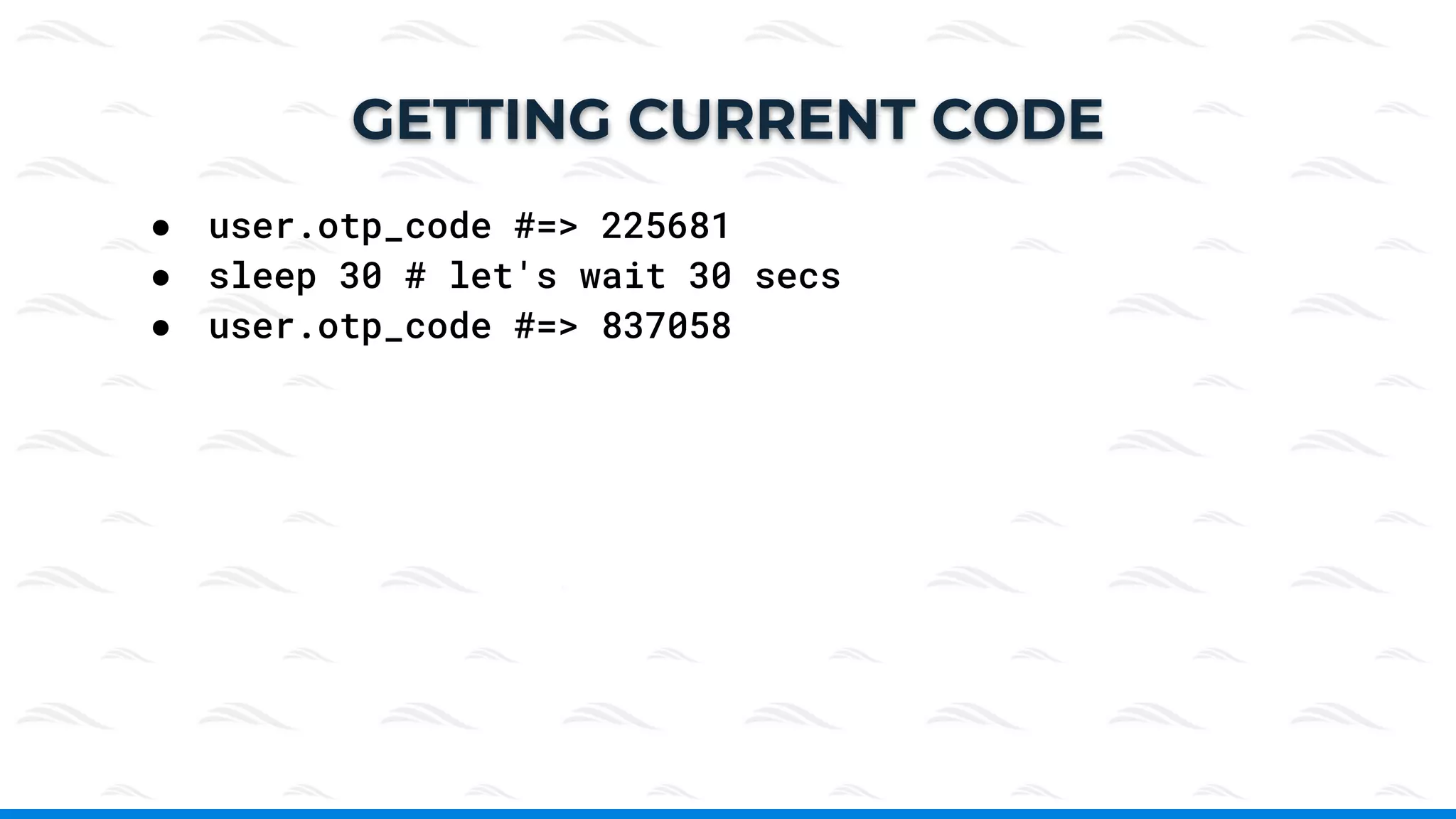
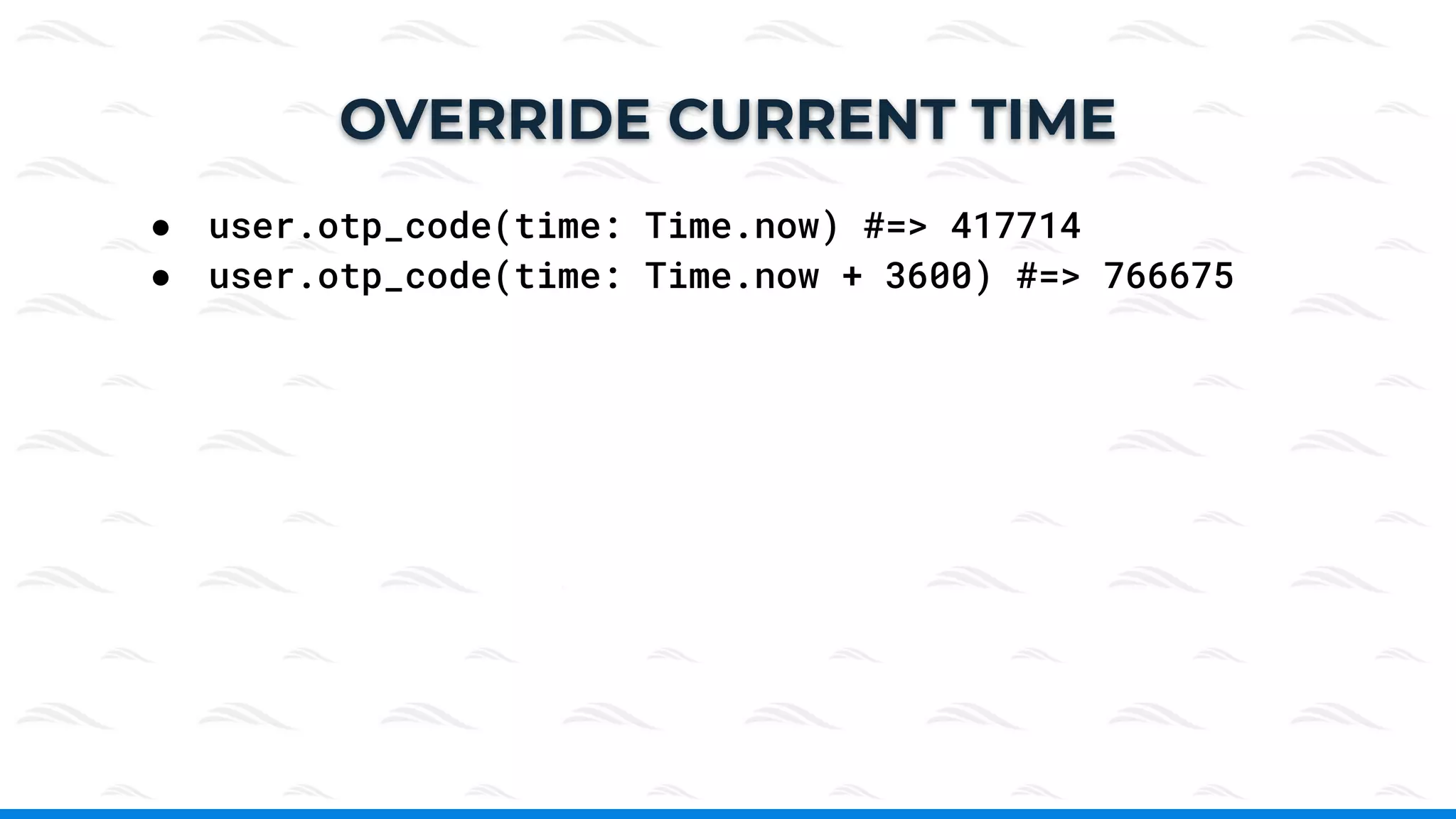
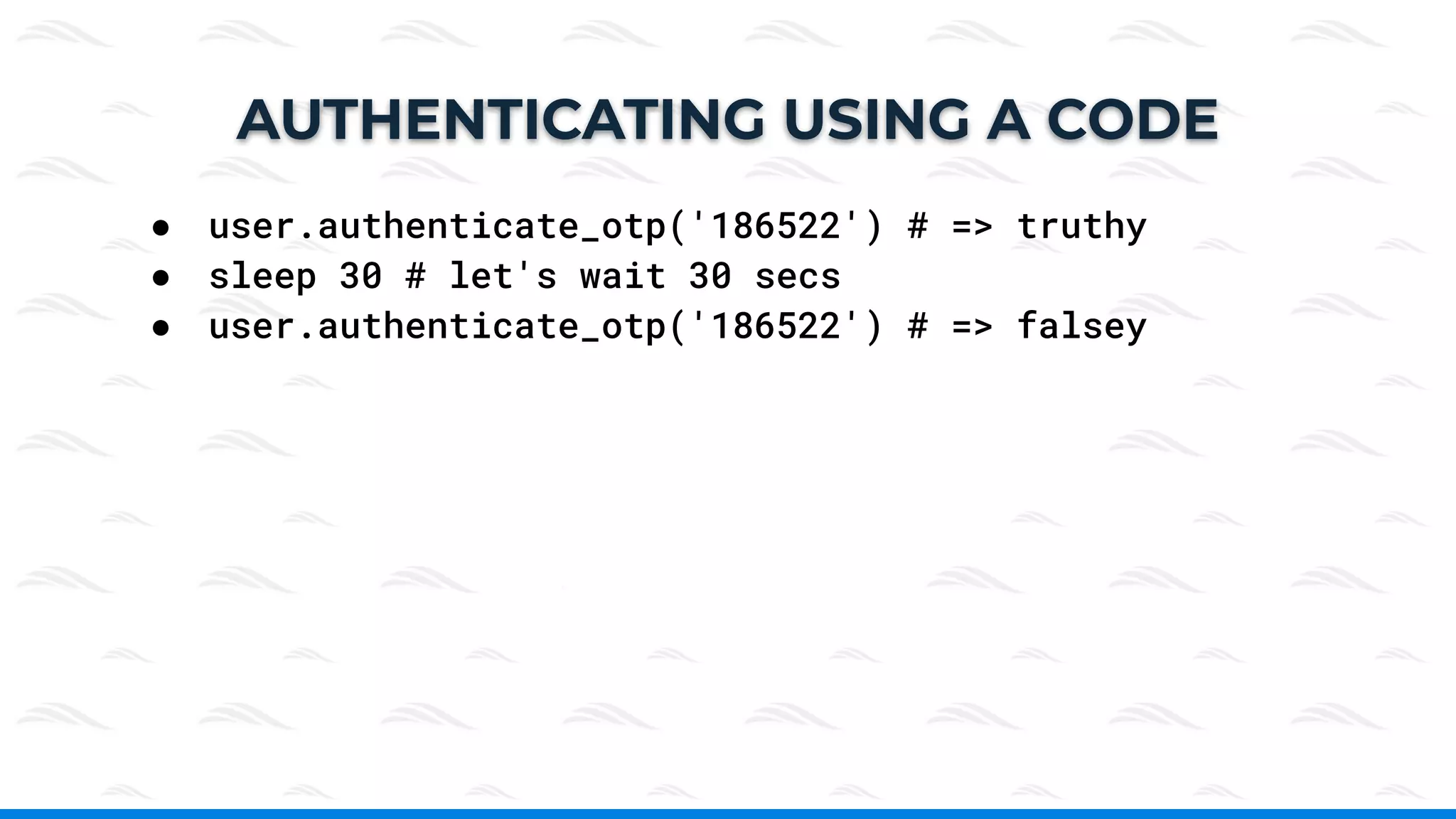
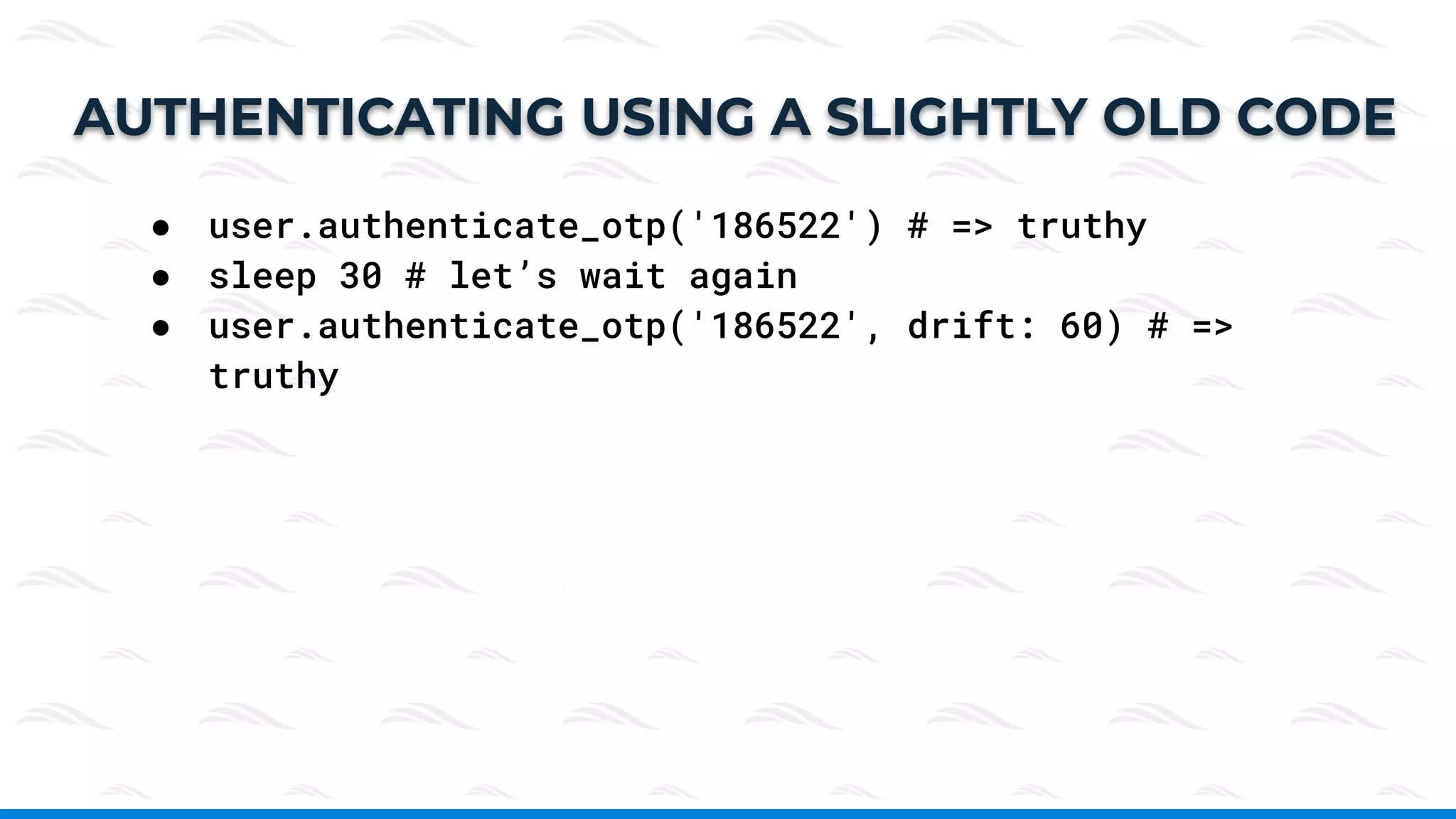
This document provides an overview of two-factor authentication (2FA), which adds an extra layer of security beyond just passwords, typically using a verification code from a mobile or computer app. It introduces a gem/library called 'active_model_otp' for implementing 2FA in user models within Ruby on Rails applications, detailing installation, configuration, and usage. Additional resources and a demo are linked for further exploration.