Addressing Data Security Issues in Digital Evaluation
•
0 likes•4 views
We, at learning spiral provide you with revolutionary digital services to transform your evaluation process.
Report
Share
Report
Share
Download to read offline
Recommended
Addressing Data Security in Digital Evaluation

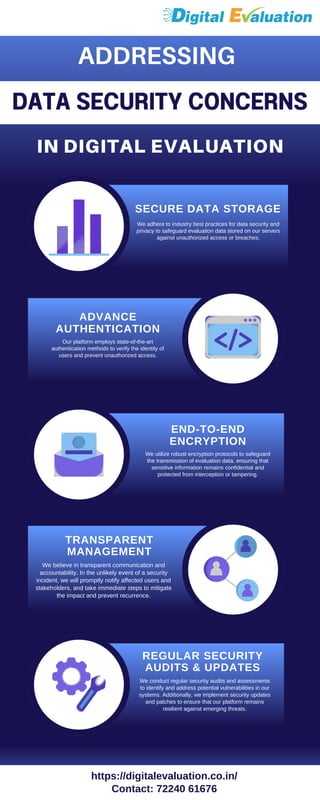
Addressing data security concerns in digital evaluation is crucial to protect sensitive information. Ensuring robust security measures, such as encryption and access controls, can safeguard data integrity and privacy, fostering trust and compliance in digital assessment systems.
ADDRESSING DATA SECURITY CONCERNS IN DIGITAL EVALUATION

Addressing data security concerns in digital evaluation is crucial to protect sensitive information. Ensuring robust security measures, such as encryption and access controls, can safeguard data integrity and privacy, fostering trust and compliance in digital assessment systems.
Trust stream penetration testing 1.12

Trust Stream are expert penetration testers based in Edinburgh. They ensure their client's IT systems meet and exceed the highest standards for compliance and security.
CyberKnight capabilties

Cyber Knight is one of The leading IT Security firms specializing in providing Enterprise Risk Services and Defensive Security Services. We has a proven track record of assisting numerous global organizations obtain and maintain desired levels of online security.
Best Practices for Robust IT Network Security

It is imperative to secure an IT network, particularly in a business-friendly state like New Jersey
Essential Managed Cloud Security Measures Every Business Needs

In today's rapidly evolving digital landscape, safeguarding your business's data and operations in the cloud is paramount. This guide outlines the critical managed cloud security measures that every business should implement to ensure a secure and resilient cloud environment.
https://katprotech.com/services/cloud-security-managed-services/
Exploring the Seven Key Attributes of Security Testing.pdf

Security Testing Service is a crucial process that evaluates the resilience of an organization's digital assets against potential cyberattacks. In this blog, we will delve into the seven key attributes of security testing and understand their significance in safeguarding our digital world.
Database Security Assessment | Database Security Assessment Services

Database Security Assessment involves a comprehensive evaluation of the security measures implemented to protect databases. This process includes regular updates and patching, robust access controls, encryption of sensitive data, continuous monitoring of database activity, routine security audits, and a solid backup and recovery plan. By adhering to these best practices and fostering a security-aware culture, organizations can fortify their databases against potential threats, ensuring the integrity and confidentiality of their valuable information.
Recommended
Addressing Data Security in Digital Evaluation

Addressing data security concerns in digital evaluation is crucial to protect sensitive information. Ensuring robust security measures, such as encryption and access controls, can safeguard data integrity and privacy, fostering trust and compliance in digital assessment systems.
ADDRESSING DATA SECURITY CONCERNS IN DIGITAL EVALUATION

Addressing data security concerns in digital evaluation is crucial to protect sensitive information. Ensuring robust security measures, such as encryption and access controls, can safeguard data integrity and privacy, fostering trust and compliance in digital assessment systems.
Trust stream penetration testing 1.12

Trust Stream are expert penetration testers based in Edinburgh. They ensure their client's IT systems meet and exceed the highest standards for compliance and security.
CyberKnight capabilties

Cyber Knight is one of The leading IT Security firms specializing in providing Enterprise Risk Services and Defensive Security Services. We has a proven track record of assisting numerous global organizations obtain and maintain desired levels of online security.
Best Practices for Robust IT Network Security

It is imperative to secure an IT network, particularly in a business-friendly state like New Jersey
Essential Managed Cloud Security Measures Every Business Needs

In today's rapidly evolving digital landscape, safeguarding your business's data and operations in the cloud is paramount. This guide outlines the critical managed cloud security measures that every business should implement to ensure a secure and resilient cloud environment.
https://katprotech.com/services/cloud-security-managed-services/
Exploring the Seven Key Attributes of Security Testing.pdf

Security Testing Service is a crucial process that evaluates the resilience of an organization's digital assets against potential cyberattacks. In this blog, we will delve into the seven key attributes of security testing and understand their significance in safeguarding our digital world.
Database Security Assessment | Database Security Assessment Services

Database Security Assessment involves a comprehensive evaluation of the security measures implemented to protect databases. This process includes regular updates and patching, robust access controls, encryption of sensitive data, continuous monitoring of database activity, routine security audits, and a solid backup and recovery plan. By adhering to these best practices and fostering a security-aware culture, organizations can fortify their databases against potential threats, ensuring the integrity and confidentiality of their valuable information.
Cyber Security | Information Security

Lumiverse Solutions Pvt. Ltd. is a leading cyber security company, dedicated to safeguarding businesses from evolving cyber threats. We offer industry-standard security services, including vulnerability assessments, to protect your websites and data. With over 5 years of experience serving clients around the globe across multiple industries like banking and financial healthcare, government. we provide information security, digital forensic investigation, security assessment, consulting, IT solutions, and corporate technical training. Trust us to secure your digital assets. Know more at www.lumiversesolutions.com
Simplifying IT Security for GDPR Compliance: Sharique M Rizvi 

Implementing Security Technology for Compliance - GDPR
Sharique M Rizvi
Data Security Considerations in Data Migration with the Right Tools.pdf

In an era where data is not just a commodity but the backbone of business operations, the process of data migration holds paramount importance. Whether it's transitioning to a new system, upgrading existing infrastructure, or simply restructuring data architecture, the integrity and security of data must be preserved throughout the migration process. This is where Ask On Data, a leading data migration tool, emerges as a reliable ally in safeguarding sensitive information while ensuring a seamless transition.
braincavesoft-com-cyber-security.pdf

At BrainCave Software, we understand the critical importance of safeguarding your digital assets against cyber threats.
braincavesoft-com-cyber-security (1).pdf

Protect Your Business With Our Robust Cyber Security Services!
AURISEG CONSULTING PRIVATE LIMITED 

Auriseg is a leading information security company
based out of Chennai, India With a spread over footprint
and rich experience, Auriseg provides complete
information security solutions specializing in
implementing holistic, integrated, and sustainable
information protection programs. We are a full service
information security provider committed to delivering
technology solutions to ensure impenetrable security
to more than 100 customers across India and
USA.
Security and Privacy Considerations in the Open Network for Digital Commerce.pdf

Security and privacy considerations play a vital role in the Open Network for Digital Commerce, ensuring the protection of users' sensitive information and enabling secure transactions in the open network. In this open network, robust security measures are implemented to safeguard against potential threats and unauthorized access. Privacy considerations in digital commerce are of utmost importance, with stringent protocols in place to protect personal data and ensure compliance with privacy regulations.
Guide: Security and Compliance

At Survey Analytics, nothing is more paramount than the security of your valuable data. We go to great lengths to ensure that your proprietary information is secure at all times. In this guide you can see an overview of our security compliance as well as our certificates.
Security Testing

Security Testing is a process to determine how well a system protects against unauthorized internal or external access or wilful damage. It is performed to check whether there is any information leakage in the sense by encrypting the application or using wide range of software etc..
Seguridad de la información 

Seguridad de la Información Gestión y Aplicación de protocolos de Seguridad Informática
https://spotintelligence.com

security whitepaper from <a href="https://spotintelligence.com">Spot Intelligence </a> https://spotintelligence.com
Data Security and Compliance in Enterprise Cloud Migration.pdf

This article will explore the best practices organizations should follow regarding data security and compliance during the enterprise cloud migration process.
Xcina MSSP Overview

Key monitoring and reporting requirements for organisations looking for Managed Security Services to mitigate cyber risk.
The Hacker Playbook: How to Think like a Cybercriminal to Reduce Risk

In this presentation from their joint webinar, security experts and trainers at CQURE, Greg Tworek and Mike Jankowski-Lorek, help you put on your hacker cap to better identify dangerous vulnerabilities, strengthen your systems, and STOP the data breaches that litter the news sites today. They will also demonstrate how to exploit systems and how (from the hacker perspective) this can be proactively mitigated.
Catch the full on-demand webinar here:
https://www.beyondtrust.com/resources/webinar/hackers-playbook-think-like-cybercriminal-reduce-risk/?access_code=de936e36f25bb91acaae7593959af3c1
TYPES OF DATA ANNOTATION THAT ARE USED.pdf

Data annotation involves labeling datasets with relevant tags or labels to provide context for machine learning models. It ensures accurate and structured data, enabling effective model training for tasks like image recognition or sentiment analysis. Data annotation is essential for developing reliable and efficient AI systems
DATA LABELING : AREAS OF APPLICATION.pdf

Data labeling involves annotating datasets with relevant tags or labels to provide context for machine learning models. It ensures accurate and structured data, facilitating model training for tasks like image recognition or natural language processing. Effective data labeling is crucial for building reliable and efficient AI systems.
More Related Content
Similar to Addressing Data Security Issues in Digital Evaluation
Cyber Security | Information Security

Lumiverse Solutions Pvt. Ltd. is a leading cyber security company, dedicated to safeguarding businesses from evolving cyber threats. We offer industry-standard security services, including vulnerability assessments, to protect your websites and data. With over 5 years of experience serving clients around the globe across multiple industries like banking and financial healthcare, government. we provide information security, digital forensic investigation, security assessment, consulting, IT solutions, and corporate technical training. Trust us to secure your digital assets. Know more at www.lumiversesolutions.com
Simplifying IT Security for GDPR Compliance: Sharique M Rizvi 

Implementing Security Technology for Compliance - GDPR
Sharique M Rizvi
Data Security Considerations in Data Migration with the Right Tools.pdf

In an era where data is not just a commodity but the backbone of business operations, the process of data migration holds paramount importance. Whether it's transitioning to a new system, upgrading existing infrastructure, or simply restructuring data architecture, the integrity and security of data must be preserved throughout the migration process. This is where Ask On Data, a leading data migration tool, emerges as a reliable ally in safeguarding sensitive information while ensuring a seamless transition.
braincavesoft-com-cyber-security.pdf

At BrainCave Software, we understand the critical importance of safeguarding your digital assets against cyber threats.
braincavesoft-com-cyber-security (1).pdf

Protect Your Business With Our Robust Cyber Security Services!
AURISEG CONSULTING PRIVATE LIMITED 

Auriseg is a leading information security company
based out of Chennai, India With a spread over footprint
and rich experience, Auriseg provides complete
information security solutions specializing in
implementing holistic, integrated, and sustainable
information protection programs. We are a full service
information security provider committed to delivering
technology solutions to ensure impenetrable security
to more than 100 customers across India and
USA.
Security and Privacy Considerations in the Open Network for Digital Commerce.pdf

Security and privacy considerations play a vital role in the Open Network for Digital Commerce, ensuring the protection of users' sensitive information and enabling secure transactions in the open network. In this open network, robust security measures are implemented to safeguard against potential threats and unauthorized access. Privacy considerations in digital commerce are of utmost importance, with stringent protocols in place to protect personal data and ensure compliance with privacy regulations.
Guide: Security and Compliance

At Survey Analytics, nothing is more paramount than the security of your valuable data. We go to great lengths to ensure that your proprietary information is secure at all times. In this guide you can see an overview of our security compliance as well as our certificates.
Security Testing

Security Testing is a process to determine how well a system protects against unauthorized internal or external access or wilful damage. It is performed to check whether there is any information leakage in the sense by encrypting the application or using wide range of software etc..
Seguridad de la información 

Seguridad de la Información Gestión y Aplicación de protocolos de Seguridad Informática
https://spotintelligence.com

security whitepaper from <a href="https://spotintelligence.com">Spot Intelligence </a> https://spotintelligence.com
Data Security and Compliance in Enterprise Cloud Migration.pdf

This article will explore the best practices organizations should follow regarding data security and compliance during the enterprise cloud migration process.
Xcina MSSP Overview

Key monitoring and reporting requirements for organisations looking for Managed Security Services to mitigate cyber risk.
The Hacker Playbook: How to Think like a Cybercriminal to Reduce Risk

In this presentation from their joint webinar, security experts and trainers at CQURE, Greg Tworek and Mike Jankowski-Lorek, help you put on your hacker cap to better identify dangerous vulnerabilities, strengthen your systems, and STOP the data breaches that litter the news sites today. They will also demonstrate how to exploit systems and how (from the hacker perspective) this can be proactively mitigated.
Catch the full on-demand webinar here:
https://www.beyondtrust.com/resources/webinar/hackers-playbook-think-like-cybercriminal-reduce-risk/?access_code=de936e36f25bb91acaae7593959af3c1
Similar to Addressing Data Security Issues in Digital Evaluation (20)
Simplifying IT Security for GDPR Compliance: Sharique M Rizvi 

Simplifying IT Security for GDPR Compliance: Sharique M Rizvi
Data Security Considerations in Data Migration with the Right Tools.pdf

Data Security Considerations in Data Migration with the Right Tools.pdf
Security and Privacy Considerations in the Open Network for Digital Commerce.pdf

Security and Privacy Considerations in the Open Network for Digital Commerce.pdf
How To Successfully Defend Against Irc Bots, Compromises, And Information Leaks

How To Successfully Defend Against Irc Bots, Compromises, And Information Leaks
Data Security and Compliance in Enterprise Cloud Migration.pdf

Data Security and Compliance in Enterprise Cloud Migration.pdf
The Hacker Playbook: How to Think like a Cybercriminal to Reduce Risk

The Hacker Playbook: How to Think like a Cybercriminal to Reduce Risk
More from priyanshilearningspi
TYPES OF DATA ANNOTATION THAT ARE USED.pdf

Data annotation involves labeling datasets with relevant tags or labels to provide context for machine learning models. It ensures accurate and structured data, enabling effective model training for tasks like image recognition or sentiment analysis. Data annotation is essential for developing reliable and efficient AI systems
DATA LABELING : AREAS OF APPLICATION.pdf

Data labeling involves annotating datasets with relevant tags or labels to provide context for machine learning models. It ensures accurate and structured data, facilitating model training for tasks like image recognition or natural language processing. Effective data labeling is crucial for building reliable and efficient AI systems.
ADVANTAGES OF USING: DATA ANNOTATION.pdf

Data annotation is essential for training AI models effectively. Precise labeling ensures accurate predictions, while scalability handles large datasets efficiently. Contextual understanding enhances model comprehension, and adaptability caters to diverse needs. Quality assurance processes maintain data integrity, while collaboration fosters synergy among annotators, driving innovation in AI technologies.
TYPES OF DATA ANNOTATION THAT ARE USED.pptx

Data annotation involves labeling datasets with relevant tags or labels to provide context for machine learning models. It ensures accurate and structured data, enabling effective model training for tasks like image recognition or sentiment analysis. Data annotation is essential for developing reliable and efficient AI systems
DATA LABELING: AREAS OF APPLICATION.pptx

Data labeling involves annotating datasets with relevant tags or labels to provide context for machine learning models. It ensures accurate and structured data, facilitating model training for tasks like image recognition or natural language processing. Effective data labeling is crucial for building reliable and efficient AI systems.
ADVANTAGES OF USING DATA ANNOTATION.pptx

Data annotation is essential for training AI models effectively. Precise labeling ensures accurate predictions, while scalability handles large datasets efficiently. Contextual understanding enhances model comprehension, and adaptability caters to diverse needs. Quality assurance processes maintain data integrity, while collaboration fosters synergy among annotators, driving innovation in AI technologies.
AI Data Solutions: Learning Spiral Pvt Ltd

Learning spiral has a workforce with diverse set of skills and the ability to deliver data annotation and data labeling services at scale. We have a rich history of 15+ years of handling sensitive data on a large scale. Our affordable data annotation and data labeling services provided by trained in-house dedicated professionals will ensure high quality labeled data to meet your needs.
Types of Data Annotation that can be used

Data annotation involves labeling datasets with relevant tags or labels to provide context for machine learning models. It ensures accurate and structured data, enabling effective model training for tasks like image recognition or sentiment analysis. Data annotation is essential for developing reliable and efficient AI systems.
Advantages of Data Using Annotation .pdf

Data annotation is essential for training AI models effectively. Precise labeling ensures accurate predictions, while scalability handles large datasets efficiently. Contextual understanding enhances model comprehension, and adaptability caters to diverse needs. Quality assurance processes maintain data integrity, while collaboration fosters synergy among annotators, driving innovation in AI technologies.
Services at Digital Evaluation by Learning Spiral

We offer comprehensive digital evaluation services designed to enhance efficiency and accuracy in assessments. Our solutions cater to various educational and professional needs, ensuring a seamless and effective evaluation process.
Ensuring Fairness & Equity in Digital Evaluation.pdf

Ensuring fairness and equity in digital evaluation is paramount. By implementing unbiased algorithms, inclusive design, and accessibility features, we strive to create an equitable assessment environment that accurately reflects every individual's abilities and potential.
10 BENEFITS OF DIGITAL EVALUATION BY LEARNING SPIRAL

Digital evaluation offers numerous advantages in various fields, enhancing efficiency and accuracy. It leverages technology to streamline assessment processes, providing significant benefits such as real-time feedback, improved data management, and personalized learning experiences.
Services at Digital Evaluation by Learning Spiral Pvt Ltd

We offer comprehensive digital evaluation services designed to enhance efficiency and accuracy in assessments. Our solutions cater to various educational and professional needs, ensuring a seamless and effective evaluation process.
Ensuring Fairness & Equity in Digital Evaluation.pptx

Ensuring fairness and equity in digital evaluation is paramount. By implementing unbiased algorithms, inclusive design, and accessibility features, we strive to create an equitable assessment environment that accurately reflects every individual's abilities and potential.
10 BENEFITS OF DIGITAL EVALUATION BY LEARNING SPIRAL PVT. LTD.

Digital evaluation offers numerous advantages in various fields, enhancing efficiency and accuracy. It leverages technology to streamline assessment processes, providing significant benefits such as real-time feedback, improved data management, and personalized learning experiences.
Ensuring Fairness & Equity in Digital Evaluation.pdf

We, at learning spiral provide you with revolutionary digital services to transform your evaluation process.
Learning Spiral Services for Digital Evaluation

We, at learning spiral provide you with revolutionary digital services to transform your evaluation process.
More from priyanshilearningspi (17)
Ensuring Fairness & Equity in Digital Evaluation.pdf

Ensuring Fairness & Equity in Digital Evaluation.pdf
10 BENEFITS OF DIGITAL EVALUATION BY LEARNING SPIRAL

10 BENEFITS OF DIGITAL EVALUATION BY LEARNING SPIRAL
Services at Digital Evaluation by Learning Spiral Pvt Ltd

Services at Digital Evaluation by Learning Spiral Pvt Ltd
Ensuring Fairness & Equity in Digital Evaluation.pptx

Ensuring Fairness & Equity in Digital Evaluation.pptx
10 BENEFITS OF DIGITAL EVALUATION BY LEARNING SPIRAL PVT. LTD.

10 BENEFITS OF DIGITAL EVALUATION BY LEARNING SPIRAL PVT. LTD.
Ensuring Fairness & Equity in Digital Evaluation.pdf

Ensuring Fairness & Equity in Digital Evaluation.pdf
Recently uploaded
GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...

GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...Nguyen Thanh Tu Collection
https://app.box.com/s/4hfk1xwgxnova7f4dm37birdzflj806wUnit 2- Research Aptitude (UGC NET Paper I).pdf

This slide describes the research aptitude of unit 2 in the UGC NET paper I.
How to Break the cycle of negative Thoughts

We all have good and bad thoughts from time to time and situation to situation. We are bombarded daily with spiraling thoughts(both negative and positive) creating all-consuming feel , making us difficult to manage with associated suffering. Good thoughts are like our Mob Signal (Positive thought) amidst noise(negative thought) in the atmosphere. Negative thoughts like noise outweigh positive thoughts. These thoughts often create unwanted confusion, trouble, stress and frustration in our mind as well as chaos in our physical world. Negative thoughts are also known as “distorted thinking”.
How to Create Map Views in the Odoo 17 ERP

The map views are useful for providing a geographical representation of data. They allow users to visualize and analyze the data in a more intuitive manner.
Model Attribute Check Company Auto Property

In Odoo, the multi-company feature allows you to manage multiple companies within a single Odoo database instance. Each company can have its own configurations while still sharing common resources such as products, customers, and suppliers.
The Challenger.pdf DNHS Official Publication

Read| The latest issue of The Challenger is here! We are thrilled to announce that our school paper has qualified for the NATIONAL SCHOOLS PRESS CONFERENCE (NSPC) 2024. Thank you for your unwavering support and trust. Dive into the stories that made us stand out!
Unit 8 - Information and Communication Technology (Paper I).pdf

This slides describes the basic concepts of ICT, basics of Email, Emerging Technology and Digital Initiatives in Education. This presentations aligns with the UGC Paper I syllabus.
CLASS 11 CBSE B.St Project AIDS TO TRADE - INSURANCE

Class 11 CBSE Business Studies Project ( AIDS TO TRADE - INSURANCE)
How to Make a Field invisible in Odoo 17

It is possible to hide or invisible some fields in odoo. Commonly using “invisible” attribute in the field definition to invisible the fields. This slide will show how to make a field invisible in odoo 17.
Palestine last event orientationfvgnh .pptx

An EFL lesson about the current events in Palestine. It is intended to be for intermediate students who wish to increase their listening skills through a short lesson in power point.
Ethnobotany and Ethnopharmacology ......

Ethnobotany and Ethnopharmacology:
Ethnobotany in herbal drug evaluation,
Impact of Ethnobotany in traditional medicine,
New development in herbals,
Bio-prospecting tools for drug discovery,
Role of Ethnopharmacology in drug evaluation,
Reverse Pharmacology.
Introduction to Quality Improvement Essentials

This is a presentation by Dada Robert in a Your Skill Boost masterclass organised by the Excellence Foundation for South Sudan (EFSS) on Saturday, the 25th and Sunday, the 26th of May 2024.
He discussed the concept of quality improvement, emphasizing its applicability to various aspects of life, including personal, project, and program improvements. He defined quality as doing the right thing at the right time in the right way to achieve the best possible results and discussed the concept of the "gap" between what we know and what we do, and how this gap represents the areas we need to improve. He explained the scientific approach to quality improvement, which involves systematic performance analysis, testing and learning, and implementing change ideas. He also highlighted the importance of client focus and a team approach to quality improvement.
Sectors of the Indian Economy - Class 10 Study Notes pdf

The Indian economy is classified into different sectors to simplify the analysis and understanding of economic activities. For Class 10, it's essential to grasp the sectors of the Indian economy, understand their characteristics, and recognize their importance. This guide will provide detailed notes on the Sectors of the Indian Economy Class 10, using specific long-tail keywords to enhance comprehension.
For more information, visit-www.vavaclasses.com
How to Split Bills in the Odoo 17 POS Module

Bills have a main role in point of sale procedure. It will help to track sales, handling payments and giving receipts to customers. Bill splitting also has an important role in POS. For example, If some friends come together for dinner and if they want to divide the bill then it is possible by POS bill splitting. This slide will show how to split bills in odoo 17 POS.
ESC Beyond Borders _From EU to You_ InfoPack general.pdf

ESC Beyond Borders _From EU to You_ InfoPack general.pdfFundacja Rozwoju Społeczeństwa Przedsiębiorczego
Wolontariat grupowyHome assignment II on Spectroscopy 2024 Answers.pdf

Answers to Home assignment on UV-Visible spectroscopy: Calculation of wavelength of UV-Visible absorption
Recently uploaded (20)
GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...

GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...
Unit 8 - Information and Communication Technology (Paper I).pdf

Unit 8 - Information and Communication Technology (Paper I).pdf
CLASS 11 CBSE B.St Project AIDS TO TRADE - INSURANCE

CLASS 11 CBSE B.St Project AIDS TO TRADE - INSURANCE
aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa

aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa
Sectors of the Indian Economy - Class 10 Study Notes pdf

Sectors of the Indian Economy - Class 10 Study Notes pdf
ESC Beyond Borders _From EU to You_ InfoPack general.pdf

ESC Beyond Borders _From EU to You_ InfoPack general.pdf
Home assignment II on Spectroscopy 2024 Answers.pdf

Home assignment II on Spectroscopy 2024 Answers.pdf
Addressing Data Security Issues in Digital Evaluation
- 1. ADDRESSING DATA SECURITY CONCERNS IN DIGITAL EVALUATION SECURE DATA STORAGE We adhere to industry best practices for data security and privacy to safeguard evaluation data stored on our servers against unauthorized access or breaches. ADVANCE AUTHENTICATION Our platform employs state-of-the-art authentication methods to verify the identity of users and prevent unauthorized access. END-TO-END ENCRYPTION We utilize robust encryption protocols to safeguard the transmission of evaluation data, ensuring that sensitive information remains confidential and protected from interception or tampering. TRANSPARENT MANAGEMENT REGULAR SECURITY AUDITS & UPDATES We conduct regular security audits and assessments to identify and address potential vulnerabilities in our systems. Additionally, we implement security updates and patches to ensure that our platform remains resilient against emerging threats. We believe in transparent communication and accountability. In the unlikely event of a security incident, we will promptly notify affected users and stakeholders, and take immediate steps to mitigate the impact and prevent recurrence. https://digitalevaluation.co.in/ Contact: 72240 61676