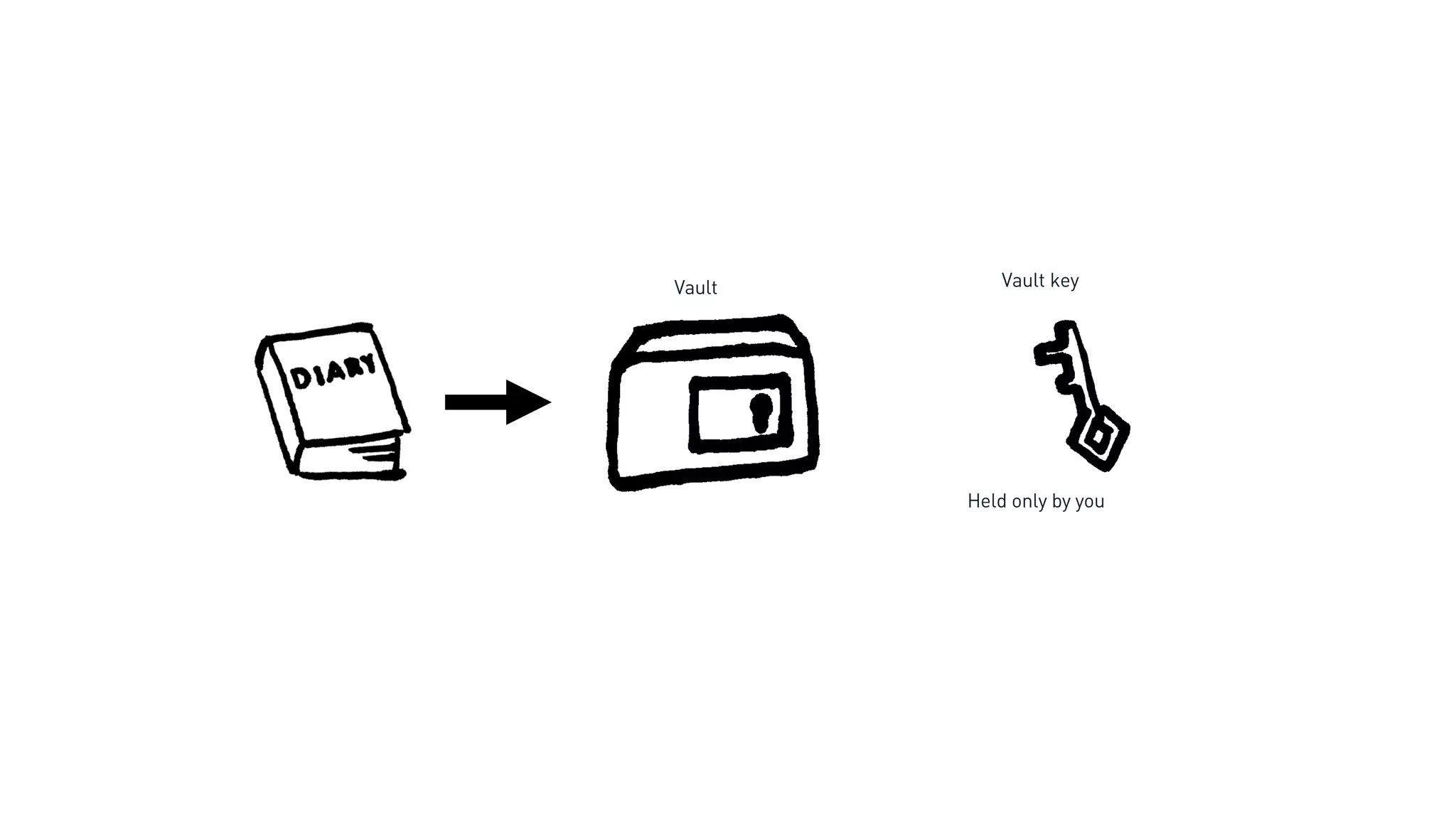
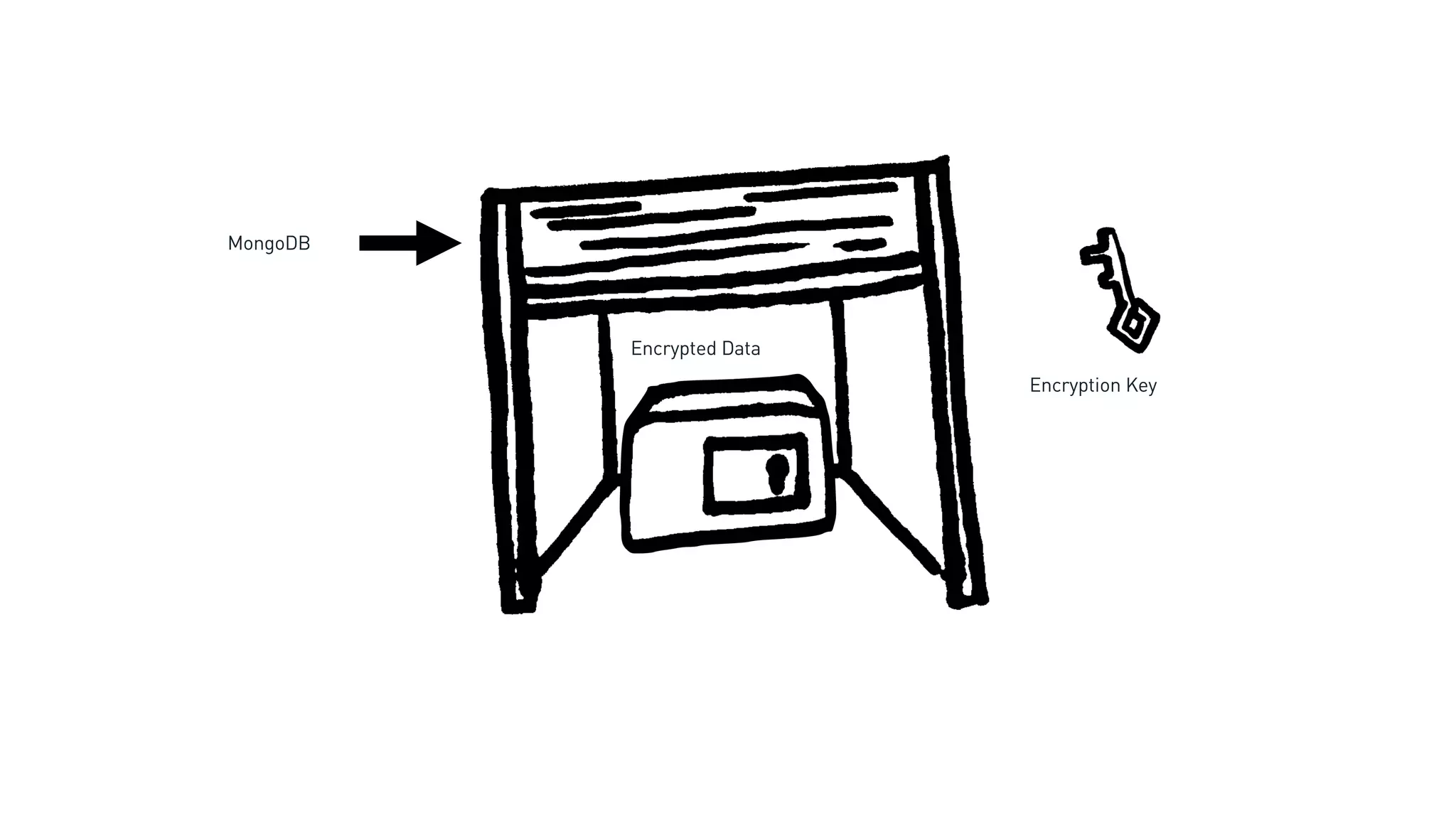
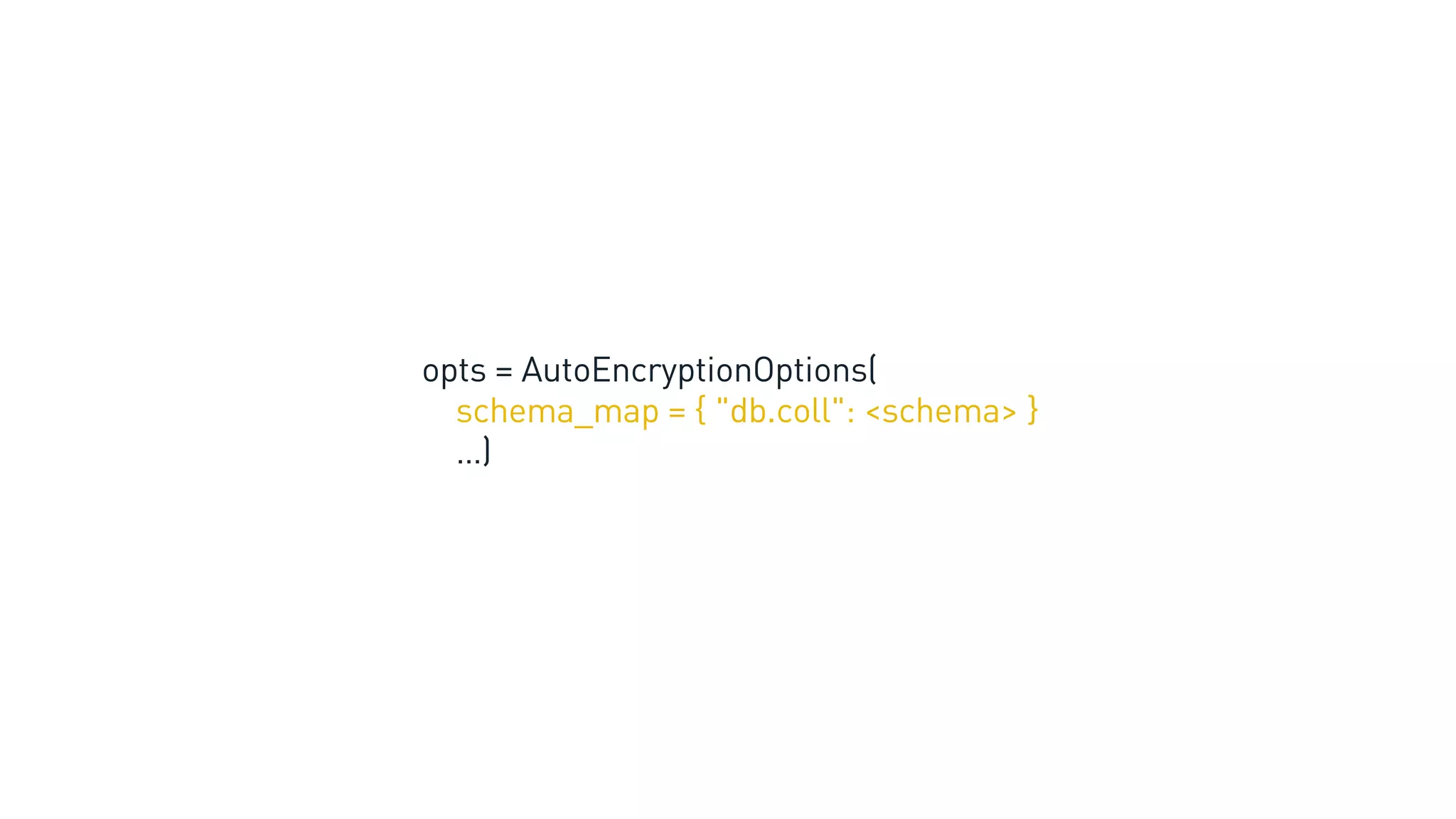
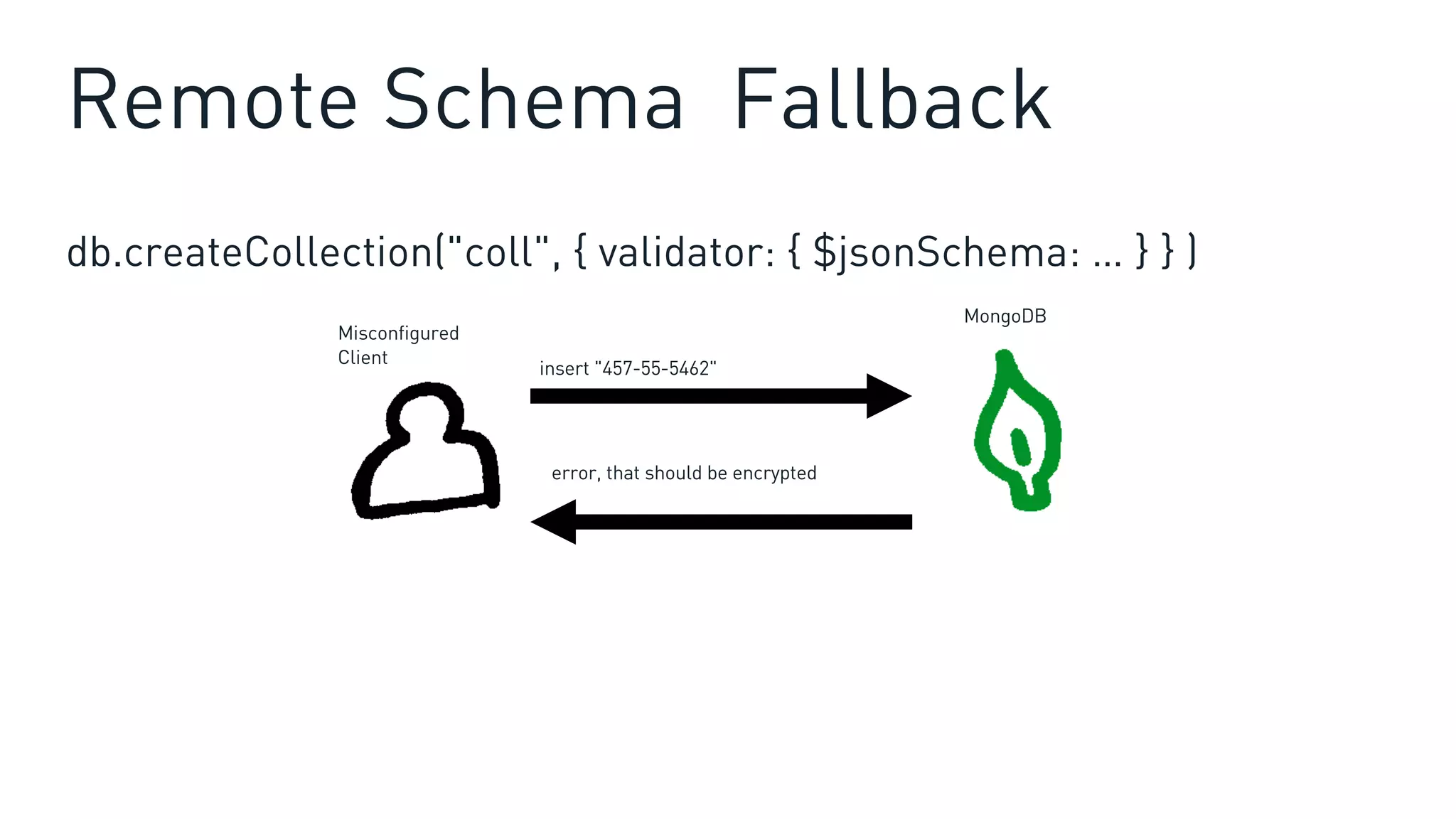
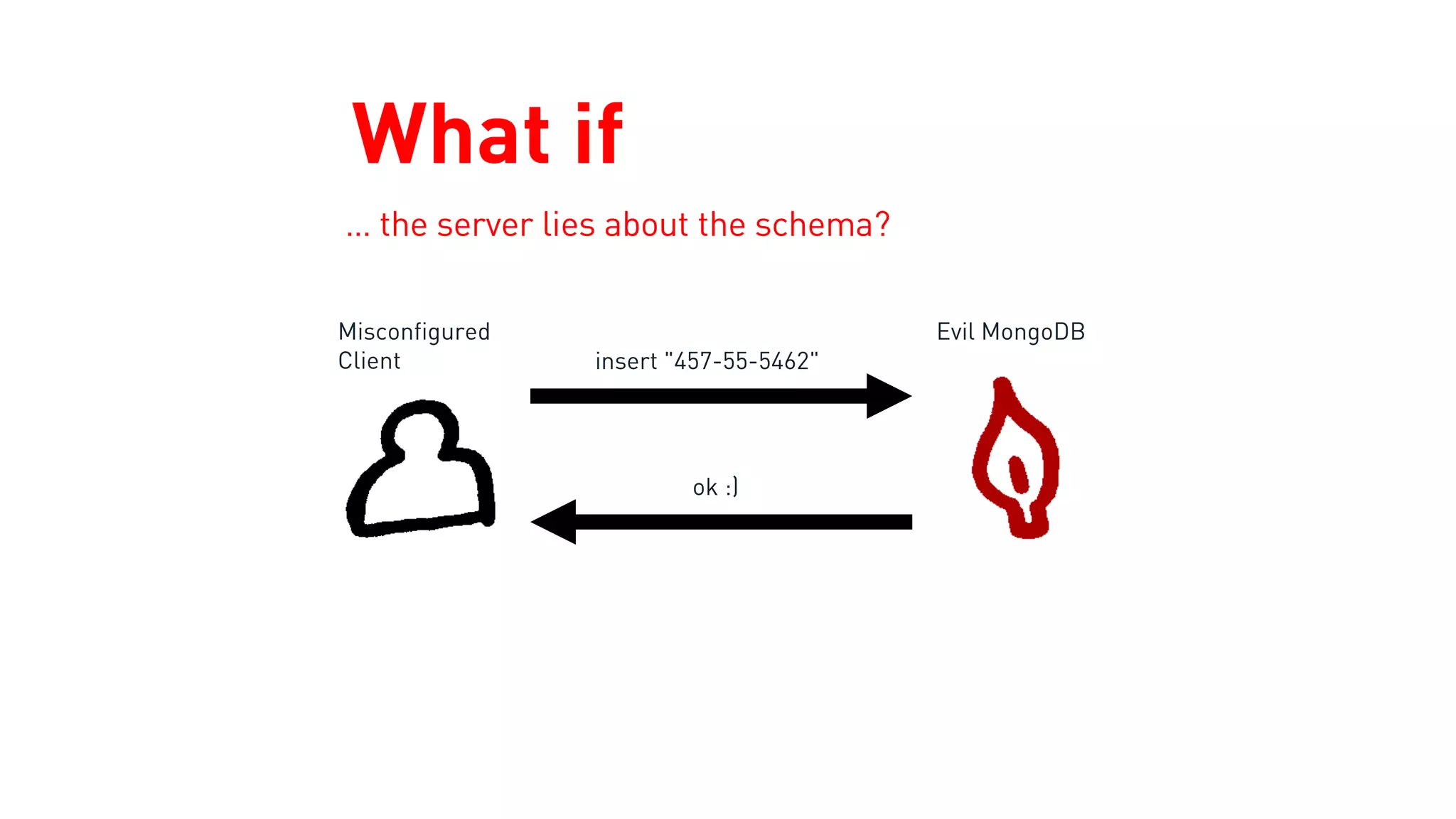
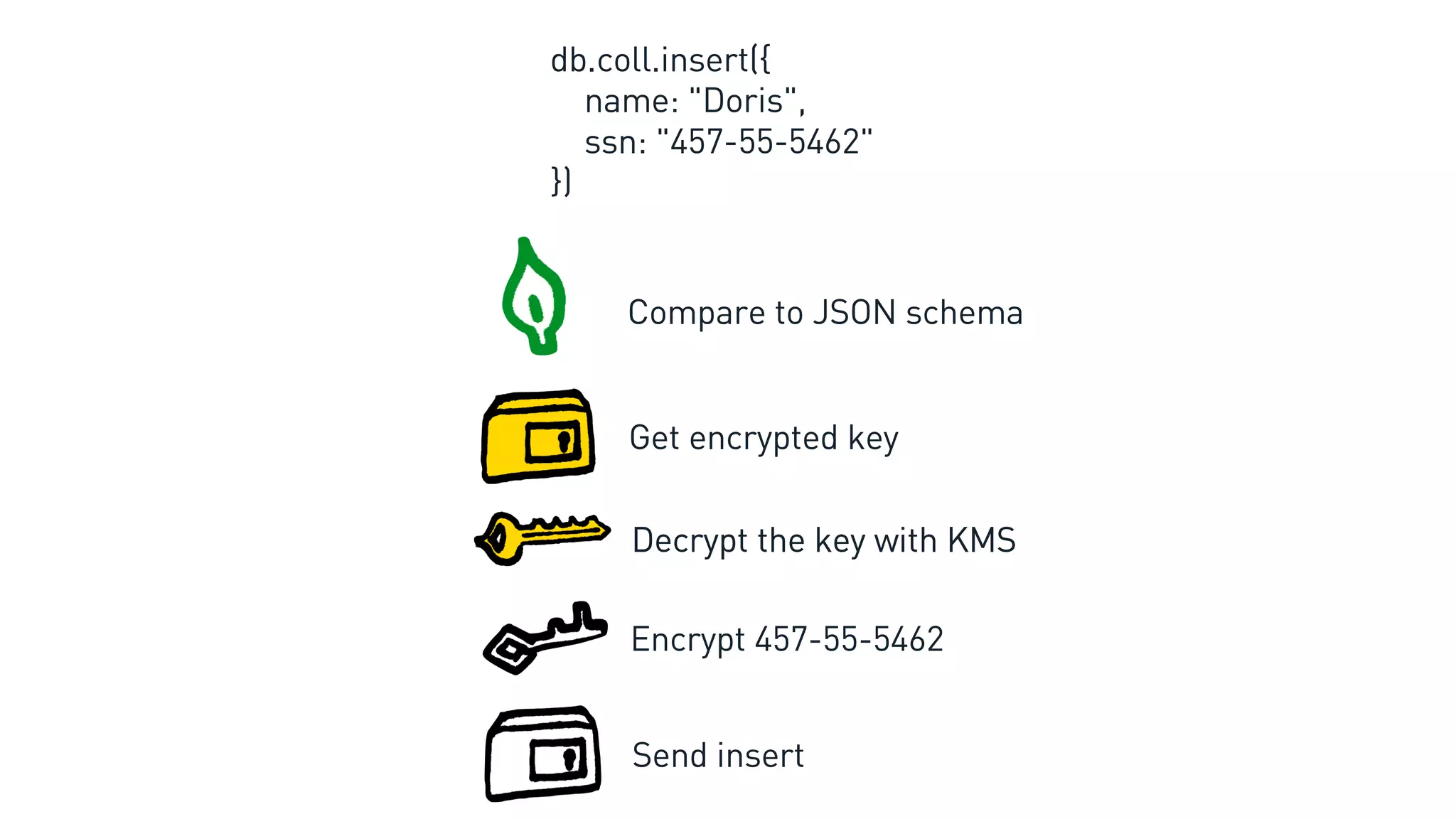
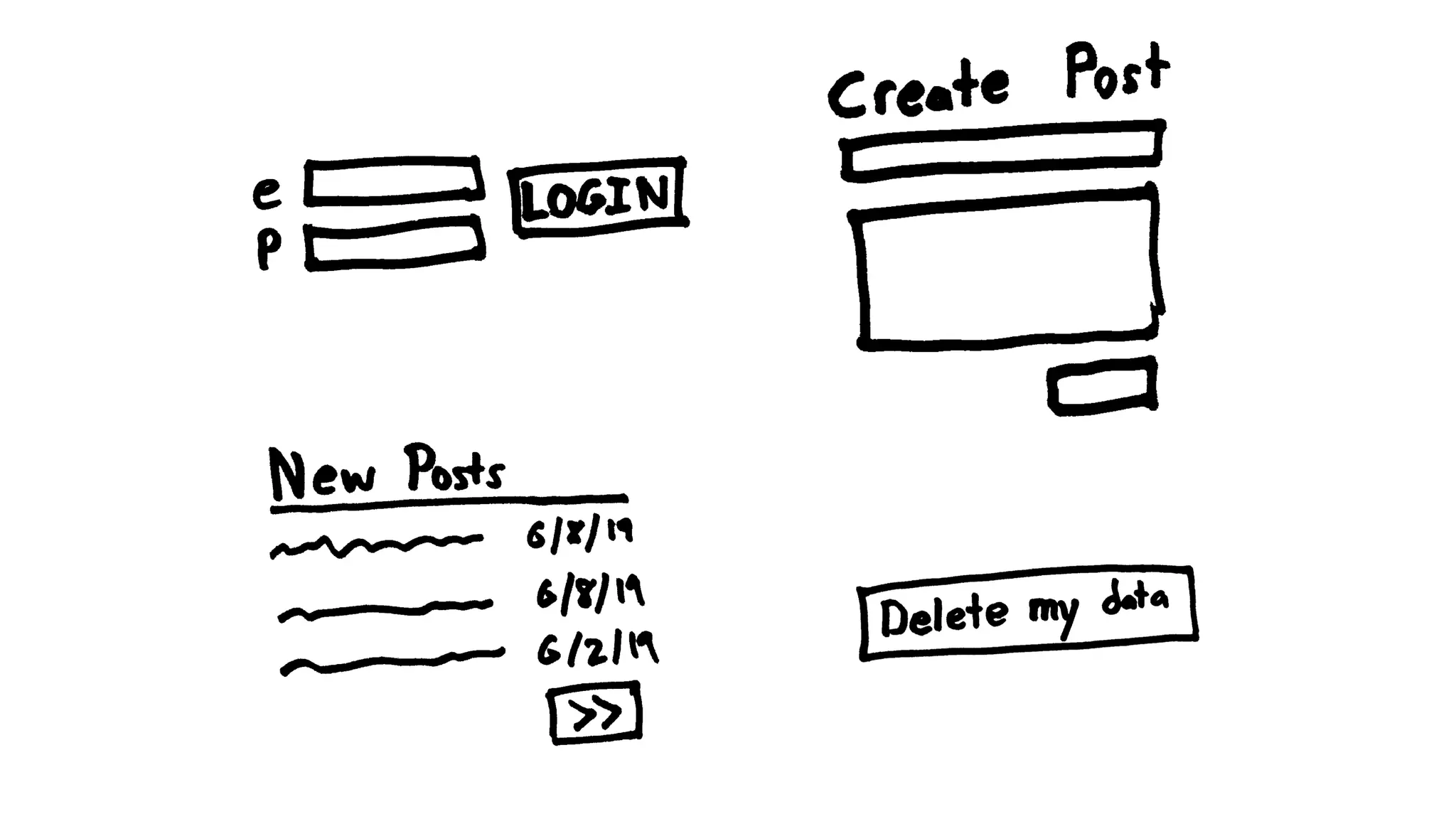
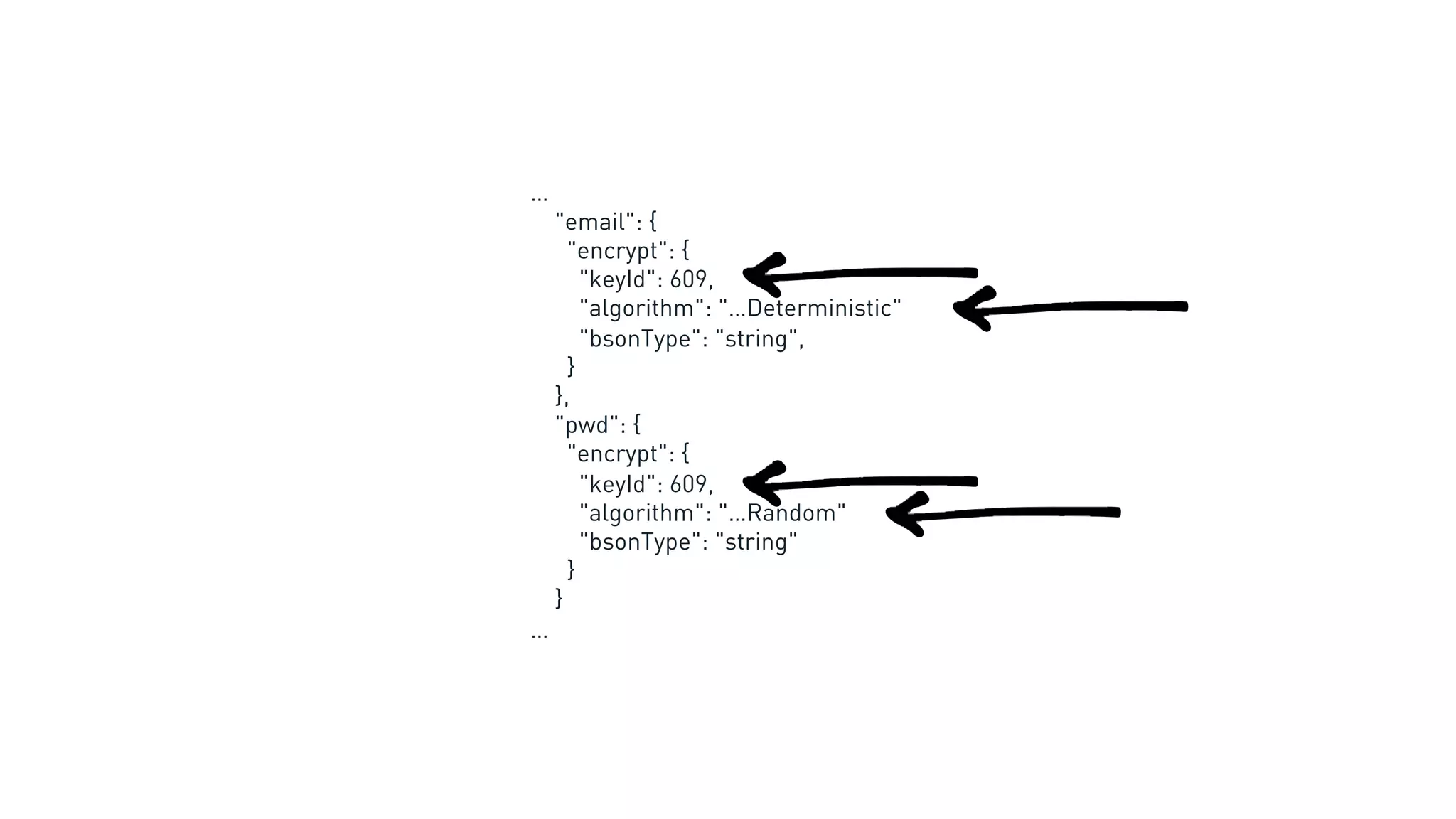
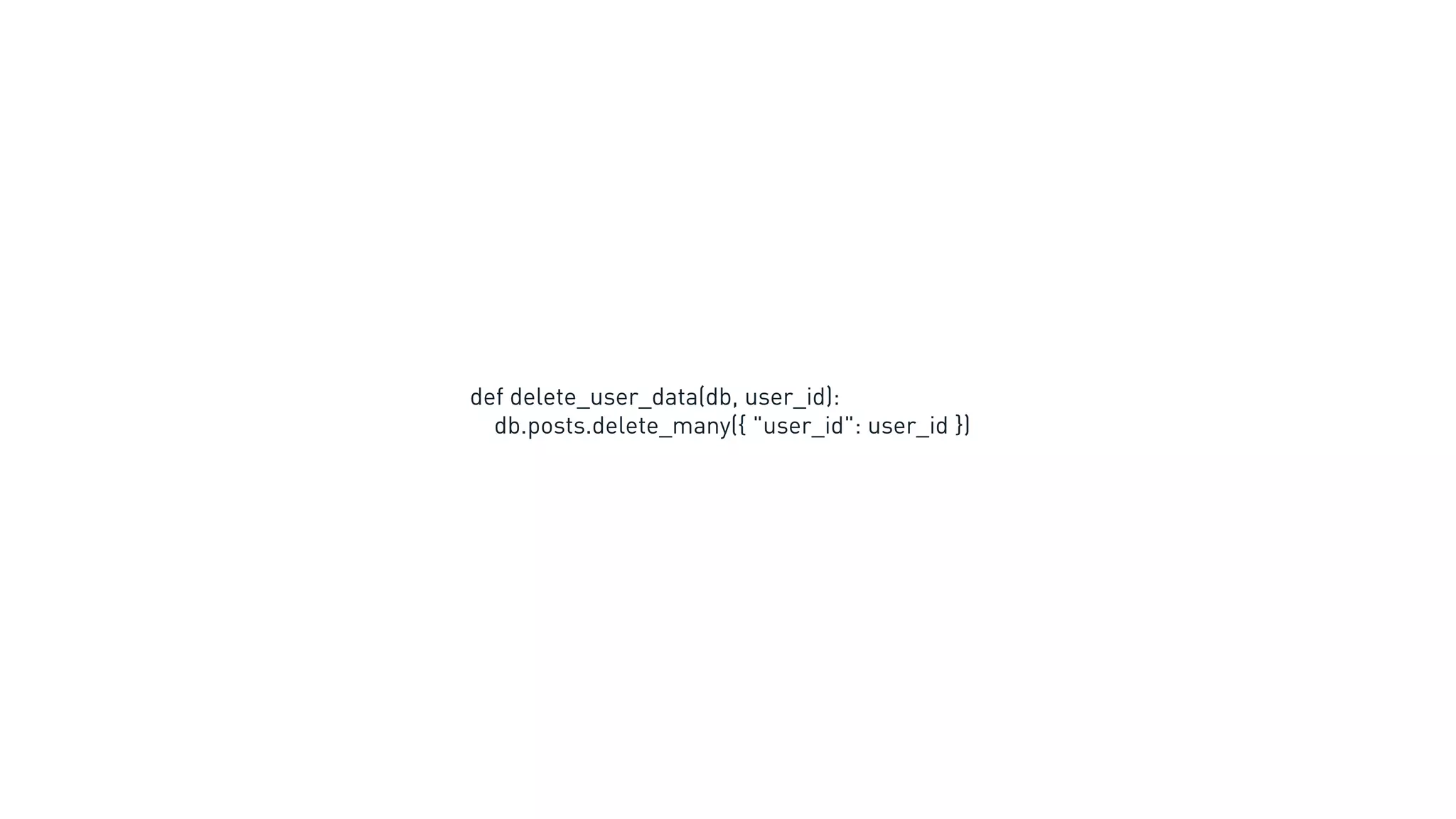
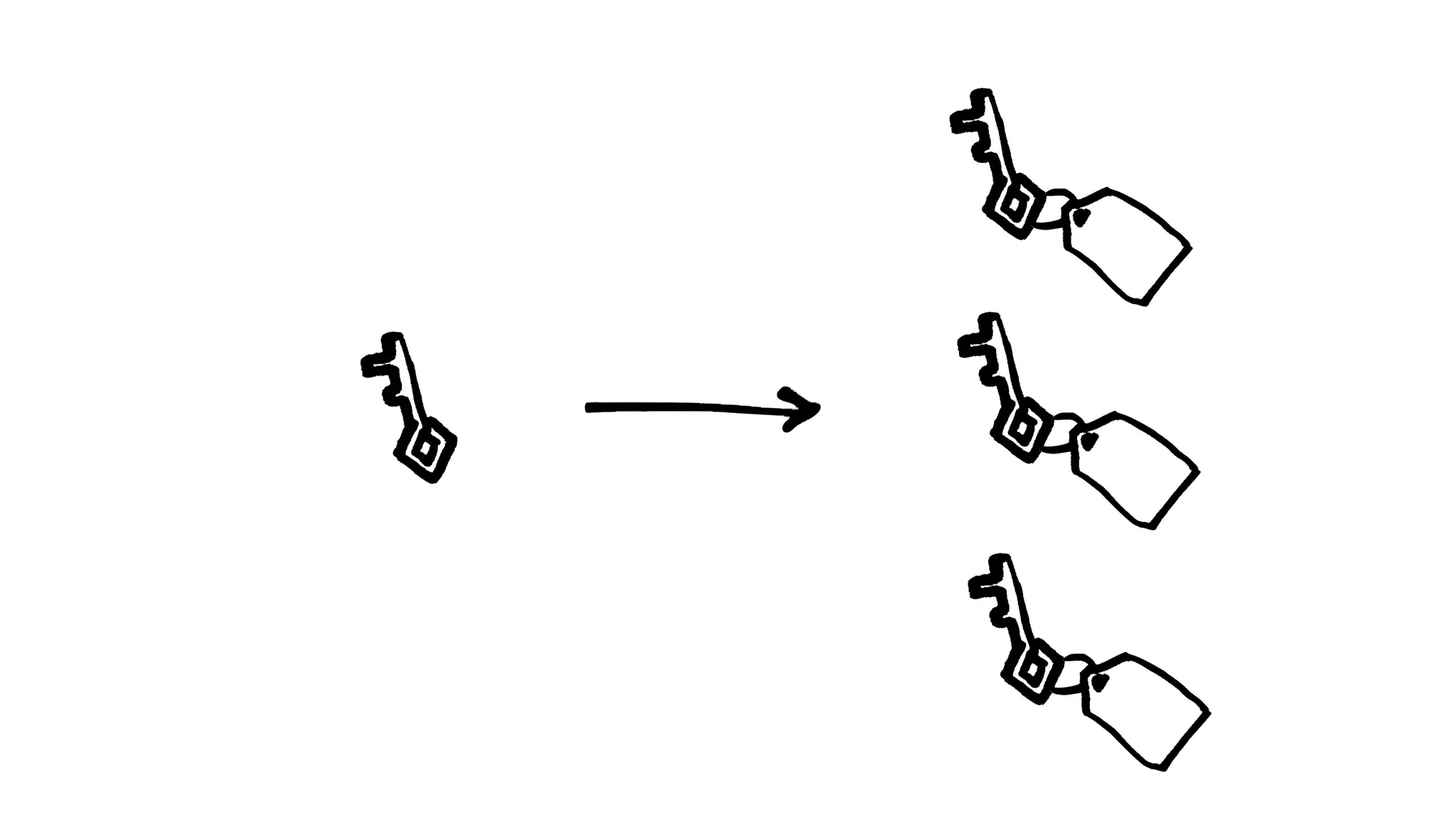
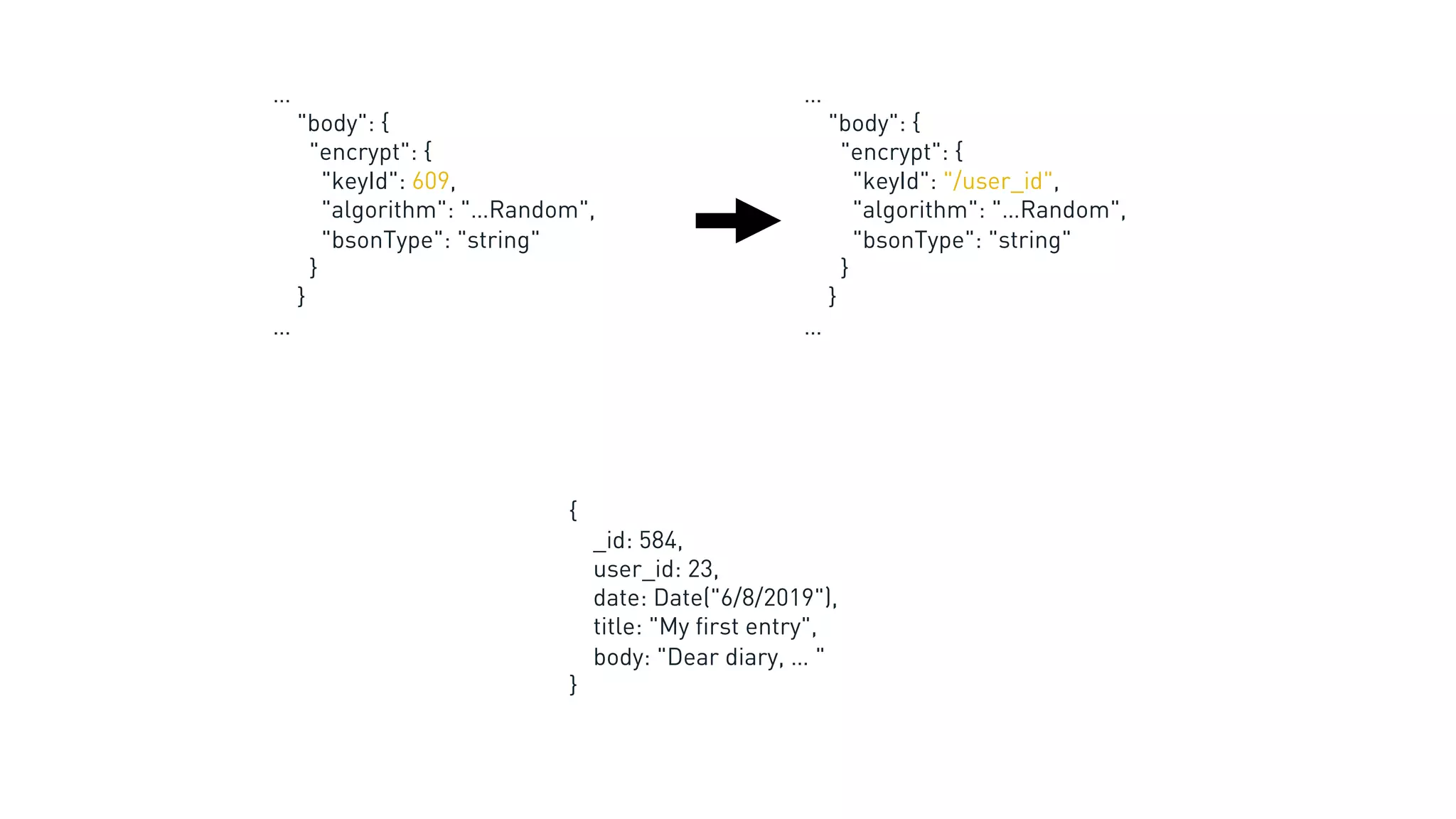
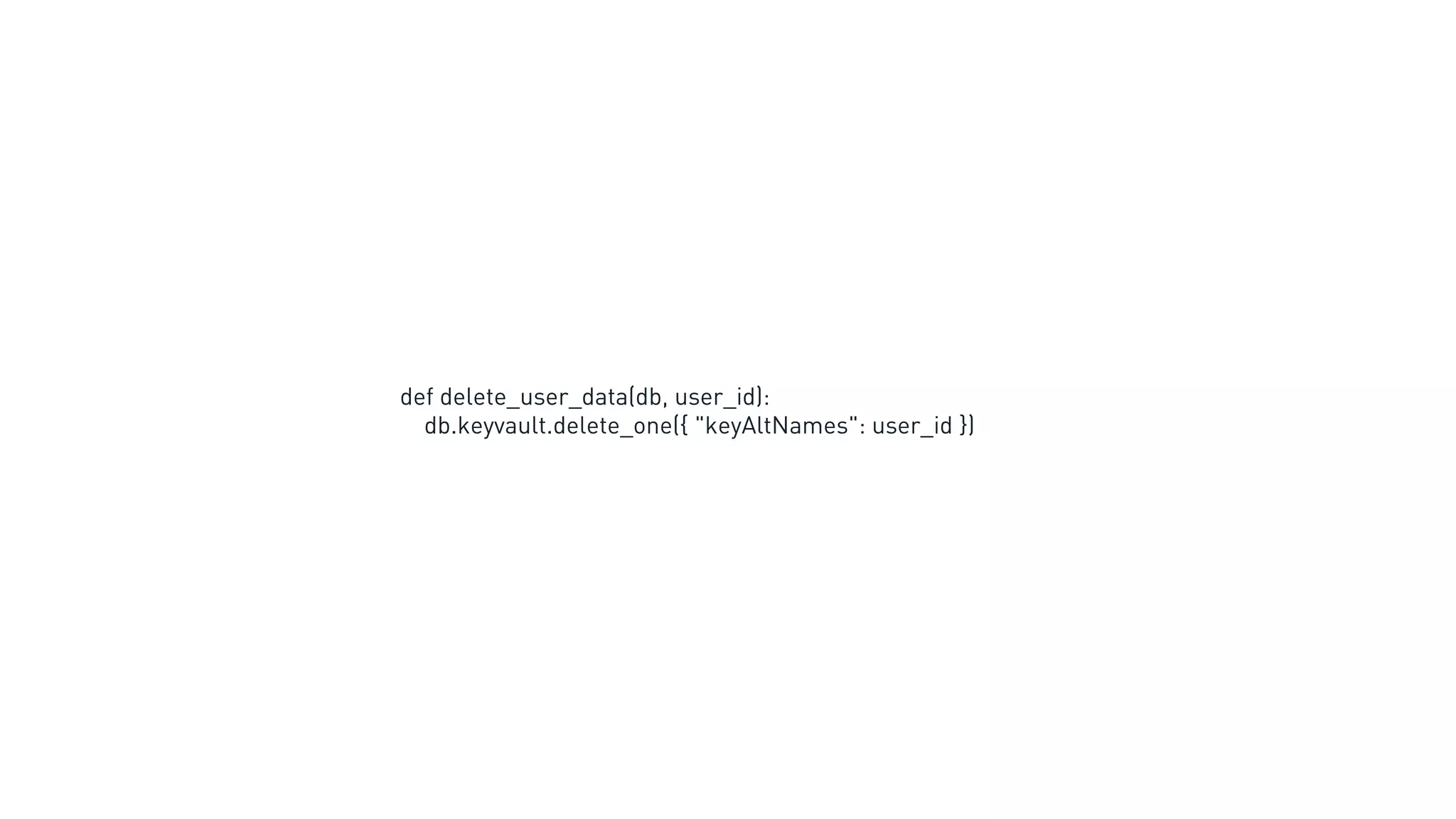
This document discusses MongoDB's new client-side field level encryption capabilities in version 4.2. It describes how client-side encryption works, including encrypting and decrypting data before it is sent to or retrieved from the database. It also covers key management and the use of JSON schemas to define which fields should be encrypted.

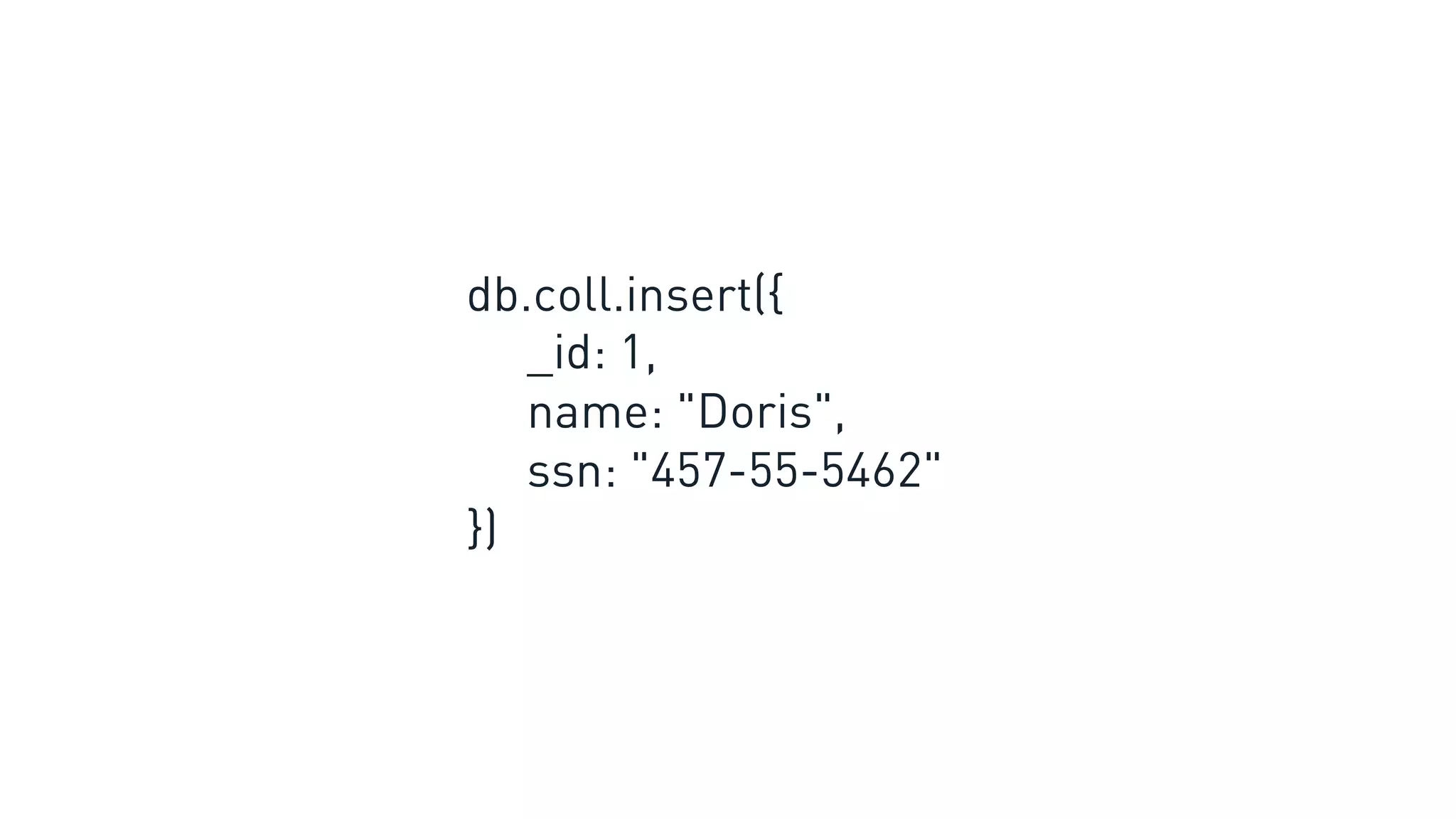
![db.coll.insert({
name: "Doris",
ssn: "457-55-5462"
})
{
insert: "coll",
documents: [{
name: "Doris",
ssn: BinData(6, "a10x…")
}]
}
You see: MongoDB sees:
Encrypt before sending](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-12-2048.jpg)
![db.coll.update({}, {
$set: { ssn: "457-55-5462" }
})
{
update: "coll",
updates: [{
q:{},
u: {
$set: { ssn: BinData(6, "a10x…") }
}
}]
}
You see: MongoDB sees:
Update that overwrites value](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-26-2048.jpg)
![db.coll.aggregate([{
$project: { name_ssn: {$concat: [ "$name", " - ", "$ssn" ] } }
}]
Aggregate acting on the data](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-27-2048.jpg)
![Find with equality query
* For deterministic encryption
db.test.find(
{
$and: [
{
$or: [
{ ssn : { $in : [ "457-55-5462", "153-96-2097" ]} },
{ ssn: { $exists: false } }
]
},
{ name: "Doris" }
]
}
)
You see:](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-29-2048.jpg)
![Find with equality query
* For deterministic encryption
MongoDB sees:
{
find: "coll",
filter: {
$and: [
{
$or: [
{ ssn : { $in : [ BinData(6, "a10x…"), BinData(6, "8dk1…") ]} },
{ ssn: { $exists: false } }
]
},
{ name: "Doris" }
]
}
}](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-30-2048.jpg)



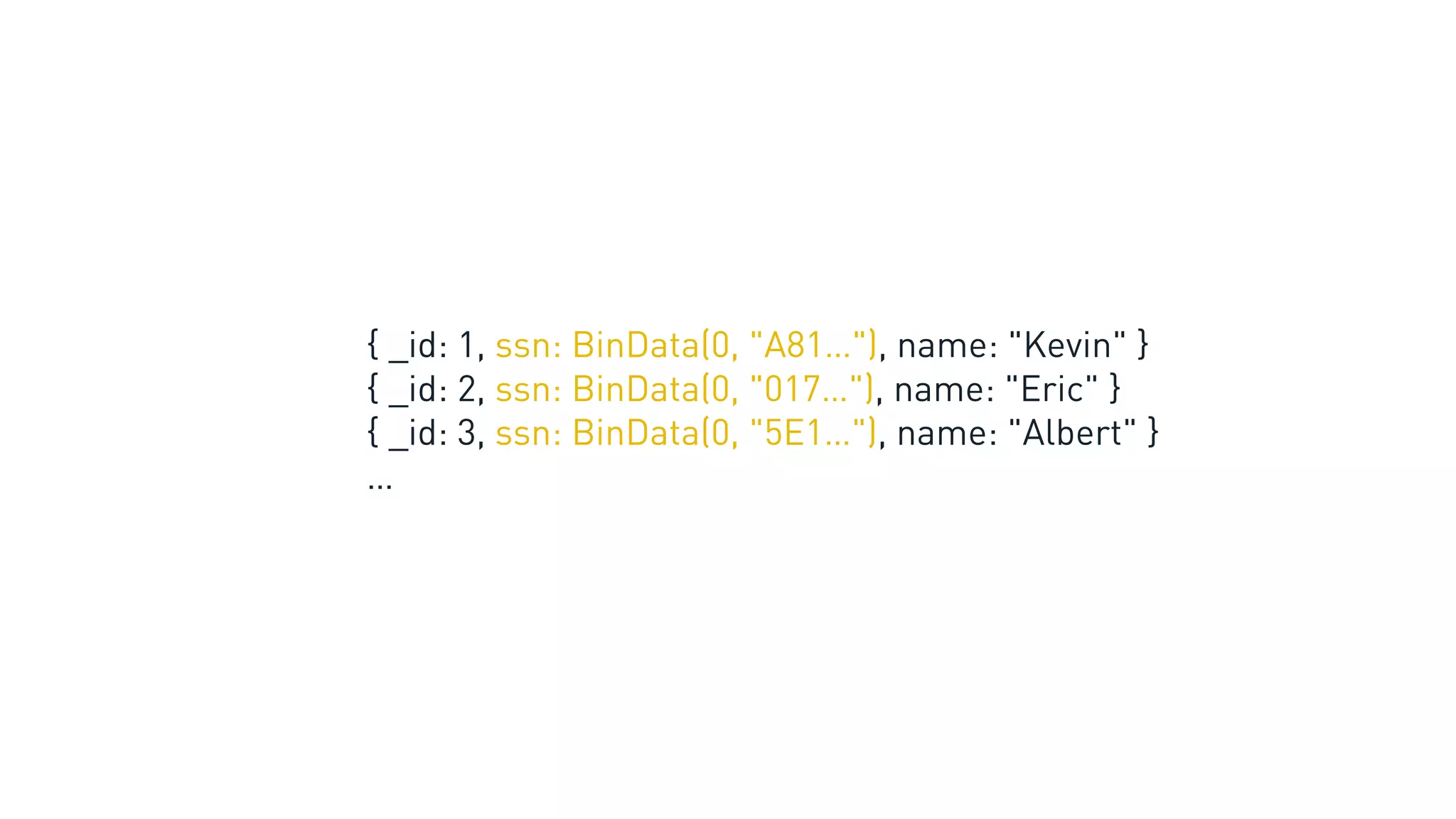


![{
name: "Doris"
ssn: "457-55-5462",
email: "Doris@gmail.com",
credit_card: "4690-6950-9373-8791",
comments: [ …. ],
avatar: BinData(0, "0fi8…"),
profile: { likes: {…}, dislikes: {…} }
}](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-48-2048.jpg)
![Describes JSON
{
bsonType: "object",
properties: {
a: {
bsonType: "int"
maximum: 10
}
b: { bsonType: "string" }
},
required: ["a", "b"]
}
{
a: 5,
b: "hi"
}
{
a: 11,
b: false
}
JSON Schema](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-51-2048.jpg)
![{
bsonType: "object",
properties: {
ssn: {
encrypt: { … }
}
},
required: ["ssn"]
}
JSON Schema "encrypt"](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-52-2048.jpg)
![encrypt: {
keyId: <UUID[]> or <string>,
algorithm: <string>
bsonType: <string> or <string[]>
}
bsonType indicates the type of underlying data.
algorithm indicates how to encrypt (Random or Deterministic).
keyId indicates the key used to encrypt.](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-53-2048.jpg)



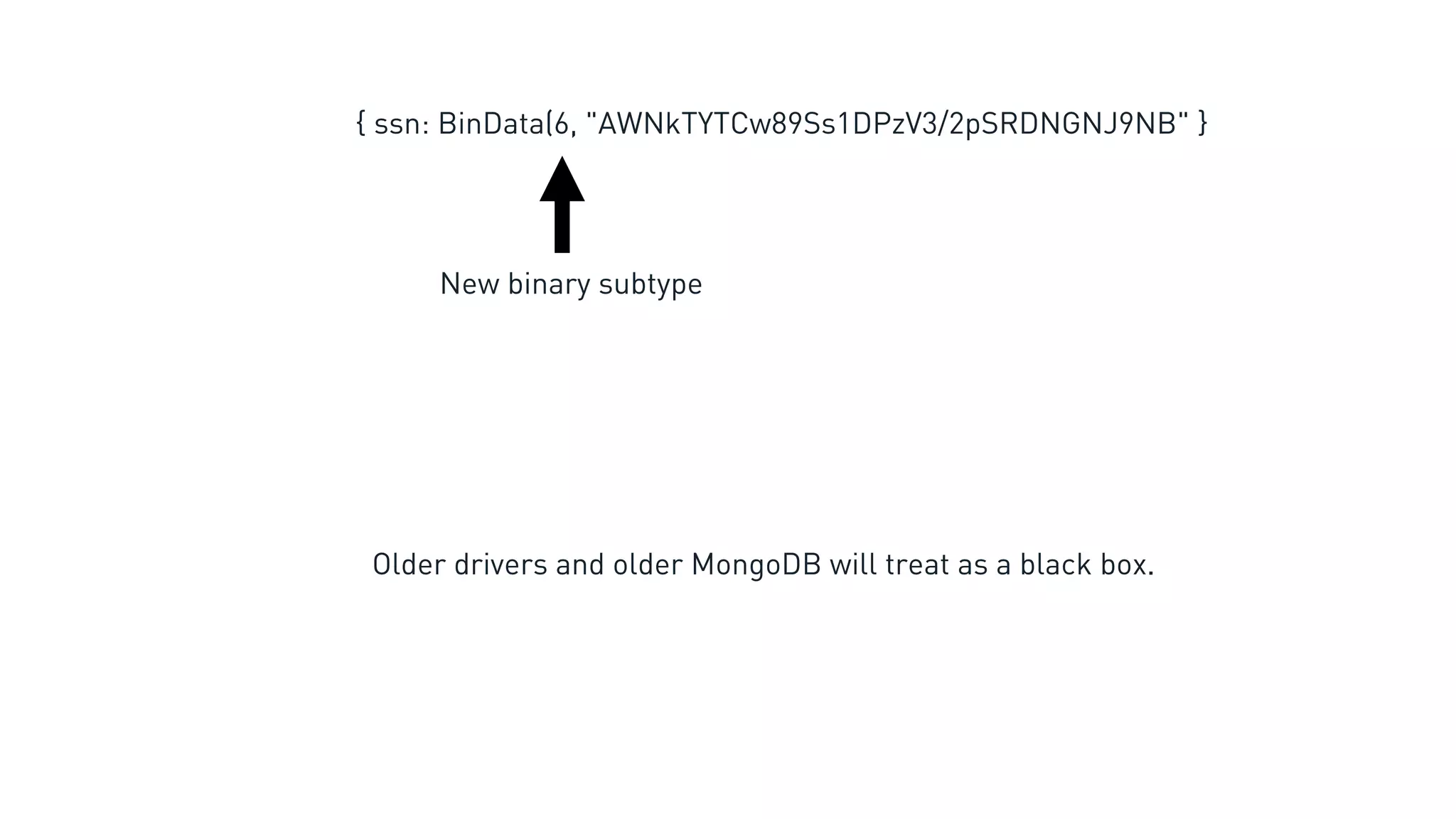
![byte algorithm
byte[16] key_id
byte original_bson_type
byte* payload
Ciphertext](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-89-2048.jpg)
![byte algorithm
byte[16] key_id
byte original_bson_type
byte* payload
key_id + algorithm describes how to decrypt.
No JSON Schema necessary!
Ciphertext](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-90-2048.jpg)
![byte algorithm
byte[16] key_id
byte original_bson_type
byte* payload
Provides extra server-side validation.
But prohibits single-value types (MinKey, MaxKey, Undefined, Null)
Ciphertext](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-91-2048.jpg)
![byte algorithm
byte[16] key_id
byte original_bson_type
byte* payload
Payload includes encoded IV and padding block, and HMAC.
Ciphertext adds between 66 to 82 bytes of overhead.
Ciphertext](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-92-2048.jpg)

![{
_id: 23
email: "Doris@gmail.com",
pwd: "19dg8%"
following: [ 9, 20, 95 ]
}](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-101-2048.jpg)
![client = MongoClient(
auto_encryption_opts=opts)
def register(db, email, pwd):
db.users.insert_one({ "email": email, "pwd": pwd })
def login(db, email, pwd):
user = db.users.find_one({ "email": email })
if user and matches(user["pwd"], pwd):
return True
else:
return False](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-103-2048.jpg)


![encryption = ClientEncryption(…)
def register(encryption, db, email, pwd):
user_id = db.users.insert_one({
"email": email,
"pwd": pwd
}).inserted_id
opts = DataKeyOpts(keyAltNames=[user_id])
encryption.create_data_key("aws", opts)](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-112-2048.jpg)
![def get_follower_posts(db, user):
cursor = db.posts.find_many(
{ "user_id": { "$in": user["followers"] } },
limit = 20,
sort = { "date": DESCENDING }
)
return list(cursor)](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-116-2048.jpg)
![def list_follower_posts(db, user):
cursor = db.posts.find_many(
{ "user_id": { "$in": user["followers"] } },
limit = 20,
sort = { "date": DESCENDING },
projection = { "body": False }
)
return list(cursor)](https://image.slidesharecdn.com/mdblocalmunichflebl-191024135855/75/MongoDB-local-Munich-2019-New-Encryption-Capabilities-in-MongoDB-4-2-A-Deep-Dive-into-Protecting-Sensitive-Workloads-117-2048.jpg)