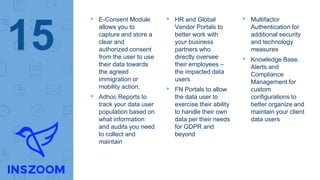
The document discusses the implications of the GDPR (General Data Protection Regulation) for U.S. businesses, emphasizing the need for compliance and awareness of customer expectations regarding data privacy. It highlights InsZoom's commitment to GDPR readiness, including its data security practices, technical measures, and compliance tools designed to facilitate customer needs. The document underscores the evolving landscape of data privacy and the importance of maintaining high standards of security and transparency for personal data handling.