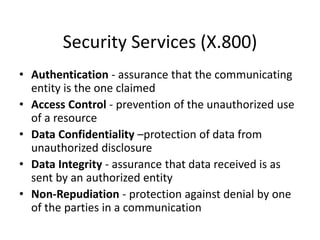
Cyber security involves protecting computer systems, networks, and data from malicious attacks and damage. It works to defend against threats through practices like authentication, access control, encryption, and integrity checks. Common security services include authentication to verify identities, access control to restrict unauthorized use of resources, encryption to protect confidential data, and integrity checks to ensure data hasn't been altered. Security mechanisms implement these services using techniques like encryption, digital signatures, access controls, and auditing. Attacks can be passive like eavesdropping or active like masquerading, replaying messages, or denial of service.