5 Ultimate Things You Should Know About Dark Web
•
0 likes•55 views
If you're curious about accessing the dark web safely, then I suggest you take a look at these five things that can help you browse the dark web safely without any hassle. Check it out now.
Report
Share
Report
Share
Download to read offline
Recommended
Dark Web.pptx

Dark Web insights regarding how to use the dark web and how to benefit from it. The reason i did this is to do the awareness of Dark Web as a concept. Try to learn it and to use it in a good way because it's very important.
Darknet

Presentation on Darkweb/Darknet/DeepWeb.
Basic Knowledge and and Brief Presentation on the Hidden world of darknet.
Idea on How the search engine works.
What is Torr and How it vWorks.
Market of hiddenweb, bitcoin, and how it is used for illegal puchase of drugsd and child pornography.
ABOUT DARK WEB 

Its shows about 'Dark Web', where it came from. And how it works.
It shows whether it is legal and illegal and also it show case study.
It tells about punishments from using dark web. it explains how danger the dark web is?. it tells about risky contents that are found in dark web. it also tells about the dangers of dark web to users who are using it. it explains legal actions, for who are enter into dark web. it also gives example like case study.
deep web.pdf

When you hear about the deep web, you might think of illicit activities like drugs and other criminal products being sold on hidden websites or phishing scams. But that isn’t really what the deep web is all about. In fact, you access the deep web every day without even realizing it.Please visit here https://deepweb.blog/ for more information.
Deep Web Stories_ Tales from the Unindexed Internet.pdf

In this comprehensive article, we delve into the enigmatic world of the Deep Web, uncovering its mysteries, its significance, and the stories that remain hidden from mainstream search engines.
Recommended
Dark Web.pptx

Dark Web insights regarding how to use the dark web and how to benefit from it. The reason i did this is to do the awareness of Dark Web as a concept. Try to learn it and to use it in a good way because it's very important.
Darknet

Presentation on Darkweb/Darknet/DeepWeb.
Basic Knowledge and and Brief Presentation on the Hidden world of darknet.
Idea on How the search engine works.
What is Torr and How it vWorks.
Market of hiddenweb, bitcoin, and how it is used for illegal puchase of drugsd and child pornography.
ABOUT DARK WEB 

Its shows about 'Dark Web', where it came from. And how it works.
It shows whether it is legal and illegal and also it show case study.
It tells about punishments from using dark web. it explains how danger the dark web is?. it tells about risky contents that are found in dark web. it also tells about the dangers of dark web to users who are using it. it explains legal actions, for who are enter into dark web. it also gives example like case study.
deep web.pdf

When you hear about the deep web, you might think of illicit activities like drugs and other criminal products being sold on hidden websites or phishing scams. But that isn’t really what the deep web is all about. In fact, you access the deep web every day without even realizing it.Please visit here https://deepweb.blog/ for more information.
Deep Web Stories_ Tales from the Unindexed Internet.pdf

In this comprehensive article, we delve into the enigmatic world of the Deep Web, uncovering its mysteries, its significance, and the stories that remain hidden from mainstream search engines.
Dark Web Site.pdf

While the dark web remains a mysterious and complex aspect of cyberspace, it is crucial for individuals to understand its workings. The existence of dark web sites poses both opportunities and risks, highlighting the need for concerted efforts in striking a balance between privacy advocacy and tackling cybercrime. Awareness combined with effective measures can help ensure a safer digital landscape. Please visit here https://darkweblinks.guide/ for more information.
Dw communication

This presentation was made by collecting all publicly available materials and it is purely for educational purpose. Author wants to thank each and every contributor of pictures, video, text in this presentation.
Dark Web Kristin Finklea Specialist in Domestic Se

Dark Web
Kristin Finklea
Specialist in Domestic Security
March 10, 2017
Congressional Research Service
7-5700
www.crs.gov
R44101
Dark Web
Congressional Research Service
Summary
The layers of the Internet go far beyond the surface content that many can easily access in their
daily searches. The other content is that of the Deep Web, content that has not been indexed by
traditional search engines such as Google. The furthest corners of the Deep Web, segments known
as the Dark Web, contain content that has been intentionally concealed. The Dark Web may be
used for legitimate purposes as well as to conceal criminal or otherwise malicious activities. It is
the exploitation of the Dark Web for illegal practices that has garnered the interest of officials and
policymakers.
Individuals can access the Dark Web by using special software such as Tor (short for The Onion
Router). Tor relies upon a network of volunteer computers to route users’ web traffic through a
series of other users’ computers such that the traffic cannot be traced to the original user. Some
developers have created tools—such as Tor2web—that may allow individuals access to Tor-
hosted content without downloading and installing the Tor software, though accessing the Dark
Web through these means does not anonymize activity. Once on the Dark Web, users often
navigate it through directories such as the “Hidden Wiki,” which organizes sites by category,
similar to Wikipedia. Individuals can also search the Dark Web with search engines, which may
be broad, searching across the Deep Web, or more specific, searching for contraband like illicit
drugs, guns, or counterfeit money. While on the Dark Web, individuals may communicate
through means such as secure email, web chats, or personal messaging hosted on Tor. Though
tools such as Tor aim to anonymize content and activity, researchers and security experts are
constantly developing means by which certain hidden services or individuals could be identified
or “deanonymized.”
Anonymizing services such as Tor have been used for legal and illegal activities ranging from
maintaining privacy to selling illegal goods—mainly purchased with Bitcoin or other digital
currencies. They may be used to circumvent censorship, access blocked content, or maintain the
privacy of sensitive communications or business plans. However, a range of malicious actors,
from criminals to terrorists to state-sponsored spies, can also leverage cyberspace and the Dark
Web can serve as a forum for conversation, coordination, and action. It is unclear how much of
the Dark Web is dedicated to serving a particular illicit market at any one time, and, because of
the anonymity of services such as Tor, it is even further unclear how much traffic is actually
flowing to any given site.
Just as criminals can rely upon the anonymity of the Dark Web, so too can the law enforcement,
military, and intellige ...
Deep web

Right below the surface of where the iceberg meets underwater is the deep web.
It’s comprised of the same general hostnames as sites on the surface web, but along with the extension of those domains.
This is the specific URL of your Facebook Messenger thread with a friend, or the Department of Justice’s public archival material, or Harvard’s internal communications system. The deep web is the majority of the internet as a whole.
Dark web sites - Exploring the Dark Web, Dark Web Sites, and the Elusive Link...

Dark web sites - Exploring the Dark Web, Dark Web Sites, and the Elusive Link...Auto Parts Wholesale Online
Dark WebMensworldhq.com what happens on the dark web

What happens on the dark web? How do you access it, what's on it and is it a safe place to visit? If you've ever wondered... find out here....
Dark Web and Threat Intelligence

The Dark Web consists of World Wide Web content existing on darknets, which are overlay networks that use the Internet, but require specific software, configurations, or authorization to access. The Dark Web forms a small part of the Deep Web - the part of the web not indexed by search engines - although sometimes the term, Deep Web, is mistakenly used to refer specifically to the Dark Web. Credit: Marlabs Inc
What Is Dark Web.docx

The dark web is a part of the internet that is intentionally hidden and requires special tools, software, or authorization to access.
What is the Dark Web & How to Access itWe explain the Dark Web, .docx

What is the Dark Web & How to Access it
We explain the Dark Web, how it differs from the Deep Web, and how to get on the Dark Web using the Tor browser.
By Matt Egan | 30 Jan 2019
The internet is a much, much bigger place than you probably realise. You know about Facebook, Google, BBC iPlayer and Amazon, but do you really know what's lurking beyond those user-friendly and respectable websites?
This is but a tiny corner of the internet, and the Dark Web and the Deep Web loom in much shadier corners. Using Tor you can access them, but should you even want to visit the Dark Web or the Deep Web?
Let's take a tour to help you make up your mind.What is the Dark Web?
The Dark Web is a term that refers specifically to a collection of websites that exist on an encrypted network and cannot be found by using traditional search engines or visited by using traditional browsers.
Almost all sites on the so-called Dark Web hide their identity using the Tor encryption tool. You may know Tor for its ability to hide your identity and activity. You can use Tor to spoof your location so it appears you're in a different country to where you're really located, making it much like using a VPN service.
When a website is run through Tor it has much the same effect.
Indeed, it multiplies the effect. To visit a site on the Dark Web that is using Tor encryption, the web user needs to be using Tor. Just as the end user's IP address is bounced through several layers of encryption to appear to be at another IP address on the Tor network, so is that of the website.
There are several layers of magnitude more secrecy than the already secret act of using Tor to visit a website on the open internet - for both parties.
Thus, sites on the Dark Web can be visited by anyone, but it is very difficult to work out who is behind the sites. And it can be dangerous if you slip up and your identity is discovered.
You can also read our in-depth guide to using Tor if you want to know more about using the web anonymously and sending messages securely.
Why would I want to use the Dark Web?
Not all Dark Web sites use Tor. Some use similar services such as I2P, for example the Silk Road Reloaded. But the principle remains the same. The visitor has to use the same encryption tool as the site and - crucially - know where to find the site, in order to type in the URL and visit.
Infamous examples of Dark Web sites include the Silk Road and its offspring. The Silk Road was (and maybe still is) a website for the buying and selling of recreational drugs, and a lot more scary things besides. But there are also legitimate uses for the Dark Web. (Also see: Is it legal to buy drugs online?)
People operating within closed, totalitarian societies can use the Dark Web to communicate with the outside world. And given recent revelations about US- and UK government snooping on web use, you may feel it is sensible to take your communication on to the Dark Web.
The Dark Web hit the headlines in August 2015 ( ...
test test test test testtest test testtest test testtest test testtest test ...

salamsasalamlamsalamsalamsalamsalamsalamsalamsalam
一比一原版(CSU毕业证)加利福尼亚州立大学毕业证成绩单专业办理

CSU毕业证原版定制【微信:176555708】【加利福尼亚州立大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
More Related Content
Similar to 5 Ultimate Things You Should Know About Dark Web
Dark Web Site.pdf

While the dark web remains a mysterious and complex aspect of cyberspace, it is crucial for individuals to understand its workings. The existence of dark web sites poses both opportunities and risks, highlighting the need for concerted efforts in striking a balance between privacy advocacy and tackling cybercrime. Awareness combined with effective measures can help ensure a safer digital landscape. Please visit here https://darkweblinks.guide/ for more information.
Dw communication

This presentation was made by collecting all publicly available materials and it is purely for educational purpose. Author wants to thank each and every contributor of pictures, video, text in this presentation.
Dark Web Kristin Finklea Specialist in Domestic Se

Dark Web
Kristin Finklea
Specialist in Domestic Security
March 10, 2017
Congressional Research Service
7-5700
www.crs.gov
R44101
Dark Web
Congressional Research Service
Summary
The layers of the Internet go far beyond the surface content that many can easily access in their
daily searches. The other content is that of the Deep Web, content that has not been indexed by
traditional search engines such as Google. The furthest corners of the Deep Web, segments known
as the Dark Web, contain content that has been intentionally concealed. The Dark Web may be
used for legitimate purposes as well as to conceal criminal or otherwise malicious activities. It is
the exploitation of the Dark Web for illegal practices that has garnered the interest of officials and
policymakers.
Individuals can access the Dark Web by using special software such as Tor (short for The Onion
Router). Tor relies upon a network of volunteer computers to route users’ web traffic through a
series of other users’ computers such that the traffic cannot be traced to the original user. Some
developers have created tools—such as Tor2web—that may allow individuals access to Tor-
hosted content without downloading and installing the Tor software, though accessing the Dark
Web through these means does not anonymize activity. Once on the Dark Web, users often
navigate it through directories such as the “Hidden Wiki,” which organizes sites by category,
similar to Wikipedia. Individuals can also search the Dark Web with search engines, which may
be broad, searching across the Deep Web, or more specific, searching for contraband like illicit
drugs, guns, or counterfeit money. While on the Dark Web, individuals may communicate
through means such as secure email, web chats, or personal messaging hosted on Tor. Though
tools such as Tor aim to anonymize content and activity, researchers and security experts are
constantly developing means by which certain hidden services or individuals could be identified
or “deanonymized.”
Anonymizing services such as Tor have been used for legal and illegal activities ranging from
maintaining privacy to selling illegal goods—mainly purchased with Bitcoin or other digital
currencies. They may be used to circumvent censorship, access blocked content, or maintain the
privacy of sensitive communications or business plans. However, a range of malicious actors,
from criminals to terrorists to state-sponsored spies, can also leverage cyberspace and the Dark
Web can serve as a forum for conversation, coordination, and action. It is unclear how much of
the Dark Web is dedicated to serving a particular illicit market at any one time, and, because of
the anonymity of services such as Tor, it is even further unclear how much traffic is actually
flowing to any given site.
Just as criminals can rely upon the anonymity of the Dark Web, so too can the law enforcement,
military, and intellige ...
Deep web

Right below the surface of where the iceberg meets underwater is the deep web.
It’s comprised of the same general hostnames as sites on the surface web, but along with the extension of those domains.
This is the specific URL of your Facebook Messenger thread with a friend, or the Department of Justice’s public archival material, or Harvard’s internal communications system. The deep web is the majority of the internet as a whole.
Dark web sites - Exploring the Dark Web, Dark Web Sites, and the Elusive Link...

Dark web sites - Exploring the Dark Web, Dark Web Sites, and the Elusive Link...Auto Parts Wholesale Online
Dark WebMensworldhq.com what happens on the dark web

What happens on the dark web? How do you access it, what's on it and is it a safe place to visit? If you've ever wondered... find out here....
Dark Web and Threat Intelligence

The Dark Web consists of World Wide Web content existing on darknets, which are overlay networks that use the Internet, but require specific software, configurations, or authorization to access. The Dark Web forms a small part of the Deep Web - the part of the web not indexed by search engines - although sometimes the term, Deep Web, is mistakenly used to refer specifically to the Dark Web. Credit: Marlabs Inc
What Is Dark Web.docx

The dark web is a part of the internet that is intentionally hidden and requires special tools, software, or authorization to access.
What is the Dark Web & How to Access itWe explain the Dark Web, .docx

What is the Dark Web & How to Access it
We explain the Dark Web, how it differs from the Deep Web, and how to get on the Dark Web using the Tor browser.
By Matt Egan | 30 Jan 2019
The internet is a much, much bigger place than you probably realise. You know about Facebook, Google, BBC iPlayer and Amazon, but do you really know what's lurking beyond those user-friendly and respectable websites?
This is but a tiny corner of the internet, and the Dark Web and the Deep Web loom in much shadier corners. Using Tor you can access them, but should you even want to visit the Dark Web or the Deep Web?
Let's take a tour to help you make up your mind.What is the Dark Web?
The Dark Web is a term that refers specifically to a collection of websites that exist on an encrypted network and cannot be found by using traditional search engines or visited by using traditional browsers.
Almost all sites on the so-called Dark Web hide their identity using the Tor encryption tool. You may know Tor for its ability to hide your identity and activity. You can use Tor to spoof your location so it appears you're in a different country to where you're really located, making it much like using a VPN service.
When a website is run through Tor it has much the same effect.
Indeed, it multiplies the effect. To visit a site on the Dark Web that is using Tor encryption, the web user needs to be using Tor. Just as the end user's IP address is bounced through several layers of encryption to appear to be at another IP address on the Tor network, so is that of the website.
There are several layers of magnitude more secrecy than the already secret act of using Tor to visit a website on the open internet - for both parties.
Thus, sites on the Dark Web can be visited by anyone, but it is very difficult to work out who is behind the sites. And it can be dangerous if you slip up and your identity is discovered.
You can also read our in-depth guide to using Tor if you want to know more about using the web anonymously and sending messages securely.
Why would I want to use the Dark Web?
Not all Dark Web sites use Tor. Some use similar services such as I2P, for example the Silk Road Reloaded. But the principle remains the same. The visitor has to use the same encryption tool as the site and - crucially - know where to find the site, in order to type in the URL and visit.
Infamous examples of Dark Web sites include the Silk Road and its offspring. The Silk Road was (and maybe still is) a website for the buying and selling of recreational drugs, and a lot more scary things besides. But there are also legitimate uses for the Dark Web. (Also see: Is it legal to buy drugs online?)
People operating within closed, totalitarian societies can use the Dark Web to communicate with the outside world. And given recent revelations about US- and UK government snooping on web use, you may feel it is sensible to take your communication on to the Dark Web.
The Dark Web hit the headlines in August 2015 ( ...
Similar to 5 Ultimate Things You Should Know About Dark Web (20)
Dark web sites - Navigating the Depths of Secrecy, Sites, and Links.pdf

Dark web sites - Navigating the Depths of Secrecy, Sites, and Links.pdf
Dark Web Kristin Finklea Specialist in Domestic Se

Dark Web Kristin Finklea Specialist in Domestic Se
Dark web sites - Exploring the Dark Web, Dark Web Sites, and the Elusive Link...

Dark web sites - Exploring the Dark Web, Dark Web Sites, and the Elusive Link...
Dark web sites -Unveiling the Dark Web and its Enigmatic Links.pdf

Dark web sites -Unveiling the Dark Web and its Enigmatic Links.pdf
What is the Dark Web & How to Access itWe explain the Dark Web, .docx

What is the Dark Web & How to Access itWe explain the Dark Web, .docx
Journey into the Shadows A Beginner's Guide to the Dark Web.pptx

Journey into the Shadows A Beginner's Guide to the Dark Web.pptx
Recently uploaded
test test test test testtest test testtest test testtest test testtest test ...

salamsasalamlamsalamsalamsalamsalamsalamsalamsalam
一比一原版(CSU毕业证)加利福尼亚州立大学毕业证成绩单专业办理

CSU毕业证原版定制【微信:176555708】【加利福尼亚州立大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
History+of+E-commerce+Development+in+China-www.cfye-commerce.shop

History+of+E-commerce+Development+in+China-www.cfye-commerce.shop
急速办(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单原版一模一样

原版纸张【微信:741003700 】【(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
How to Use Contact Form 7 Like a Pro.pptx

Contact Form 7 is a popular plugins for WordPress. This is an introduction into its features and usage.
一比一原版(SLU毕业证)圣路易斯大学毕业证成绩单专业办理

SLU毕业证原版定制【微信:176555708】【圣路易斯大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
The+Prospects+of+E-Commerce+in+China.pptx

The Prospects of E-commerce in China,www.cfye-commerce.shop
一比一原版(LBS毕业证)伦敦商学院毕业证成绩单专业办理

LBS毕业证原版定制【微信:176555708】【伦敦商学院毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
This 7-second Brain Wave Ritual Attracts Money To You.!

Discover the power of a simple 7-second brain wave ritual that can attract wealth and abundance into your life. By tapping into specific brain frequencies, this technique helps you manifest financial success effortlessly. Ready to transform your financial future? Try this powerful ritual and start attracting money today!
APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024

Ellisha Heppner, Grant Management Lead, presented an update on APNIC Foundation to the PNG DNS Forum held from 6 to 10 May, 2024 in Port Moresby, Papua New Guinea.
1比1复刻(bath毕业证书)英国巴斯大学毕业证学位证原版一模一样

原版纸张【微信:741003700 】【(bath毕业证书)英国巴斯大学毕业证学位证】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines

Talk presented at Kubernetes Community Day, New York, May 2024.
Technical summary of Multi-Cluster Kubernetes Networking architectures with focus on 4 key topics.
1) Key patterns for Multi-cluster architectures
2) Architectural comparison of several OSS/ CNCF projects to address these patterns
3) Evolution trends for the APIs of these projects
4) Some design recommendations & guidelines for adopting/ deploying these solutions.
Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx

Brad Spiegel Macon GA’s journey exemplifies the profound impact that one individual can have on their community. Through his unwavering dedication to digital inclusion, he’s not only bridging the gap in Macon but also setting an example for others to follow.
1.Wireless Communication System_Wireless communication is a broad term that i...

Wireless communication involves the transmission of information over a distance without the help of wires, cables or any other forms of electrical conductors.
Wireless communication is a broad term that incorporates all procedures and forms of connecting and communicating between two or more devices using a wireless signal through wireless communication technologies and devices.
Features of Wireless Communication
The evolution of wireless technology has brought many advancements with its effective features.
The transmitted distance can be anywhere between a few meters (for example, a television's remote control) and thousands of kilometers (for example, radio communication).
Wireless communication can be used for cellular telephony, wireless access to the internet, wireless home networking, and so on.
Internet-Security-Safeguarding-Your-Digital-World (1).pptx

# Internet Security: Safeguarding Your Digital World
In the contemporary digital age, the internet is a cornerstone of our daily lives. It connects us to vast amounts of information, provides platforms for communication, enables commerce, and offers endless entertainment. However, with these conveniences come significant security challenges. Internet security is essential to protect our digital identities, sensitive data, and overall online experience. This comprehensive guide explores the multifaceted world of internet security, providing insights into its importance, common threats, and effective strategies to safeguard your digital world.
## Understanding Internet Security
Internet security encompasses the measures and protocols used to protect information, devices, and networks from unauthorized access, attacks, and damage. It involves a wide range of practices designed to safeguard data confidentiality, integrity, and availability. Effective internet security is crucial for individuals, businesses, and governments alike, as cyber threats continue to evolve in complexity and scale.
### Key Components of Internet Security
1. **Confidentiality**: Ensuring that information is accessible only to those authorized to access it.
2. **Integrity**: Protecting information from being altered or tampered with by unauthorized parties.
3. **Availability**: Ensuring that authorized users have reliable access to information and resources when needed.
## Common Internet Security Threats
Cyber threats are numerous and constantly evolving. Understanding these threats is the first step in protecting against them. Some of the most common internet security threats include:
### Malware
Malware, or malicious software, is designed to harm, exploit, or otherwise compromise a device, network, or service. Common types of malware include:
- **Viruses**: Programs that attach themselves to legitimate software and replicate, spreading to other programs and files.
- **Worms**: Standalone malware that replicates itself to spread to other computers.
- **Trojan Horses**: Malicious software disguised as legitimate software.
- **Ransomware**: Malware that encrypts a user's files and demands a ransom for the decryption key.
- **Spyware**: Software that secretly monitors and collects user information.
### Phishing
Phishing is a social engineering attack that aims to steal sensitive information such as usernames, passwords, and credit card details. Attackers often masquerade as trusted entities in email or other communication channels, tricking victims into providing their information.
### Man-in-the-Middle (MitM) Attacks
MitM attacks occur when an attacker intercepts and potentially alters communication between two parties without their knowledge. This can lead to the unauthorized acquisition of sensitive information.
### Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks
Recently uploaded (20)
test test test test testtest test testtest test testtest test testtest test ...

test test test test testtest test testtest test testtest test testtest test ...
History+of+E-commerce+Development+in+China-www.cfye-commerce.shop

History+of+E-commerce+Development+in+China-www.cfye-commerce.shop
This 7-second Brain Wave Ritual Attracts Money To You.!

This 7-second Brain Wave Ritual Attracts Money To You.!
APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024

APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024
Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines

Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines
Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx

Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx
guildmasters guide to ravnica Dungeons & Dragons 5...

guildmasters guide to ravnica Dungeons & Dragons 5...
1.Wireless Communication System_Wireless communication is a broad term that i...

1.Wireless Communication System_Wireless communication is a broad term that i...
Internet-Security-Safeguarding-Your-Digital-World (1).pptx

Internet-Security-Safeguarding-Your-Digital-World (1).pptx
5 Ultimate Things You Should Know About Dark Web
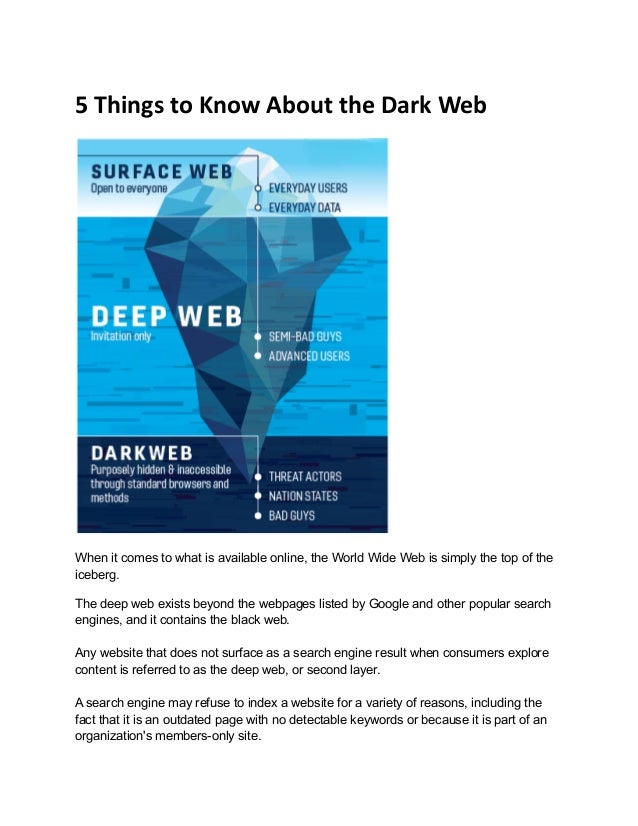
- 1. 5 Things to Know About the Dark Web When it comes to what is available online, the World Wide Web is simply the top of the iceberg. The deep web exists beyond the webpages listed by Google and other popular search engines, and it contains the black web. Any website that does not surface as a search engine result when consumers explore content is referred to as the deep web, or second layer. A search engine may refuse to index a website for a variety of reasons, including the fact that it is an outdated page with no detectable keywords or because it is part of an organization's members-only site.
- 2. The deep web could also be used to store sensitive and confidential material, such as legal or scientific documents, medical records, and competitor information. The dark web is a subset of the deep web that contains purposely hidden websites that can only be accessed with an encrypted browser such as The Onion Router, also known as Tor. Here are some things to be aware of when it comes to accessing the black market or dark web. 1. You must know exactly what you're looking for. "A distinct perspective and skill set are required on the dark web," explains Peraton vice president John M. "There are no standard search engines or algorithms to aid users; instead, they must be patient to study and hunt for the data they seek." The user must also verify the accuracy of material acquired on particular sites and establish that the sources are legitimate on the dark web. Outside of links shared publicly by others, there is no possibility to stumble into websites—every activity must be planned. Sites, website pages, and forums go up and down in a matter of days, providing another layer of complexity to navigation that distinguishes the dark web from the surface web. 2. Infecting your computer while exploring the dark web is simple. Users are less protected on the dark web because it is uncontrolled. As a result, infecting your computer is as simple as clicking links or downloading data. John M. advises that "many of the websites accessible using a Tor browser are packed with malware." "If you're going to access the black market or dark web, do so on a machine that you can re-image when you're done."
- 3. He also points out that viewing some information on the dark web may violate federal law, even if the person does so unintentionally. 4. The dark web has a few advantages. In ways that the surface web often fails to do, the dark web can help secure users' privacy. Users who are avoiding government censorship, for example, can share information about what is going on in their nation. Whistleblowers frequently use the dark web to recruit partners who can help them disseminate their secrets more widely. When the COVID-19 outbreak first broke out in Wuhan, China, information about the outreach was hidden, and doctors were forbidden from speaking out about the hazard. Concerned about the virus's potential spread, Chinese internet users submitted updates on the black web, knowing that their authorities would have a much harder time tracing the material. 5. Rather of static websites, many dark web sites are interactive forums. Locked-down forums abound on the dark web, where information is shared and traded. Because admission is by invitation only, the average internet user will be excluded from this environment. On the dark web, these discussion rooms are where the more sinister activities take place. As a result, to get the true scoop, intelligence gathering often necessitates personal participation in these chat platforms. Anonymous chat users are frequently tracked by federal agencies in order to gather information for investigations or piece together the identification of a suspect.
- 4. Although the black web is only a small part of the deep web, it is a source of significant concern and caution. Using a Tor browser and secure VPN to surf safely, troves of vital information can be unearthed to prevent future harm. A company's or government agency's ability to detect and protect against dark web threats is a valuable asset. Originally Published at Dev.to
