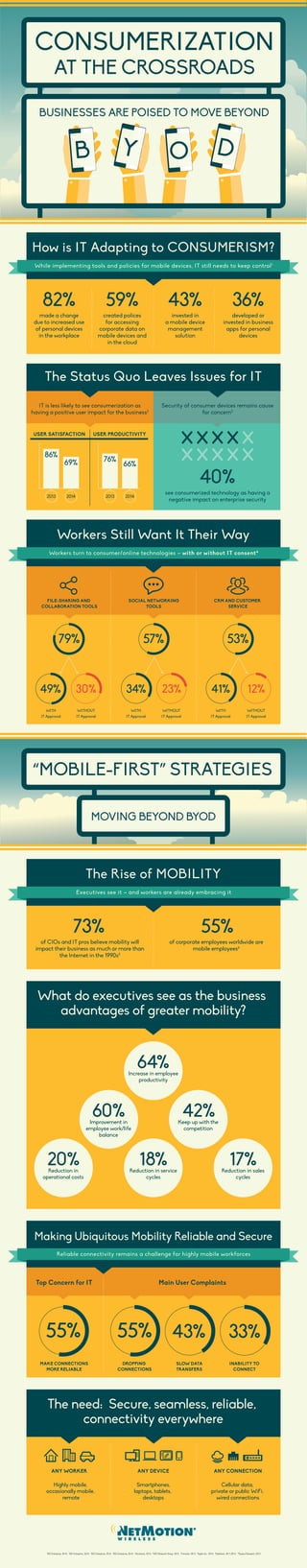
Consumerization at the Crossroads Infographic
•
0 likes•294 views
How is IT adapting to the rise of consumerism and BYOD? Why are executives driving mobility strategies in their organizations? Learn in our infographic!
Report
Share
Report
Share
Download to read offline
Recommended
How Is Mobile Changing How You Capture And Create Process-Based Content?

Learn how mobile is changing capture and creation processes for content. A presentation by 4Point from the AIIM Road Trip 2015.
Incredible Facts about BYOD

Incredible Facts about BYOD:
BYOD can help with more than savings:
• Increasing employee satisfaction via opt-in programs
• Attracting and retaining staff
• Expanding the number of mobile users – and the mobile app
opportunity
• Offloading the management of non-strategic devices
• Adopting technology at the speed of consumer markets
2014 Security Trends: SIEM, Endpoint Security, Data Loss, Mobile Devices and ...

Thanks to you, the audience at UltimateWindowsSecurity, for the 2014 Survey. It was a great success with over 600 respondents! I appreciate all of you who took the time give me your thoughts.
You’ve provided some great ideas for real training for free™ in the coming year and I’ve learned which topics are most important to you. That’s going to benefit all of us.
In this presentation, we'll present our findings. We’ll talk about the community’s top goals for 2014, which topics you recommended I cover in 2014 and what our community sees as the greatest security concerns for 2014. And we’ll discuss other trends emerging from the data.
Find out about the top trends, such as:
SIEM – What are the top SIEM solutions? What is the UWS community’s top 3 biggest challenges with log/monitoring/security analytics?
Endpoint Security – How widely is application whitelisting being used and what is driving its adoption? Which endpoint security technologies really work and which are just hype?
Mobile Devices – Are employee owned mobile devices supported at your organization? Is your biggest concern with mobile devices malware, data loss, compliance?
The Cloud – How widely are your peers embracing the cloud? Is your organization’s security policy, technology and training keeping up with the move to the cloud?
Advanced Security Topics – What are your peers doing about “big data”? What about endpoints as sensors, and other new security approaches?
This will be a fact-filled and fascinating presentation on where we are and where we are going on a host of different security fronts. Don’t miss it.
The changing mobile broadband landscape

1) Smartphone and mobile internet usage is growing rapidly in India, with overall smartphone penetration reaching 45% in 2015, up from 38% in 2013. Instant messaging, social networking, and bill payments are some of the most popular smartphone services.
2) Mobile broadband consumer groups in India are hugely varied, ranging from prudent business users to tech enthusiasts to image-conscious socialites. Around 1/3 of urban Indians now use smartphones.
3) Adoption barriers include high device and data costs, lack of digital literacy, and indoor and outdoor connectivity issues that are more commonly experienced in small to mid-sized cities. Over half of users do not see mobile internet as useful.
Infographic: Mobile user is always on

This document summarizes the results of a mobile survey conducted in 2013 with over 25,000 respondents across 43 countries. The survey found that lines between personal and work technology are blurred, with many using their personal devices for work. It also found that mobile users are highly engaged with their devices on weekends and evenings for activities like purchasing, video viewing, and interacting with ads. Mobile users are also much more likely to research, purchase, and recommend products and services online compared to 2012 levels.
M'sia Digital Scene - APRC 2013 Summit, Bankok.

This is a presentation on The Digital Scene in M'sia. I presented this during the Asia Pacific Research Committee Summit in Bangkok.
Fitness Flyer - Mobiloitte

The global market for fitness-related wearable technology is estimated to grow to 5,049.2 million US dollars by 2020.The revenue generated through fitness related apps will reach 3,827 million US dollars in 2020. The activity trackers and fitness applications are taking the place of personal coaches.
INFOGRAPHIC: Winning with Mobile

Organizations that want to leverage anytime, anywhere productivity need more than BYOD; they need a comprehensive mobile management and security framework. To learn more about Symantec Mobility Solutions, visit http://www.symantec.com/mobility.
Recommended
How Is Mobile Changing How You Capture And Create Process-Based Content?

Learn how mobile is changing capture and creation processes for content. A presentation by 4Point from the AIIM Road Trip 2015.
Incredible Facts about BYOD

Incredible Facts about BYOD:
BYOD can help with more than savings:
• Increasing employee satisfaction via opt-in programs
• Attracting and retaining staff
• Expanding the number of mobile users – and the mobile app
opportunity
• Offloading the management of non-strategic devices
• Adopting technology at the speed of consumer markets
2014 Security Trends: SIEM, Endpoint Security, Data Loss, Mobile Devices and ...

Thanks to you, the audience at UltimateWindowsSecurity, for the 2014 Survey. It was a great success with over 600 respondents! I appreciate all of you who took the time give me your thoughts.
You’ve provided some great ideas for real training for free™ in the coming year and I’ve learned which topics are most important to you. That’s going to benefit all of us.
In this presentation, we'll present our findings. We’ll talk about the community’s top goals for 2014, which topics you recommended I cover in 2014 and what our community sees as the greatest security concerns for 2014. And we’ll discuss other trends emerging from the data.
Find out about the top trends, such as:
SIEM – What are the top SIEM solutions? What is the UWS community’s top 3 biggest challenges with log/monitoring/security analytics?
Endpoint Security – How widely is application whitelisting being used and what is driving its adoption? Which endpoint security technologies really work and which are just hype?
Mobile Devices – Are employee owned mobile devices supported at your organization? Is your biggest concern with mobile devices malware, data loss, compliance?
The Cloud – How widely are your peers embracing the cloud? Is your organization’s security policy, technology and training keeping up with the move to the cloud?
Advanced Security Topics – What are your peers doing about “big data”? What about endpoints as sensors, and other new security approaches?
This will be a fact-filled and fascinating presentation on where we are and where we are going on a host of different security fronts. Don’t miss it.
The changing mobile broadband landscape

1) Smartphone and mobile internet usage is growing rapidly in India, with overall smartphone penetration reaching 45% in 2015, up from 38% in 2013. Instant messaging, social networking, and bill payments are some of the most popular smartphone services.
2) Mobile broadband consumer groups in India are hugely varied, ranging from prudent business users to tech enthusiasts to image-conscious socialites. Around 1/3 of urban Indians now use smartphones.
3) Adoption barriers include high device and data costs, lack of digital literacy, and indoor and outdoor connectivity issues that are more commonly experienced in small to mid-sized cities. Over half of users do not see mobile internet as useful.
Infographic: Mobile user is always on

This document summarizes the results of a mobile survey conducted in 2013 with over 25,000 respondents across 43 countries. The survey found that lines between personal and work technology are blurred, with many using their personal devices for work. It also found that mobile users are highly engaged with their devices on weekends and evenings for activities like purchasing, video viewing, and interacting with ads. Mobile users are also much more likely to research, purchase, and recommend products and services online compared to 2012 levels.
M'sia Digital Scene - APRC 2013 Summit, Bankok.

This is a presentation on The Digital Scene in M'sia. I presented this during the Asia Pacific Research Committee Summit in Bangkok.
Fitness Flyer - Mobiloitte

The global market for fitness-related wearable technology is estimated to grow to 5,049.2 million US dollars by 2020.The revenue generated through fitness related apps will reach 3,827 million US dollars in 2020. The activity trackers and fitness applications are taking the place of personal coaches.
INFOGRAPHIC: Winning with Mobile

Organizations that want to leverage anytime, anywhere productivity need more than BYOD; they need a comprehensive mobile management and security framework. To learn more about Symantec Mobility Solutions, visit http://www.symantec.com/mobility.
FOSE: Perspectives on Mobility & BYOD in the Government Market

This document discusses perspectives on mobility and bring your own device (BYOD) trends. It notes that mobile device sales now outpace PC sales and lists key drivers for business mobility adoption like attracting talent and improving productivity. While BYOD adoption is growing, it also brings risks like data theft and malware. The document outlines strategies for managing BYOD risks, including keeping devices updated, using passcodes, policies, mobile device management, app controls, encryption, and training.
Fitness

The digital healthcare network comprises of telehealth, mHealth(mobile), electronic patient records, wearable, and social media. Predictive analytics will help in providing preventive healthcare facilities rather than curative healthcare.
FITC NETPULSE WEBINAR 2015 - A WORLD OF APPS

This webinar content was created through a collaboration between Netpulse and the Fitness Industry Technology Council. It explores apps for fitness tracking, health and health clubs.
A World of Apps: Mobile Technology for Your Club Webinar

View Presentation: http://blog.netpulse.com/a-world-of-apps-mobile-technology-for-your-club-webinar-video
With more than 100,000 Android and iOS apps dedicated to mobile health, health and fitness apps are the the fastest growing app categories in the app store. How can you take advantage of this explosive growth?
Join Netpulse and Bryan O'Rourke, president of FIT-C, as we discuss the wonderful world of mobile apps and practical ways for operators to take advantage of this latest trend.
Is your enterprise ready for WYOD? 

Is your enterprise ready for WYOD? Wearable devices are marching into the Enterprise, creating security concerns for IT. This infographic highlights the growing importance of considering the mobile information security of wearable devices.
Fitness Flyers

HEALTH TRACKING, FITNESS MONITORING, DIETING, RUNNING, WORKOUT, PERSONAL TRAINING
Mobility has changed the way people workout, track health progress and get personal assistance.
Our team at Mobiloitte, designs mobile app solutions that help entrepreneurs and businesses mobilize their health & fitness ideas into mobile apps for different activities tracking and analysis needs. Want to track location, use gyro-sensor or build a wearable fitness app? Why not.
Slideshare reports say enterprise mobility is rising

Enterprise mobility is rising as businesses adopt mobile platforms for internal and external operations. When apps are implemented with security features, it redefines workflows and helps businesses, employees, partners, and prospects. A report found that enterprises are realizing mobile apps can simplify procedures for both internal and external computing needs. It was also noted that enterprise app activations are shifting more towards Android and document editing apps were highly used in Q2 2014. Mobile developers are addressing security concerns by improving code and adding encryption features.
Start-up Business Infographic

This document shows statistics on startup failure rates and industry survival rates. Over the first 4 years, the percentage of startups still operating declines each year from 71% after the first year to 37% after 4 years. After 4 years, the industries with the highest percentages of startups still operating are finance/insurance/real estate and education/health at 58% and 56% respectively, while information has the lowest survival rate at 37%.
Mobile learning

There are a number of benefits that organizations can accrue from the workforce and many of those advantages arise from the easy deployment of mobile learning applications.
https://www.designingdigitally.com/what-we-do/mobile-learning
Performance Monitoring Best Practices

Pressure to deliver new features and functionality fast, often with technologies new to your development/operations team, means you need to be ever more vigilant in how users experience your services – 24×7. This deck reviews performance monitoring best practices and how to implement them.
Infographic: Mobile the Final Frontier 

Wearable tech and the "internet of things" all need a hub to operate around and that hub is the mobile device.
Collaboration infographic on Midsize Business

Mobile device use is rising rapidly in businesses, with more employees working from home, while commuting, and in public places. Most IT departments have implemented solutions like secure wireless networks and device management to support this increased mobility. However, IT must now prepare for supporting greater mobile connectivity, speed, and integration with business apps. Cisco offers unified communications, networking, and security solutions to help mid-sized businesses navigate this next phase of mobility.
Good Mobility Index Report (Q1 2015)

The document is a quarterly report from Good Technology summarizing enterprise mobility trends. Key findings include secure browsers being the most popular app after email; insurance aggressively using custom apps; iOS maintaining a strong market share of over 70% led by the iPhone 6; and Android gaining tablet share while Windows tablets emerge.
Mary meeker's report 2016

India is experiencing the fastest growth in internet usage and is emerging as a major market. The Asia-Pacific region remains the largest market for smartphones, with Android dominating over iOS. While internet advertising is growing significantly in the US, adblocking is more prevalent on mobile than desktop. The impact of the internet is already broad but will continue expanding as the current generation of users grows and stays engaged online.
Digital Health On Your Wrist

As the Apple Watch enters the market, the "race to the wrist" intensifies with a deluge of use cases and apps in healthcare.
Mobile Technology and Opportunities for the Media

Extentia’s CEO Umeed Kothavala addressed students at the Department of Communication and Journalism, University of Mumbai on ‘Mobile Technology and Opportunities for the Media’.
This session was about mobile technology, related facts, mobile media channels, consumption of news on mobile, social media and mobile news, and the impact of citizen journalism.
Do let us know your comments/feedback on this presentation!
Mobile Landscape

India has over 800 million mobile subscribers, with 381 million able to access the internet and 60 million actively using mobile internet. Smartphone users account for 60 million, with more active mobile internet users residing in major metro areas. Tablet shipments are growing rapidly in India, and tablets have historically been the fastest selling consumer technology devices, taking fewer days to reach 1 million units sold than other devices.
Citrix Mobile Analytics Report September 2014: Mobile subscriber data usage t...

The Citrix Mobile Analytics Report for September 2014 provides insight into the personal experience of the mobile network subscriber and the impact of subscriber data usage on the mobile network. Citrix collected data from a global cross-section of its customers and applied big data analysis techniques to develop the report, which is intended to provide mobile network operators with real-world examples that can inform their decisions as they consider ways to improve their subscribers’ experience and better monetize data traffic. The report further provides the general reader with a snapshot of the state of the mobile data ecosystem.
Syskan Technosoft

The document lists details on mobile phone users, internet usage, and smartphone adoption in India. It also notes that 10-20% of the annual cost of smartphones goes to repairs and that there is high demand for skills in smartphone and tablet servicing. The document promotes courses by SysKan Technosoft on these topics.
The Future is Now – Software-Enabled Innovation

The Internet has disrupted almost every industry on earth in the past 25 years. Now, smart products, embedded with sensors and mechanisms that link them through the Internet, are turning the physical world into an information system.
Mobile Security Trends in the Workplace

Mobile security is a top priority for IT professionals in 2014 according to a survey. By 2020, 80% of access to enterprises will be via mobile devices. While 90% of employees use personal devices for work, less than half of organizations have mobile security policies. The majority of IT professionals see securing mobile data as important but only 13% feel their current solutions effectively do so. There is also a disconnect between BYOD policies and employee awareness and compliance, creating risks of unintended data leakage. [/SUMMARY]
The consumerization of it

This document summarizes a survey of 290 IT professionals about bring your own device (BYOD) and bring your own software (BYOS) trends. Some key findings include:
- 59% of businesses allow BYOD and 53% allow BYOS. Smartphones and tablets are the most common personal devices used for work.
- Nearly all IT professionals report challenges with BYOD/BYOS including security risks, loss of data, and managing access controls.
- While adoption of BYOD/BYOS is high, formal policies to regulate personal usage are still relatively rare.
More Related Content
What's hot
FOSE: Perspectives on Mobility & BYOD in the Government Market

This document discusses perspectives on mobility and bring your own device (BYOD) trends. It notes that mobile device sales now outpace PC sales and lists key drivers for business mobility adoption like attracting talent and improving productivity. While BYOD adoption is growing, it also brings risks like data theft and malware. The document outlines strategies for managing BYOD risks, including keeping devices updated, using passcodes, policies, mobile device management, app controls, encryption, and training.
Fitness

The digital healthcare network comprises of telehealth, mHealth(mobile), electronic patient records, wearable, and social media. Predictive analytics will help in providing preventive healthcare facilities rather than curative healthcare.
FITC NETPULSE WEBINAR 2015 - A WORLD OF APPS

This webinar content was created through a collaboration between Netpulse and the Fitness Industry Technology Council. It explores apps for fitness tracking, health and health clubs.
A World of Apps: Mobile Technology for Your Club Webinar

View Presentation: http://blog.netpulse.com/a-world-of-apps-mobile-technology-for-your-club-webinar-video
With more than 100,000 Android and iOS apps dedicated to mobile health, health and fitness apps are the the fastest growing app categories in the app store. How can you take advantage of this explosive growth?
Join Netpulse and Bryan O'Rourke, president of FIT-C, as we discuss the wonderful world of mobile apps and practical ways for operators to take advantage of this latest trend.
Is your enterprise ready for WYOD? 

Is your enterprise ready for WYOD? Wearable devices are marching into the Enterprise, creating security concerns for IT. This infographic highlights the growing importance of considering the mobile information security of wearable devices.
Fitness Flyers

HEALTH TRACKING, FITNESS MONITORING, DIETING, RUNNING, WORKOUT, PERSONAL TRAINING
Mobility has changed the way people workout, track health progress and get personal assistance.
Our team at Mobiloitte, designs mobile app solutions that help entrepreneurs and businesses mobilize their health & fitness ideas into mobile apps for different activities tracking and analysis needs. Want to track location, use gyro-sensor or build a wearable fitness app? Why not.
Slideshare reports say enterprise mobility is rising

Enterprise mobility is rising as businesses adopt mobile platforms for internal and external operations. When apps are implemented with security features, it redefines workflows and helps businesses, employees, partners, and prospects. A report found that enterprises are realizing mobile apps can simplify procedures for both internal and external computing needs. It was also noted that enterprise app activations are shifting more towards Android and document editing apps were highly used in Q2 2014. Mobile developers are addressing security concerns by improving code and adding encryption features.
Start-up Business Infographic

This document shows statistics on startup failure rates and industry survival rates. Over the first 4 years, the percentage of startups still operating declines each year from 71% after the first year to 37% after 4 years. After 4 years, the industries with the highest percentages of startups still operating are finance/insurance/real estate and education/health at 58% and 56% respectively, while information has the lowest survival rate at 37%.
Mobile learning

There are a number of benefits that organizations can accrue from the workforce and many of those advantages arise from the easy deployment of mobile learning applications.
https://www.designingdigitally.com/what-we-do/mobile-learning
Performance Monitoring Best Practices

Pressure to deliver new features and functionality fast, often with technologies new to your development/operations team, means you need to be ever more vigilant in how users experience your services – 24×7. This deck reviews performance monitoring best practices and how to implement them.
Infographic: Mobile the Final Frontier 

Wearable tech and the "internet of things" all need a hub to operate around and that hub is the mobile device.
Collaboration infographic on Midsize Business

Mobile device use is rising rapidly in businesses, with more employees working from home, while commuting, and in public places. Most IT departments have implemented solutions like secure wireless networks and device management to support this increased mobility. However, IT must now prepare for supporting greater mobile connectivity, speed, and integration with business apps. Cisco offers unified communications, networking, and security solutions to help mid-sized businesses navigate this next phase of mobility.
Good Mobility Index Report (Q1 2015)

The document is a quarterly report from Good Technology summarizing enterprise mobility trends. Key findings include secure browsers being the most popular app after email; insurance aggressively using custom apps; iOS maintaining a strong market share of over 70% led by the iPhone 6; and Android gaining tablet share while Windows tablets emerge.
Mary meeker's report 2016

India is experiencing the fastest growth in internet usage and is emerging as a major market. The Asia-Pacific region remains the largest market for smartphones, with Android dominating over iOS. While internet advertising is growing significantly in the US, adblocking is more prevalent on mobile than desktop. The impact of the internet is already broad but will continue expanding as the current generation of users grows and stays engaged online.
Digital Health On Your Wrist

As the Apple Watch enters the market, the "race to the wrist" intensifies with a deluge of use cases and apps in healthcare.
Mobile Technology and Opportunities for the Media

Extentia’s CEO Umeed Kothavala addressed students at the Department of Communication and Journalism, University of Mumbai on ‘Mobile Technology and Opportunities for the Media’.
This session was about mobile technology, related facts, mobile media channels, consumption of news on mobile, social media and mobile news, and the impact of citizen journalism.
Do let us know your comments/feedback on this presentation!
Mobile Landscape

India has over 800 million mobile subscribers, with 381 million able to access the internet and 60 million actively using mobile internet. Smartphone users account for 60 million, with more active mobile internet users residing in major metro areas. Tablet shipments are growing rapidly in India, and tablets have historically been the fastest selling consumer technology devices, taking fewer days to reach 1 million units sold than other devices.
Citrix Mobile Analytics Report September 2014: Mobile subscriber data usage t...

The Citrix Mobile Analytics Report for September 2014 provides insight into the personal experience of the mobile network subscriber and the impact of subscriber data usage on the mobile network. Citrix collected data from a global cross-section of its customers and applied big data analysis techniques to develop the report, which is intended to provide mobile network operators with real-world examples that can inform their decisions as they consider ways to improve their subscribers’ experience and better monetize data traffic. The report further provides the general reader with a snapshot of the state of the mobile data ecosystem.
Syskan Technosoft

The document lists details on mobile phone users, internet usage, and smartphone adoption in India. It also notes that 10-20% of the annual cost of smartphones goes to repairs and that there is high demand for skills in smartphone and tablet servicing. The document promotes courses by SysKan Technosoft on these topics.
The Future is Now – Software-Enabled Innovation

The Internet has disrupted almost every industry on earth in the past 25 years. Now, smart products, embedded with sensors and mechanisms that link them through the Internet, are turning the physical world into an information system.
What's hot (20)
FOSE: Perspectives on Mobility & BYOD in the Government Market

FOSE: Perspectives on Mobility & BYOD in the Government Market
A World of Apps: Mobile Technology for Your Club Webinar

A World of Apps: Mobile Technology for Your Club Webinar
Slideshare reports say enterprise mobility is rising

Slideshare reports say enterprise mobility is rising
Citrix Mobile Analytics Report September 2014: Mobile subscriber data usage t...

Citrix Mobile Analytics Report September 2014: Mobile subscriber data usage t...
Similar to Consumerization at the Crossroads Infographic
Mobile Security Trends in the Workplace

Mobile security is a top priority for IT professionals in 2014 according to a survey. By 2020, 80% of access to enterprises will be via mobile devices. While 90% of employees use personal devices for work, less than half of organizations have mobile security policies. The majority of IT professionals see securing mobile data as important but only 13% feel their current solutions effectively do so. There is also a disconnect between BYOD policies and employee awareness and compliance, creating risks of unintended data leakage. [/SUMMARY]
The consumerization of it

This document summarizes a survey of 290 IT professionals about bring your own device (BYOD) and bring your own software (BYOS) trends. Some key findings include:
- 59% of businesses allow BYOD and 53% allow BYOS. Smartphones and tablets are the most common personal devices used for work.
- Nearly all IT professionals report challenges with BYOD/BYOS including security risks, loss of data, and managing access controls.
- While adoption of BYOD/BYOS is high, formal policies to regulate personal usage are still relatively rare.
Logicalis Global CIO Survey 2016

Digital enablers: the challenges facing CIOs in an age of digital transformation. Research from Logicalis based on a global study of CIO pressures and priorities.
Preparing for the Future of Enterprise Mobility -- Insights Not to Miss

Interested in knowing what CIOs and other IT executives really think about the future of enterprise mobility? Join Enterprise Mobile as we delve into the results of a survey conducted to assess the business impact of enterprise mobility based on input from technology leaders. We’ll give you tips to prepare for the future of enterprise mobility, secrets to removing barriers to mobile strategy implementation and show you how other companies are embracing mobile security.
Watch the presentation here: http://bit.ly/180vPc5
Download our BYOD Policy Template here: http://bit.ly/1aEJqd8
2014 Secure Mobility Survey Report

A critical gap exists between the enterprise mobility vision and
real-world implementations.
Enterprise mobility and trends like bring your own device
(BYOD) aren’t just hot topics of conversation.
According to the over 1,600 IT and security professionals we surveyed, mobility is a top priority for most IT departments.
Unfortunately, there’s a critical gap between the vision these IT leaders have for enterprise mobility and the real-world implementations.
The insights gathered from IT professionals in the Americas, Asia Pacific, Europe, the Middle East, and Africa demonstrate that organisations from around the world share many of the same priorities, challenges and risks.
Digital Transformation and the Role of IAM

We surveyed 200 IT decision makers across four countries
to learn where they are in their journey and the role that identity and access management (IAM) plays in the path to digital transformation.
10 Incredible BYOD Facts

BYOD (bring your own device) is becoming increasingly common, with 90% of American workers using their personal smartphones for work even without official BYOD policies. While BYOD can increase productivity and reduce costs, it also poses security risks if devices are not properly secured and monitored. The document outlines 10 lesser-known facts about BYOD trends, such as that over half of companies now allow or require BYOD, and education workers have the highest rate of smartphone usage at work at 95.2%.
VMware Model for Enterprise Mobility

This document discusses how increased mobility and use of mobile devices is driving workforce productivity higher. It notes that employees who use mobile devices for work increase their productivity by an estimated 9 hours per week on average. The growth of bring your own device (BYOD) programs and software-as-a-service (SaaS) applications is enabling more mobile work styles. However, this increased mobility also presents security risks to companies' data and applications. The challenge for CIOs is to develop strategies that allow for mobility and choice while still securely managing users and enforcing policies across devices.
BYOD

Its about the changes the company makes in their organization for their employee...Is it good or bad ?
Mobility Research 2014: Mobility Fueling the Digital Surge

The document summarizes a survey of executives about their company's use of mobility technologies. It finds that most companies see mobility as a top priority and have a mobility strategy, but many struggle with implementation challenges. It identifies "mobility leaders" who take a more comprehensive and strategic approach by integrating mobility across their entire organization and viewing it as part of their overall digital transformation.
It consumerisation presentation

The document discusses the consumerization of information technology in enterprises. It notes that trends originating in consumer technologies like social media and mobile devices are increasingly being used in the workplace. This blurs the lines between work and personal technologies and devices. It poses security challenges as employees use their own smartphones and tablets for work. The document recommends that enterprises establish policies and protocols to securely manage the use of consumer devices and platforms at work. It also suggests implementing data loss prevention programs to mitigate the risks to confidential data and intellectual property from the consumerization of IT.
It consumerisation presentation

The document discusses the consumerization of information technology in enterprises. It notes that trends originating in consumer technologies like social media and mobile devices are increasingly being used in the workplace. This blurs the lines between work and personal technologies and devices. It poses security challenges as employees use their own smartphones and tablets for work. The document recommends that enterprises establish policies and protocols to securely manage the use of consumer devices and platforms at work. It also suggests implementing data loss prevention programs to mitigate the risks to confidential data and intellectual property from the consumerization of IT.
The impact of mobile devices on information security

Etude sur les risques et les coûts induits par la multiplication de l'utilisation des plate-formes mobiles au sein des entreprises.
“The Impact of Mobile Devices on Information Security: A Survey of IT and Sec...

1. The survey found that the number of personal mobile devices connecting to corporate networks continues to grow significantly, with 75% of companies now allowing personal devices on networks, up from 67% in 2013.
2. IT and security professionals expect that the rise in mobile devices will lead to more mobile security incidents, with 82% anticipating increased incidents in the coming year. The costs of remediating incidents is also increasing.
3. Employee behavior is seen as a major factor in mobile security risks, with most respondents saying careless employees pose a greater threat than cybercriminals and that employee actions likely enabled recent high-profile breaches.
Integrating Enterprise Mobility - an Assessment WHITE PAPER

We offer complete satisfaction to our customers by following standardized SDLC processes, hiring the best of breed developers and mastering most of our requirements gathering, wireframing, designing, developing, testing, delivering, deploying and maintenance tasks.
Ours is an off-shore model, but we ensure that both customer and Mobiloitte are always in touch by keeping communications open, providing regular updates and iterative releases so that the customer is always well informed.
Insight 2020 Technology Report: IT Trends for Midmarket and Small Business

For midmarket and small business, IT is a complex world. How are others in your space managing IT today, while taking steps to prepare for tomorrow's needs? We interviewed 408 IT pros to find out. View the SlideShare to see key statistics from our Insight 2020 Technology Report: IT Trends for Midmarket and Small Business. Find out how other companies in this space are managing IT and procurement, equipping their workforce with the right tech, handling cloud migration and where they are in their digital transformation journey.
CIO COVID-19 Impact Survey, Infographic

CIO conducted the COVID-19 Impact Study to better understand how organizations were prepared for this past month and beyond, and how IT leaders are responding.
How enterprise mobility improves productivty

Enterprise mobility has so many benefits to business, but we don't speak about it anymore because of other trending terms. The importance of this service has never been as critical as it is today with faster connectivity looming that will make mobile devices the go-to device for all businesses today.
Get Ready for Wearables at Work

Wearable technology has left the realm of science fiction and landed squarely in the real world. This Spiceworks white paper, based on a recent survey of IT pros, looks at barriers and benefits to adoption of wearables in the workplace. To learn more, visit http://smbz.us/1bbIhQv
Managing Mobile Business Insecurities

Hundreds of millions of people use smartphones for everyday tasks. As more people use their phones for personal and business purposes, the number of uncontrolled smart phones is growing.
Similar to Consumerization at the Crossroads Infographic (20)
Preparing for the Future of Enterprise Mobility -- Insights Not to Miss

Preparing for the Future of Enterprise Mobility -- Insights Not to Miss
Mobility Research 2014: Mobility Fueling the Digital Surge

Mobility Research 2014: Mobility Fueling the Digital Surge
The impact of mobile devices on information security

The impact of mobile devices on information security
“The Impact of Mobile Devices on Information Security: A Survey of IT and Sec...

“The Impact of Mobile Devices on Information Security: A Survey of IT and Sec...
Integrating Enterprise Mobility - an Assessment WHITE PAPER

Integrating Enterprise Mobility - an Assessment WHITE PAPER
Insight 2020 Technology Report: IT Trends for Midmarket and Small Business

Insight 2020 Technology Report: IT Trends for Midmarket and Small Business
More from NetMotion Wireless
Telemedicine Strategies: Manageing Data and Mobile Devices

Gain insights into real-world examples of successful telehealth mobile integrations. Join the University of Mississippi Medical center, the Hackensack University Medical Center, and NetMotion Wireless as they discuss telehealth challenges and benefits, including:
Device integration and interoperability challenges
Data privacy and security concerns
Improved patient care outcomes
Decreased re-admissions and cost controls
Are Tablets Changing the Game for Field Service?

Review the findings for a Pennwell Research Survey to discover how tablets are being adopted by the Utility industry and what challenges their impact has on IT.
Perfectly Adapted, Not Quite Adopted Table Infographic

How are tablets being adopted in the Utility industry? What is the operating system that is commonly being used ? What are challenges are the tablet adopters facing? Learn more in our infographic!
Telemedicine: Prepare for Take-off Infographic

How and why is Telemedicine growing in the US? How will this impact the usage of technology in the healthcare industry? View our infographic to learn more!
NetMotion Wireless Healthcare Goes Mobile Infographic

View the "Highly Mobile Medicine Infographic" to learn:
What issues are on IT's radar
What are the top complaints from clinicians in the field
How many organizations are allowing BYOD (Bring Your Own Device)
NetMotion Wireless Strategies For Managing Cellular Network Performance

NetMotion Wireless Strategies For Managing Cellular Network Performance: How Enterprise Can Manage and Optimize Their Critical Mobile Deployment
NetMotion Wireless Continuity of Emergency Response Communications

Effective emergency response requires reliable communication between response agencies, but disasters often damage infrastructure, disrupting communication. To address this, agencies should establish redundant communication channels using a combination of wired, wireless, and satellite technologies and ensure first responders can connect reliably through mobile VPNs to coordinate response and recovery efforts despite intermittent connectivity. Planning for communication contingencies and deploying portable wireless equipment enables response even when primary communication channels have failed.
NetMotion Wireless Survey on the Evolutionary Growth in Mobile Technologies U...

NetMotion Wireless Government On The Move: Survey on the Evolutionary Growth in Mobile Technologies Used by Government Agencies
Frost & Sullivan Global Mobile VPN Products Market

Frost & Sullivan Global Mobile VPN Products Market: Meeting the Wireless Security Challenge with an Emerging VPN for the Remote Worker
Rysavy Research Trends in Enterprise Cellular Network Data Usage Webinar

Trends in Enterprise Cellular Network Data Usage Webinar
Presented by InfoWeek, NetMotion Wireless and Rysavy Research
NetMotion Wireless Troubleshooting Wireless Cellular Networks Webinar

This document discusses the growing reliance on cellular networks due to increased workforce mobility and availability of mobile devices. It notes challenges in managing cellular networks due to low visibility into network performance and user experiences. A solution presented is network management software that provides real-time monitoring of field users and cellular networks to help optimize deployments and inform business decisions. A demonstration of Locality software is provided, which analyzes network data to give insights into coverage, carriers, and device performance across public cellular networks and corporate infrastructure.
Frost & Sullivan The New Mobility: How Mobile Applications and Devices are Ch...

The New Mobility: How Mobile Applications and Devices are Changing Your Business
NetMotion Wireless and Frost & Sullivan
Rysavy Research Trends In Enterprise Cellular Network Data Usage Survey Results

In 2013, NetMotion Wireless and Rysavy Research conducted a survey of more than 400 networking professionals from a variety of industries, to gain insight into the state of cellular data deployments. This survey provides insight into the value of these deployments, current practices, and challenges. Also, it uncovers where there might be shortfalls and opportunities to improve efficiency and effectiveness as we look toward the future of mobile data.
More from NetMotion Wireless (13)
Telemedicine Strategies: Manageing Data and Mobile Devices

Telemedicine Strategies: Manageing Data and Mobile Devices
Perfectly Adapted, Not Quite Adopted Table Infographic

Perfectly Adapted, Not Quite Adopted Table Infographic
NetMotion Wireless Healthcare Goes Mobile Infographic

NetMotion Wireless Healthcare Goes Mobile Infographic
NetMotion Wireless Strategies For Managing Cellular Network Performance

NetMotion Wireless Strategies For Managing Cellular Network Performance
NetMotion Wireless Continuity of Emergency Response Communications

NetMotion Wireless Continuity of Emergency Response Communications
NetMotion Wireless Survey on the Evolutionary Growth in Mobile Technologies U...

NetMotion Wireless Survey on the Evolutionary Growth in Mobile Technologies U...
Frost & Sullivan Global Mobile VPN Products Market

Frost & Sullivan Global Mobile VPN Products Market
Rysavy Research Trends in Enterprise Cellular Network Data Usage Webinar

Rysavy Research Trends in Enterprise Cellular Network Data Usage Webinar
NetMotion Wireless Troubleshooting Wireless Cellular Networks Webinar

NetMotion Wireless Troubleshooting Wireless Cellular Networks Webinar
Frost & Sullivan The New Mobility: How Mobile Applications and Devices are Ch...

Frost & Sullivan The New Mobility: How Mobile Applications and Devices are Ch...
Rysavy Research Trends In Enterprise Cellular Network Data Usage Survey Results

Rysavy Research Trends In Enterprise Cellular Network Data Usage Survey Results
Recently uploaded
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
Session 1 - Intro to Robotic Process Automation.pdf

👉 Check out our full 'Africa Series - Automation Student Developers (EN)' page to register for the full program:
https://bit.ly/Automation_Student_Kickstart
In this session, we shall introduce you to the world of automation, the UiPath Platform, and guide you on how to install and setup UiPath Studio on your Windows PC.
📕 Detailed agenda:
What is RPA? Benefits of RPA?
RPA Applications
The UiPath End-to-End Automation Platform
UiPath Studio CE Installation and Setup
💻 Extra training through UiPath Academy:
Introduction to Automation
UiPath Business Automation Platform
Explore automation development with UiPath Studio
👉 Register here for our upcoming Session 2 on June 20: Introduction to UiPath Studio Fundamentals: https://community.uipath.com/events/details/uipath-lagos-presents-session-2-introduction-to-uipath-studio-fundamentals/
“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...

“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/temporal-event-neural-networks-a-more-efficient-alternative-to-the-transformer-a-presentation-from-brainchip/
Chris Jones, Director of Product Management at BrainChip , presents the “Temporal Event Neural Networks: A More Efficient Alternative to the Transformer” tutorial at the May 2024 Embedded Vision Summit.
The expansion of AI services necessitates enhanced computational capabilities on edge devices. Temporal Event Neural Networks (TENNs), developed by BrainChip, represent a novel and highly efficient state-space network. TENNs demonstrate exceptional proficiency in handling multi-dimensional streaming data, facilitating advancements in object detection, action recognition, speech enhancement and language model/sequence generation. Through the utilization of polynomial-based continuous convolutions, TENNs streamline models, expedite training processes and significantly diminish memory requirements, achieving notable reductions of up to 50x in parameters and 5,000x in energy consumption compared to prevailing methodologies like transformers.
Integration with BrainChip’s Akida neuromorphic hardware IP further enhances TENNs’ capabilities, enabling the realization of highly capable, portable and passively cooled edge devices. This presentation delves into the technical innovations underlying TENNs, presents real-world benchmarks, and elucidates how this cutting-edge approach is positioned to revolutionize edge AI across diverse applications.Essentials of Automations: Exploring Attributes & Automation Parameters

Building automations in FME Flow can save time, money, and help businesses scale by eliminating data silos and providing data to stakeholders in real-time. One essential component to orchestrating complex automations is the use of attributes & automation parameters (both formerly known as “keys”). In fact, it’s unlikely you’ll ever build an Automation without using these components, but what exactly are they?
Attributes & automation parameters enable the automation author to pass data values from one automation component to the next. During this webinar, our FME Flow Specialists will cover leveraging the three types of these output attributes & parameters in FME Flow: Event, Custom, and Automation. As a bonus, they’ll also be making use of the Split-Merge Block functionality.
You’ll leave this webinar with a better understanding of how to maximize the potential of automations by making use of attributes & automation parameters, with the ultimate goal of setting your enterprise integration workflows up on autopilot.
A Deep Dive into ScyllaDB's Architecture

This talk will cover ScyllaDB Architecture from the cluster-level view and zoom in on data distribution and internal node architecture. In the process, we will learn the secret sauce used to get ScyllaDB's high availability and superior performance. We will also touch on the upcoming changes to ScyllaDB architecture, moving to strongly consistent metadata and tablets.
Main news related to the CCS TSI 2023 (2023/1695)

An English 🇬🇧 translation of a presentation to the speech I gave about the main changes brought by CCS TSI 2023 at the biggest Czech conference on Communications and signalling systems on Railways, which was held in Clarion Hotel Olomouc from 7th to 9th November 2023 (konferenceszt.cz). Attended by around 500 participants and 200 on-line followers.
The original Czech 🇨🇿 version of the presentation can be found here: https://www.slideshare.net/slideshow/hlavni-novinky-souvisejici-s-ccs-tsi-2023-2023-1695/269688092 .
The videorecording (in Czech) from the presentation is available here: https://youtu.be/WzjJWm4IyPk?si=SImb06tuXGb30BEH .
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
Skybuffer SAM4U tool for SAP license adoption

Manage and optimize your license adoption and consumption with SAM4U, an SAP free customer software asset management tool.
SAM4U, an SAP complimentary software asset management tool for customers, delivers a detailed and well-structured overview of license inventory and usage with a user-friendly interface. We offer a hosted, cost-effective, and performance-optimized SAM4U setup in the Skybuffer Cloud environment. You retain ownership of the system and data, while we manage the ABAP 7.58 infrastructure, ensuring fixed Total Cost of Ownership (TCO) and exceptional services through the SAP Fiori interface.
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
LF Energy Webinar: Carbon Data Specifications: Mechanisms to Improve Data Acc...

This LF Energy webinar took place June 20, 2024. It featured:
-Alex Thornton, LF Energy
-Hallie Cramer, Google
-Daniel Roesler, UtilityAPI
-Henry Richardson, WattTime
In response to the urgency and scale required to effectively address climate change, open source solutions offer significant potential for driving innovation and progress. Currently, there is a growing demand for standardization and interoperability in energy data and modeling. Open source standards and specifications within the energy sector can also alleviate challenges associated with data fragmentation, transparency, and accessibility. At the same time, it is crucial to consider privacy and security concerns throughout the development of open source platforms.
This webinar will delve into the motivations behind establishing LF Energy’s Carbon Data Specification Consortium. It will provide an overview of the draft specifications and the ongoing progress made by the respective working groups.
Three primary specifications will be discussed:
-Discovery and client registration, emphasizing transparent processes and secure and private access
-Customer data, centering around customer tariffs, bills, energy usage, and full consumption disclosure
-Power systems data, focusing on grid data, inclusive of transmission and distribution networks, generation, intergrid power flows, and market settlement data
The Microsoft 365 Migration Tutorial For Beginner.pptx

This presentation will help you understand the power of Microsoft 365. However, we have mentioned every productivity app included in Office 365. Additionally, we have suggested the migration situation related to Office 365 and how we can help you.
You can also read: https://www.systoolsgroup.com/updates/office-365-tenant-to-tenant-migration-step-by-step-complete-guide/
What is an RPA CoE? Session 1 – CoE Vision

In the first session, we will review the organization's vision and how this has an impact on the COE Structure.
Topics covered:
• The role of a steering committee
• How do the organization’s priorities determine CoE Structure?
Speaker:
Chris Bolin, Senior Intelligent Automation Architect Anika Systems
Leveraging the Graph for Clinical Trials and Standards

Katja Glaß
OpenStudyBuilder Community Manager - Katja Glaß Consulting
Marius Conjeaud
Principal Consultant - Neo4j
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
Demystifying Knowledge Management through Storytelling

The Department of Veteran Affairs (VA) invited Taylor Paschal, Knowledge & Information Management Consultant at Enterprise Knowledge, to speak at a Knowledge Management Lunch and Learn hosted on June 12, 2024. All Office of Administration staff were invited to attend and received professional development credit for participating in the voluntary event.
The objectives of the Lunch and Learn presentation were to:
- Review what KM ‘is’ and ‘isn’t’
- Understand the value of KM and the benefits of engaging
- Define and reflect on your “what’s in it for me?”
- Share actionable ways you can participate in Knowledge - - Capture & Transfer
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Must Know Postgres Extension for DBA and Developer during Migration

Mydbops Opensource Database Meetup 16
Topic: Must-Know PostgreSQL Extensions for Developers and DBAs During Migration
Speaker: Deepak Mahto, Founder of DataCloudGaze Consulting
Date & Time: 8th June | 10 AM - 1 PM IST
Venue: Bangalore International Centre, Bangalore
Abstract: Discover how PostgreSQL extensions can be your secret weapon! This talk explores how key extensions enhance database capabilities and streamline the migration process for users moving from other relational databases like Oracle.
Key Takeaways:
* Learn about crucial extensions like oracle_fdw, pgtt, and pg_audit that ease migration complexities.
* Gain valuable strategies for implementing these extensions in PostgreSQL to achieve license freedom.
* Discover how these key extensions can empower both developers and DBAs during the migration process.
* Don't miss this chance to gain practical knowledge from an industry expert and stay updated on the latest open-source database trends.
Mydbops Managed Services specializes in taking the pain out of database management while optimizing performance. Since 2015, we have been providing top-notch support and assistance for the top three open-source databases: MySQL, MongoDB, and PostgreSQL.
Our team offers a wide range of services, including assistance, support, consulting, 24/7 operations, and expertise in all relevant technologies. We help organizations improve their database's performance, scalability, efficiency, and availability.
Contact us: info@mydbops.com
Visit: https://www.mydbops.com/
Follow us on LinkedIn: https://in.linkedin.com/company/mydbops
For more details and updates, please follow up the below links.
Meetup Page : https://www.meetup.com/mydbops-databa...
Twitter: https://twitter.com/mydbopsofficial
Blogs: https://www.mydbops.com/blog/
Facebook(Meta): https://www.facebook.com/mydbops/
Recently uploaded (20)
Session 1 - Intro to Robotic Process Automation.pdf

Session 1 - Intro to Robotic Process Automation.pdf
9 CEO's who hit $100m ARR Share Their Top Growth Tactics Nathan Latka, Founde...

9 CEO's who hit $100m ARR Share Their Top Growth Tactics Nathan Latka, Founde...
“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...

“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...
Essentials of Automations: Exploring Attributes & Automation Parameters

Essentials of Automations: Exploring Attributes & Automation Parameters
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
LF Energy Webinar: Carbon Data Specifications: Mechanisms to Improve Data Acc...

LF Energy Webinar: Carbon Data Specifications: Mechanisms to Improve Data Acc...
The Microsoft 365 Migration Tutorial For Beginner.pptx

The Microsoft 365 Migration Tutorial For Beginner.pptx
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
Leveraging the Graph for Clinical Trials and Standards

Leveraging the Graph for Clinical Trials and Standards
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
Demystifying Knowledge Management through Storytelling

Demystifying Knowledge Management through Storytelling
Must Know Postgres Extension for DBA and Developer during Migration

Must Know Postgres Extension for DBA and Developer during Migration
Consumerization at the Crossroads Infographic
- 1. BUSINESSES ARE POISED TO MOVE BEYOND Y OB D CONSUMERIZATION AT THE CROSSROADS MOVING BEYOND BYOD “MOBILE-FIRST” STRATEGIES How is IT Adapting to CONSUMERISM? 82% made a change due to increased use of personal devices in the workplace created polices for accessing corporate data on mobile devices and in the cloud 59% invested in a mobile device management solution 43% developed or invested in business apps for personal devices 36% While implementing tools and policies for mobile devices, IT still needs to keep control1 The Rise of MOBILITY 73% of CIOs and IT pros believe mobility will impact their business as much or more than the Internet in the 1990s5 of corporate employees worldwide are mobile employees6 55% Executives see it – and workers are already embracing it The Status Quo Leaves Issues for IT 86% 2013 2014 69% 2013 2014 76% 66% USER SATISFACTION USER PRODUCTIVITY see consumerized technology as having a negative impact on enterprise security 40% Workers Still Want It Their Way Workers turn to consumer/online technologies – with or without IT consent4 79% 49% 30% 34% 23% 57% 41% 12% 53% WITH IT Approval WITHOUT IT Approval WITH IT Approval WITHOUT IT Approval WITH IT Approval WITHOUT IT Approval Making Ubiquitous Mobility Reliable and Secure Reliable connectivity remains a challenge for highly mobile workforces Top Concern for IT Main User Complaints 55% MAKE CONNECTIONS MORE RELIABLE What do executives see as the business advantages of greater mobility? 64%Increase in employee productivity 18%Reduction in service cycles 20%Reduction in operational costs 17%Reduction in sales cycles 60%Improvement in employee work/life balance 42%Keep up with the competition The need: Secure, seamless, reliable, connectivity everywhere 55% DROPPING CONNECTIONS SLOW DATA TRANSFERS INABILITY TO CONNECT 33%43% FILE-SHARING AND COLLABORATION TOOLS SOCIAL NETWORKING TOOLS CRM AND CUSTOMER SERVICE IT is less likely to see consumerization as having a positive user impact for the business2 Security of consumer devices remains cause for concern3 ANY WORKER ANY DEVICE ANY CONNECTION Highly mobile, occasionally mobile, remote Smartphones, laptops, tablets, desktops Cellular data, private or public WiFi, wired connections 1 IDG Enterprise, 2014; 2 IDG Enterprise, 2014; 3 IDG Enterprise, 2014; 4 IDG Enterprise, 2014; 5 Accenture, 2013; 6 VDC Research Group, 2012; 7 Forrester, 2013; 8 Apple Inc., 2014; 9 Vodafone, 2011-2013; 10 Rysavy Research, 2013
