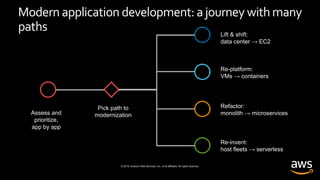
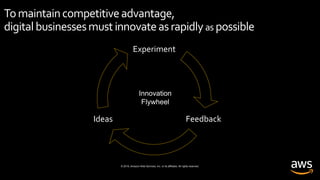
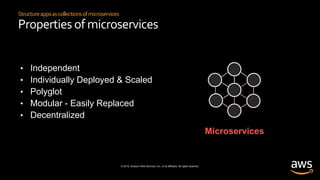
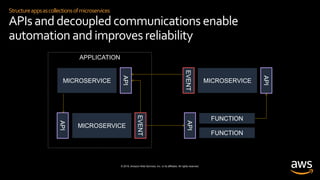
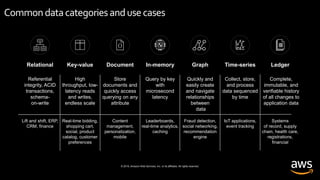
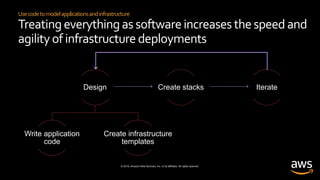
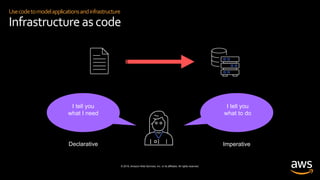
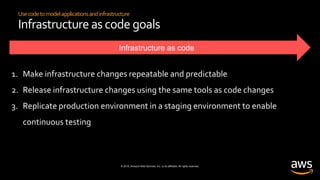
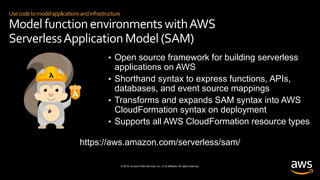
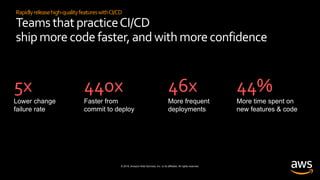
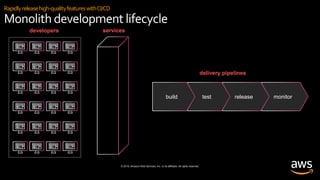
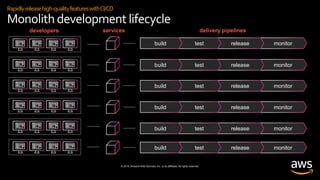
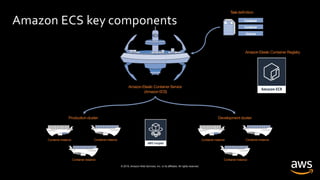
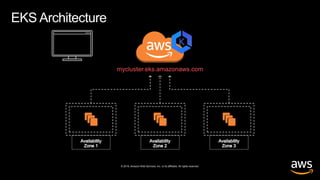
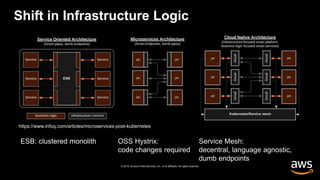
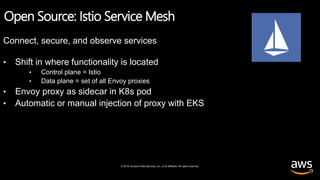
The document discusses the development of modern applications in the cloud, emphasizing the importance of microservices architecture and serverless technologies for enhancing agility and innovation. It outlines various modernization paths, including lift-and-shift and refactoring strategies while highlighting the role of continuous integration and delivery (CI/CD) for rapid feature deployment. Additionally, it covers the significance of infrastructure as code and automation in managing application deployments efficiently.