Big Data - The BIIIG Solution
•
1 like•3,229 views
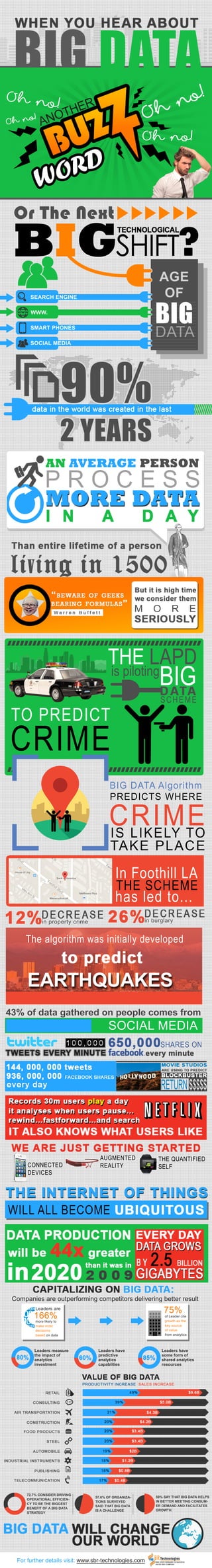
At the moment big data is a massive buzzword. The entire business world is trying to unearth the real essence of the term. Are you one of them? Then take a look at this fantastic presentation to discover a number of unknown facts on big data – the way it is offering big solution to businesses. Don't forget to share your thoughts and ideas with us.
Report
Share
Report
Share
Download to read offline
Recommended
Beyond Diversity: Embracing inclusion

Diversity is much-praised for fostering healthier and more innovative workplaces. But whichever way you slice ‘diversity’, the majority of our teams reflect one demographic, and simply adding “a diverse hire” won’t magically produce these results. So are the claims true? If so, what else do we need to do?
Through our time training and placing coders from widely differing backgrounds we’ve had to get to grips with the realities of integrating teams.
This talk looks at the importance of inclusive practices and explores the link with quality and innovation. We also investigate some of the unconscious biases and infrastructure challenges that reinforce exclusion.
With collaboration at their heart, agile teams are best placed to promote inclusion. How can we extend agile practices to place conscious attention on creating connections and to build truly healthy, demographically representative teams?
118 Hacker-Powered Facts From The 2018 Hacker-Powered Security Report

Another year, another Hacker-Powered Security Report! We pulled out 100 of the report’s top facts—and then added 18 more, since it’s 2018. See below for a better understanding of how hacker-powered security is disrupting (in a good way) how organizations approach security. More security teams are adding VDPs, more are supplementing their skills and bandwidth with hackers, and more are augmenting their standard pen tests with hacker challenges.
In 2018, the HackerOne community and those using our platform have combined to crush every metric that we track. Organizations awarded more than $11 million in bounties. Hackers submitted more than 78,000 reports. Bounties were awarded to hackers in over 100 countries.
Unfortunately, the only metric that hasn’t changed much is the percentage of Forbes Global 2000 companies without vulnerability disclosure policies.
Read on for all of the facts!
Media140: Welcome to Oxford

An opening presentation by Paul Squires, welcoming delegates to Media140 Oxford. Paul touches on the history of the term "reputation", and some thoughts on its literal definition.
Cable TV Future in Full-On Network Society, VCTA Annual Meeting

Glen Hiemstra, Founder and CEO of Futurist.com presents the closing Keynote to the annual meeting of the Virginia Cable TV Association on Nov. 12, 2013 in Williamsburg, Virginia. Glen reviews the most important events, trends, and developments shaping the coming decade, from customer demographics to sustainability and home security, to economic disparity and ability to pay, to industry churn and the issues of privacy and transparency. The major focus is the future of technology including 3D connectivity, internet of things, artificial intelligence, quantified health, big data, new currencies, and more.
Recommended
Beyond Diversity: Embracing inclusion

Diversity is much-praised for fostering healthier and more innovative workplaces. But whichever way you slice ‘diversity’, the majority of our teams reflect one demographic, and simply adding “a diverse hire” won’t magically produce these results. So are the claims true? If so, what else do we need to do?
Through our time training and placing coders from widely differing backgrounds we’ve had to get to grips with the realities of integrating teams.
This talk looks at the importance of inclusive practices and explores the link with quality and innovation. We also investigate some of the unconscious biases and infrastructure challenges that reinforce exclusion.
With collaboration at their heart, agile teams are best placed to promote inclusion. How can we extend agile practices to place conscious attention on creating connections and to build truly healthy, demographically representative teams?
118 Hacker-Powered Facts From The 2018 Hacker-Powered Security Report

Another year, another Hacker-Powered Security Report! We pulled out 100 of the report’s top facts—and then added 18 more, since it’s 2018. See below for a better understanding of how hacker-powered security is disrupting (in a good way) how organizations approach security. More security teams are adding VDPs, more are supplementing their skills and bandwidth with hackers, and more are augmenting their standard pen tests with hacker challenges.
In 2018, the HackerOne community and those using our platform have combined to crush every metric that we track. Organizations awarded more than $11 million in bounties. Hackers submitted more than 78,000 reports. Bounties were awarded to hackers in over 100 countries.
Unfortunately, the only metric that hasn’t changed much is the percentage of Forbes Global 2000 companies without vulnerability disclosure policies.
Read on for all of the facts!
Media140: Welcome to Oxford

An opening presentation by Paul Squires, welcoming delegates to Media140 Oxford. Paul touches on the history of the term "reputation", and some thoughts on its literal definition.
Cable TV Future in Full-On Network Society, VCTA Annual Meeting

Glen Hiemstra, Founder and CEO of Futurist.com presents the closing Keynote to the annual meeting of the Virginia Cable TV Association on Nov. 12, 2013 in Williamsburg, Virginia. Glen reviews the most important events, trends, and developments shaping the coming decade, from customer demographics to sustainability and home security, to economic disparity and ability to pay, to industry churn and the issues of privacy and transparency. The major focus is the future of technology including 3D connectivity, internet of things, artificial intelligence, quantified health, big data, new currencies, and more.
The 2018 Hacker Report: Insights on the hacker mindset, who they are, and the...

We are in the age of the hacker. Never before has there been more opportunities to learn, more tools, more welcoming companies and more money up for grabs. At the end of last year, we tapped into our community of ethical hackers to better understand how they like to work, what’s most important to them and what needs to change. The 2018 Hacker Report is the largest survey ever conducted of the ethical hacking community with 1,698 respondents.
Women Wired Weekend

i developed this presentation for Women Wired Weekend event, basic idea was to open the techno savvy audience's mind to digital divide, and to propose videogames as a media as one of fun
Branding 360 Conference: Transparency in a customer obsessed world

This presentation deals with with the power of TRANSPARENCY. How companies around the world, big and small ,are embracing total transparency with complete respect to privacy. to male the societies we live in fair and equitable The transparency is allowing them to build extraordinary trust and thrive in a world of increasing skepticism and extraordinary data where the ability to distinguish between truths and half truths or fact from fiction is becoming increasingly challenging and often impossible. The transparency is allowing corporations to delight customers and drive a level of personalisation that has never been seen before. Data lies at the heart of this transparency and combined with Machine learning and Artificial intelligence is breaking new grounds in customer obsession. Consumers are seeking this transparency and rewarding companies with their loyalty and more willing to pay premiums. This is cutting across progressive governments, companies, brands, shareholders, employees and is even driving richer peer to peer collaboration. The holy grail of total consumer transparency is when infotech meets Biotech revealing our every action and a wide range of emotions .Lastly the presentation makes an effort to characterise this phenomenon across industries from food, health & media to transportation, retail and fashion among others. Hope you enjoy this overview
A to Z: The influence of generational shifts on work and technology

As Gen Y becomes a larger player in the Australian workplace, what impact will their unique behaviours and skills have on the workforce as a whole?
Discover how their ideas and expectations could shape not only the future of your business but the future of technology, social media and marketing.
Click through to our SlideShare for insights on how generational shifts are influencing the way we work, communicate and collaborate.
Are You a Hacker's Target?

Are you a hacker’s target? How do they get your information? In the world of network security, cybercrime and information warfare, it’s important to protect yourself. Check out the infographic below and let us know: how have you been a hacker’s target?
Government innovation pnwdgs

Keynote Presentation from the Pacific Northwest Digital Government Summit
New York Digital Government Summit- Dustin Haisler Keynote

Keynote presentation from September 5, 2014, New York Digital Government Summit.
JWT: SXSW Interactive 2015 (April 2015)

This year’s SXSW Interactive was bigger than ever, with over 33,000 attendees and hundreds of panels and events. Our latest report explores key themes from the ballooning festival, from innovations in sustainability to the new frontier of artificial intelligence and virtual immortality. The report features on-the-ground insights, brand examples and interviews with experts from tech and academia.
A look back at some of our achievements

We thought to take a moment to reflect and look back at some of our achievements over the last couple of years.
#Businessconsultingcompany #accomplishments #digitalsuccess
Social Media Marketing Trends - Social Intelligence Report 2014

No one could deny the role of social media to reach out potential consumers. Take a look at the industry report which has been created based on social media marketing trends in 2014. It has been crafted after an in-depth analysis of how different established brands have reinforced their presence in the industry utilizing the social media platforms. It will also offer you a detailed view about the performance of different social networking sites in 2014 Get to know about the social networking site gaining more impetus for brand promotion in recent time.
Hope this visually appealing presentation will delight you. We would love to know your feedback about our presentation. You can also share with us your social media campaign experience in 2014.
Top Ten Amazon Drone Threats by SBR-Technologies

Top Ten Amazon Drone Threats presented by SBR-Technologies
A Social Media Guide for Small Business Owners

Social Media is the newest marketing tool. With minimum investments create viral social media campaigns and reach out to your targeted market. Follow the presentation and learn how to create an effective and successful Social Media Campaign for small business owners.
Facebook Promotion Best Practices

Follow this tutorial for easy and essential Facebook Promotion tips.
8 s ocial media strategies

SBR-Technologies offers highly customized social media marketing services that help companies of small and medium sized enterprises to develop a prominent presence in the online arena. To cater to every requirements of the clients, we at, SBR-Technologies formulate comprehensive social media plans to ensure the growth of the business to the very best.
SBR Technologies Pvt Ltd wins ISO 9001: 2008 Certification

SBR Technologies Pvt Ltd, one of the leading player in the web service and web application forte has recently been awarded with ISO 9001: 2008 Certification.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
More Related Content
Similar to Big Data - The BIIIG Solution
The 2018 Hacker Report: Insights on the hacker mindset, who they are, and the...

We are in the age of the hacker. Never before has there been more opportunities to learn, more tools, more welcoming companies and more money up for grabs. At the end of last year, we tapped into our community of ethical hackers to better understand how they like to work, what’s most important to them and what needs to change. The 2018 Hacker Report is the largest survey ever conducted of the ethical hacking community with 1,698 respondents.
Women Wired Weekend

i developed this presentation for Women Wired Weekend event, basic idea was to open the techno savvy audience's mind to digital divide, and to propose videogames as a media as one of fun
Branding 360 Conference: Transparency in a customer obsessed world

This presentation deals with with the power of TRANSPARENCY. How companies around the world, big and small ,are embracing total transparency with complete respect to privacy. to male the societies we live in fair and equitable The transparency is allowing them to build extraordinary trust and thrive in a world of increasing skepticism and extraordinary data where the ability to distinguish between truths and half truths or fact from fiction is becoming increasingly challenging and often impossible. The transparency is allowing corporations to delight customers and drive a level of personalisation that has never been seen before. Data lies at the heart of this transparency and combined with Machine learning and Artificial intelligence is breaking new grounds in customer obsession. Consumers are seeking this transparency and rewarding companies with their loyalty and more willing to pay premiums. This is cutting across progressive governments, companies, brands, shareholders, employees and is even driving richer peer to peer collaboration. The holy grail of total consumer transparency is when infotech meets Biotech revealing our every action and a wide range of emotions .Lastly the presentation makes an effort to characterise this phenomenon across industries from food, health & media to transportation, retail and fashion among others. Hope you enjoy this overview
A to Z: The influence of generational shifts on work and technology

As Gen Y becomes a larger player in the Australian workplace, what impact will their unique behaviours and skills have on the workforce as a whole?
Discover how their ideas and expectations could shape not only the future of your business but the future of technology, social media and marketing.
Click through to our SlideShare for insights on how generational shifts are influencing the way we work, communicate and collaborate.
Are You a Hacker's Target?

Are you a hacker’s target? How do they get your information? In the world of network security, cybercrime and information warfare, it’s important to protect yourself. Check out the infographic below and let us know: how have you been a hacker’s target?
Government innovation pnwdgs

Keynote Presentation from the Pacific Northwest Digital Government Summit
New York Digital Government Summit- Dustin Haisler Keynote

Keynote presentation from September 5, 2014, New York Digital Government Summit.
JWT: SXSW Interactive 2015 (April 2015)

This year’s SXSW Interactive was bigger than ever, with over 33,000 attendees and hundreds of panels and events. Our latest report explores key themes from the ballooning festival, from innovations in sustainability to the new frontier of artificial intelligence and virtual immortality. The report features on-the-ground insights, brand examples and interviews with experts from tech and academia.
Similar to Big Data - The BIIIG Solution (10)
The 2018 Hacker Report: Insights on the hacker mindset, who they are, and the...

The 2018 Hacker Report: Insights on the hacker mindset, who they are, and the...
Branding 360 Conference: Transparency in a customer obsessed world

Branding 360 Conference: Transparency in a customer obsessed world
A to Z: The influence of generational shifts on work and technology

A to Z: The influence of generational shifts on work and technology
New York Digital Government Summit- Dustin Haisler Keynote

New York Digital Government Summit- Dustin Haisler Keynote
More from SBR-Technologies
A look back at some of our achievements

We thought to take a moment to reflect and look back at some of our achievements over the last couple of years.
#Businessconsultingcompany #accomplishments #digitalsuccess
Social Media Marketing Trends - Social Intelligence Report 2014

No one could deny the role of social media to reach out potential consumers. Take a look at the industry report which has been created based on social media marketing trends in 2014. It has been crafted after an in-depth analysis of how different established brands have reinforced their presence in the industry utilizing the social media platforms. It will also offer you a detailed view about the performance of different social networking sites in 2014 Get to know about the social networking site gaining more impetus for brand promotion in recent time.
Hope this visually appealing presentation will delight you. We would love to know your feedback about our presentation. You can also share with us your social media campaign experience in 2014.
Top Ten Amazon Drone Threats by SBR-Technologies

Top Ten Amazon Drone Threats presented by SBR-Technologies
A Social Media Guide for Small Business Owners

Social Media is the newest marketing tool. With minimum investments create viral social media campaigns and reach out to your targeted market. Follow the presentation and learn how to create an effective and successful Social Media Campaign for small business owners.
Facebook Promotion Best Practices

Follow this tutorial for easy and essential Facebook Promotion tips.
8 s ocial media strategies

SBR-Technologies offers highly customized social media marketing services that help companies of small and medium sized enterprises to develop a prominent presence in the online arena. To cater to every requirements of the clients, we at, SBR-Technologies formulate comprehensive social media plans to ensure the growth of the business to the very best.
SBR Technologies Pvt Ltd wins ISO 9001: 2008 Certification

SBR Technologies Pvt Ltd, one of the leading player in the web service and web application forte has recently been awarded with ISO 9001: 2008 Certification.
More from SBR-Technologies (7)
Social Media Marketing Trends - Social Intelligence Report 2014

Social Media Marketing Trends - Social Intelligence Report 2014
SBR Technologies Pvt Ltd wins ISO 9001: 2008 Certification

SBR Technologies Pvt Ltd wins ISO 9001: 2008 Certification
Recently uploaded
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
Recently uploaded (20)
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Big Data - The BIIIG Solution
- 1. BUZ WORD ANOTHER OrTheNext BIGSHIFT SEARCHENGINE SMARTPHONES SOCIALMEDIA WWW. BIG DATA BIG AGE OF 90% 2YEARS ANAVERAGEPERSON MOREDATA PROCESS M O R E THELAPD ispiloting BIG SCHEME TOPREDICT CRIME BIGDATAAlgorithm PREDICTSWHERE CRIMEISLIKELYTO TAKEPLACE InFoothillLA hasledto... THESCHEME inpropertycrime inburglary Thealgorithmwasinitiallydeveloped EARTHQUAKES 43% ofdatagatheredonpeoplecomesfrom SOCIALMEDIA SHARESON RETURN$$$$$ CONNECTED DEVICES AUGMENTED REALITY THEQUANTIFIED SELF 57.6% OFORGANIZA- TIONSSURVEYED SAIDTHATBIGDATA ISACHALLENGE 50% SAYTHATBIGDATAHELPS INBETTERMEETINGCONSUM- ERDEMANDANDFACILITATES GROWTH 72.7% CONSIDERDRIVING OPERATIONALEFFICIEN- CYTOBETHEBIGGEST BENEFITOFABIGDATA STRATEGY Companiesareoutperformingcompetitorsdeliveringbetterresult Leadersare morelikelyto makemost decisions basedondata 166% ofLeadercite growthasthe keysource ofvalue from analytics 75% Leadersmeasure theimpactof analytics investment Leadershave predictive analytics capablities Leadershave someform of sharedanalytics resources
