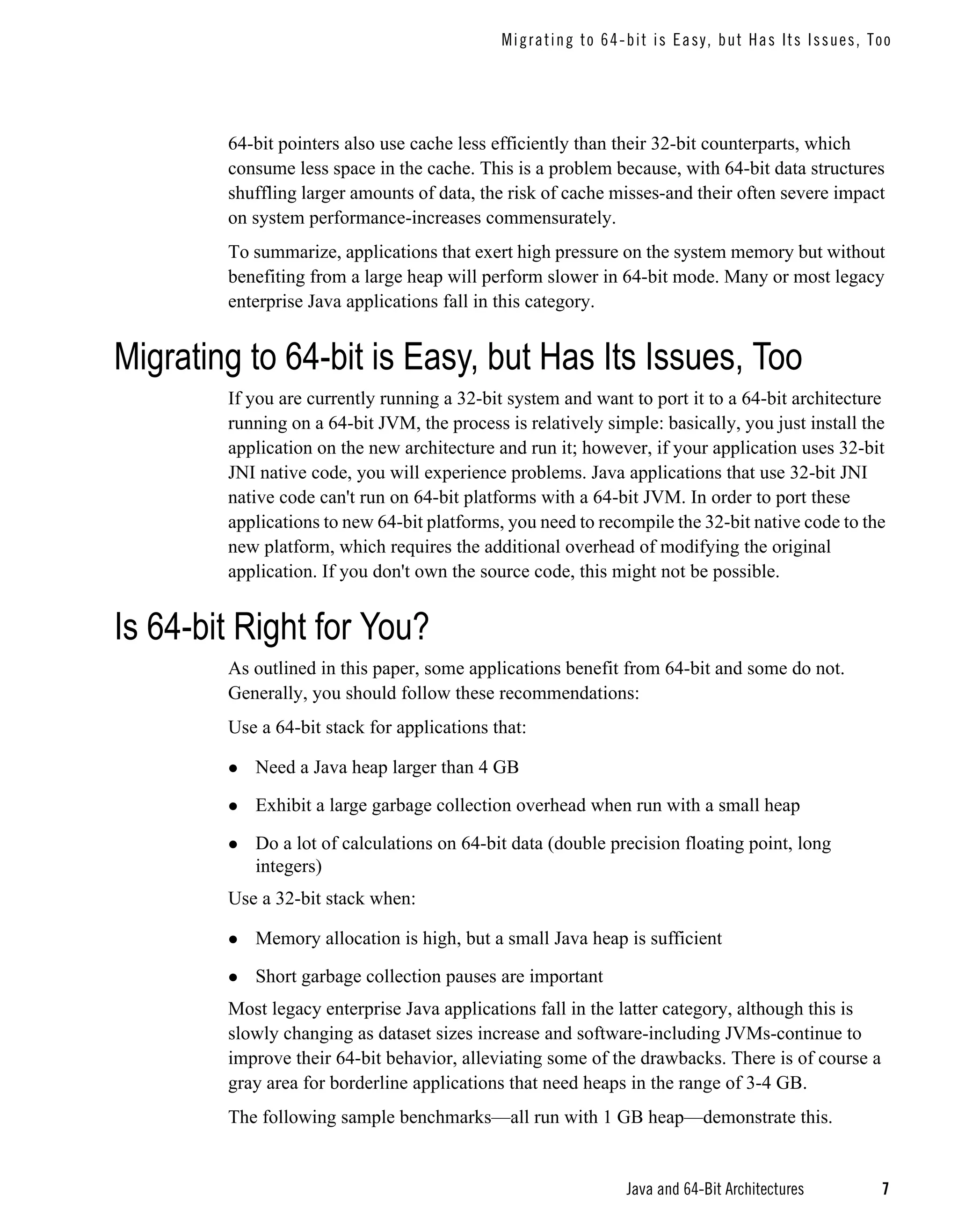
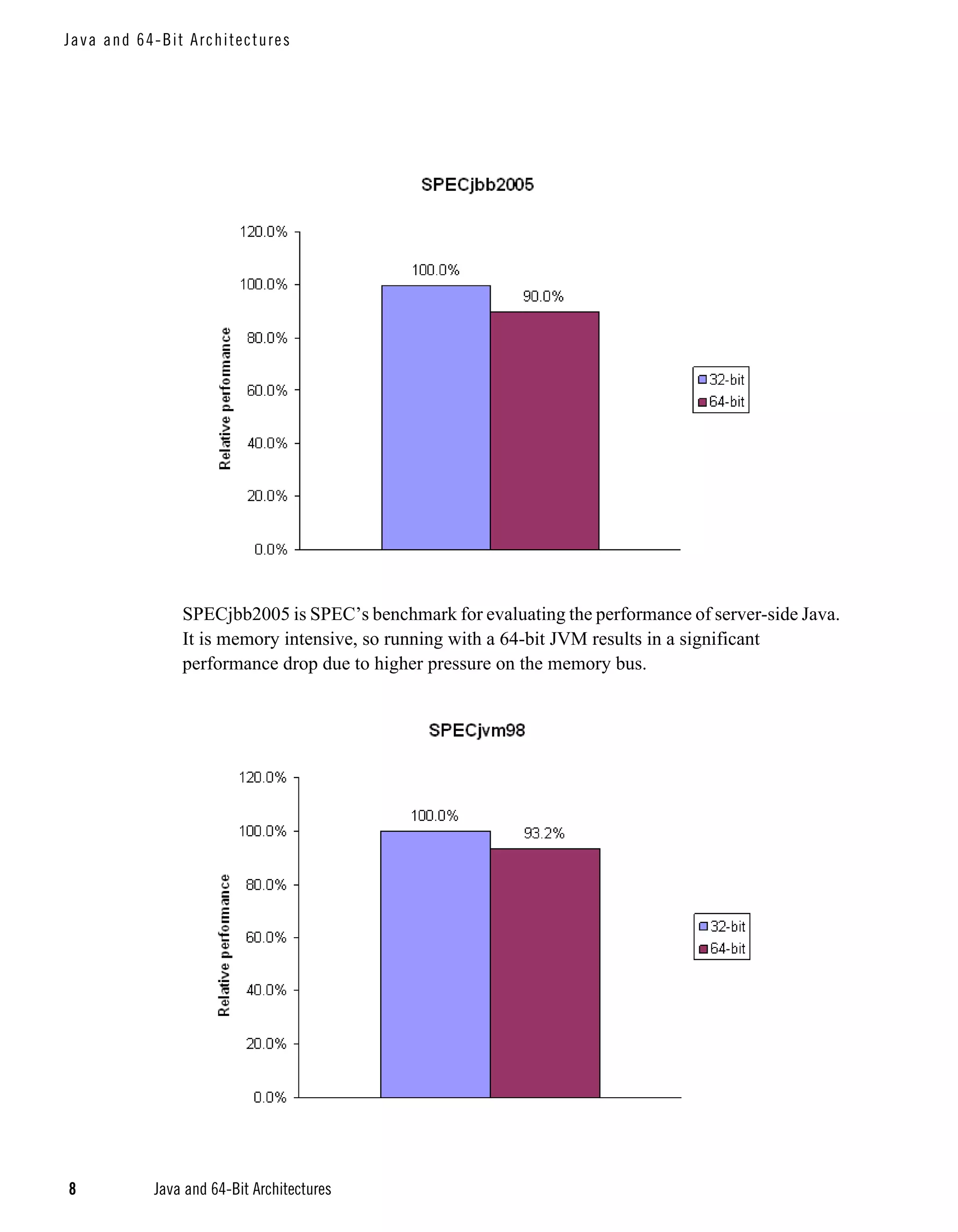
This document discusses the benefits of 64-bit architectures for Java applications. 64-bit systems can access and manipulate vastly more memory than 32-bit systems, allowing Java applications to process extremely large datasets. Migrating a Java application to 64-bit is usually simple by switching to a 64-bit Java Virtual Machine, though applications using native code may require additional porting work. While 64-bit systems enable processing of large datasets, they also increase memory usage. The document provides guidelines to help determine whether a 64-bit or 32-bit system is best for a given application.