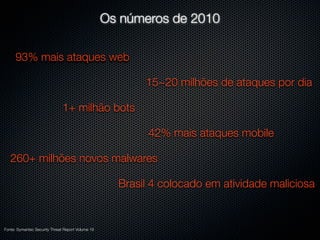
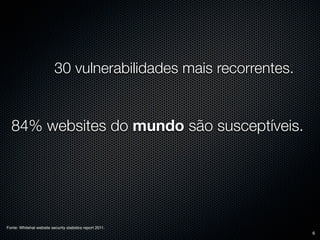
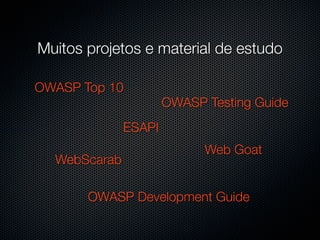
The document discusses web security threats and statistics from 2010, finding a 93% increase in web attacks, 1+ million bots, and 260+ million new malware. It also notes that 84% of websites are susceptible to one of the top 30 vulnerabilities. The document promotes the OWASP organization as helping to defend against these threats through various open source projects, guides, and a discussion group.