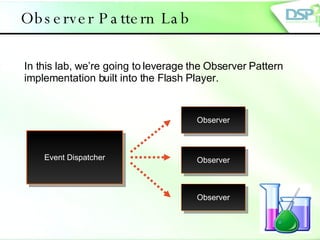
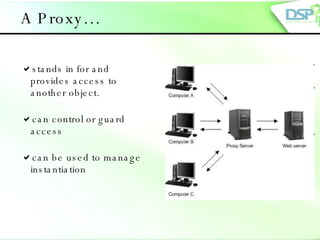
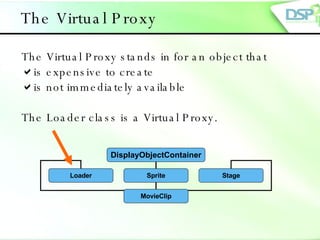
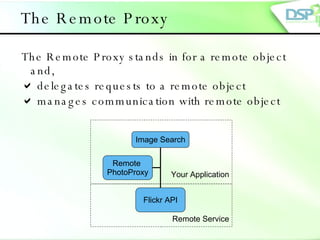
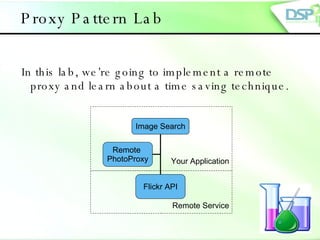
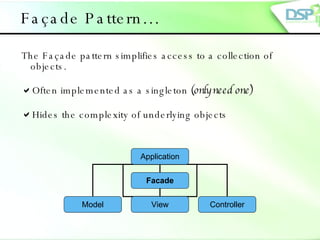
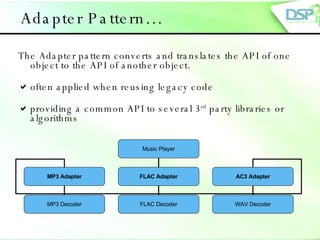
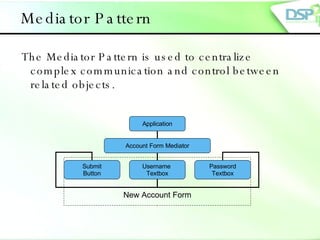
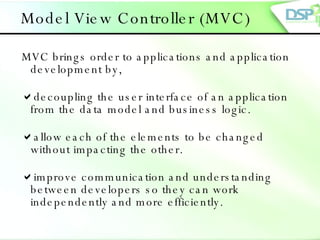
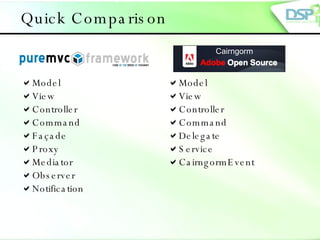
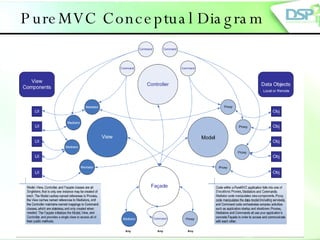
The document provides an overview of various design patterns in ActionScript 3, including Singleton, Command, Observer, Proxy, Facade, Adapter, and Mediator patterns. It emphasizes how these patterns solve common design problems, facilitate development workflow, and improve communication among development teams. Each pattern is explained with examples and related concepts, leading into a discussion about the Model-View-Controller (MVC) framework.

![DSP-IP Contact information Download slides at: www.dsp-ip.com Course materials & lecture request Projects development services: Adi Yakov Training Manager [email_address] +972-9-8651933 www.dsp-ip.com Mail : [email_address] Phone: +972-9-8850956, Fax : +972-50- 8962910 Alona Ashkenazi Development Services [email_address] +972-9-8850956](https://image.slidesharecdn.com/actionscript-design-patterns-and-platforms-1227020326115061-9/85/ActionScript-Design-Patterns-32-320.jpg)