Fear, Uncertainty and Doubt
•
0 likes•949 views
Presentation given in collaboration with Laurent Schmid (electric-haze.org) at the Espace Jules Verne of the Maison D\'ailleurs, Yverdon, Switzerland.
Report
Share
Report
Share
Recommended
Botnets - What, How and Why by Utsav Mittal @ OWASP Delhi July, 2014 Monthly ...

Botnets - What, How and Why by Utsav Mittal @ OWASP Delhi July, 2014 Monthly Meeting in Adobe Systems, Noida
AtlSecCon 2016

Here are the slides that I presented at the Atlantic Security Conference this year (2016).
Beveilig je data met windows 10 

Het beveiligen van de productiviteit, samenwerking en enterprise data is van cruciaal belang op het moment dat organisaties transformeren naar een Digital Workplace. De “Anniversary Update” van Windows 10 bevat enorm veel nieuwe functionaliteiten om deze zaken te waarborgen. In combinatie met de Enterprise Mobility + Security (EMS) oplossing van Microsoft zijn bedrijven in staat om identiteiten onder controle te houden en enterprise data te behoeden voor fouten van medewerkers. In deze deep dive sessie breng ik je op de hoogte van nieuwe functionaliteiten, zoals Enterprise Data Protection en Phone Sign-in.
Recommended
Botnets - What, How and Why by Utsav Mittal @ OWASP Delhi July, 2014 Monthly ...

Botnets - What, How and Why by Utsav Mittal @ OWASP Delhi July, 2014 Monthly Meeting in Adobe Systems, Noida
AtlSecCon 2016

Here are the slides that I presented at the Atlantic Security Conference this year (2016).
Beveilig je data met windows 10 

Het beveiligen van de productiviteit, samenwerking en enterprise data is van cruciaal belang op het moment dat organisaties transformeren naar een Digital Workplace. De “Anniversary Update” van Windows 10 bevat enorm veel nieuwe functionaliteiten om deze zaken te waarborgen. In combinatie met de Enterprise Mobility + Security (EMS) oplossing van Microsoft zijn bedrijven in staat om identiteiten onder controle te houden en enterprise data te behoeden voor fouten van medewerkers. In deze deep dive sessie breng ik je op de hoogte van nieuwe functionaliteiten, zoals Enterprise Data Protection en Phone Sign-in.
Global Botnet Detector

In a world where most of the internet traffic is produced by bots, who will defend the innocent from the relentless onslaught of malicious botnet activity?
Everyday, countless incidents of botnet activity occur all around the web; wreaking havoc in the form of mass security breaches, data scraping, fraudulent activity and DDoS attacks. The first step in the defense against botnets is to know when suspicious activity is taking place.
This talk covers: what a botnet is, how they work, and walks through a technique we are developing at Distil Networks to identify the presence of a botnet and a list of responsible participants. The botnet identification method described utilizes a correlation in traffic on a customer’s site, along with user fingerprinting, to first alert when a botnet is present and then identify key players.
Security News Bytes (Aug Sept 2017)

This is the Security News for the month Aug-Sep 2017 delivered at Null Pune chapter
IoT security is a nightmare. But what is the real risk?

IoT security is a nightmare. But what is the real risk?
Weaponization of IoT

We constantly see how IoT security is bypassed and abused, creating the biggest Botnet in history or the biggest DDoS attack ever recorded. But what happens when we used common devices like routers as a weapon? and/or use IoT development platforms such as Raspberry Pi, Arduino, ESP8266 and other to create cyber-weapons? Let find out!
やってみよう!0円セキュリティ

2017年05月19日 のセキュリティ共有勉強会の発表用スライド。
大抵何の専門でも「あれこれを簡単にできない?」とか言われることはあるかと思いますが、今回はそれに答えてみました。
「なるべく安くセキュリティ対策できない?」というやつです。
金がないなら金がないで、やりようはあります。
有料のツールを購入した方がベターですが、無料&知識低めでもできないわけでではありません。
Governments As Malware Authors - Mikko Hypponen at Black Hat 2014

Governments As Malware Authors - The Next Generation
Talk delivered by Mikko Hypponen at Black Hat USA 2014
Bots and Botnet

Bots and Botnet are the biggest threat of internet. Various attacks have been launched using this.
Ransomware the clock is ticking

How can we avoid\prevent a ransomware attack Please check https://firewall.firm.in/preventing-ransomware/ , Use Sophos Antivirus & Firewall
Sophos Central Platform Manage all your Sophos Antivirus & Firewall from a single, cloud-based console.
Synchronized Security
Next-gen security with real-time intelligence sharing between your endpoints and firewall.
“No other company is close to delivering this type of communication between endpoint and network security products.” Please contact us on sales@itmonteur.net
Cryto Party at CCU

Cryptopraty presentation at Columbia Central University. A guide to privacy in electronic communications.
Bsides angler-evolution talk

These are the slides that I presented on the evolution of the Angler Exploit Kit at BSides Austin 2016
Snooping on Cellular Gateways and Their Critical Role in ICS

To keep up with the growing demand of always-on and available-anywhere connectivity, the use of cellular, in comparison to its wireless mobile connectivity counterpart in the electromagnetic spectrum, is rapidly expanding. My research in the IoT space led me down the path of discovering a variety of vulnerabilities related to cellular devices manufactured by Sierra Wireless and many others. Proper disclosures have occurred; however, many manufactures have been slow to respond. This led into examining numerous publicly disclosed vulnerabilities that were considered "low-hanging-fruit" against cellular devices and other cellular-based network modems that are often deployed as out of band management interfaces. The research expanded through the details provided in configuration templates available by each device including the following:
- Wireless Network Information
- IPSec Tunnel Authentication Details
- Connected devices and services
Focusing on an obfuscated series of examples to protect the organizations, people, and companies identified; this presentation focuses on the services and systems information of the following, commonly deployed cellular-connected devices to provide an in-depth look at what is easily possible:
- Emergency Response systems
- Resource collection systems
- Transportation Safety
- Out of band management
Learn Ethical Hacking With Kali Linux | Ethical Hacking Tutorial | Kali Linux...

( ** Edureka Online Training: https://www.edureka.co/cybersecurity-certification-training ** )
This Edureka "Ethical Hacking using Kali Linux" video will give you an introduction to Ethical Hacking and Kali Linux. This video will give you an exhaustive video on the fundamentals of Kali Linux and teach how to use the operating system along with its various tools. Below are the topics in this video:
What is ethical hacking?
What is Kali Linux?
Why use Kali Linux?
Command Line Essentials
Proxychains
Macchanger
Wireless Penetration Testing
Cracking WPA2 using Aircrack-ng & Crunch
Instagram: https://www.instagram.com/edureka_lea...
Facebook: https://www.facebook.com/edurekaIN/
Twitter: https://twitter.com/edurekain
LinkedIn: https://www.linkedin.com/company/edureka
Hacking 

Hacking , Types of Hackers, Purpose of Hacking, Motives Evil and to destroy and many more. Tools used by hackers in hacking the systems. Conferences held for hackers to know about recent activities and new ways.
More Related Content
What's hot
Global Botnet Detector

In a world where most of the internet traffic is produced by bots, who will defend the innocent from the relentless onslaught of malicious botnet activity?
Everyday, countless incidents of botnet activity occur all around the web; wreaking havoc in the form of mass security breaches, data scraping, fraudulent activity and DDoS attacks. The first step in the defense against botnets is to know when suspicious activity is taking place.
This talk covers: what a botnet is, how they work, and walks through a technique we are developing at Distil Networks to identify the presence of a botnet and a list of responsible participants. The botnet identification method described utilizes a correlation in traffic on a customer’s site, along with user fingerprinting, to first alert when a botnet is present and then identify key players.
Security News Bytes (Aug Sept 2017)

This is the Security News for the month Aug-Sep 2017 delivered at Null Pune chapter
IoT security is a nightmare. But what is the real risk?

IoT security is a nightmare. But what is the real risk?
Weaponization of IoT

We constantly see how IoT security is bypassed and abused, creating the biggest Botnet in history or the biggest DDoS attack ever recorded. But what happens when we used common devices like routers as a weapon? and/or use IoT development platforms such as Raspberry Pi, Arduino, ESP8266 and other to create cyber-weapons? Let find out!
やってみよう!0円セキュリティ

2017年05月19日 のセキュリティ共有勉強会の発表用スライド。
大抵何の専門でも「あれこれを簡単にできない?」とか言われることはあるかと思いますが、今回はそれに答えてみました。
「なるべく安くセキュリティ対策できない?」というやつです。
金がないなら金がないで、やりようはあります。
有料のツールを購入した方がベターですが、無料&知識低めでもできないわけでではありません。
Governments As Malware Authors - Mikko Hypponen at Black Hat 2014

Governments As Malware Authors - The Next Generation
Talk delivered by Mikko Hypponen at Black Hat USA 2014
Bots and Botnet

Bots and Botnet are the biggest threat of internet. Various attacks have been launched using this.
Ransomware the clock is ticking

How can we avoid\prevent a ransomware attack Please check https://firewall.firm.in/preventing-ransomware/ , Use Sophos Antivirus & Firewall
Sophos Central Platform Manage all your Sophos Antivirus & Firewall from a single, cloud-based console.
Synchronized Security
Next-gen security with real-time intelligence sharing between your endpoints and firewall.
“No other company is close to delivering this type of communication between endpoint and network security products.” Please contact us on sales@itmonteur.net
Cryto Party at CCU

Cryptopraty presentation at Columbia Central University. A guide to privacy in electronic communications.
Bsides angler-evolution talk

These are the slides that I presented on the evolution of the Angler Exploit Kit at BSides Austin 2016
Snooping on Cellular Gateways and Their Critical Role in ICS

To keep up with the growing demand of always-on and available-anywhere connectivity, the use of cellular, in comparison to its wireless mobile connectivity counterpart in the electromagnetic spectrum, is rapidly expanding. My research in the IoT space led me down the path of discovering a variety of vulnerabilities related to cellular devices manufactured by Sierra Wireless and many others. Proper disclosures have occurred; however, many manufactures have been slow to respond. This led into examining numerous publicly disclosed vulnerabilities that were considered "low-hanging-fruit" against cellular devices and other cellular-based network modems that are often deployed as out of band management interfaces. The research expanded through the details provided in configuration templates available by each device including the following:
- Wireless Network Information
- IPSec Tunnel Authentication Details
- Connected devices and services
Focusing on an obfuscated series of examples to protect the organizations, people, and companies identified; this presentation focuses on the services and systems information of the following, commonly deployed cellular-connected devices to provide an in-depth look at what is easily possible:
- Emergency Response systems
- Resource collection systems
- Transportation Safety
- Out of band management
Learn Ethical Hacking With Kali Linux | Ethical Hacking Tutorial | Kali Linux...

( ** Edureka Online Training: https://www.edureka.co/cybersecurity-certification-training ** )
This Edureka "Ethical Hacking using Kali Linux" video will give you an introduction to Ethical Hacking and Kali Linux. This video will give you an exhaustive video on the fundamentals of Kali Linux and teach how to use the operating system along with its various tools. Below are the topics in this video:
What is ethical hacking?
What is Kali Linux?
Why use Kali Linux?
Command Line Essentials
Proxychains
Macchanger
Wireless Penetration Testing
Cracking WPA2 using Aircrack-ng & Crunch
Instagram: https://www.instagram.com/edureka_lea...
Facebook: https://www.facebook.com/edurekaIN/
Twitter: https://twitter.com/edurekain
LinkedIn: https://www.linkedin.com/company/edureka
Hacking 

Hacking , Types of Hackers, Purpose of Hacking, Motives Evil and to destroy and many more. Tools used by hackers in hacking the systems. Conferences held for hackers to know about recent activities and new ways.
What's hot (20)
IoT security is a nightmare. But what is the real risk?

IoT security is a nightmare. But what is the real risk?
Governments As Malware Authors - Mikko Hypponen at Black Hat 2014

Governments As Malware Authors - Mikko Hypponen at Black Hat 2014
Snooping on Cellular Gateways and Their Critical Role in ICS

Snooping on Cellular Gateways and Their Critical Role in ICS
Learn Ethical Hacking With Kali Linux | Ethical Hacking Tutorial | Kali Linux...

Learn Ethical Hacking With Kali Linux | Ethical Hacking Tutorial | Kali Linux...
Viewers also liked
Viewers also liked (8)
Fear, uncertainty, doubt. public perception versus radiation protection scien...

Fear, uncertainty, doubt. public perception versus radiation protection scien...
Navy asbestos containing material (acm) Westphalen

Navy asbestos containing material (acm) Westphalen
Endurance, Courage and Care: The 1942 Kokoda Track Campaign of Captain Alan W...

Endurance, Courage and Care: The 1942 Kokoda Track Campaign of Captain Alan W...
Pilot selection anthropometry a comparison with measures taken by a single a...

Pilot selection anthropometry a comparison with measures taken by a single a...
The Loss of HMAS SYDNEY 2: Medical Aspects- Westphalen

The Loss of HMAS SYDNEY 2: Medical Aspects- Westphalen
Recognising early deteriorating signs a project at kapooka health centre pocius

Recognising early deteriorating signs a project at kapooka health centre pocius
Similar to Fear, Uncertainty and Doubt
Cyber espionage - Tinker, taylor, soldier, spy

A look at the methodology and techniques or hackers, cyber criminals and state sponsored attackers. Explores the kill chain, Geo political instability and the dark web.
Sergey Gordeychik - How to hack a telecom and stay alive

International Security Conference "ZeroNights 2011" - http://www.zeronights.org/
How to hack a telecom and stay alive

How to hack a telecom and stay alive
Speaker: Sergey Gordeychik
Penetration testing of telecommunication companies' networks is one of the most complicated and interesting tasks of this kind. Millions of IPs, thousands of nodes, hundreds of Web servers and only one spare month. What challenges are waiting for an auditor during the telecom network testing? What to pay attention on? How to use the working time more effectively? Why is the subscriber more dangerous than hacker? Why is contractor more dangerous than subscriber? How to connect vulnerability with financial losses? Sergey Gordeychik will tell about it and the most significant and funny cases of penetration testing of telecommunication networks in his report.
Malware cryptomining uploadv3

Guest lecture in Universitat Autonoma Barcelona about malware, cryptomalware and other threat
IoT Security, Mirai Revisited

This talk revisits the 2016 Mirai attack which targeted IoT devices including IP cameras, WiFi-connected refrigerators, home routers, and more. The resulting botnet was used to attack Dyn’s DNS platform, which affected many websites including Twitter, SoundCloud, Airbnb, and Spotify.
You will learn and discuss the answers to these questions and more:
• What is the current state of Mirai and Mirai variants?
• What Distributed Denial of Service (DDoS) defenses do you have in place?
• How can you prepare to detect and defend against them botnet malware?
• What is recommended in the September 2018 NISTIR Draft,
Considerations for Managing Internet of Things (IoT) Cybersecurity and Privacy Risks.
New Botnets Trends and Threats (BH Europe 2007)

The last years have seen the growth of botnets and its transformation into a highly profitable business. Most of the botnets seen until now have used the same basic concepts. This presentation intends to show what are the major challenges faced by botnet authors and what they might try in the future to solve them.
The presentation will pass through some interesting solutions for botnet design challenges. A layered and extensible approach for Bots will be presented, showing that solutions from exploit construction (like metasploit), P2P networks (Gnutella and Skype), authentication (digital signatures) and covert channels research fields can be used to make botnets more reliable, extensible and hard to put down.
DEF CON 27 - MASARAH PAQUET CLOUSTON and OLIVER BILODEAU - the industry of so...

DEF CON 27 - MASARAH PAQUET CLOUSTON and OLIVER BILODEAU - the industry of social media manipulation driven by malware
Introduction to Malware Detection and Reverse Engineering

Beginner level presentation on Malware Identification as part of the Malware Reverse Engineering course. Learn what malware is, how it functions, how it can be detected, identified and isolated for reverse engineering. For more information about malware detection and removal visit https://www.intertel.co.za
Automation Attacks At Scale

Automation attacks are currently plaguing organizations in industries ranging from financial to retail, to gaming & entertainment. These attacks exploit stolen credential leaks, black market & custom attack toolkits, and massively scalable infrastructure to launch widely distributed attacks that are extremely difficult to detect, let alone attribute. In this presentation we will inform the audience of the scale of this problem, discuss a detection methodology to counter these attacks, and walk through 3 real-world examples of how attackers created and monetized the distributed infrastructure they require to launch these attacks.
Ethical hacking (legal)

A complete description about hacking and some internal attacks..
just shows gaining access.
Private Date and PRYING Eyes - Talking Cybersecurity at After Work Network

Private Date and PRYING Eyes - Talking Cybersecurity at After Work NetworkITP - Information Technology Professionals
Without even knowing it, you could be offering very private information to strangers every single day.
In this presentation, we will take a look at the history of security to vocabulary to modern day examples of data breaches.
Here's some of the vocabulary that we'll take a look at:
- Rootkit
- Trojan
- Ransomeware
- BOTNET
- DDoSSimilar to Fear, Uncertainty and Doubt (20)
How to hack a telecommunication company and stay alive. Sergey Gordeychik

How to hack a telecommunication company and stay alive. Sergey Gordeychik
Sergey Gordeychik - How to hack a telecom and stay alive

Sergey Gordeychik - How to hack a telecom and stay alive
DEF CON 27 - MASARAH PAQUET CLOUSTON and OLIVER BILODEAU - the industry of so...

DEF CON 27 - MASARAH PAQUET CLOUSTON and OLIVER BILODEAU - the industry of so...
Introduction to Malware Detection and Reverse Engineering

Introduction to Malware Detection and Reverse Engineering
Private Date and PRYING Eyes - Talking Cybersecurity at After Work Network

Private Date and PRYING Eyes - Talking Cybersecurity at After Work Network
More from Manuel Schmalstieg
Free & Libre Graphics – Eracom – 2019

Présentation sur les logiciels libres dans le domaine du graphisme et de l'audiovisuel. Eracom, 2019. Remerciement à Régis Wieland, organisateur de l'atelier.
Typographie et WordPress

Slides de la présentation du 9 mars 2019, journée Meetup Genève:
https://www.meetup.com/geneva-wordpress/events/256964267/
Typographie - notions de design graphique, HE-Arc, 2018

Cours rapide sur les fontes et la typographique dans les interfaces numériques.
Couleur - notions de design graphique, HE-Arc, 2018

Cours rapide sur l'utilisation de la couleur dans les interfaces graphiques. Palettes de couleur, accessibilité.
Open Talk #6

Présentation donnée au Center for Future Publishing, HEAD Genève, décembre 2018. Je parle de mon travail de publication hybride, de mon implication dans différentes communautés du logiciel libre, de l'archivage numérique...
https://ms-studio.net/talks/open-talk-center-for-future-publishing/
Workshop design graphique (HE-Arc, novembre 2017)

Workshop design graphique, pour les étudiants de la HE-Arc Ingénierie, Neuchâtel
Le design du HTML5 (Remix)

Un remix de la conférence "The Design of HTML5" par Jeremy Keith (2011) - https://speakerdeck.com/adactio/the-design-of-html5
A Book Isn’t A Book Isn’t A Book

On October 24, 2013, I gave a talk at the 4th Books in Browsers conference, San Francisco, about the mysterious phenomena of spam-as-books that has been infiltrating distribution platforms and university libraries worldwide.
ELIF - Lyon - 29-03-2016

“Quelques outils, quelques projets” - présentation donnée lors du séminaire ELIF n°1 (résistance électronique, stratégie éditoriale et cyberféminisme), organisé par Ensba Lyon et l'ESADSE.
Black Holes in the Gutenberg Galaxy

A talk delivered at the Off the Press: Electronic Publishing in the Arts conference, Rotterdam.
Also available as a video: https://vimeo.com/97508658
Date managment for minimalists

A short talk given at WordCamp Switzerland 2014, about the importance of time and date in website architecture, and in WordPress.
Presentation of my custom plugin Minimalistic Event Manager: http://wordpress.org/plugins/minimalistic-event-manager/
2x10 - le concept

2x10 = des rencontres mensuelles entre professionnels des secteurs créatifs et technologiques : graphistes, artistes visuels, concepteurs multimédia, makers, développeurs...
Présentation donnée le 13 septembre 2013 au premier meeting 2x10.
What text styles could learn from CSS

A lightning talk, given at Libre Graphics Meeting 2013 in Madrid.
My favorite feature request for Desktop Publishing (DTP) software makers: bring your style definitions on par with CSS, and let us edit the style rules **in the code**, if we want to.
Nowadays, we designers know CSS. We want that flexibility for our text style definitions!
Designing a Libre Font Specimen Book

How eleven students (of HEAD Geneva) created a type specimen book in 5 days, featuring 200+ libre and open source fonts.
View on Vimeo: https://vimeo.com/68202369
WordPress 3.5 Release Celebration (Geneva Meetup)

Support de la présentation donnée au Meetup WordPress Genève, le 5 décembre 2012. Comprend: (1) Introduction à WordPress, (2) Comment contribuer à WordPress, (3) Les nouveautés de WordPress 3.5.
Slides from the talk given at the WordPress Geneva Meetup, December 5th 2012, for the pre-release of WordPress 3.5.
Greyscale Press - stratégies d'auto-archivage

Greyscale Press produit des simulacres de livres, de 70 à 700 pages, reposant sur des textes d'origine électronique, généralement trouvés, idéalement libres de droits, abandonnés par leurs auteurs, anonymes ou non identifiables. Contenus récurrents: narration approximative ("Report from the desert"), wikipédisme ("VJing"), procès-verbaux ("IT-95-5/18-I"), interviews ("In conversation with Julian Assange"), mailing-listes ("ZKP1"), random ("La décimation"), données brutes ("Data Hammer").
VJing - From software to public space

Workshop / presentation given May 5th at Lift Conference, Geneva. By Manuel Schmalstieg and Ilan Katin.
Wiki-Sprint Geneva (Mapping Festival 2010)

This slideshow accompanied the public presentation given on May 13th 2010 at Mapping Festival Geneva, as the outcome of the Wiki-Sprint Workshop. For further information, see http://wiki-sprint.ch
More from Manuel Schmalstieg (20)
Typographie - notions de design graphique, HE-Arc, 2018

Typographie - notions de design graphique, HE-Arc, 2018
Couleur - notions de design graphique, HE-Arc, 2018

Couleur - notions de design graphique, HE-Arc, 2018
Fear, Uncertainty and Doubt
- 2. FUD FEAR, UNCERTAINTY AND DOUBT Dark Designs Symposium Yverdon - October 14 2008
- 3. BOT • derived from the word "robot" • program that performs repetitive functions • infected computer controlled by another computer
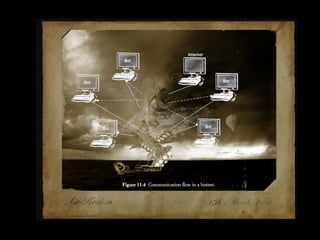
- 4. BOTNET • a network of bots • commonly used to control or attack computer systems • controlled through an IRC channel. • also referred to as “zombies” or “drones”
- 5. USE OF BOTNETS • distributing spam • mounting DDoS attacks • sniffing network traffic • key logging • click fraud (Google AdWords)
- 6. IRC • Internet Relay Chat • created in 1988 • first bots : 1993 • client / server
- 7. HISTORY • 1999: SETI@home • screensaver program • prove the viability and practicality of the 'distributed grid computing' concept
- 8. SETI@home
- 9. February 2000 • first widely publicized botnet incident • floods CNN.com, Amazon.com, eBay... • 75 computers in 52 different networks
- 10. SubSeven Discovered: June 6, 1999 also known as: Backdoor.SubSeven (Kaspersky Lab), Backdoor.SubSeven22 (Symantec), BackDoor.SubSeven (Doctor Web), Troj/Sub7-1.7 (Sophos), Backdoor:Win32/SubSeven.A (RAV)...
- 11. SubSeven
- 12. SubSeven • server / client • control over IRC • monitor keystrokes • remote desktop application
- 13. SubSeven
- 14. SubSeven
- 15. SubSeven • october 2000 • 800 infected computers found • SexxxyMovie.mpeg.exe
- 16. GTbot • modified IRC client • coupled with the hackers own scripts • port scanning • DDoS attacks
- 17. DDoS • Distributed Denial of Service Attack • attacker causes a network of computers to “flood” a victim computer with large amounts of data or specific commands
- 18. GTbot
- 19. GTbot
- 20. DDoS
- 21. Agobot • most widely circulated virus in history • best-written source code • C++ base plugin framework • GPL license
- 22. Op.Cyberslam • October 2003 • Agobot used in DDoS attack • Botnet: 5000 to 15000 computers • FBI investigation
- 23. Op.Cyberslam
- 24. Op.Cyberslam
- 25. October 2005 • Discovery of a botnet counting 1.5 million compromised computers
- 26. January 2007 • The Storm Botnet is identified. • Estimate: from 600 million computers on the Internet, 150 million belong to a botnet (Vint Cerf).
- 27. STORM BOTNET • 1 million to 50 million computer systems • encrypted P2P control • more computing power than the world’s 500 top supercomputers
- 28. Russian Business Network
- 29. RBN • cybercrime organization • personal identity theft • bulletproof hosting • child pornography, phishing, spam, and malware distribution • physically based in St. Petersburg
- 30. Companies RBNet, TcS Network, RBNetwork, Nevcon Ltd. RBusinessNetwork, (Panama), iFrame Cash, Too coin Software Aki Mon Telecom, (UK), 4Stat, 76service, Eexhost, MalwareAlarm... Rusouvenirs Ltd.,
- 31. Malware Gozi, Grab, Haxdoor, Metaphisher, Mpack, Ordergun, Pinch, Rustock, Snatch, Torpig, URsnif... • viruses or worms • send data back to RBN servers
- 32. October 2007 • Storm Botnet reduces size • fallen to 160,000 systems • partitioning / smaller networks • 40-byte key encryption
- 33. November 2007 • RBN vanishes from the web • unusual bulk registries of thousands of Web addresses in China • servers move to Shangai/Taiwan
- 34. KRAKEN BOTNET • largest botnet as of april 08 • over 400’000 bots • also known as: Bobax, Oderoor, Cotmonger
