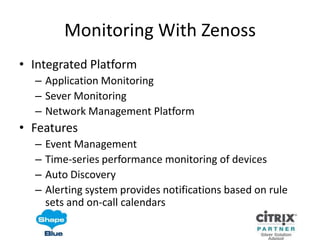
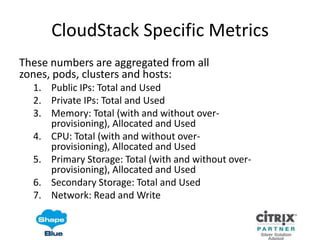
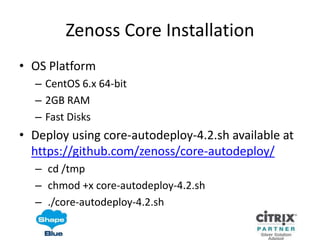
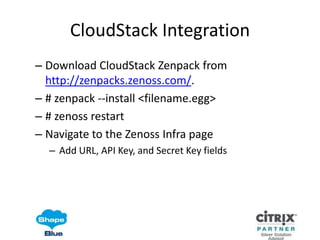
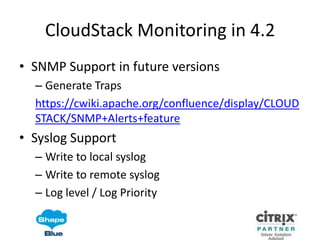
The document outlines the integration of CloudStack monitoring with Zenoss, detailing features such as event management and performance monitoring. It provides specific CloudStack metrics related to IP usage, memory, CPU, and storage, along with threshold monitoring recommendations. Additionally, it includes instructions for installing Zenoss on CentOS and integrating it with CloudStack, along with links for downloading necessary ZenPacks.