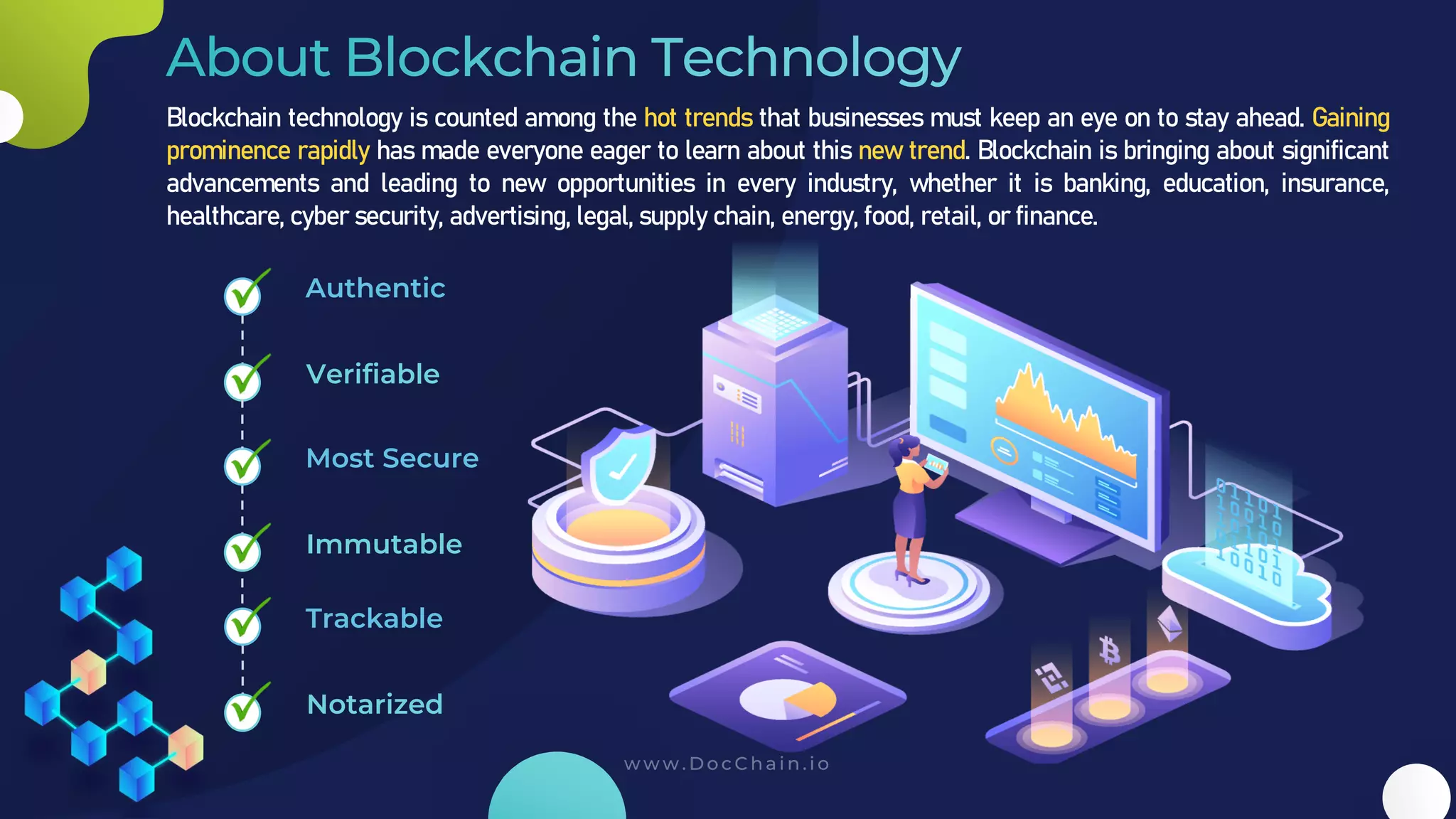
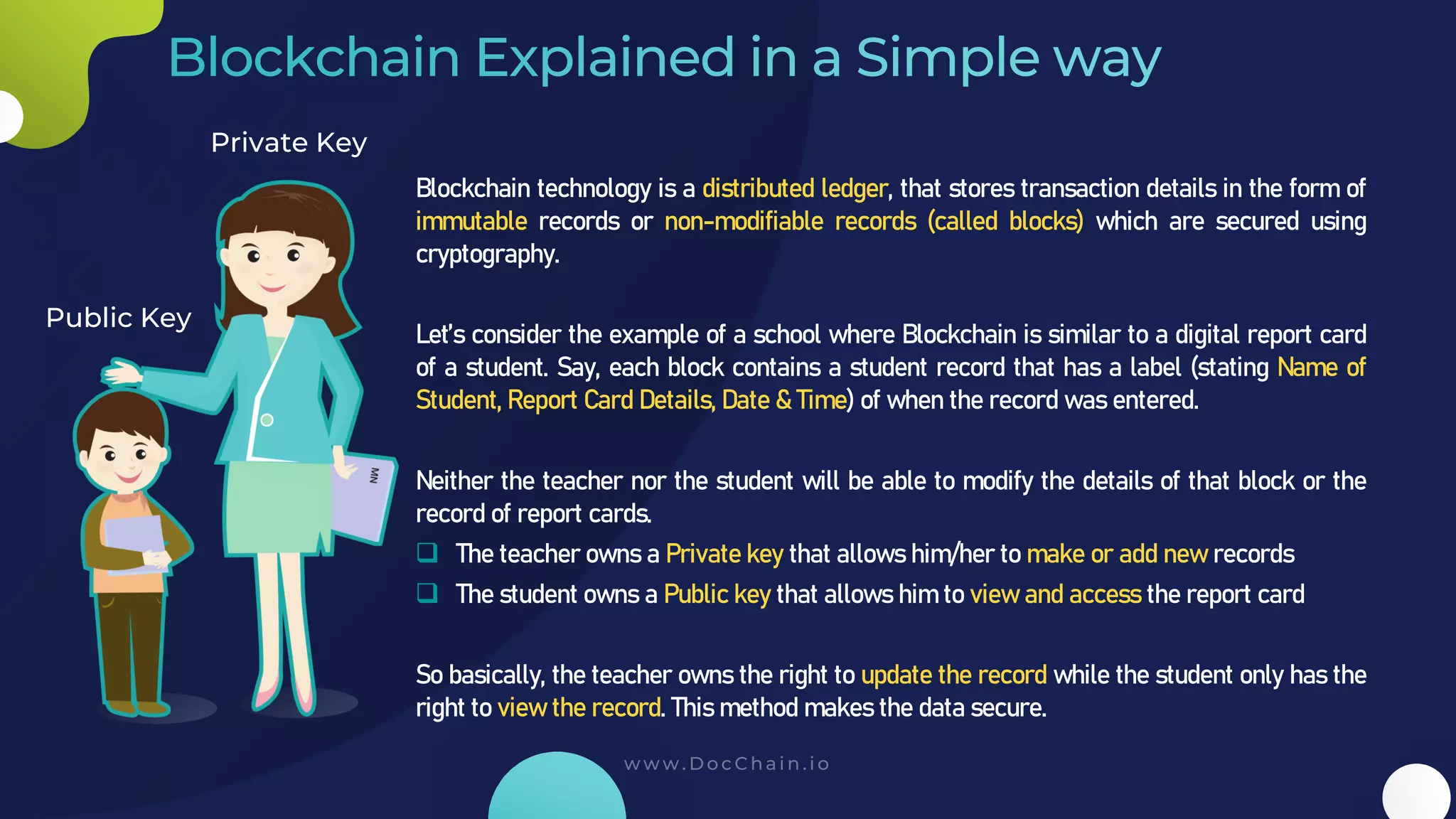
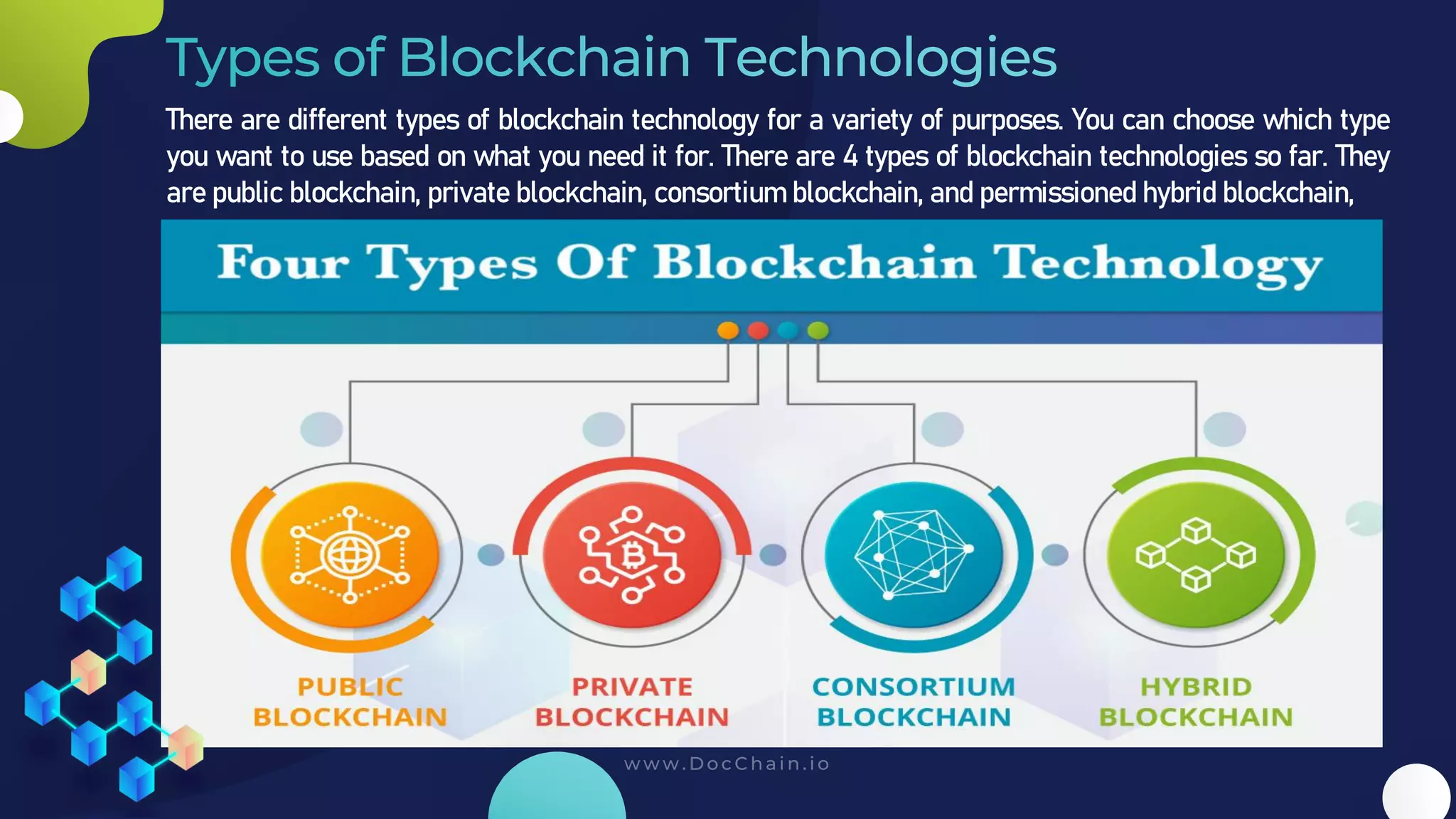
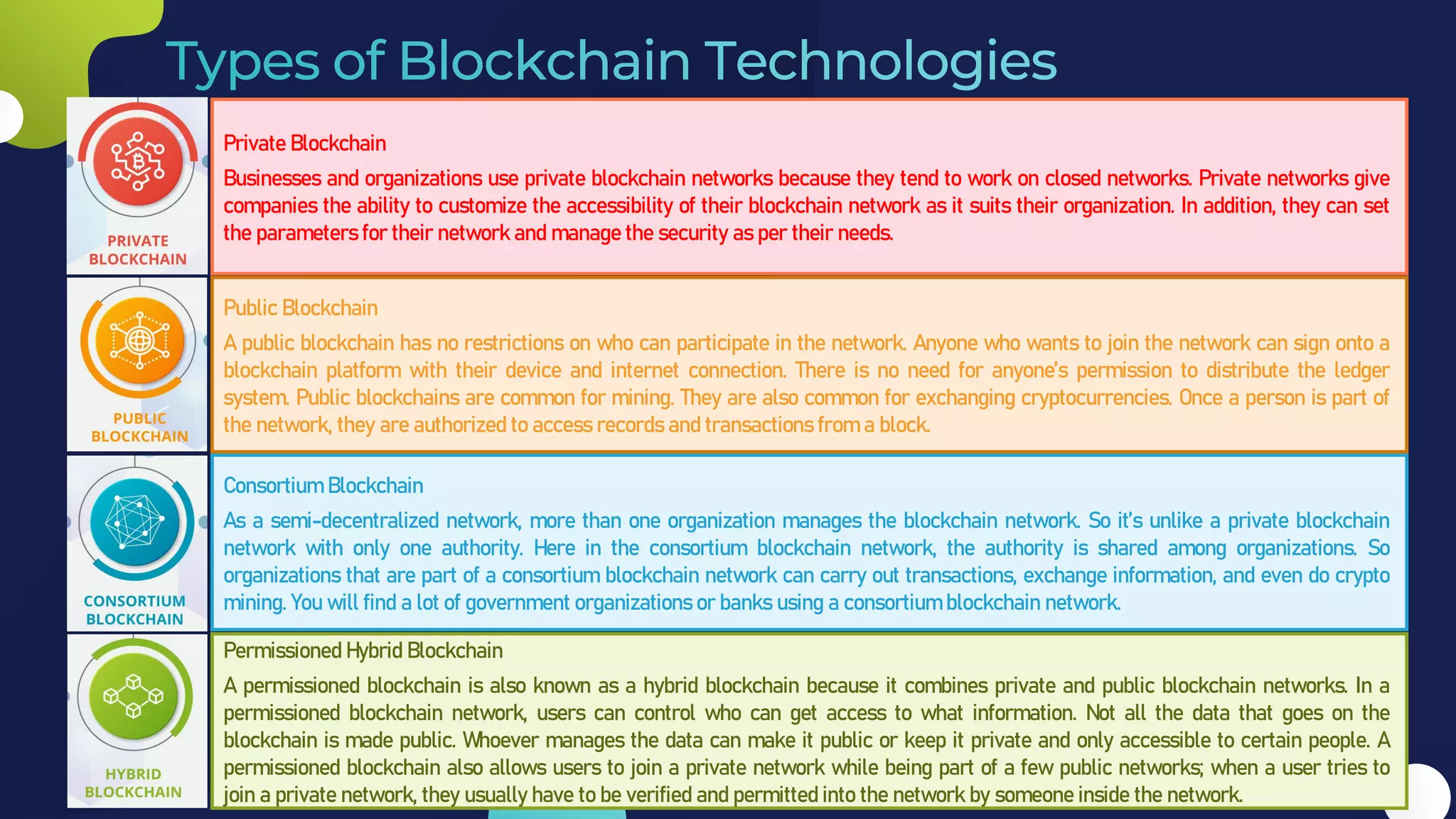
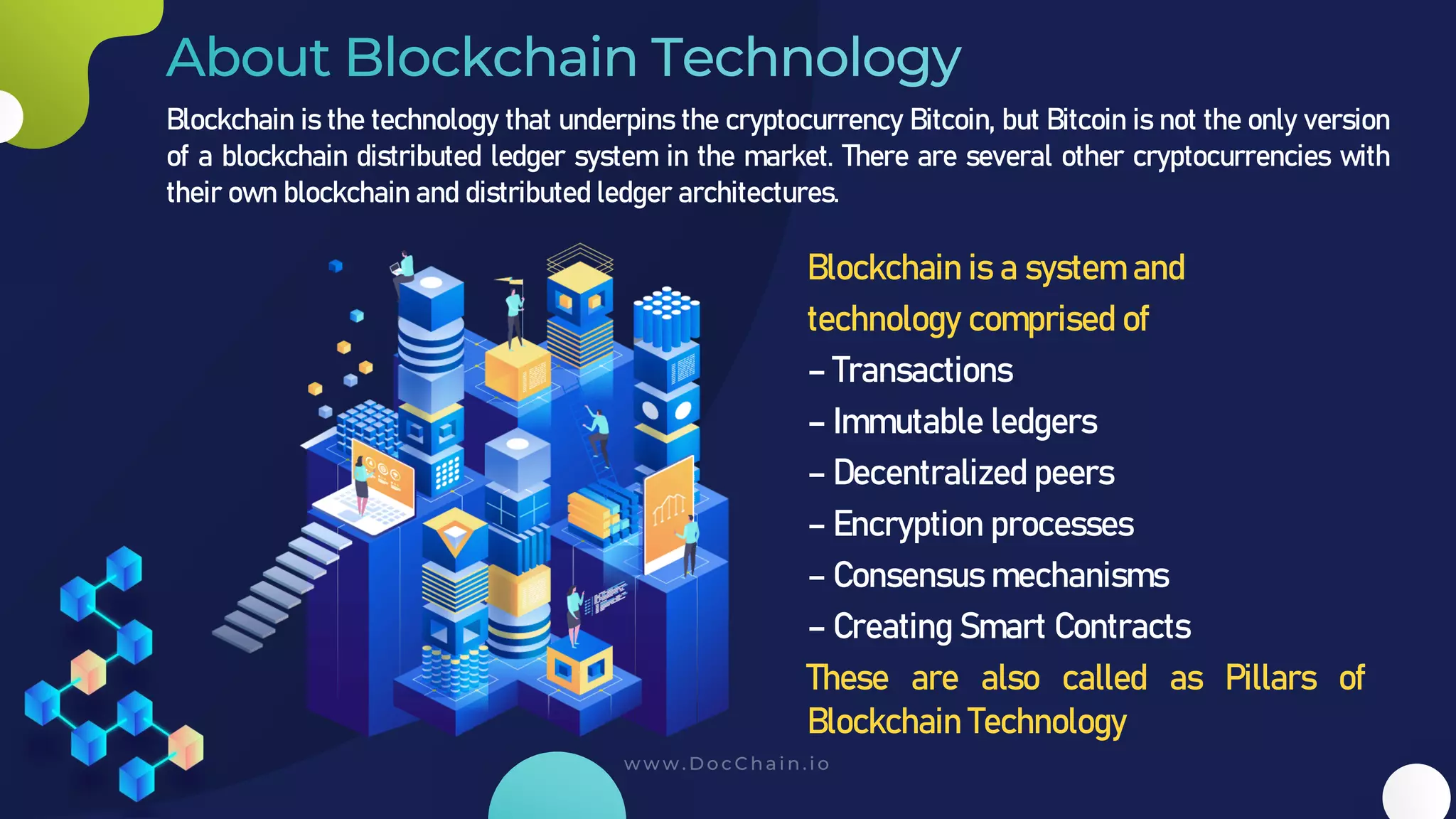
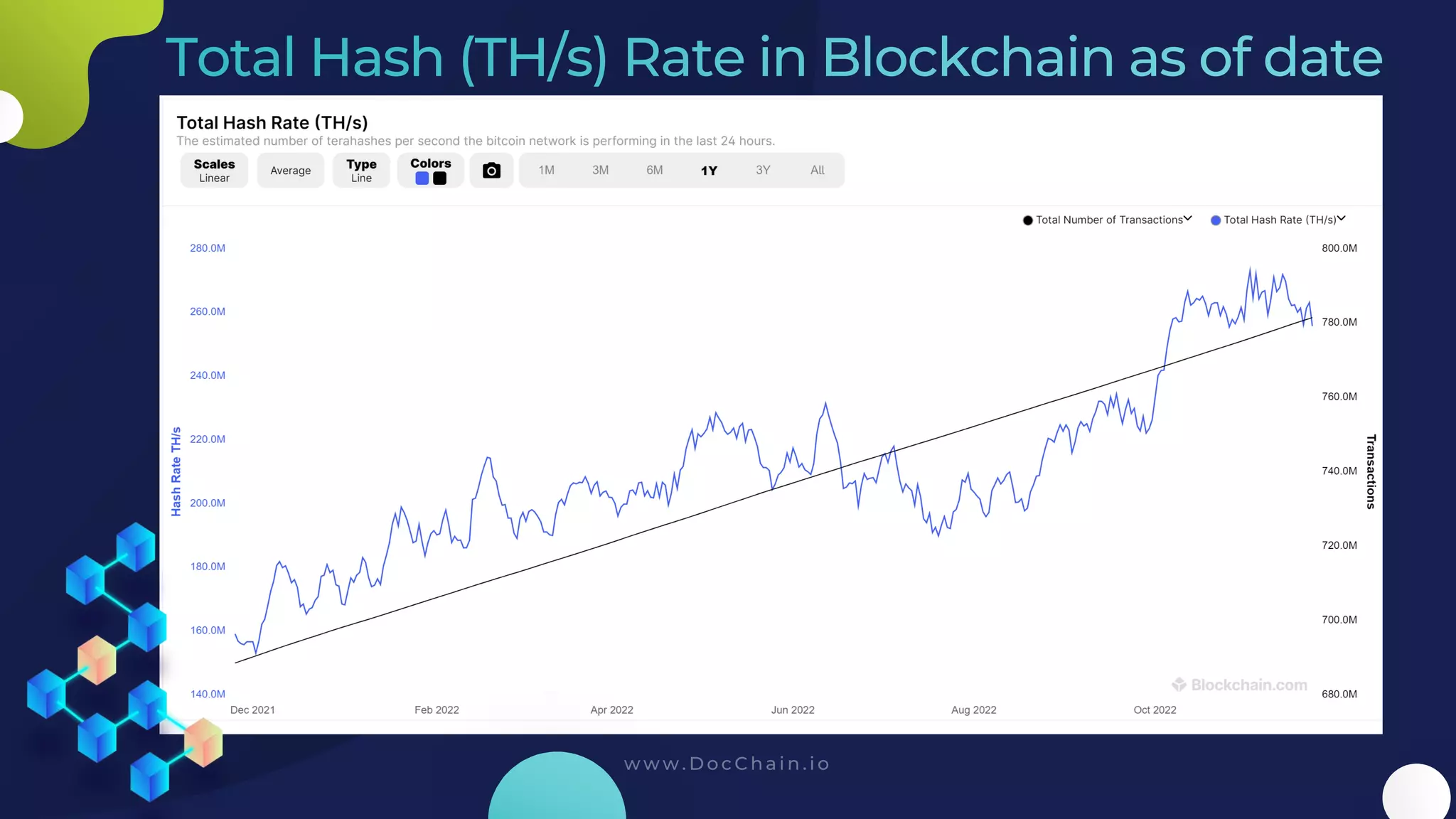
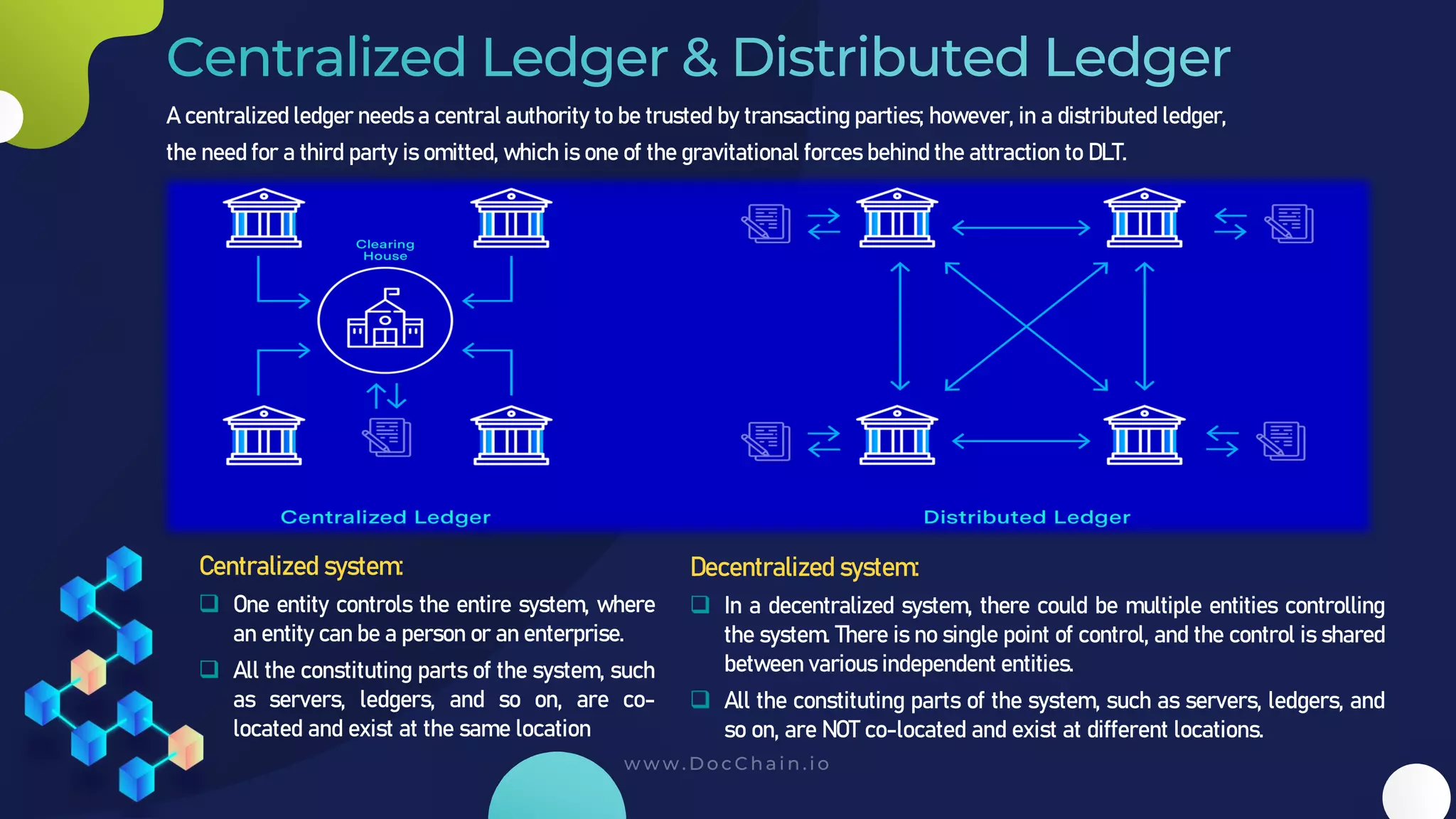
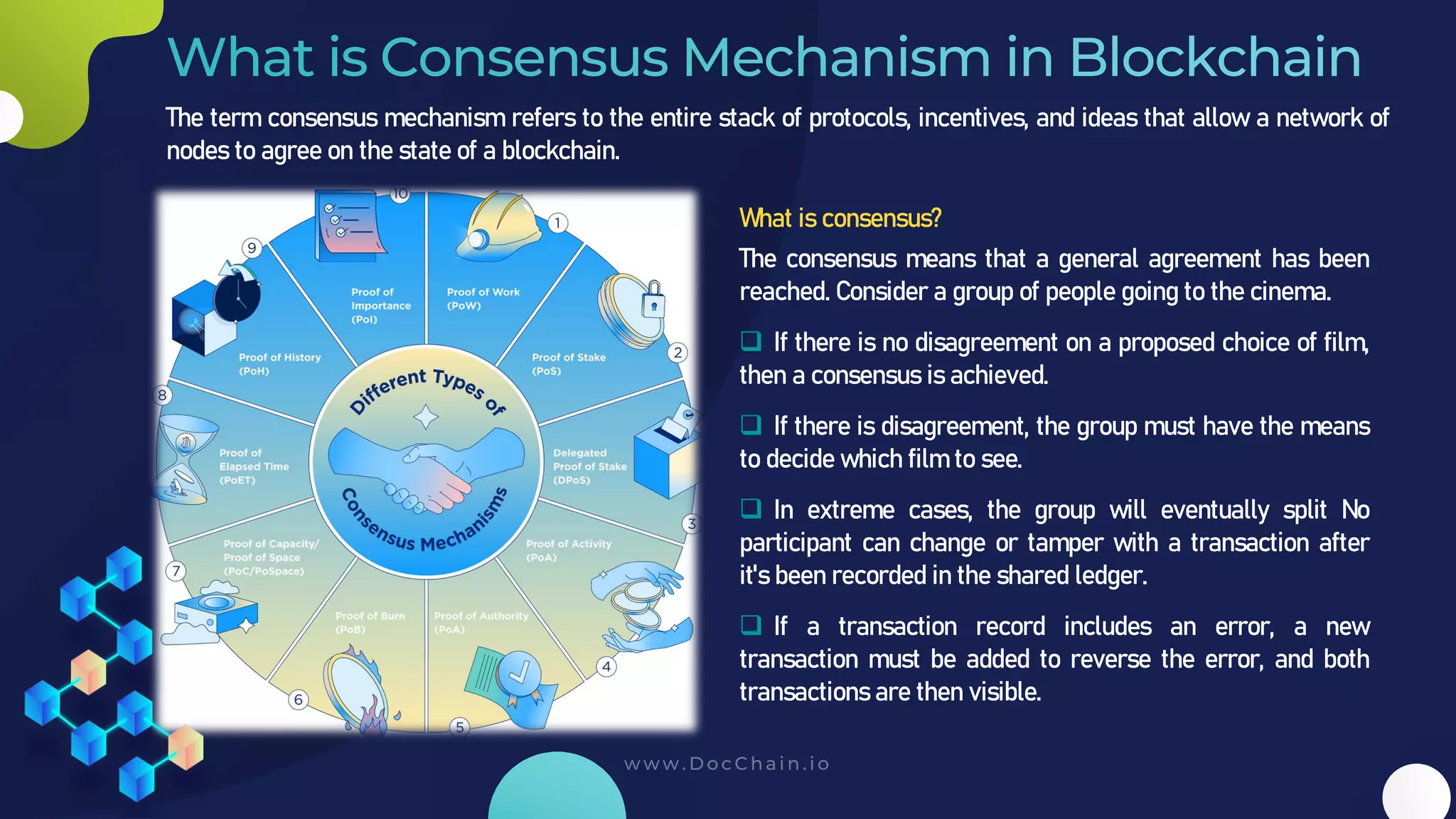
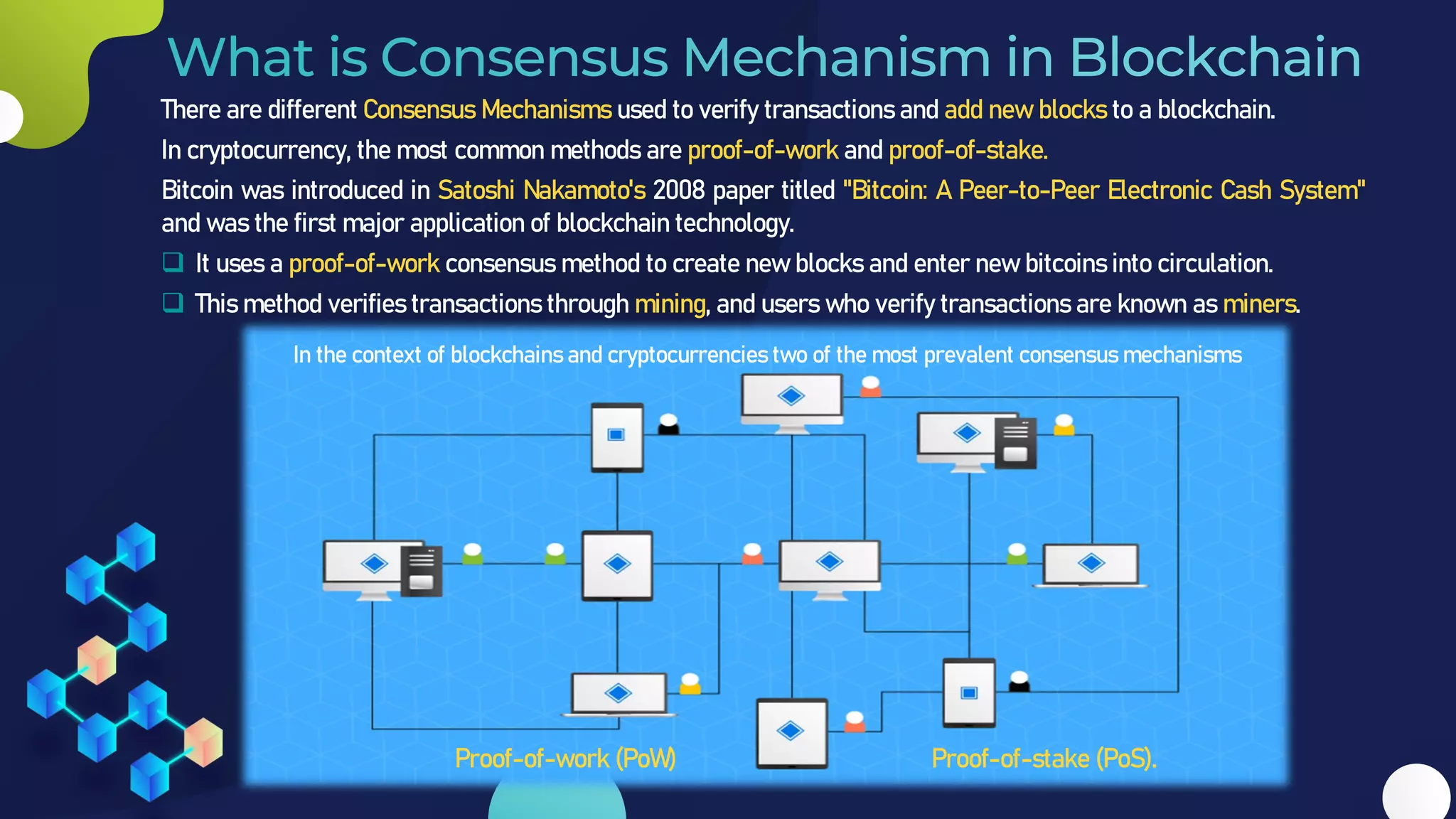
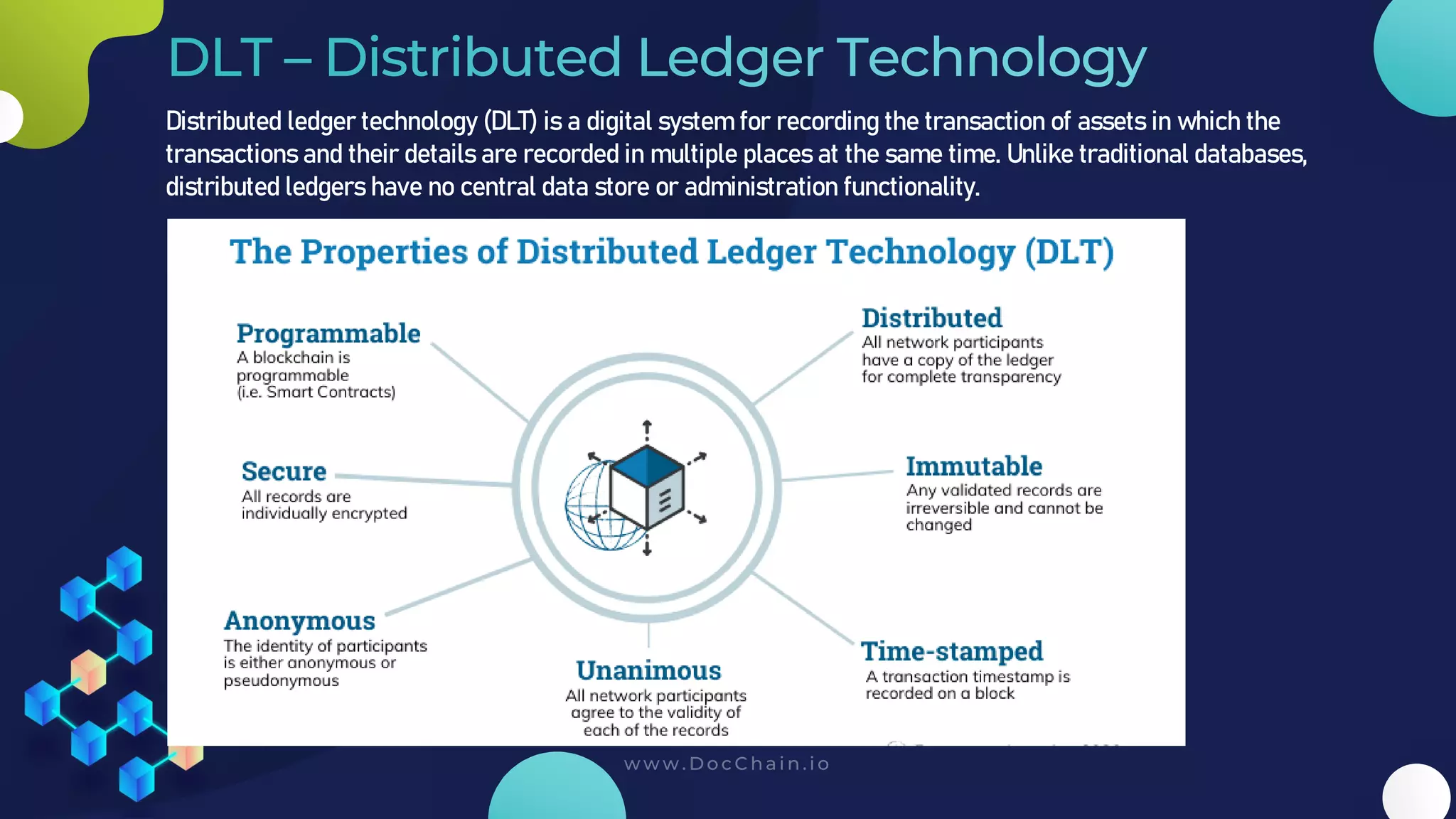
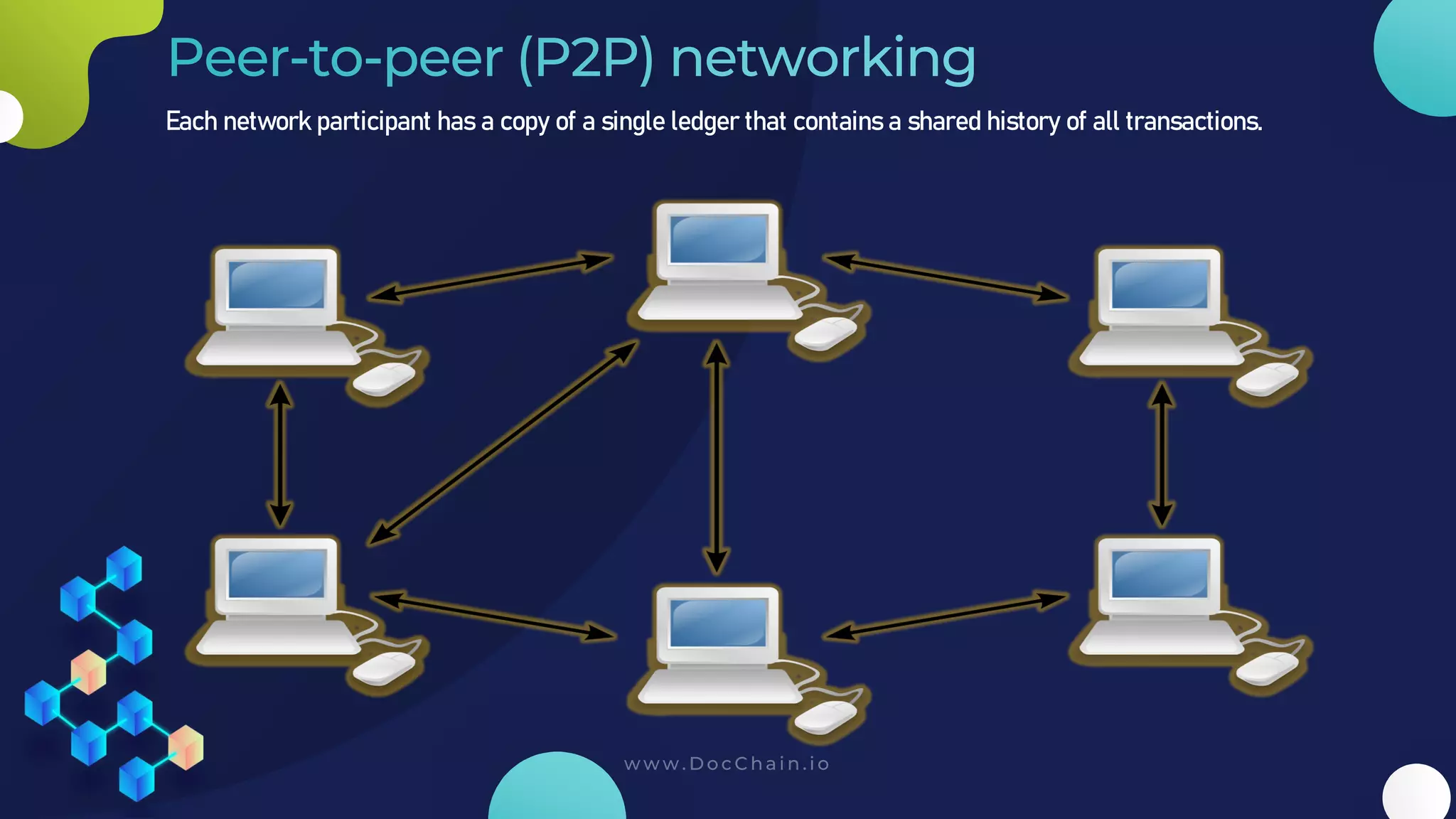
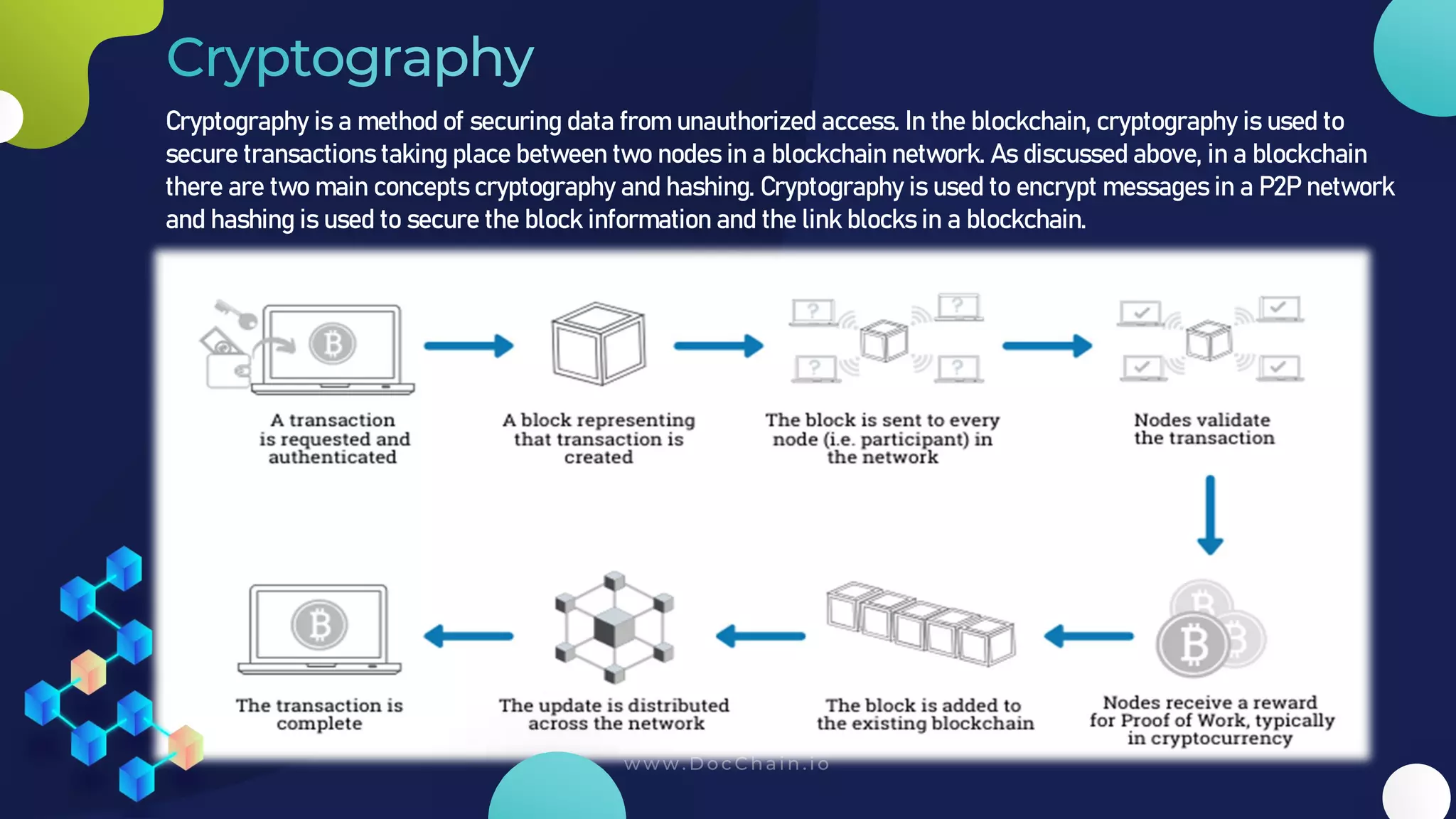
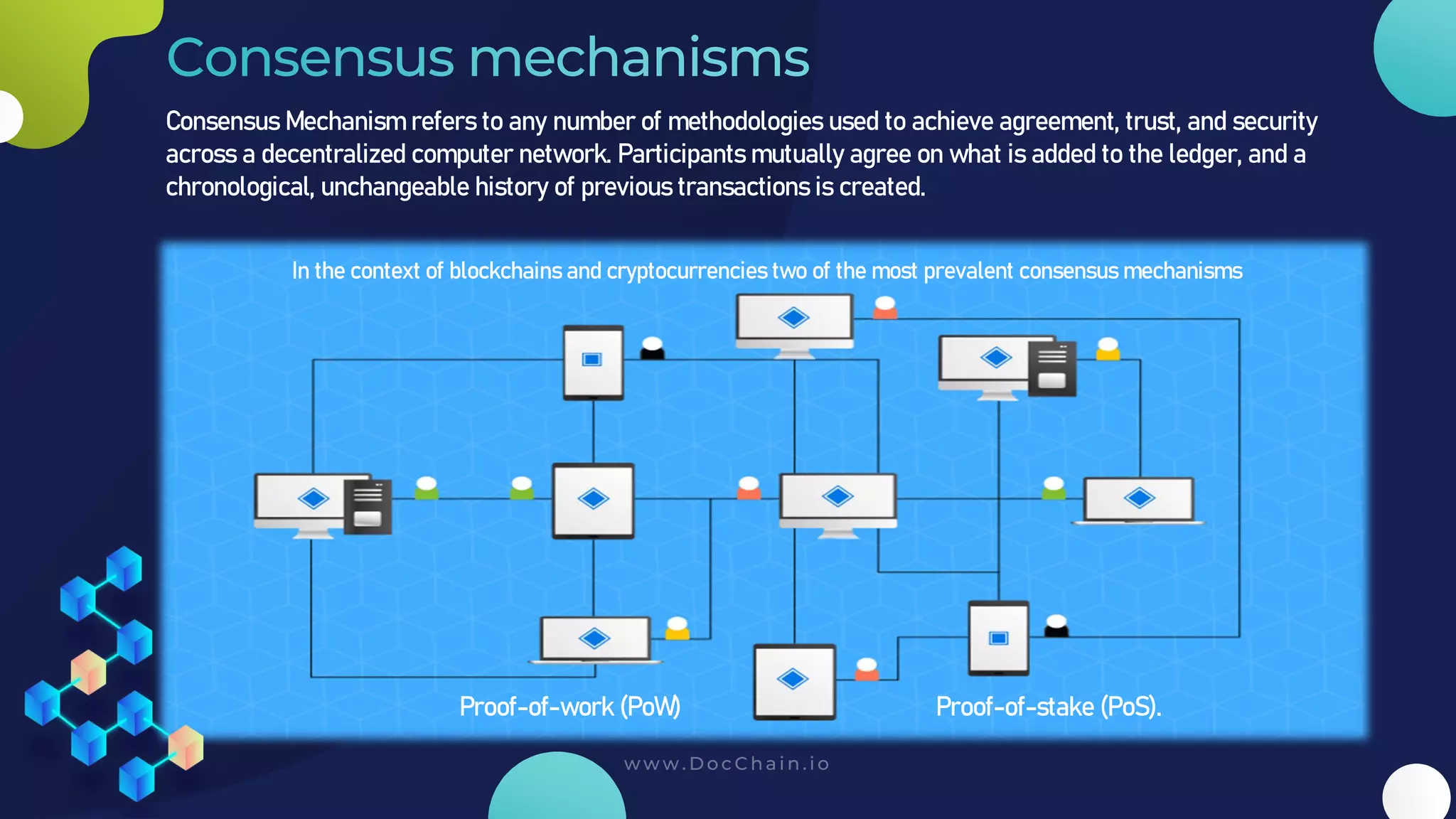
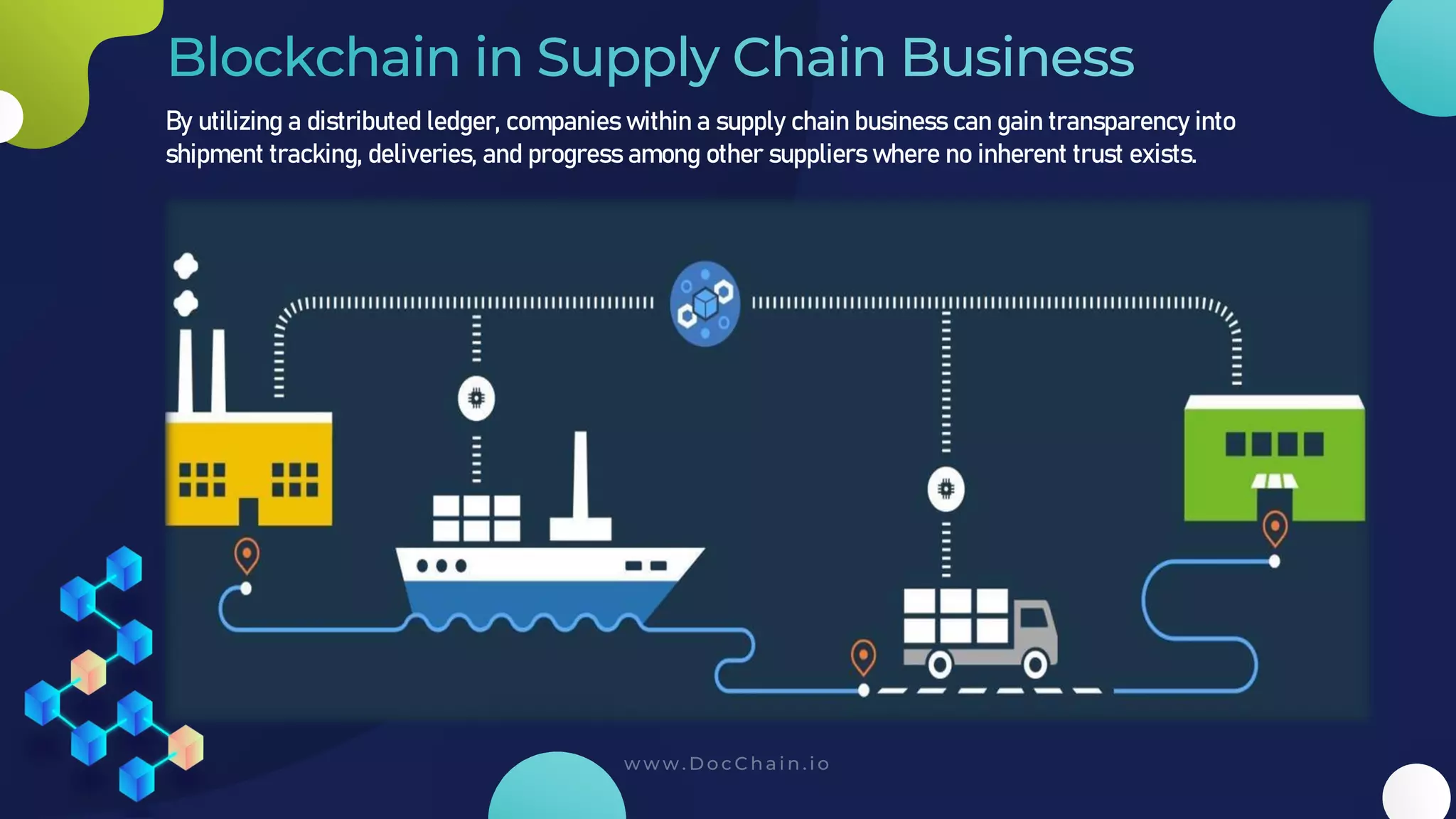
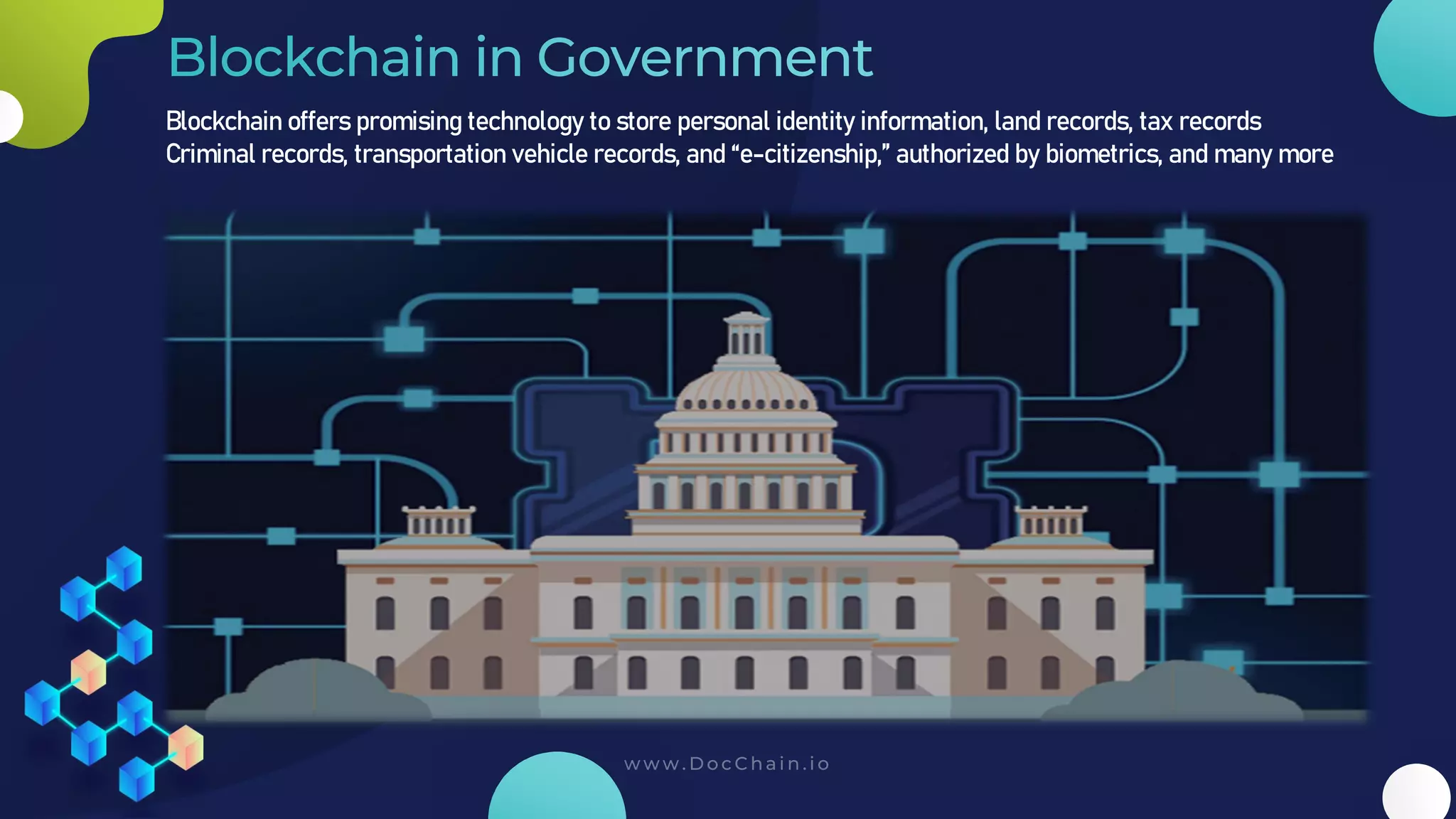
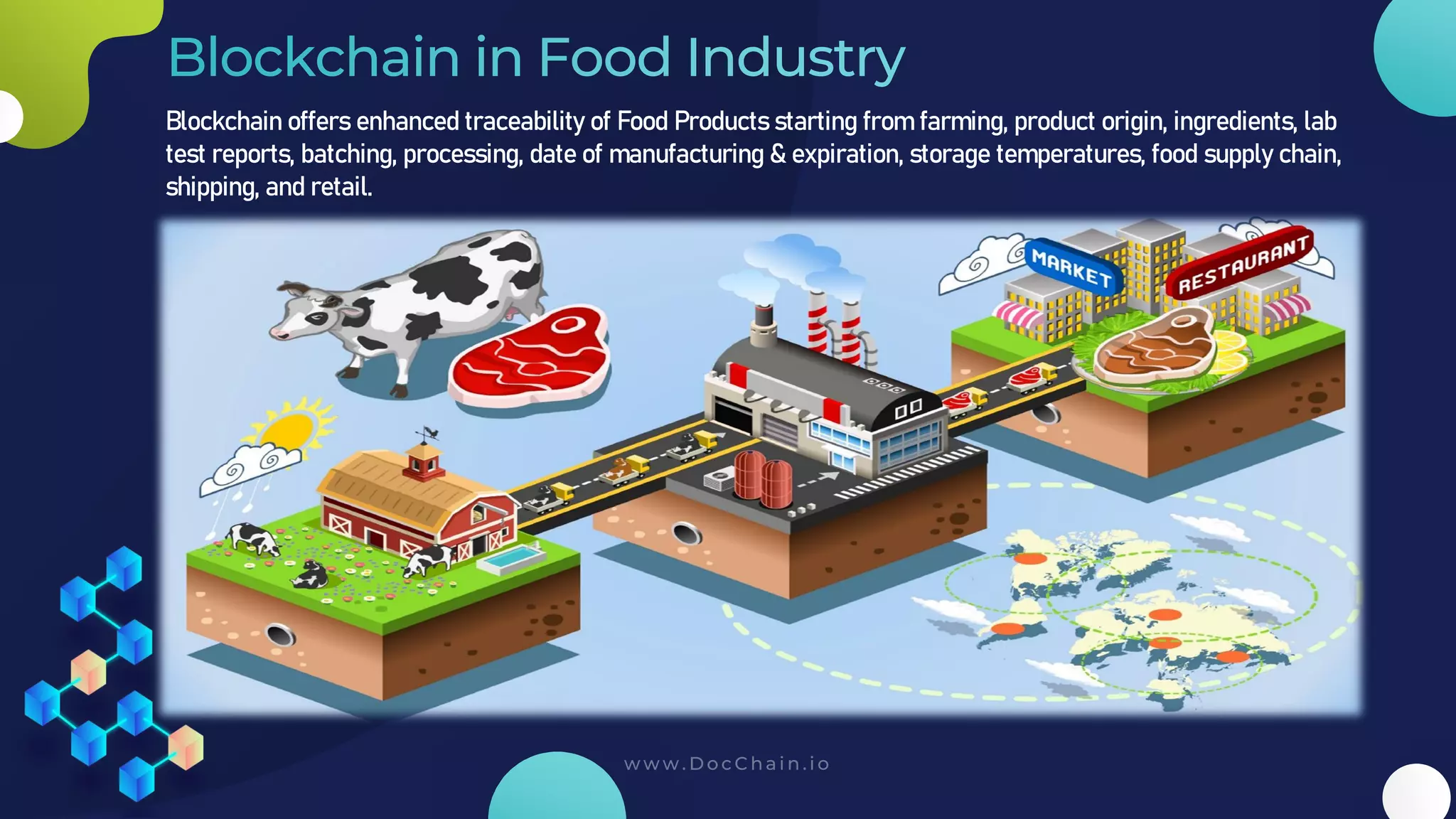
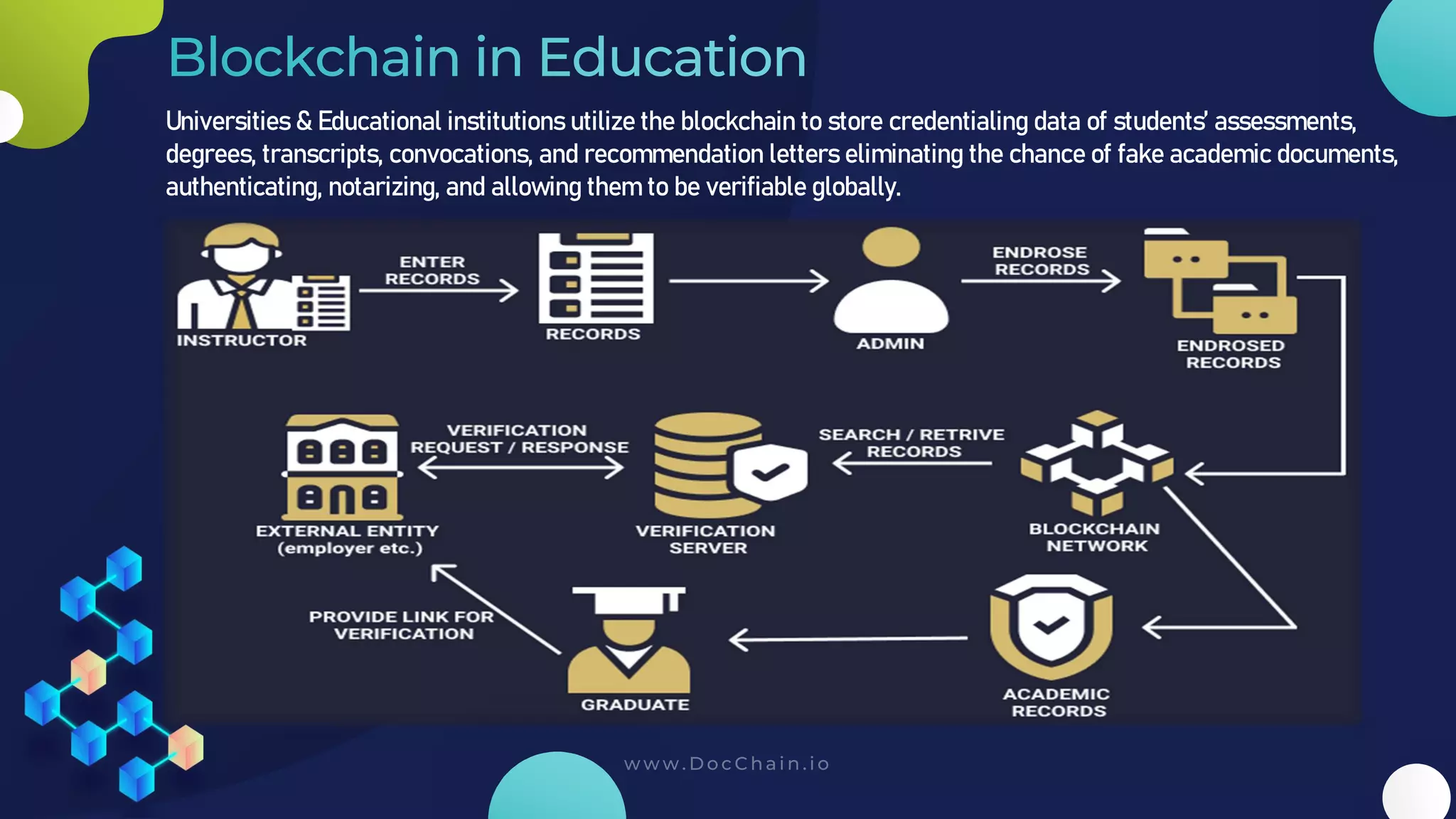
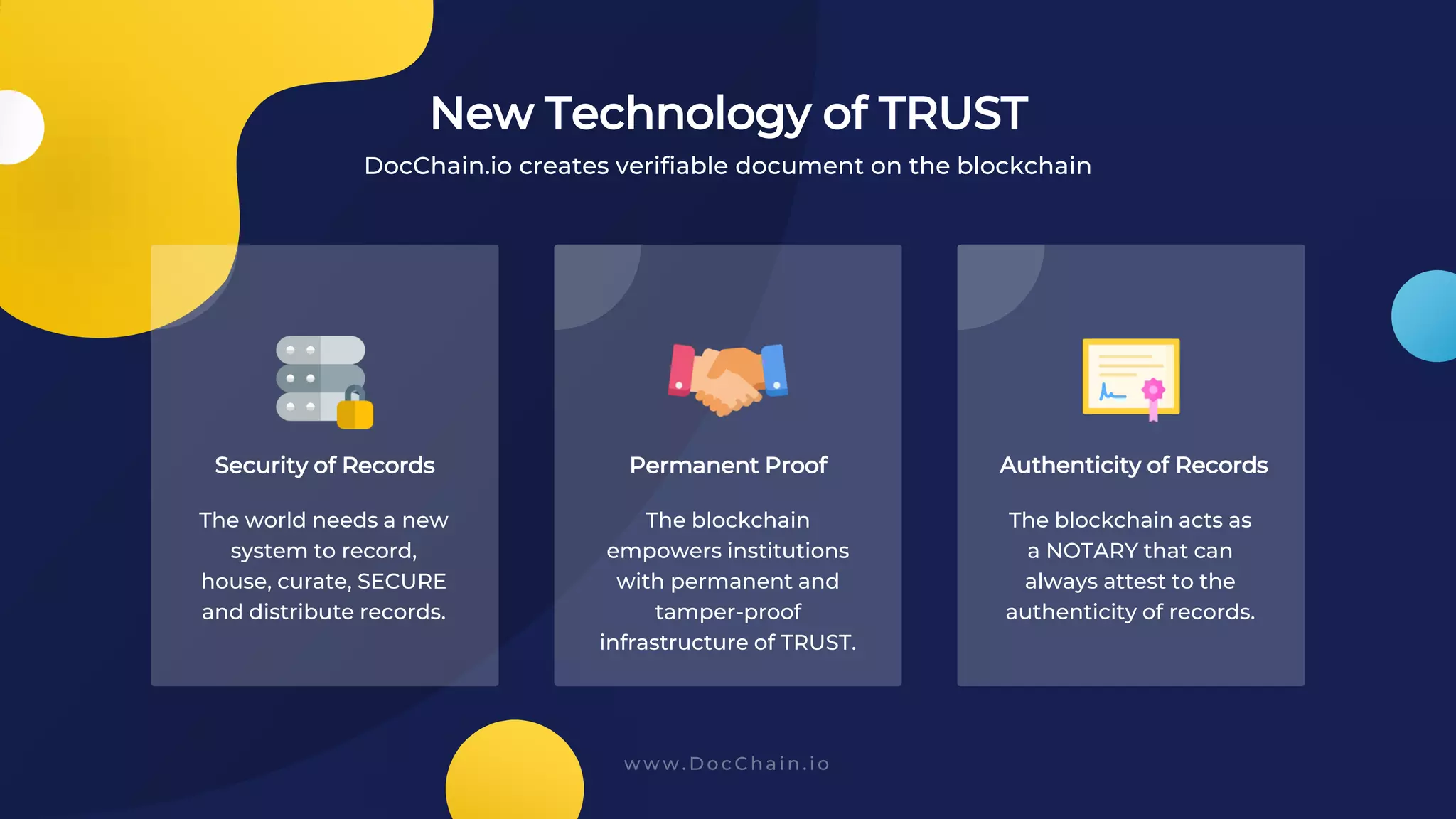
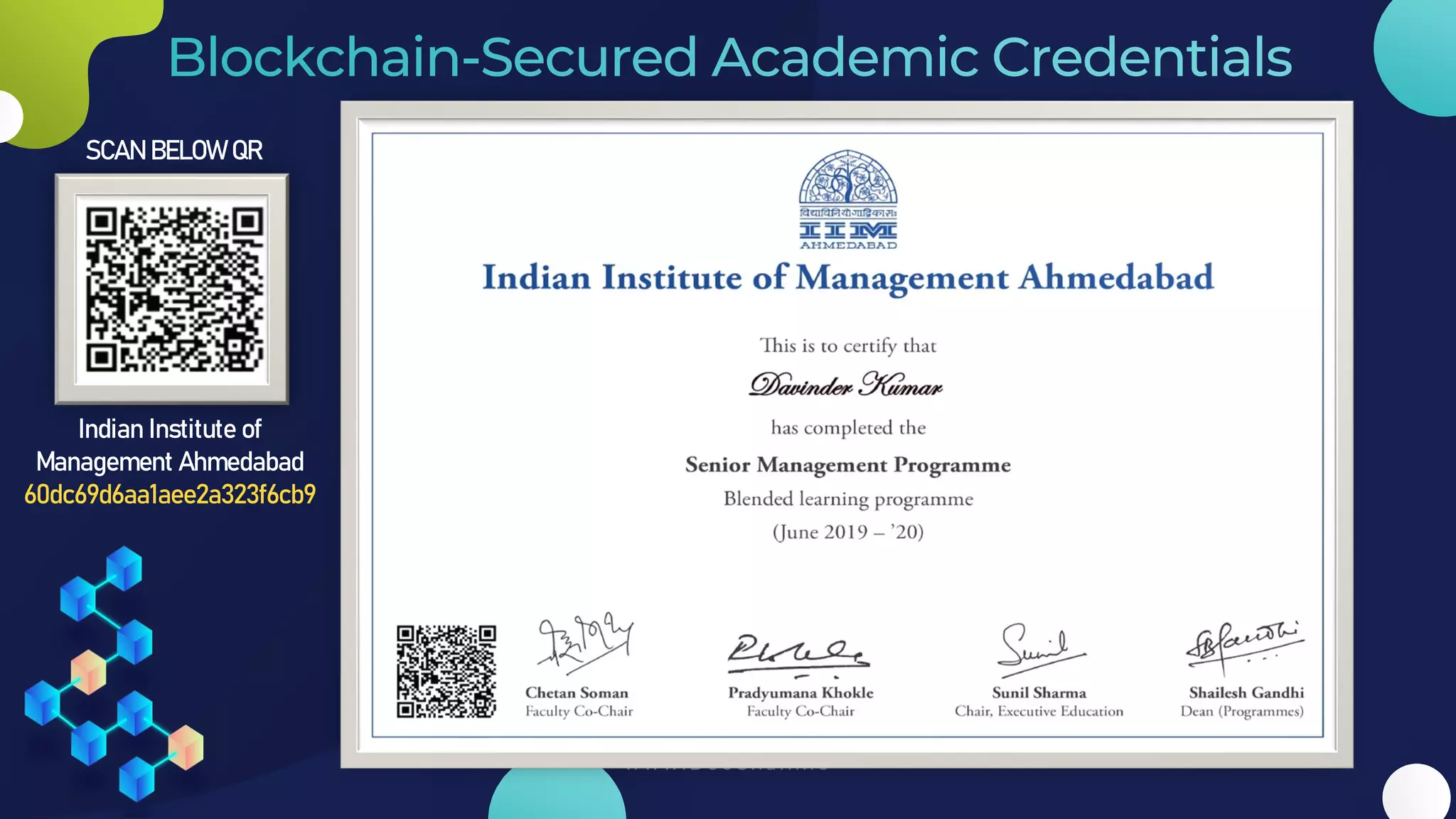
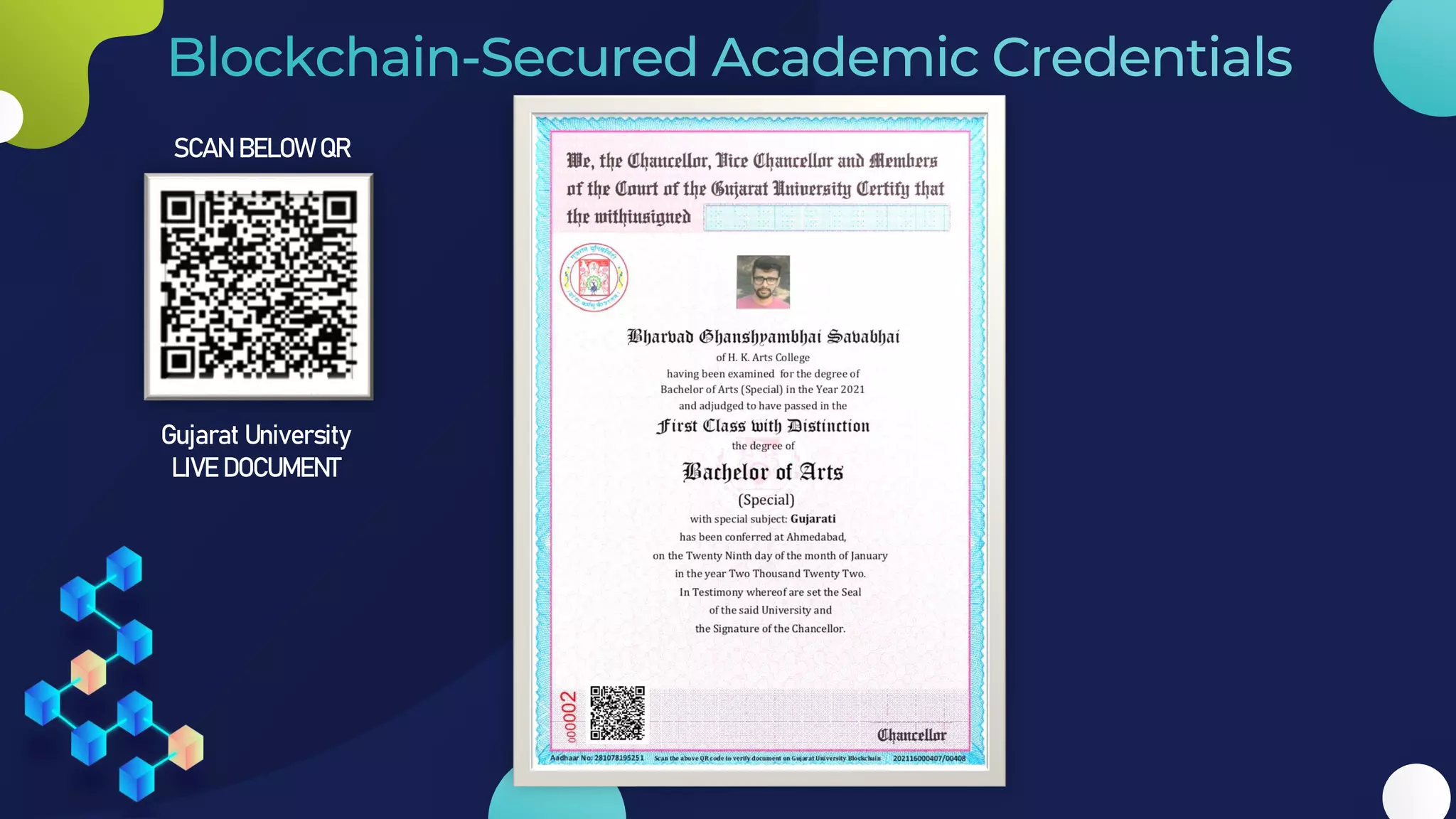
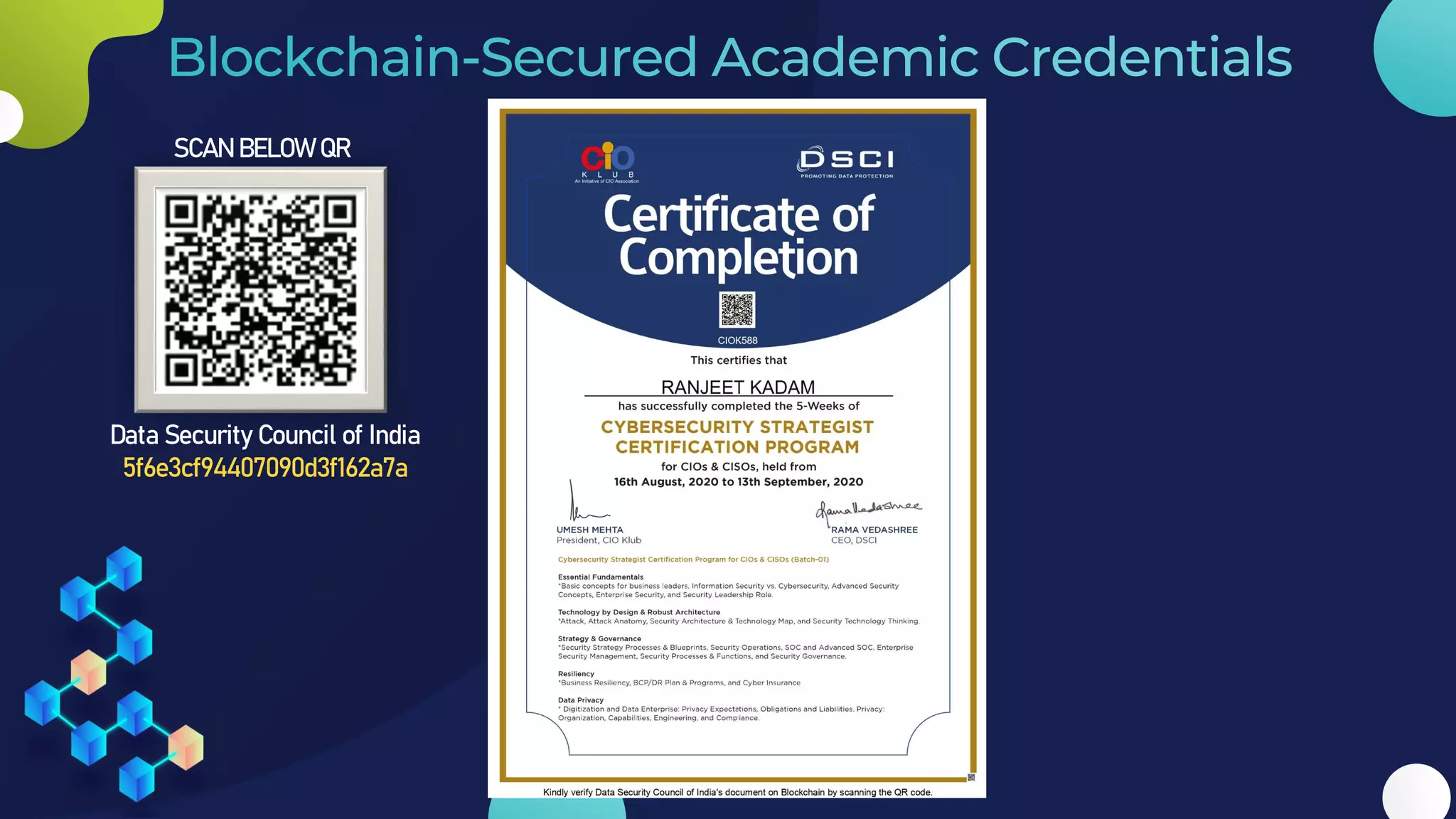
The document provides a comprehensive overview of blockchain technology, tracing its history and evolution from its theoretical inception to its practical applications in various industries. It categorizes different types of blockchain, such as public, private, consortium, and permissioned hybrid blockchains, while also discussing the foundational principles of how blockchain operates, including cryptographic security, consensus mechanisms, and the impenetrable design that ensures data integrity. The author emphasizes the necessity of understanding specific blockchain technologies tailored to unique needs and industries, urging thorough research before implementation.