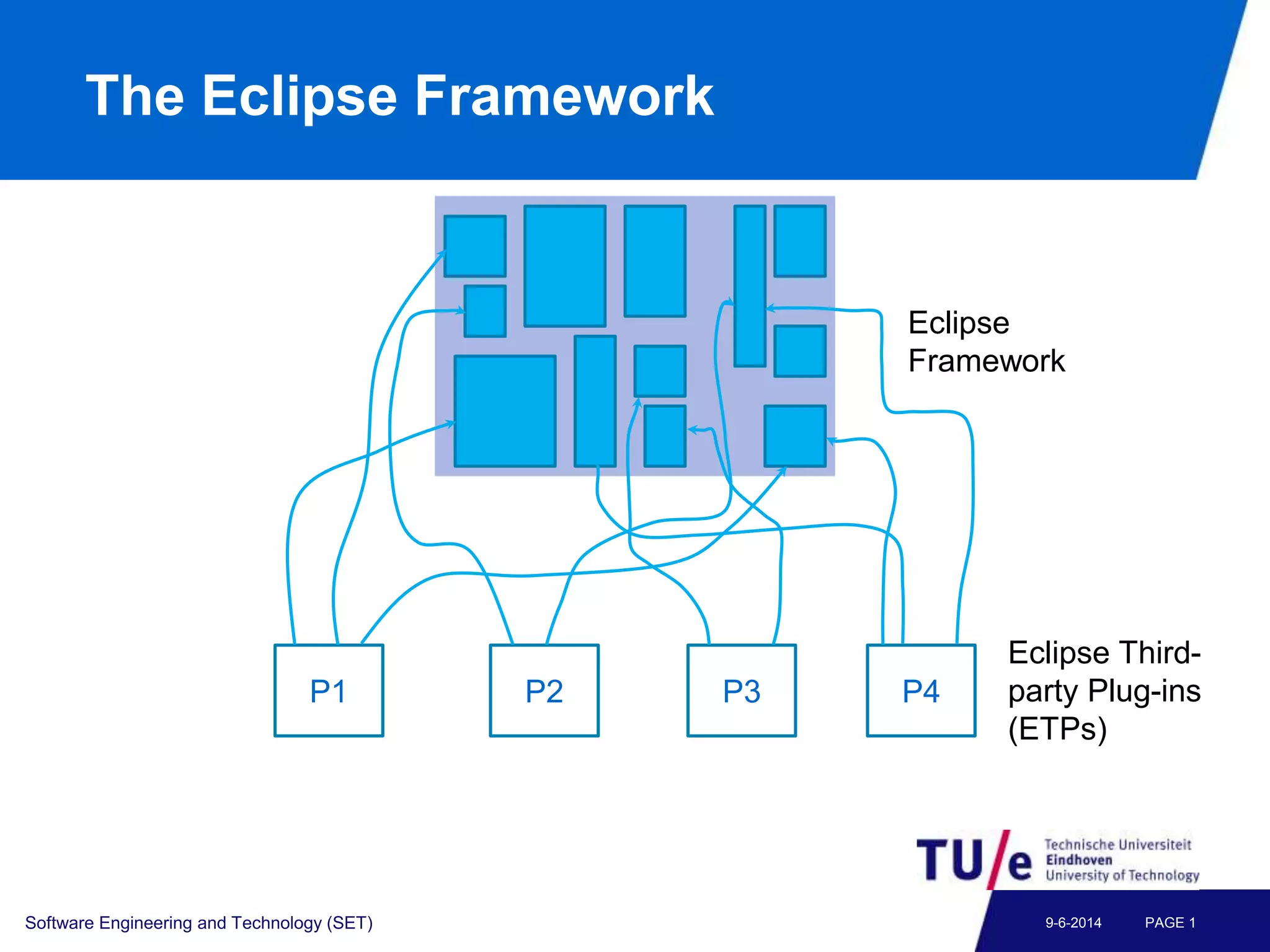
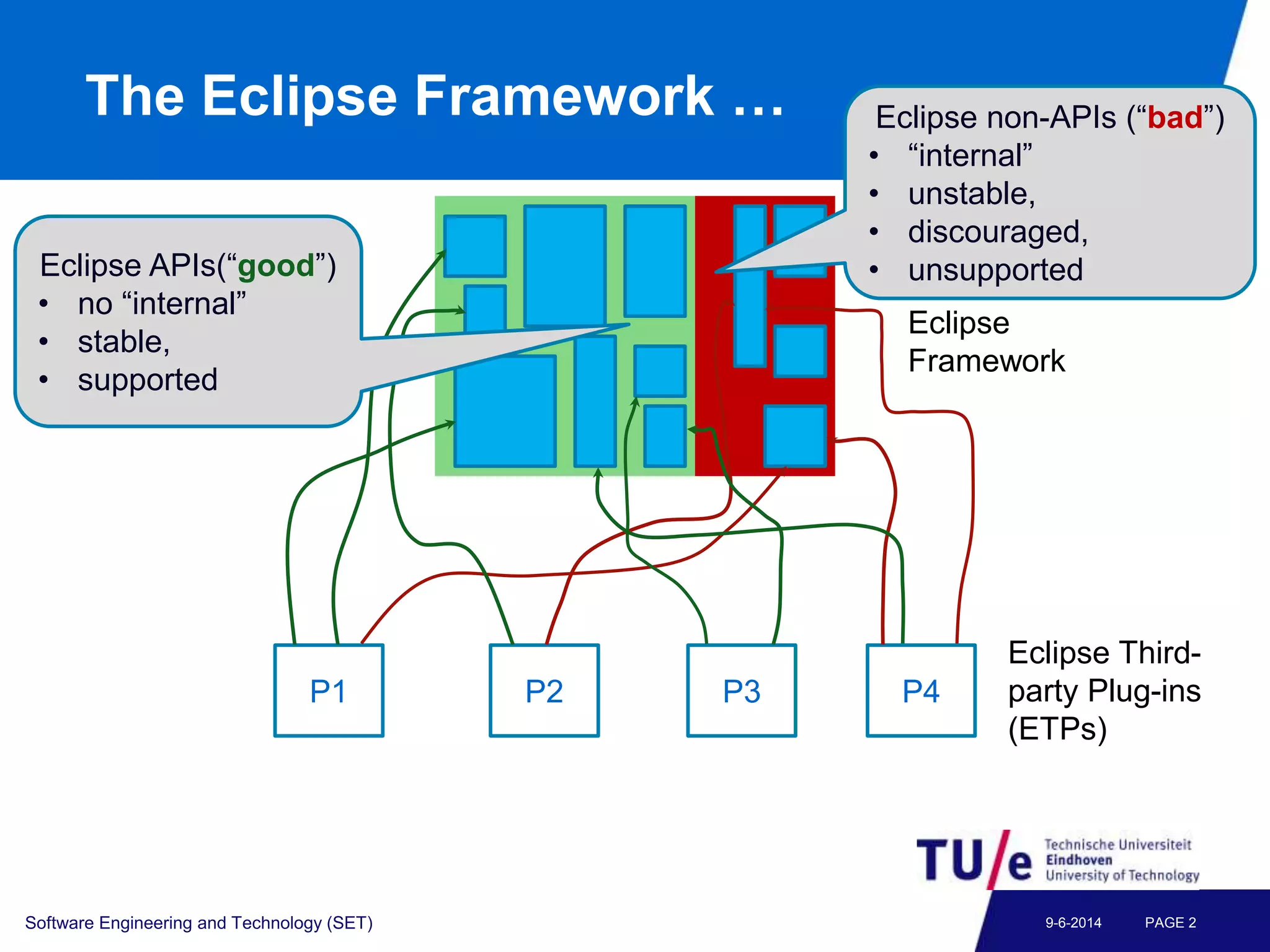
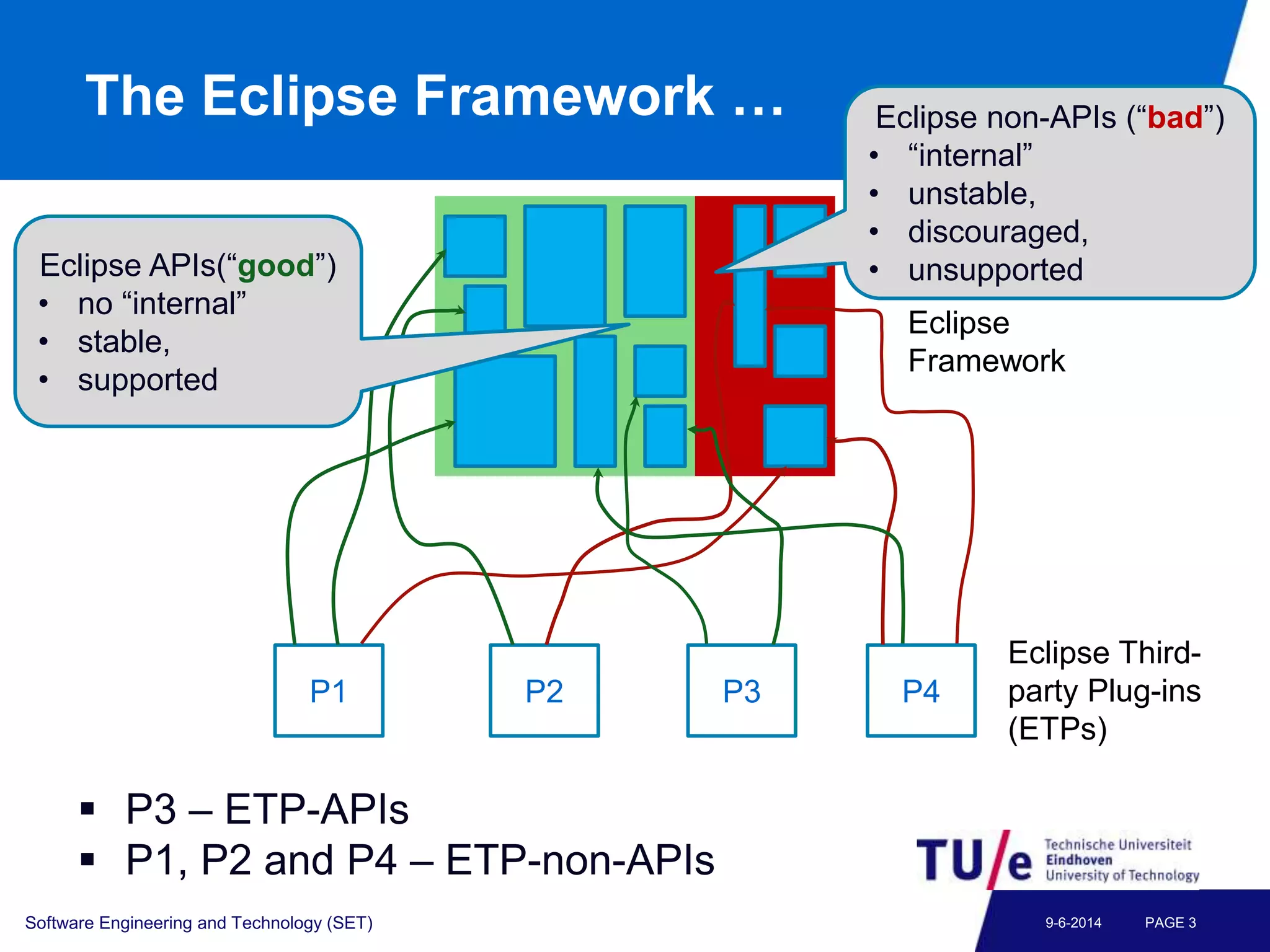
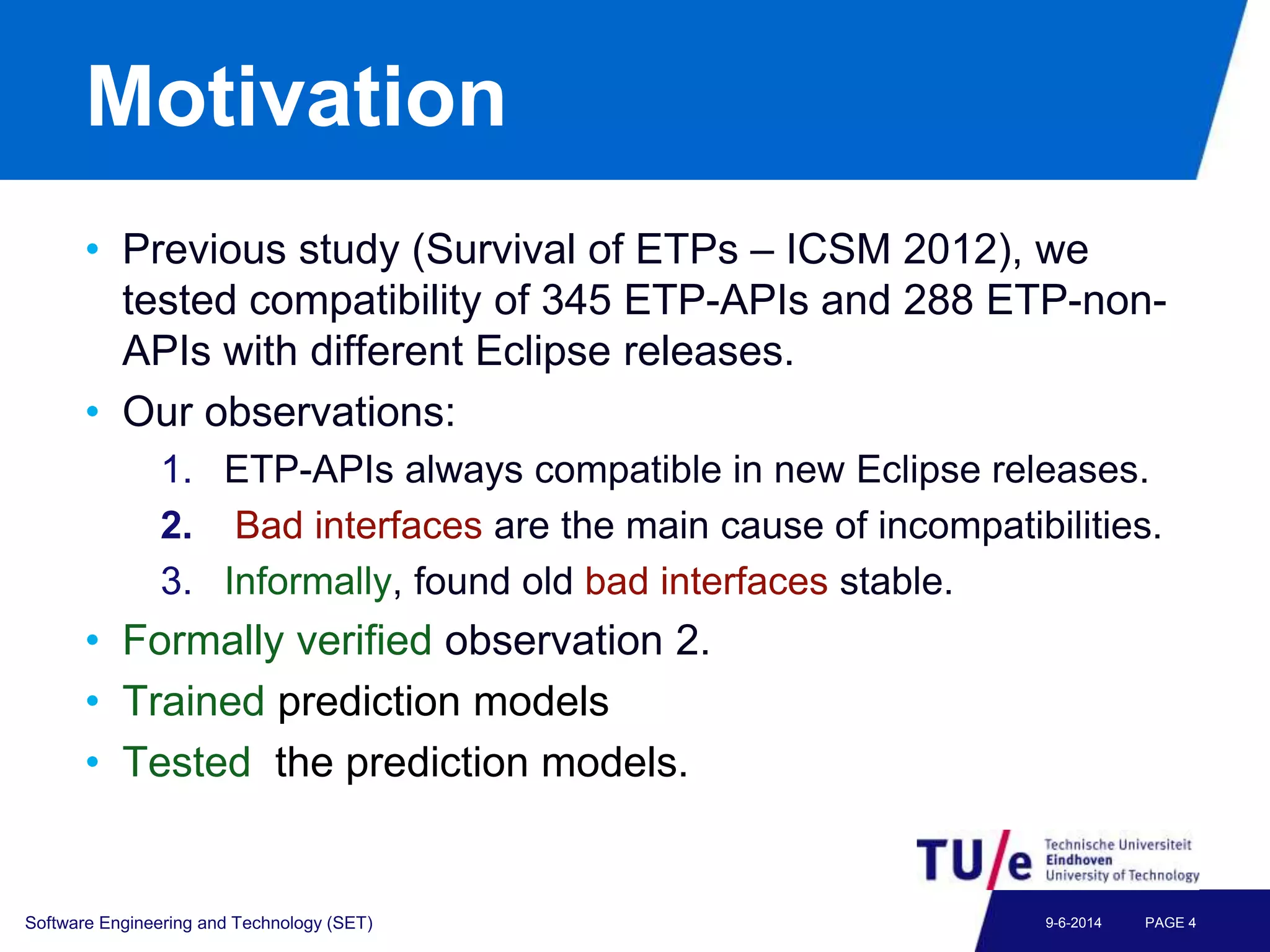
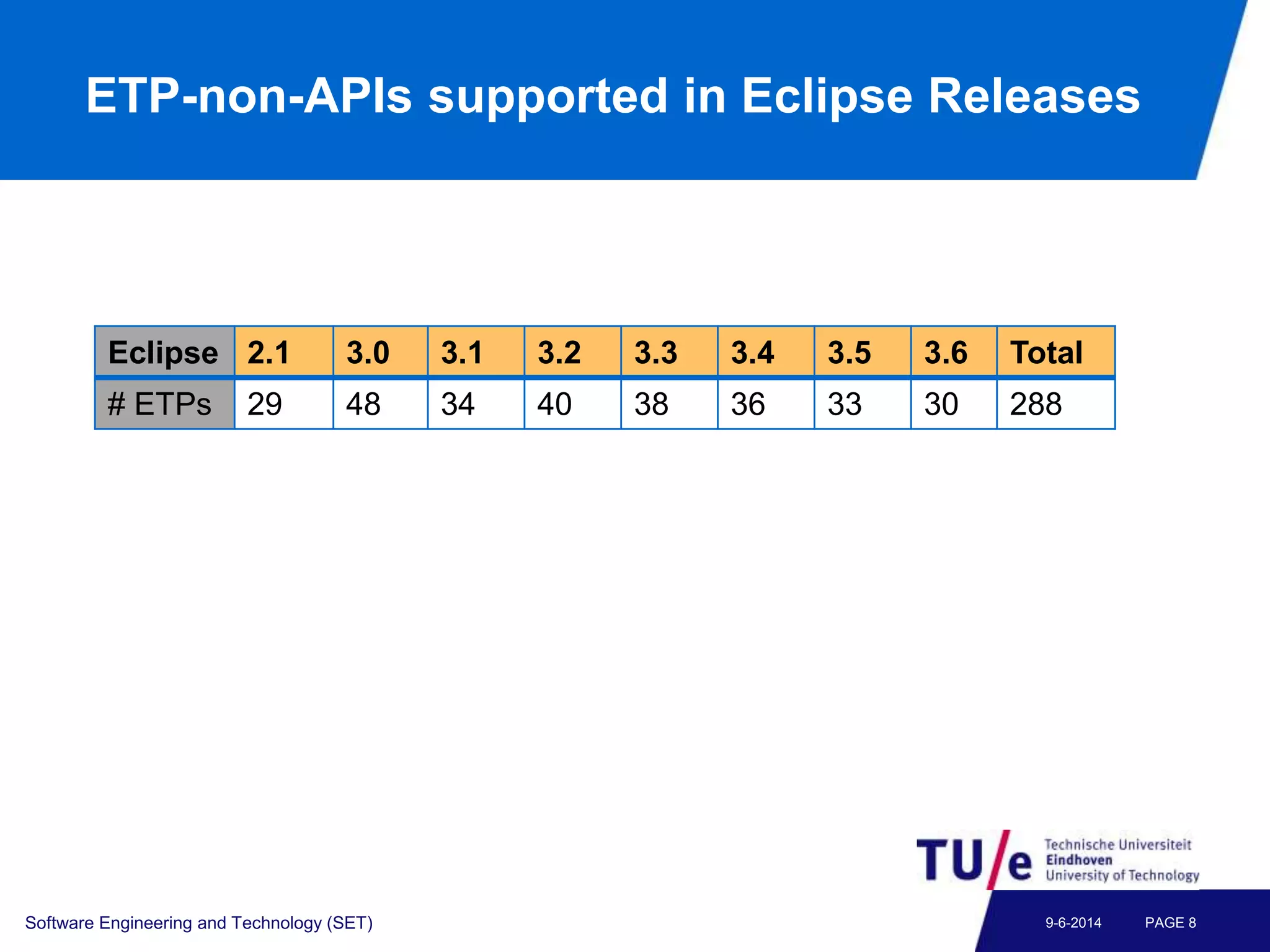
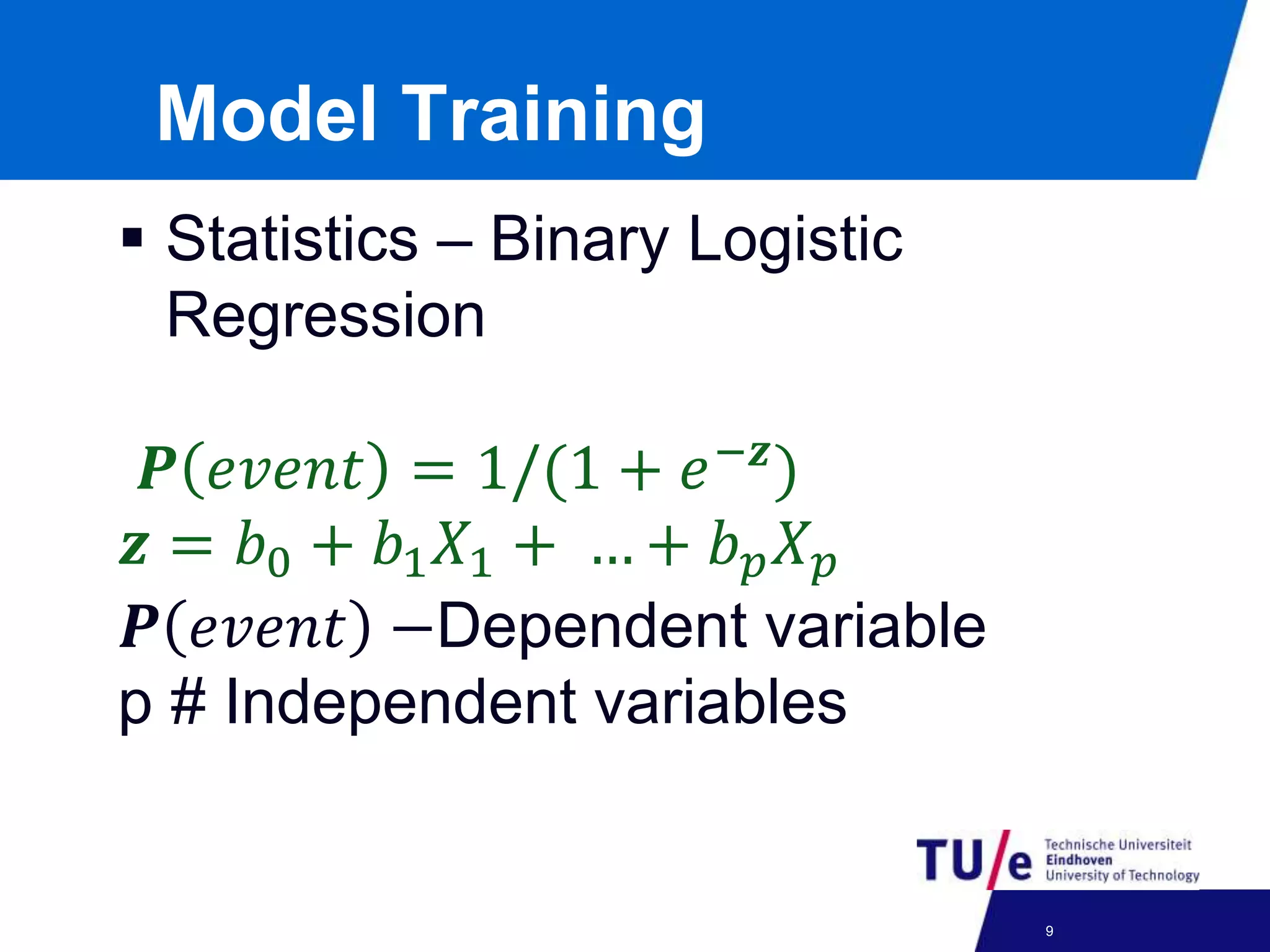
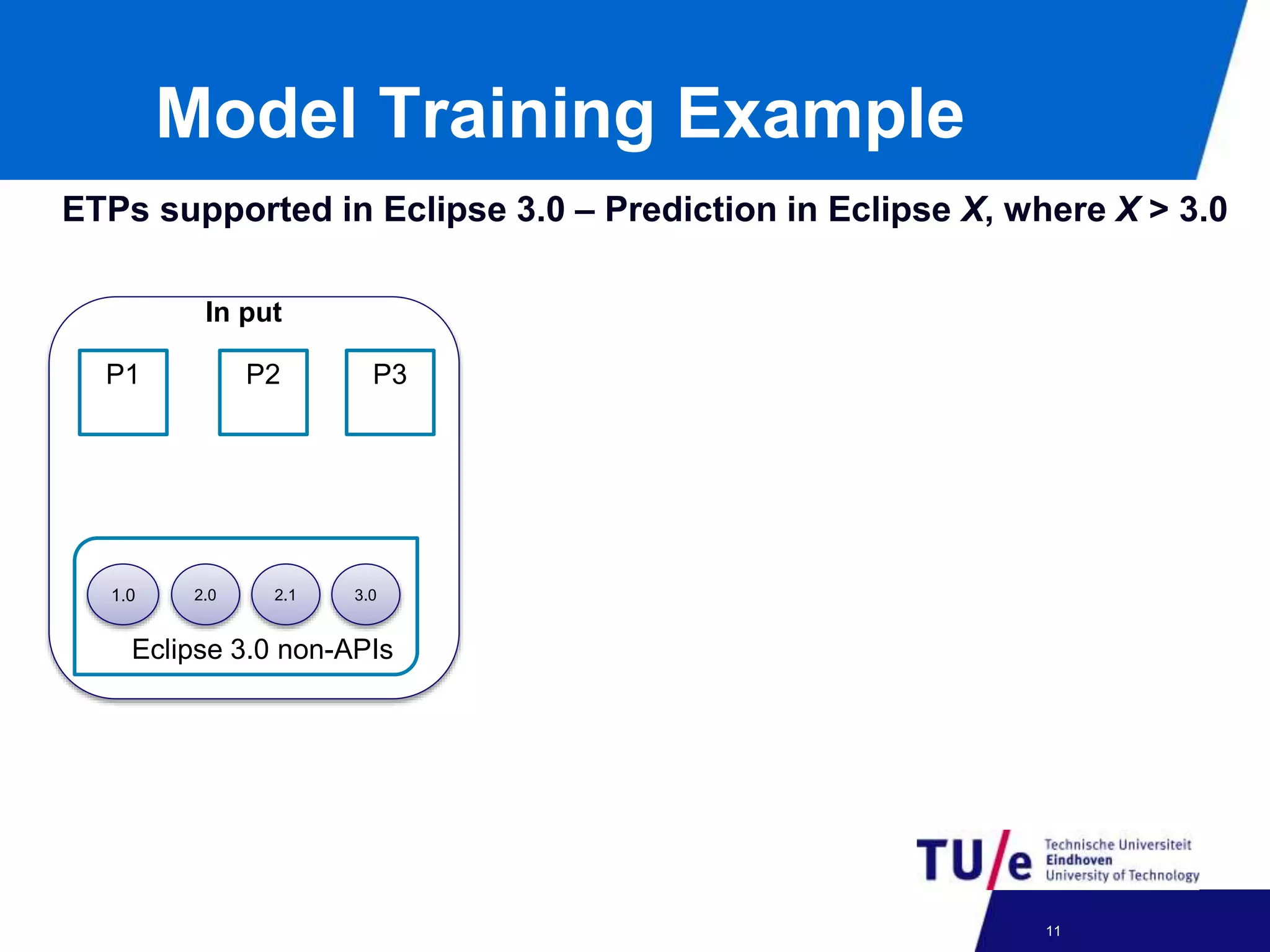
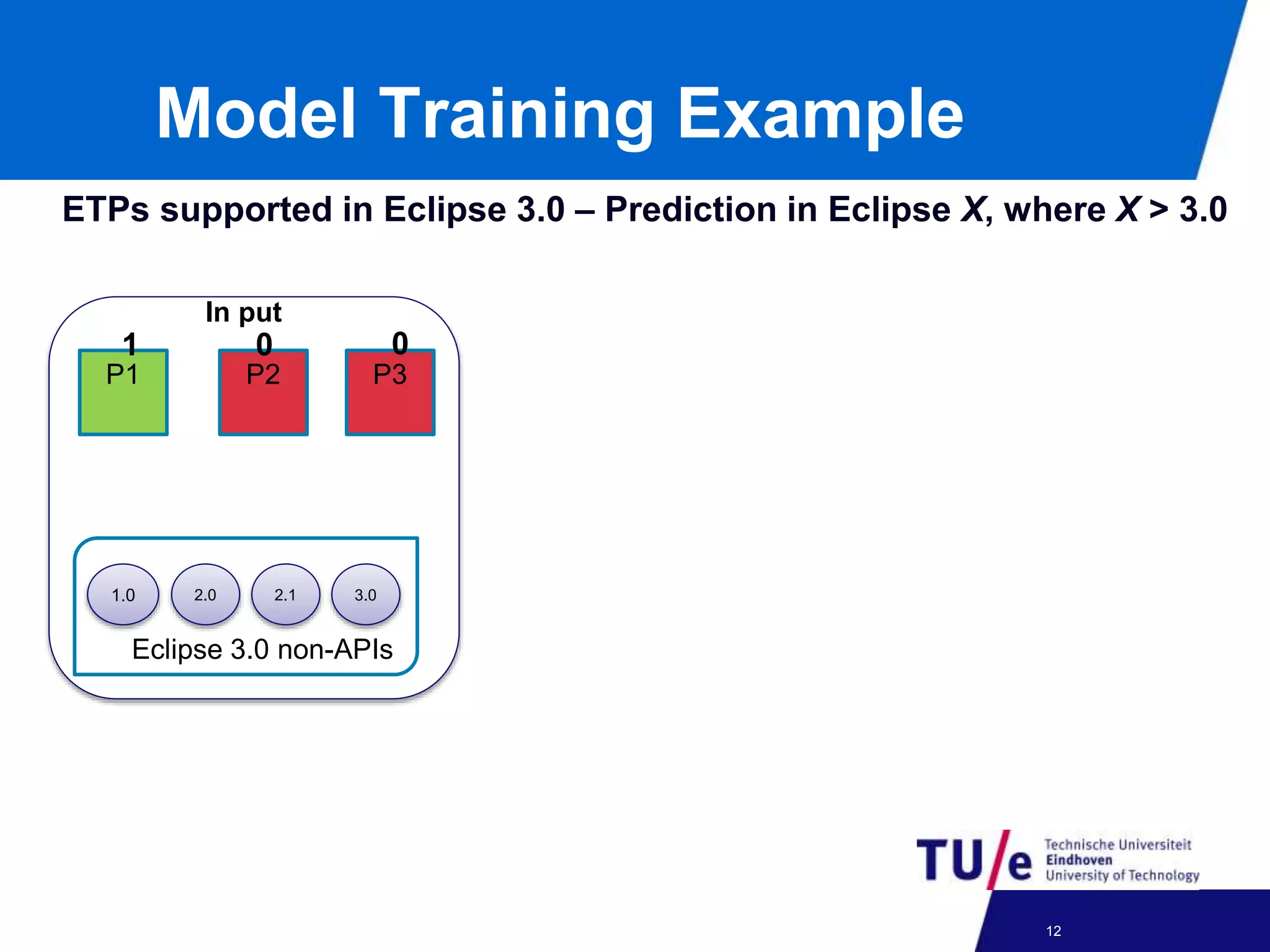
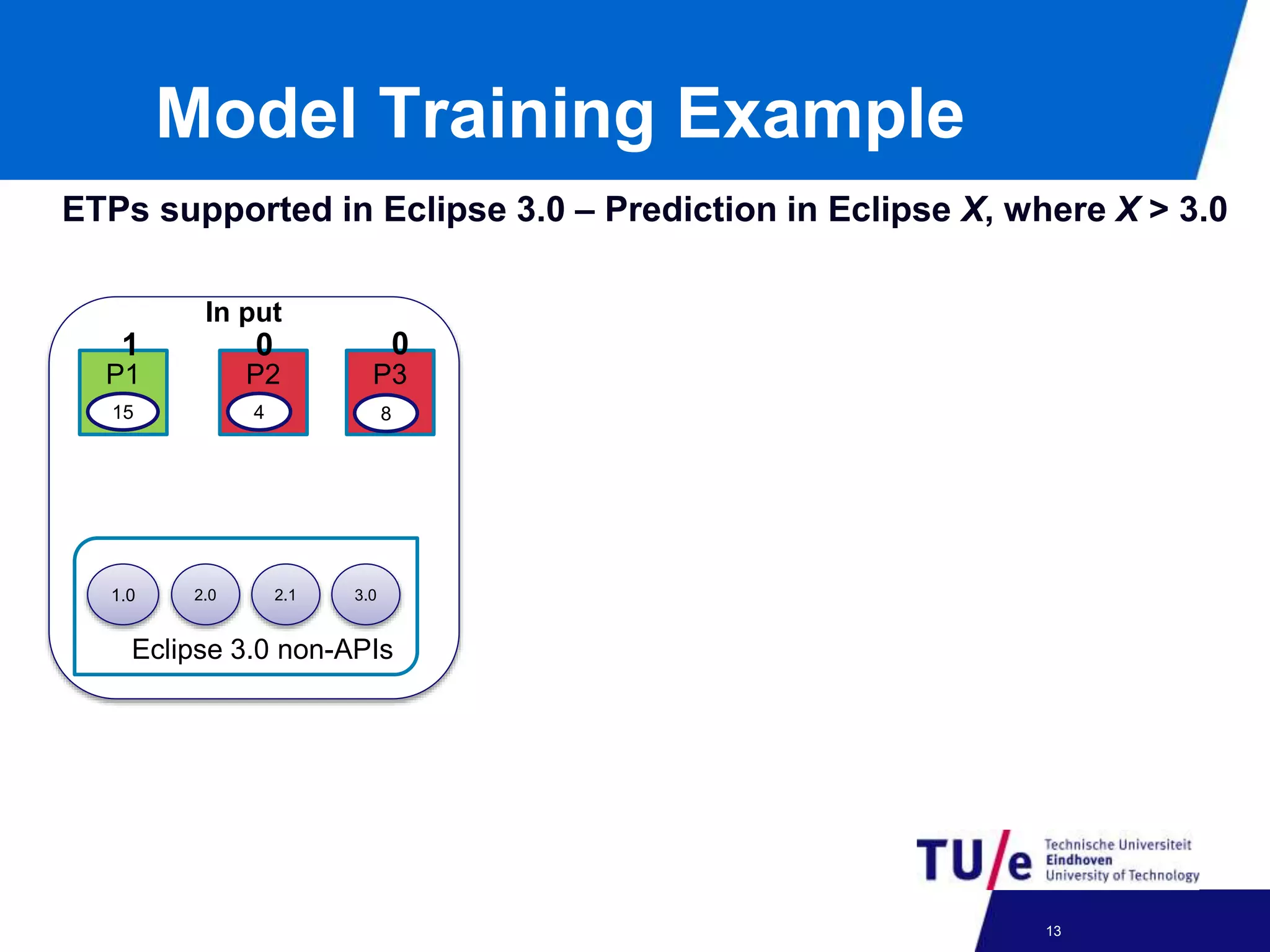
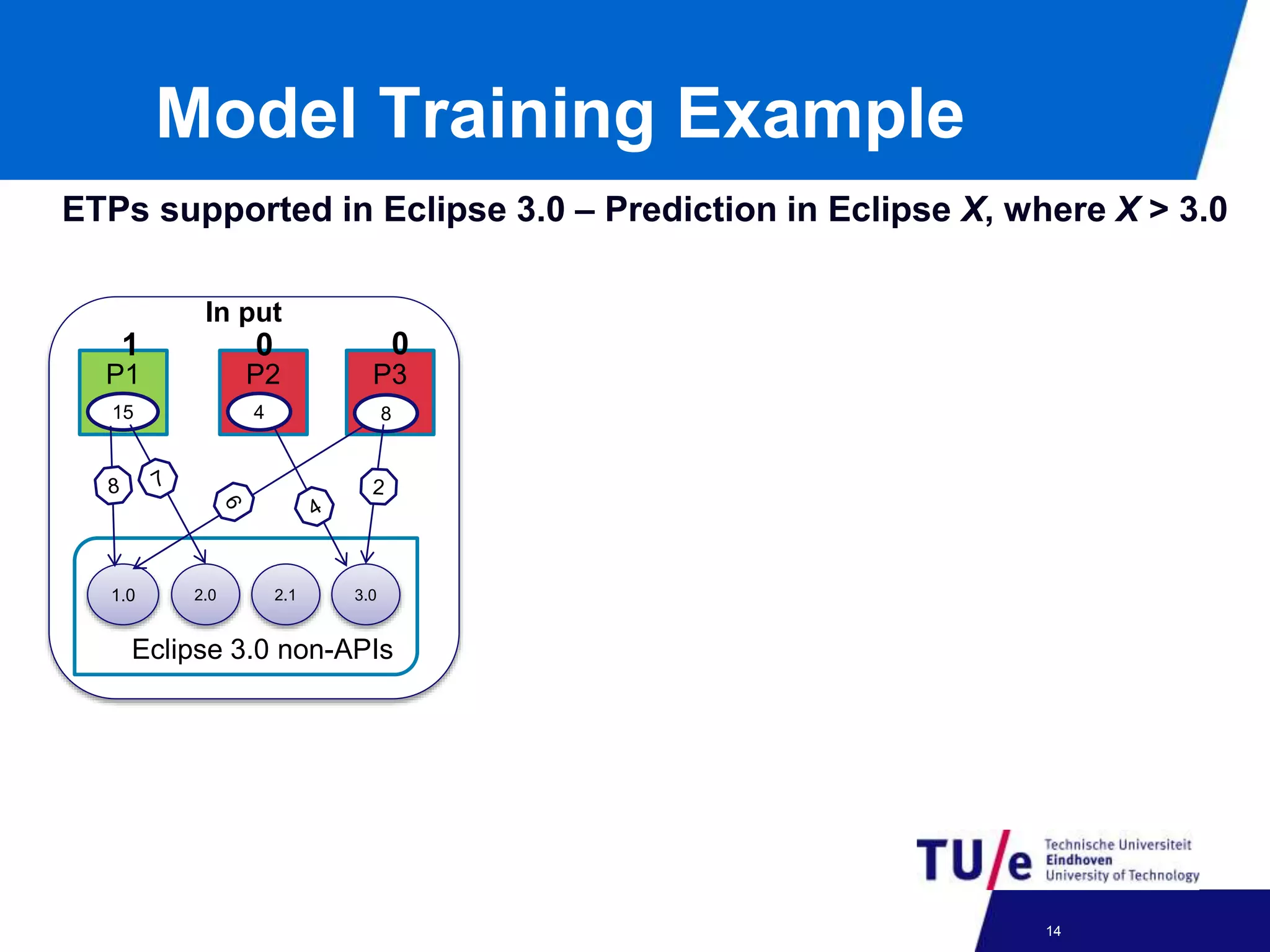
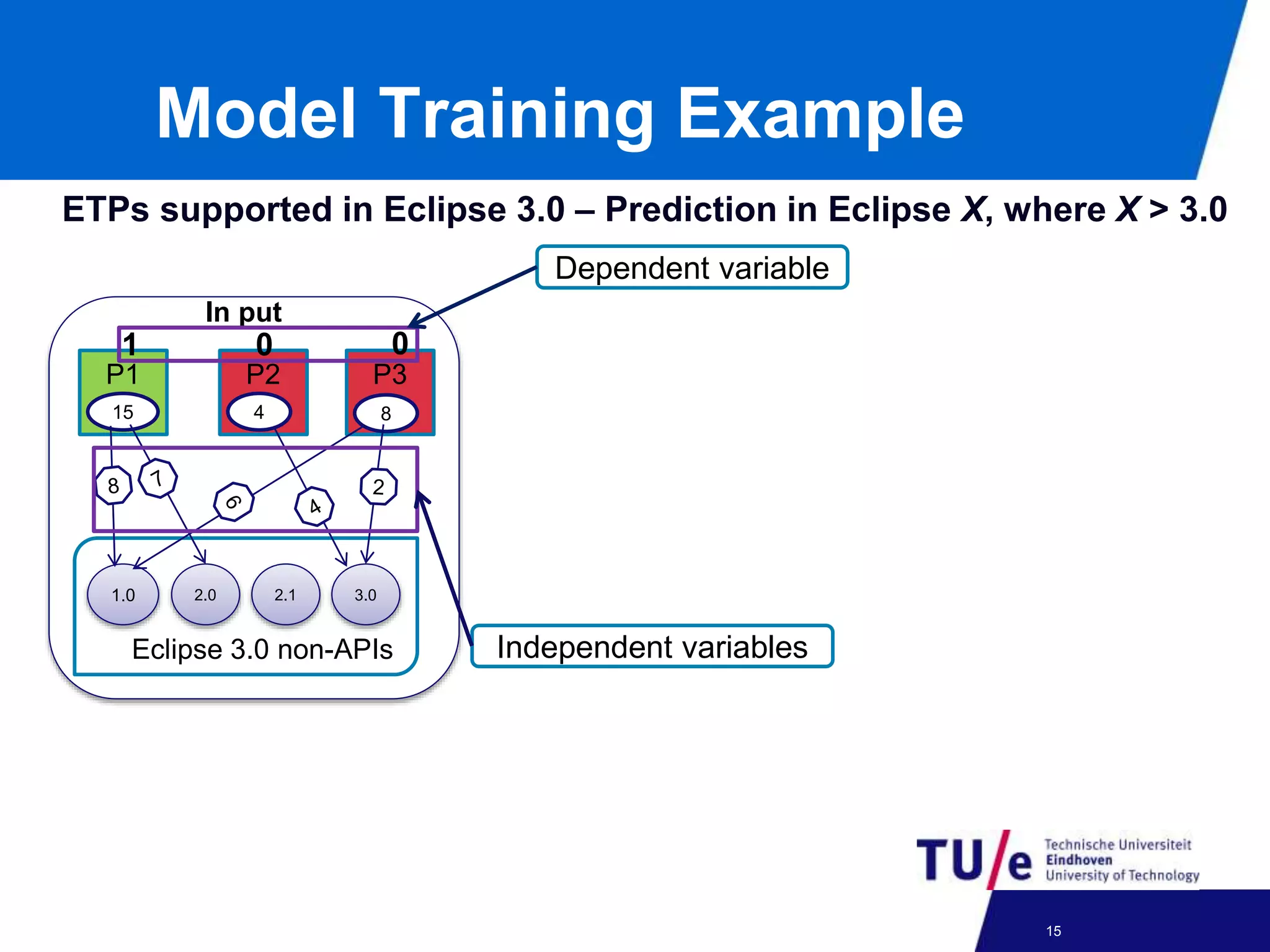
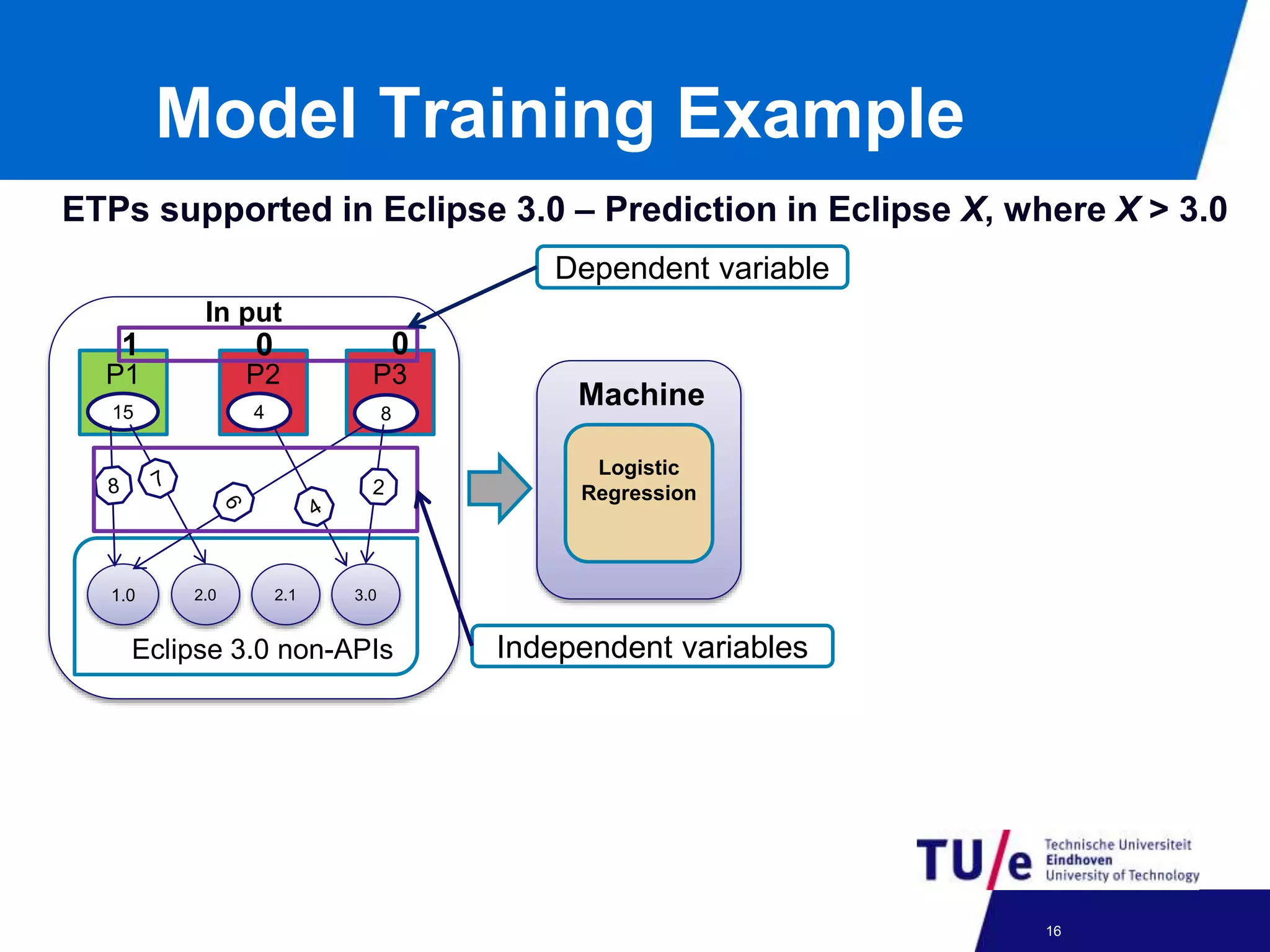
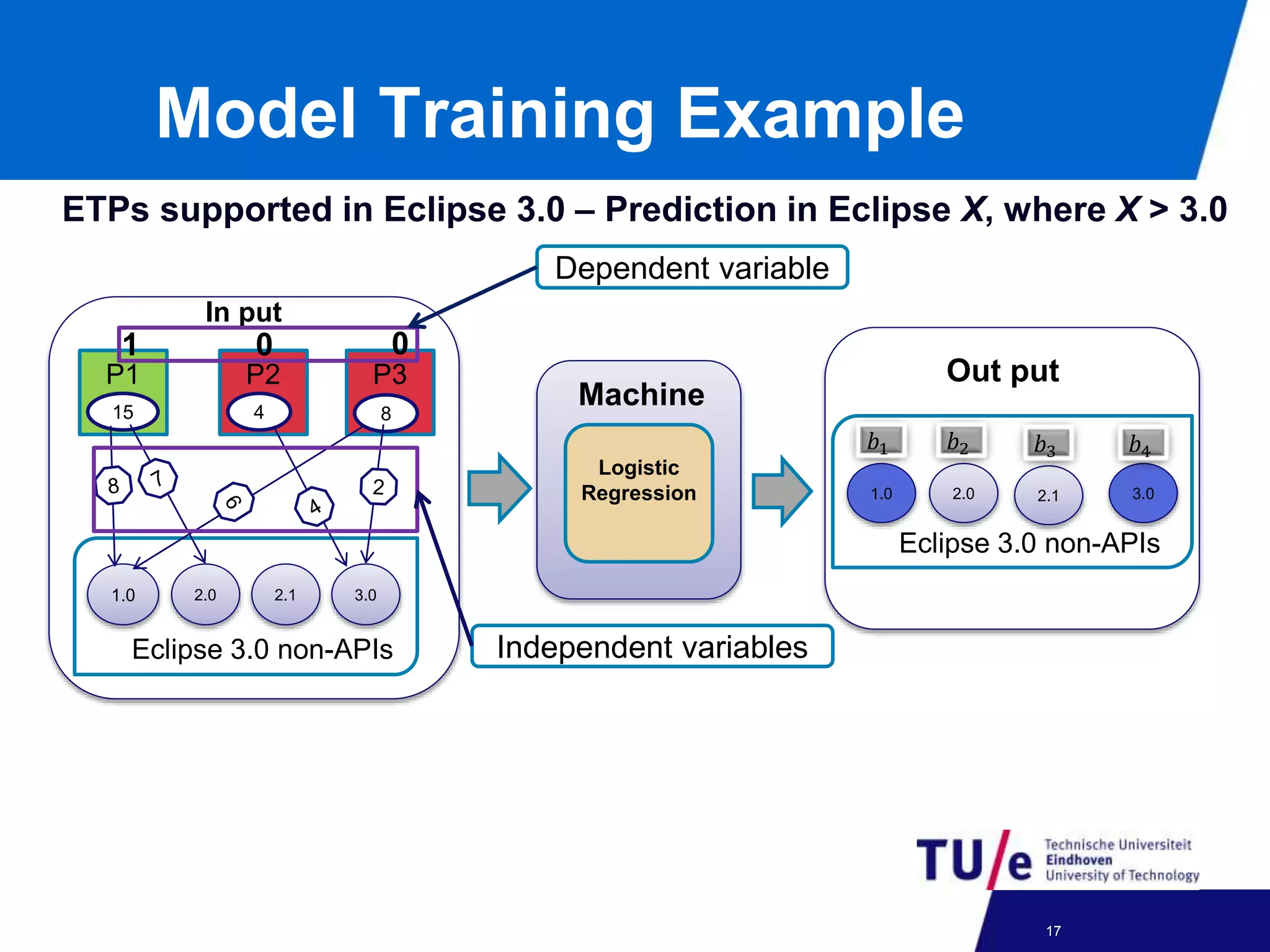
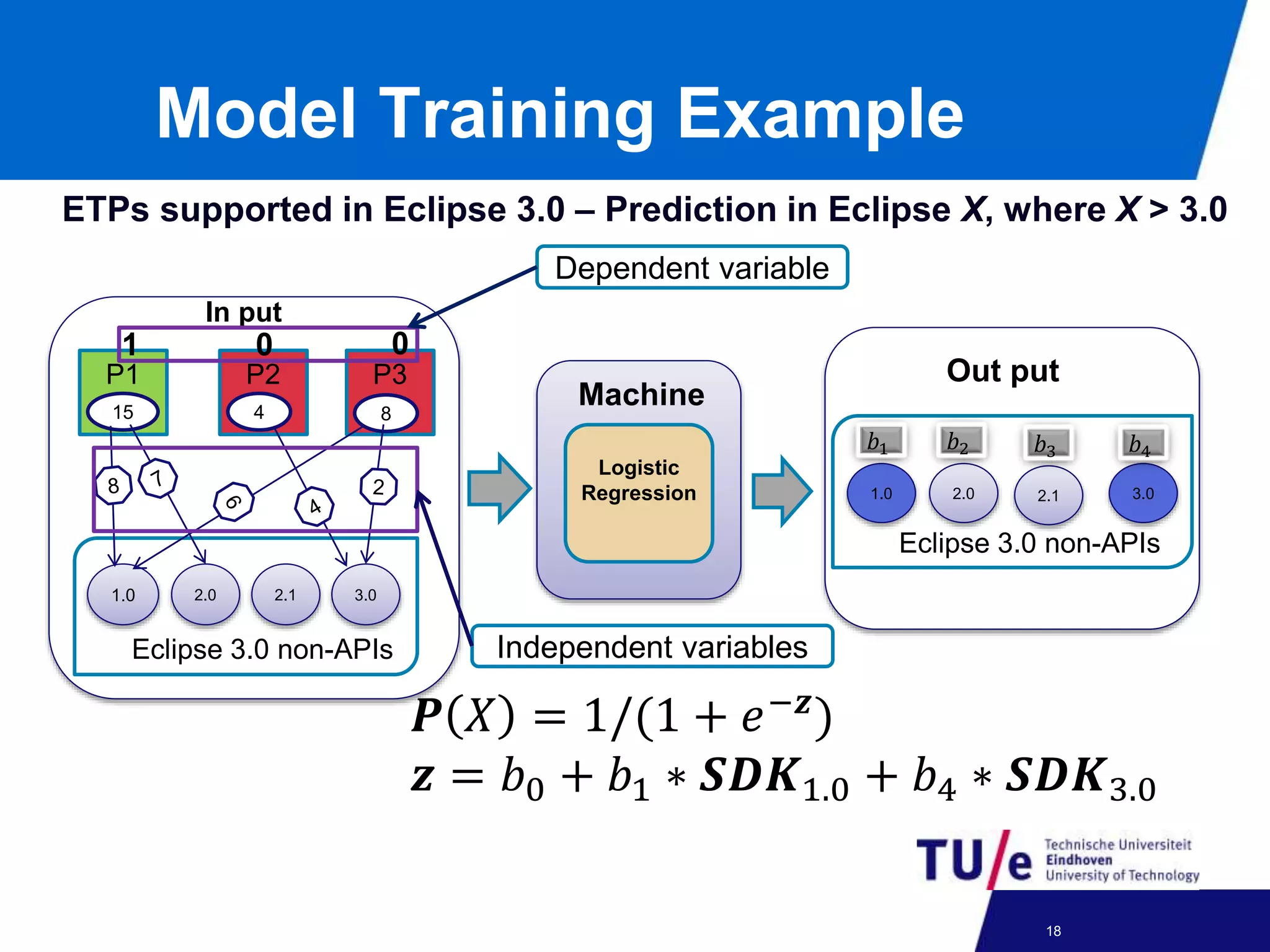
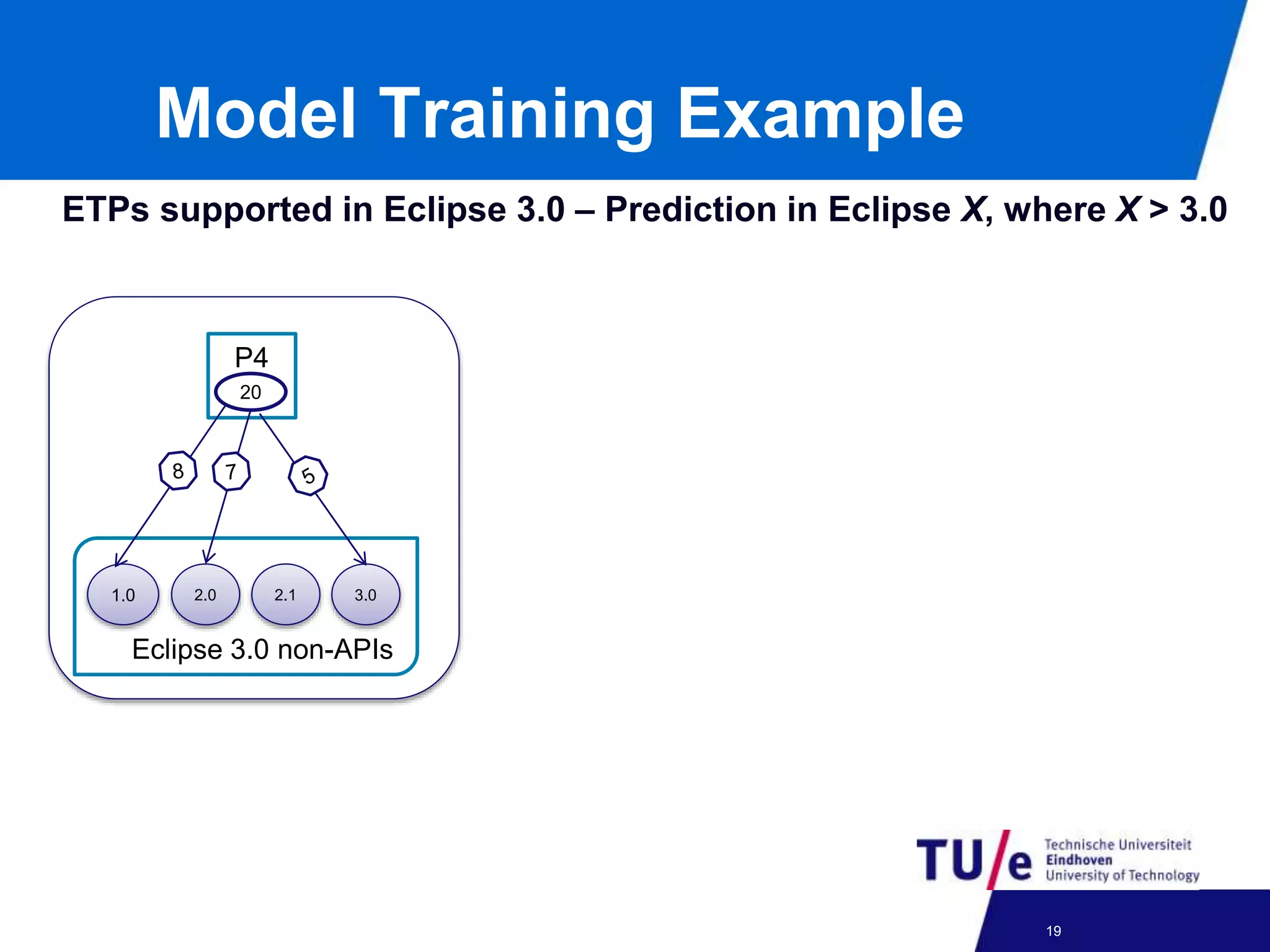
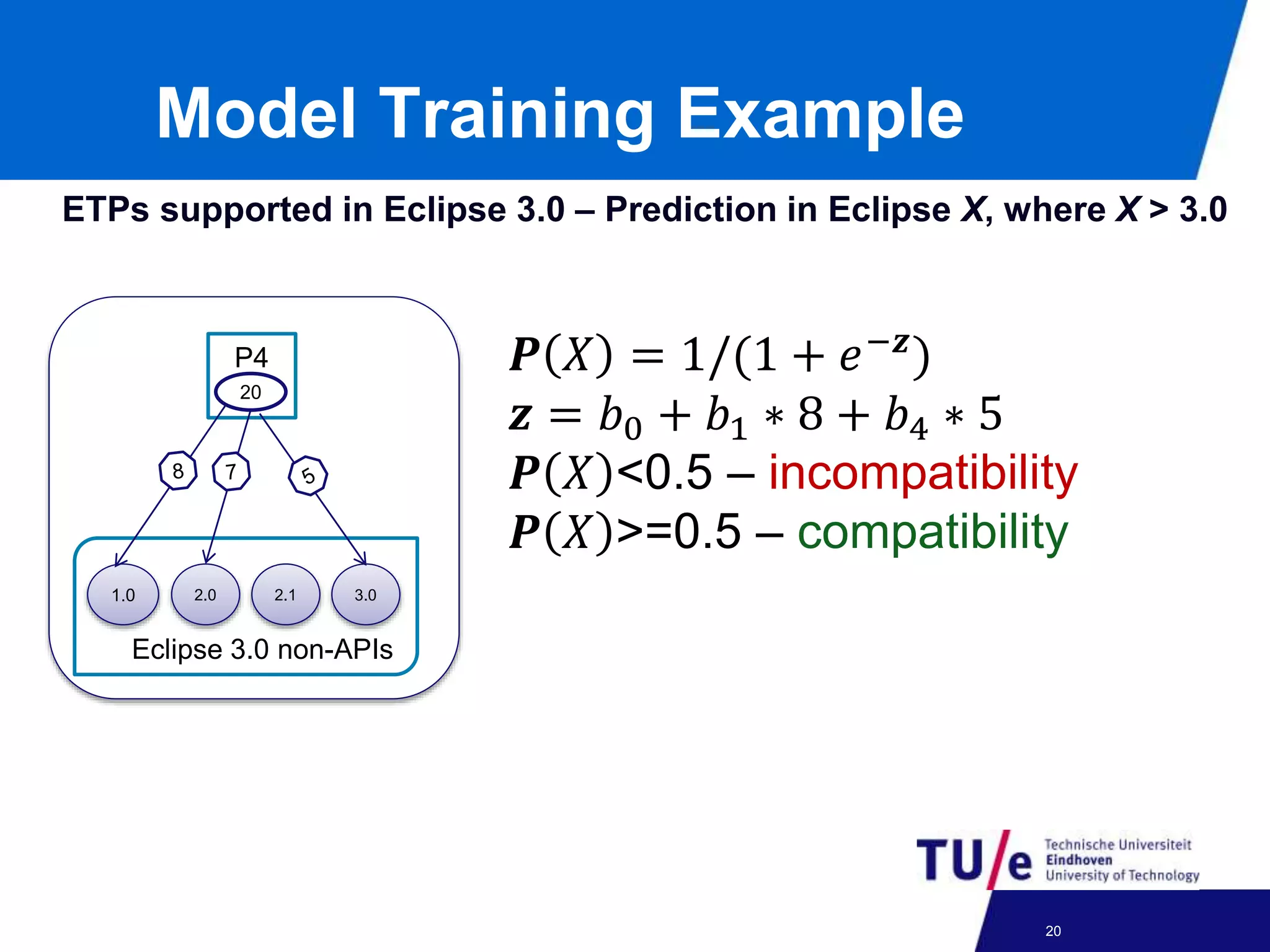
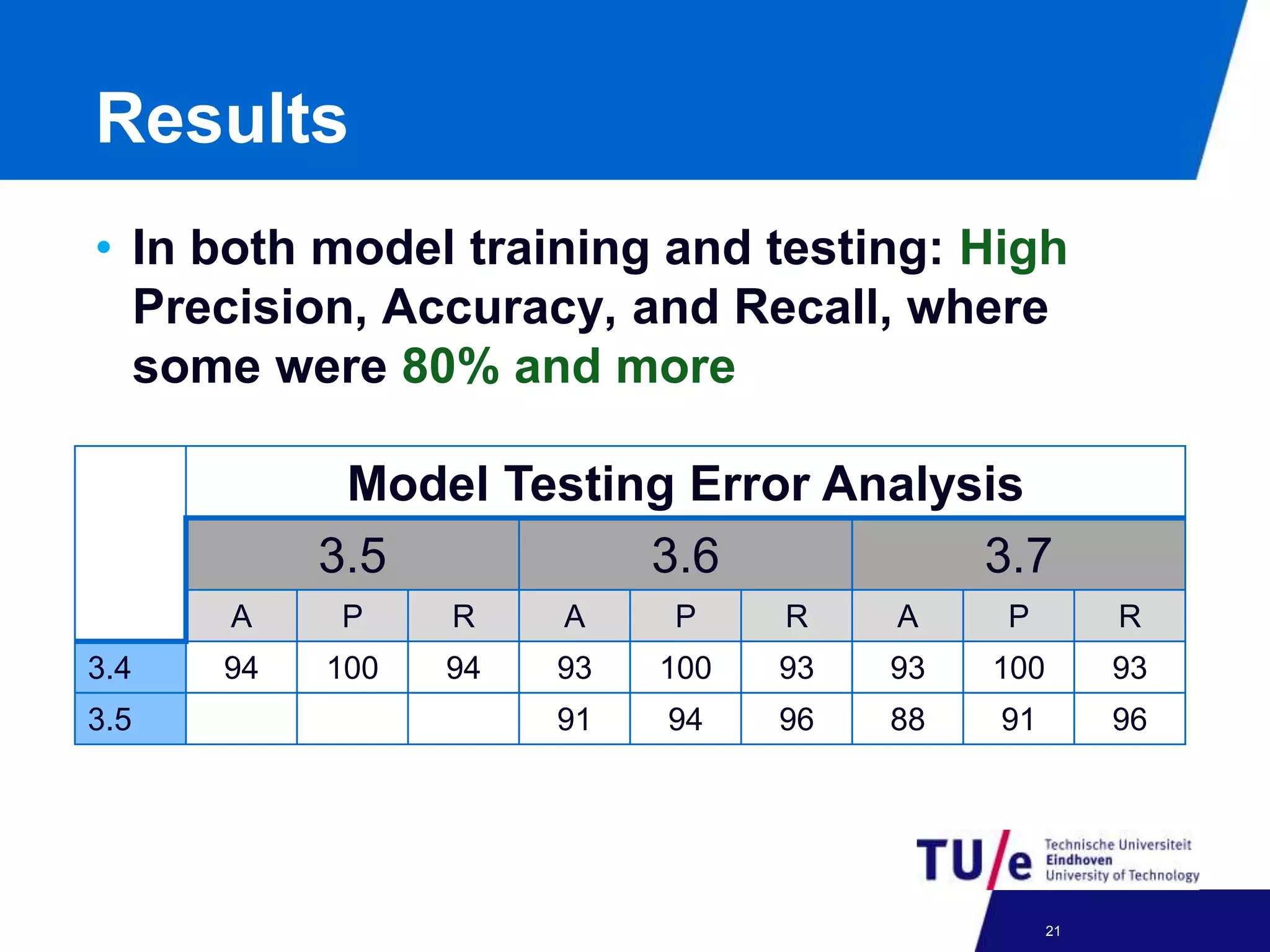
This document discusses a study on predicting the compatibility of Eclipse third-party plugins (ETPs) with new Eclipse releases. The researchers built prediction models using logistic regression based on ETPs' usage of Eclipse APIs versus non-APIs. They trained and tested 36 models and found high accuracy, precision, and recall over 80% in many cases. The models show promise for predicting compatibility and could be developed into a tool to help ETP users and developers.