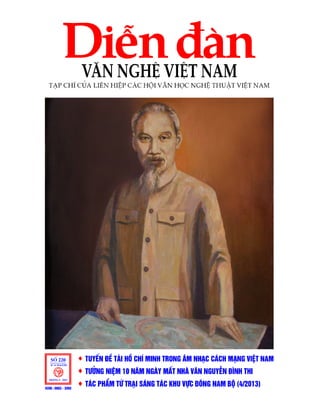
Bìa Diễn đàn Văn nghệ Việt Nam - Số 5/2013
•
0 likes•334 views
Cơ quan ngôn luận của Liên hiệp các hội Văn học, nghệ thuật Việt Nam – Số 5/2013 - vanhien.vn
Report
Share
Report
Share
Download to read offline
Recommended
Volume 2-issue-6-2085-2090

1) The document discusses the determination of non-technical losses in power systems using MATLAB simulation. Non-technical losses are difficult to calculate as they are caused by external factors to the system.
2) A case study of a transmission system in India is performed, calculating technical losses using load flow analysis in MATLAB. Non-technical losses are estimated as the difference between total losses and technical losses.
3) Additional non-technical loads are modeled by adding 3% of demand to one bus with a negative power factor. This increases both transmission losses and load. The percentage increases in losses and load due to non-technical losses are calculated and compared.
Ijarcet vol-2-issue-7-2363-2368

This document summarizes a research paper on using support vector machines (SVM) for anomaly detection, specifically for credit card fraud detection. It discusses how SVM is a supervised machine learning technique that can handle large, high-dimensional datasets. The document provides an overview of SVM, comparing it to other techniques like neural networks and clustering. It summarizes the methodology used in the research, which applied SVM to real credit card transaction data. The results showed SVM achieved high accuracy and a low false positive rate for fraud detection. In conclusion, the document states that applying this SVM method could help banks better predict fraudulent credit card transactions.
Juan barrera 

Juan Sebastian Barrera Martinez is the subject of this document. It does not provide any other details about him, his background, accomplishments or other identifying information. In just two short lines, this document only lists the name of Juan Sebastian Barrera Martinez without any other context.
Smart plant applications Used in industries

Intergraph has expanded its Global Professional Services Consultancy and Delivery Organization in Asia-Pacific with new leadership to provide consistent project delivery results across the region. The company's improved Global Professional Services Methodology provides a structured approach using best practices and processes to standardize reporting and enhance project execution. This proven methodology is scalable based on complexity and aims to streamline project governance, quality control, and risk mitigation to reduce costs and delays. Intergraph was ranked the number one provider of engineering design solutions worldwide by industry analyst ARC Advisory Group.
Advance Diploma in Accounting and Business ACCA

Minxuan Chen has been awarded the Advanced Diploma in Accounting and Business by the Association of Chartered Certified Accountants (ACCA) in October 2016. The certificate recognizes Chen's qualifications and remains the property of ACCA, who may demand its return at any time.
Ijarcet vol-2-issue-7-2378-2383

1. The document describes a technique to precisely determine the frequency of a ring oscillator using only three parameters: the number of stages (N), the capacitance at each stage (C), and the resistance (R).
2. It derives a formula for calculating the frequency by estimating the capacitance (C) through experimentation and the resistance (R) using the power dissipation at a single stage.
3. The technique was tested using LTspice simulations and was shown to estimate frequency accurately across different technologies and transistor dimensions.
Recommended
Volume 2-issue-6-2085-2090

1) The document discusses the determination of non-technical losses in power systems using MATLAB simulation. Non-technical losses are difficult to calculate as they are caused by external factors to the system.
2) A case study of a transmission system in India is performed, calculating technical losses using load flow analysis in MATLAB. Non-technical losses are estimated as the difference between total losses and technical losses.
3) Additional non-technical loads are modeled by adding 3% of demand to one bus with a negative power factor. This increases both transmission losses and load. The percentage increases in losses and load due to non-technical losses are calculated and compared.
Ijarcet vol-2-issue-7-2363-2368

This document summarizes a research paper on using support vector machines (SVM) for anomaly detection, specifically for credit card fraud detection. It discusses how SVM is a supervised machine learning technique that can handle large, high-dimensional datasets. The document provides an overview of SVM, comparing it to other techniques like neural networks and clustering. It summarizes the methodology used in the research, which applied SVM to real credit card transaction data. The results showed SVM achieved high accuracy and a low false positive rate for fraud detection. In conclusion, the document states that applying this SVM method could help banks better predict fraudulent credit card transactions.
Juan barrera 

Juan Sebastian Barrera Martinez is the subject of this document. It does not provide any other details about him, his background, accomplishments or other identifying information. In just two short lines, this document only lists the name of Juan Sebastian Barrera Martinez without any other context.
Smart plant applications Used in industries

Intergraph has expanded its Global Professional Services Consultancy and Delivery Organization in Asia-Pacific with new leadership to provide consistent project delivery results across the region. The company's improved Global Professional Services Methodology provides a structured approach using best practices and processes to standardize reporting and enhance project execution. This proven methodology is scalable based on complexity and aims to streamline project governance, quality control, and risk mitigation to reduce costs and delays. Intergraph was ranked the number one provider of engineering design solutions worldwide by industry analyst ARC Advisory Group.
Advance Diploma in Accounting and Business ACCA

Minxuan Chen has been awarded the Advanced Diploma in Accounting and Business by the Association of Chartered Certified Accountants (ACCA) in October 2016. The certificate recognizes Chen's qualifications and remains the property of ACCA, who may demand its return at any time.
Ijarcet vol-2-issue-7-2378-2383

1. The document describes a technique to precisely determine the frequency of a ring oscillator using only three parameters: the number of stages (N), the capacitance at each stage (C), and the resistance (R).
2. It derives a formula for calculating the frequency by estimating the capacitance (C) through experimentation and the resistance (R) using the power dissipation at a single stage.
3. The technique was tested using LTspice simulations and was shown to estimate frequency accurately across different technologies and transistor dimensions.
1918 1923

This document proposes a new digital watermarking technique that utilizes Discrete Wavelet Transform (DWT), Discrete Cosine Transform (DCT), Singular Value Decomposition (SVD), and Arnold Transform. It embeds a watermark image into the high frequency subbands of a cover image after applying DWT and SVD. During extraction, the receiver applies the same transforms to extract the watermark. The technique aims to provide improved robustness against various attacks like noise, compression, filtering etc. compared to existing techniques that use these transforms individually or in pairs. The document analyzes the proposed technique's performance based on the extracted watermark's peak signal-to-noise ratio after subjecting the watermarked image to different attacks.
1771 1775

The document discusses a system for integrating structured and unstructured data from heterogeneous environments. The system uses OGSA-DAI services and the Globus Toolkit to provide an abstraction layer that allows database operations on both structured data from databases and unstructured file-based data. It generates metadata from unstructured data and configures the abstraction layer to query across the different data sources. This provides users an integrated view of both structured and unstructured data through a single interface.
Ijarcet vol-2-issue-3-891-896

This document discusses a digital image processing (DIP) based system for identifying defects in industrial materials like steel rods. Images of reference and test samples are taken and compared using techniques like thresholding, histograms, and cell segmentation in MATLAB. Defects are identified by variations between the images. The system is implemented on an FPGA for hardware acceleration. Images of steel rods with and without defects are compared to demonstrate the system's ability to detect cracks. The DIP based approach can replace manual inspection and provides faster quality evaluation of industrial materials compared to software-only methods.
Elmwood guide to the living trust

This information is not intended to be legal advice. Please see our full disclaimer inside the document
International Journal of Engineering Research and Development (IJERD)

journal publishing, how to publish research paper, Call For research paper, international journal, publishing a paper, IJERD, journal of science and technology, how to get a research paper published, publishing a paper, publishing of journal, publishing of research paper, reserach and review articles, IJERD Journal, How to publish your research paper, publish research paper, open access engineering journal, Engineering journal, Mathemetics journal, Physics journal, Chemistry journal, Computer Engineering, Computer Science journal, how to submit your paper, peer reviw journal, indexed journal, reserach and review articles, engineering journal, www.ijerd.com, research journals,
yahoo journals, bing journals, International Journal of Engineering Research and Development, google journals, hard copy of journal
Ijarcet vol-2-issue-7-2389-2397

This document describes the design and implementation of a voice activated, programmable, multipurpose robot. The robot uses a microcontroller and various integrated circuits to enable voice control and wireless control via dual-tone multi-frequency signaling. The document provides details on the circuit design and components, software design in C and Assembly languages, and concludes the robot demonstrates satisfactory performance for applications such as guiding visitors or patients.
International Journal of Engineering Research and Development (IJERD)

journal publishing, how to publish research paper, Call For research paper, international journal, publishing a paper, IJERD, journal of science and technology, how to get a research paper published, publishing a paper, publishing of journal, publishing of research paper, reserach and review articles, IJERD Journal, How to publish your research paper, publish research paper, open access engineering journal, Engineering journal, Mathemetics journal, Physics journal, Chemistry journal, Computer Engineering, Computer Science journal, how to submit your paper, peer reviw journal, indexed journal, reserach and review articles, engineering journal, www.ijerd.com, research journals,
yahoo journals, bing journals, International Journal of Engineering Research and Development, google journals, hard copy of journal
1850 1854

The document discusses using machine learning algorithms like Random Forest and k-Nearest Neighbors for intrusion detection. It analyzes the KDD Cup 1999 intrusion detection dataset to classify network traffic as normal or different types of attacks. The proposed model uses Random Forest for feature selection and k-Nearest Neighbors for classification to more accurately detect known and unknown attacks. Experimental results show the combined approach achieves better detection rates than other algorithms alone, especially for novel attacks not present in training data. Further combining the algorithms into a two-stage process may yield even higher accuracy.
Neeraj Resume

Neeraj Chhangani provides his curriculum vitae, which includes information about his education, work experience, skills, and interests. He has a diploma in ITI and worked for 3 years as a Senior Operator in slickline operations for Schlumberger Asia Services Limited. His skills include knowledge of rigging up and down slickline equipment, tool preparation, and retrieving and reporting memory gauge data. He is interested in accepting challenges and traveling.
1776 1779

This document summarizes a proposed network attack alerting system that aims to reduce redundant alerts from intrusion detection systems (IDS). The system uses both network-based and host-based IDS to detect attacks launched using the Backtrack penetration testing tool on a virtual network environment. Well-known open source IDS tools from the Security Onion distribution are used to generate alerts. The system builds a database of alerts and defines rules to eliminate duplicate alerts for the same attack based on attributes like source/destination IP and port. It also establishes a severity classification scheme using threshold values of alerts and time to help administrators prioritize responses.
Toàn cảnh văn hóa, thể thao và du lịch – Số 1070 - vanhien.vn

Tuần tin của Bộ Văn hóa, Thể thao và Du ịch - Số 1070 - Đăng trên vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1069 - vanhien.vn

Tuần tin của Bộ Văn hóa, Thể thao và Du lịch. Đăng trên vanhien.vn
Diễn đàn văn nghệ Việt Nam-Số 3/2014-vanhien.vn

Tạp chí Diễn đàn văn nghệ Việt Nam - Số 3/2014. Đăng trên vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1067 - vanhien.vn

Tuần tin của Bộ Văn hóa, thể thao và Du lịch - Số 1067.
Đăng trên vanhien.vn
Diễn đàn văn nghệ Việt Nam - Số 2.

Tiếng nói của Liên hiệp các Hội Văn học nghệ thuật Việt Nam.
Số 2/2014 - Đăng trên Văn hiến Việt Nam (vanhien.vn).
Toàn cảnh văn hóa, thể thao và du lịch – Số 1066

Tuần tin của Bộ Văn hóa, Thể thao và Du lịch - Số 1066.
Đăng trên vanhien.vn.
Toàn cảnh văn hóa, thể thao và du lịch – Số 1065 - vanhien.vn

Tuần tin của Bộ Văn hóa, thể thao và Du lịch - Số 1065.
Đăng trên vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1064 –vanhien.vn

Tuần tin của Bộ Văn hóa, Thể thao và Du lịch - Số 1064.
More Related Content
Viewers also liked
1918 1923

This document proposes a new digital watermarking technique that utilizes Discrete Wavelet Transform (DWT), Discrete Cosine Transform (DCT), Singular Value Decomposition (SVD), and Arnold Transform. It embeds a watermark image into the high frequency subbands of a cover image after applying DWT and SVD. During extraction, the receiver applies the same transforms to extract the watermark. The technique aims to provide improved robustness against various attacks like noise, compression, filtering etc. compared to existing techniques that use these transforms individually or in pairs. The document analyzes the proposed technique's performance based on the extracted watermark's peak signal-to-noise ratio after subjecting the watermarked image to different attacks.
1771 1775

The document discusses a system for integrating structured and unstructured data from heterogeneous environments. The system uses OGSA-DAI services and the Globus Toolkit to provide an abstraction layer that allows database operations on both structured data from databases and unstructured file-based data. It generates metadata from unstructured data and configures the abstraction layer to query across the different data sources. This provides users an integrated view of both structured and unstructured data through a single interface.
Ijarcet vol-2-issue-3-891-896

This document discusses a digital image processing (DIP) based system for identifying defects in industrial materials like steel rods. Images of reference and test samples are taken and compared using techniques like thresholding, histograms, and cell segmentation in MATLAB. Defects are identified by variations between the images. The system is implemented on an FPGA for hardware acceleration. Images of steel rods with and without defects are compared to demonstrate the system's ability to detect cracks. The DIP based approach can replace manual inspection and provides faster quality evaluation of industrial materials compared to software-only methods.
Elmwood guide to the living trust

This information is not intended to be legal advice. Please see our full disclaimer inside the document
International Journal of Engineering Research and Development (IJERD)

journal publishing, how to publish research paper, Call For research paper, international journal, publishing a paper, IJERD, journal of science and technology, how to get a research paper published, publishing a paper, publishing of journal, publishing of research paper, reserach and review articles, IJERD Journal, How to publish your research paper, publish research paper, open access engineering journal, Engineering journal, Mathemetics journal, Physics journal, Chemistry journal, Computer Engineering, Computer Science journal, how to submit your paper, peer reviw journal, indexed journal, reserach and review articles, engineering journal, www.ijerd.com, research journals,
yahoo journals, bing journals, International Journal of Engineering Research and Development, google journals, hard copy of journal
Ijarcet vol-2-issue-7-2389-2397

This document describes the design and implementation of a voice activated, programmable, multipurpose robot. The robot uses a microcontroller and various integrated circuits to enable voice control and wireless control via dual-tone multi-frequency signaling. The document provides details on the circuit design and components, software design in C and Assembly languages, and concludes the robot demonstrates satisfactory performance for applications such as guiding visitors or patients.
International Journal of Engineering Research and Development (IJERD)

journal publishing, how to publish research paper, Call For research paper, international journal, publishing a paper, IJERD, journal of science and technology, how to get a research paper published, publishing a paper, publishing of journal, publishing of research paper, reserach and review articles, IJERD Journal, How to publish your research paper, publish research paper, open access engineering journal, Engineering journal, Mathemetics journal, Physics journal, Chemistry journal, Computer Engineering, Computer Science journal, how to submit your paper, peer reviw journal, indexed journal, reserach and review articles, engineering journal, www.ijerd.com, research journals,
yahoo journals, bing journals, International Journal of Engineering Research and Development, google journals, hard copy of journal
1850 1854

The document discusses using machine learning algorithms like Random Forest and k-Nearest Neighbors for intrusion detection. It analyzes the KDD Cup 1999 intrusion detection dataset to classify network traffic as normal or different types of attacks. The proposed model uses Random Forest for feature selection and k-Nearest Neighbors for classification to more accurately detect known and unknown attacks. Experimental results show the combined approach achieves better detection rates than other algorithms alone, especially for novel attacks not present in training data. Further combining the algorithms into a two-stage process may yield even higher accuracy.
Neeraj Resume

Neeraj Chhangani provides his curriculum vitae, which includes information about his education, work experience, skills, and interests. He has a diploma in ITI and worked for 3 years as a Senior Operator in slickline operations for Schlumberger Asia Services Limited. His skills include knowledge of rigging up and down slickline equipment, tool preparation, and retrieving and reporting memory gauge data. He is interested in accepting challenges and traveling.
1776 1779

This document summarizes a proposed network attack alerting system that aims to reduce redundant alerts from intrusion detection systems (IDS). The system uses both network-based and host-based IDS to detect attacks launched using the Backtrack penetration testing tool on a virtual network environment. Well-known open source IDS tools from the Security Onion distribution are used to generate alerts. The system builds a database of alerts and defines rules to eliminate duplicate alerts for the same attack based on attributes like source/destination IP and port. It also establishes a severity classification scheme using threshold values of alerts and time to help administrators prioritize responses.
Viewers also liked (13)
International Journal of Engineering Research and Development (IJERD)

International Journal of Engineering Research and Development (IJERD)
International Journal of Engineering Research and Development (IJERD)

International Journal of Engineering Research and Development (IJERD)
More from longvanhien
Toàn cảnh văn hóa, thể thao và du lịch – Số 1070 - vanhien.vn

Tuần tin của Bộ Văn hóa, Thể thao và Du ịch - Số 1070 - Đăng trên vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1069 - vanhien.vn

Tuần tin của Bộ Văn hóa, Thể thao và Du lịch. Đăng trên vanhien.vn
Diễn đàn văn nghệ Việt Nam-Số 3/2014-vanhien.vn

Tạp chí Diễn đàn văn nghệ Việt Nam - Số 3/2014. Đăng trên vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1067 - vanhien.vn

Tuần tin của Bộ Văn hóa, thể thao và Du lịch - Số 1067.
Đăng trên vanhien.vn
Diễn đàn văn nghệ Việt Nam - Số 2.

Tiếng nói của Liên hiệp các Hội Văn học nghệ thuật Việt Nam.
Số 2/2014 - Đăng trên Văn hiến Việt Nam (vanhien.vn).
Toàn cảnh văn hóa, thể thao và du lịch – Số 1066

Tuần tin của Bộ Văn hóa, Thể thao và Du lịch - Số 1066.
Đăng trên vanhien.vn.
Toàn cảnh văn hóa, thể thao và du lịch – Số 1065 - vanhien.vn

Tuần tin của Bộ Văn hóa, thể thao và Du lịch - Số 1065.
Đăng trên vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1064 –vanhien.vn

Tuần tin của Bộ Văn hóa, Thể thao và Du lịch - Số 1064.
Toàn cảnh văn hóa, thể thao và du lịch – Số 1063 –vanhien.vn

Tuần tin của bộ Văn hóa, Thể thao và Du lịch - Số 1063.
Đăng trên vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1062 –vanhien.vn

Tuần tin của Bộ Văn hóa, Thể thao và Du lịch - Số 1062. Đăng trên vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1059 –vanhien.vn

Tuần tin của Bộ Văn hóa, Thể thao và Du lịch - Số 1059.
Đăng trên vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1058 –vanhien.vn

Tuần tin của Bộ Văn hóa, Thể thao và Du lịch - Số 1058.
Đăng trên vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1057 –vanhien.vn

Tuần tin của Bộ Văn hóa, Thể thao và Du lịch - Số 1057.
Đăng trên vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1056 –vanhien.vn

Tuần tin của Bộ Văn hóa, Thể thao và Du lịch - số 1056. Đăng trên vanhien,vn.
More from longvanhien (20)
Toàn cảnh văn hóa, thể thao và du lịch – Số 1070 - vanhien.vn

Toàn cảnh văn hóa, thể thao và du lịch – Số 1070 - vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1069 - vanhien.vn

Toàn cảnh văn hóa, thể thao và du lịch – Số 1069 - vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1067 - vanhien.vn

Toàn cảnh văn hóa, thể thao và du lịch – Số 1067 - vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1065 - vanhien.vn

Toàn cảnh văn hóa, thể thao và du lịch – Số 1065 - vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1064 –vanhien.vn

Toàn cảnh văn hóa, thể thao và du lịch – Số 1064 –vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1063 –vanhien.vn

Toàn cảnh văn hóa, thể thao và du lịch – Số 1063 –vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1062 –vanhien.vn

Toàn cảnh văn hóa, thể thao và du lịch – Số 1062 –vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1059 –vanhien.vn

Toàn cảnh văn hóa, thể thao và du lịch – Số 1059 –vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1058 –vanhien.vn

Toàn cảnh văn hóa, thể thao và du lịch – Số 1058 –vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1057 –vanhien.vn

Toàn cảnh văn hóa, thể thao và du lịch – Số 1057 –vanhien.vn
Toàn cảnh văn hóa, thể thao và du lịch – Số 1056 –vanhien.vn

Toàn cảnh văn hóa, thể thao và du lịch – Số 1056 –vanhien.vn
Bìa Diễn đàn Văn nghệ Việt Nam - Số 5/2013
- 1. N¨m thø XXII