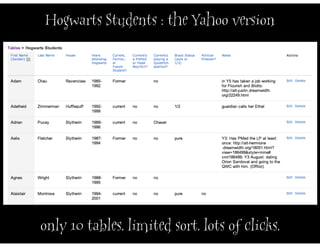
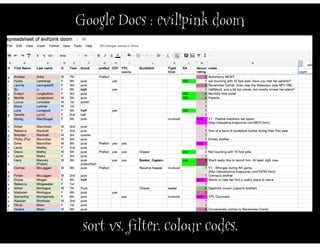
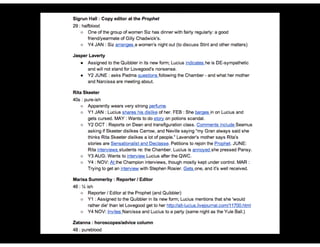
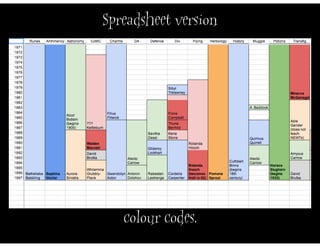
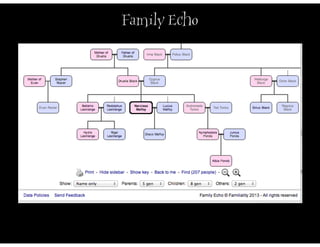
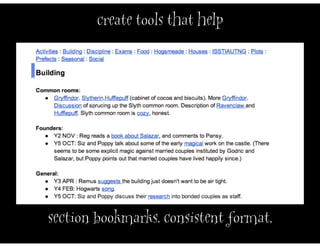
The document discusses managing collaborative projects, particularly in a fan fiction context, focusing on the use of free tools for data management and communication among participants. It outlines challenges related to technology access and organization while emphasizing the importance of clear communication and goal setting. Additionally, it highlights the use of various platforms and methods for coordinating efforts, including calendars and checklists.