clinic app
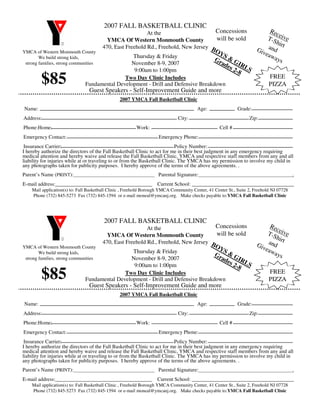
- 1. 2007 FALL BASKETBALL CLINIC Rec Concessions At the T-S eive will be sold YMCA Of Western Monmouth County hirt Giv and 470, East Freehold Rd., Freehold, New Jersey B OY YMCA of Western Monmouth County eaw S Thursday & Friday Gr & G ays We build strong kids, ad es IRLS November 8-9, 2007 strong families, strong communities 2-8 9:00am to 1:00pm $85 FREE Two Day Clinic Includes PIZZA Fundamental Development - Drill and Defensive Breakdown Guest Speakers - Self-Improvement Guide and more 2007 YMCA Fall Basketball Clinic Name: Age: Grade: Address: City: Zip: Phone:Home: Work: Cell # Emergency Contact: Emergency Phone: Insurance Carrier: Policy Number: I hereby authorize the directors of the Fall Basketball Clinic to act for me in their best judgment in any emergency requiring medical attention and hereby waive and release the Fall Basketball Clinic, YMCA and respective staff members from any and all liability for injuries while at or traveling to or from the Basketball Clinic. The YMCA has my permission to involve my child in any photographs taken for publicity purposes. I hereby approve of the terms of the above agreements. . Parent’s Name (PRINT): Parental Signature: . E-mail address:_____________________________________ Current School: _______________________________________ Mail application(s) to: Fall Basketball Clinic , Freehold Borough YMCA Community Center, 41 Center St., Suite 2, Freehold NJ 07728 Phone (732) 845-5273 Fax (732) 845-1594 or e-mail moneal@ymcanj.org. Make checks payable to:YMCA Fall Basketball Clinic 2007 FALL BASKETBALL CLINIC Rec Concessions At the T-S eive will be sold YMCA Of Western Monmouth County hirt Giv and 470, East Freehold Rd., Freehold, New Jersey B OY YMCA of Western Monmouth County eaw S Thursday & Friday Gr & G ays We build strong kids, ad es IRLS November 8-9, 2007 strong families, strong communities 2-8 9:00am to 1:00pm $85 FREE Two Day Clinic Includes PIZZA Fundamental Development - Drill and Defensive Breakdown Guest Speakers - Self-Improvement Guide and more 2007 YMCA Fall Basketball Clinic Name: Age: Grade: Address: City: Zip: Phone:Home: Work: Cell # Emergency Contact: Emergency Phone: Insurance Carrier: Policy Number: I hereby authorize the directors of the Fall Basketball Clinic to act for me in their best judgment in any emergency requiring medical attention and hereby waive and release the Fall Basketball Clinic, YMCA and respective staff members from any and all liability for injuries while at or traveling to or from the Basketball Clinic. The YMCA has my permission to involve my child in any photographs taken for publicity purposes. I hereby approve of the terms of the above agreements. . Parent’s Name (PRINT): Parental Signature: . E-mail address:_____________________________________ Current School: _______________________________________ Mail application(s) to: Fall Basketball Clinic , Freehold Borough YMCA Community Center, 41 Center St., Suite 2, Freehold NJ 07728 Phone (732) 845-5273 Fax (732) 845-1594 or e-mail moneal@ymcanj.org. Make checks payable to:YMCA Fall Basketball Clinic