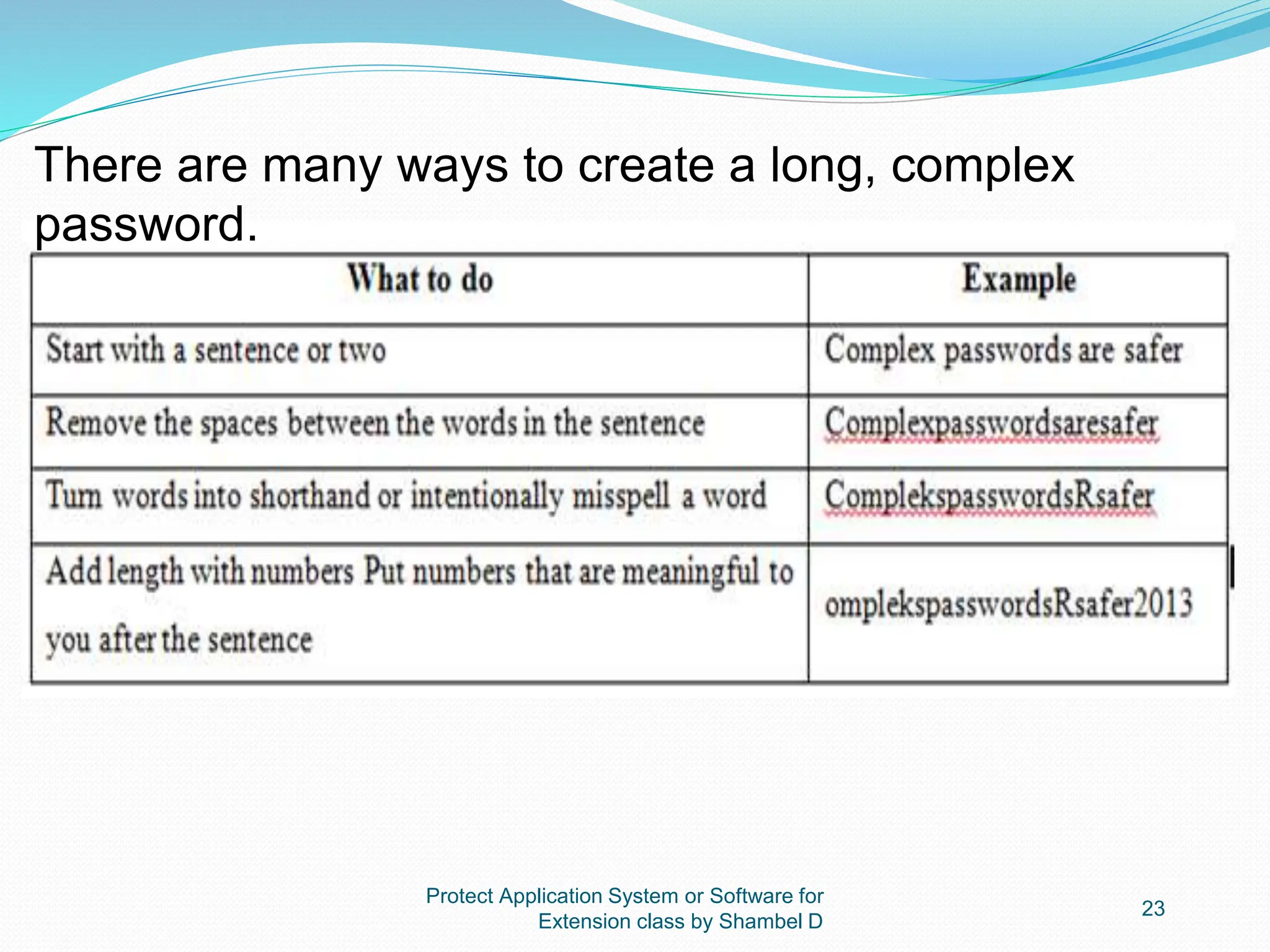
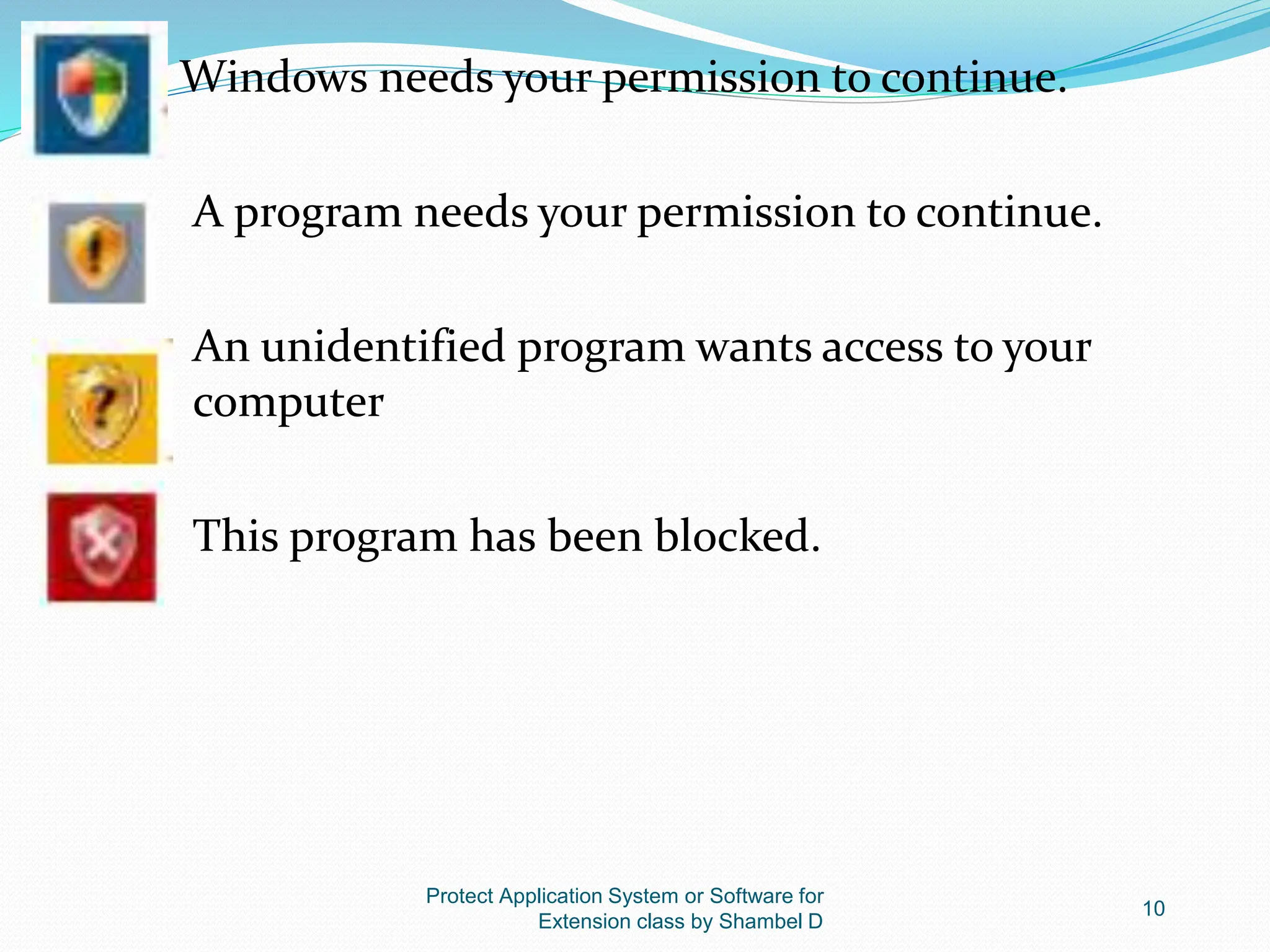
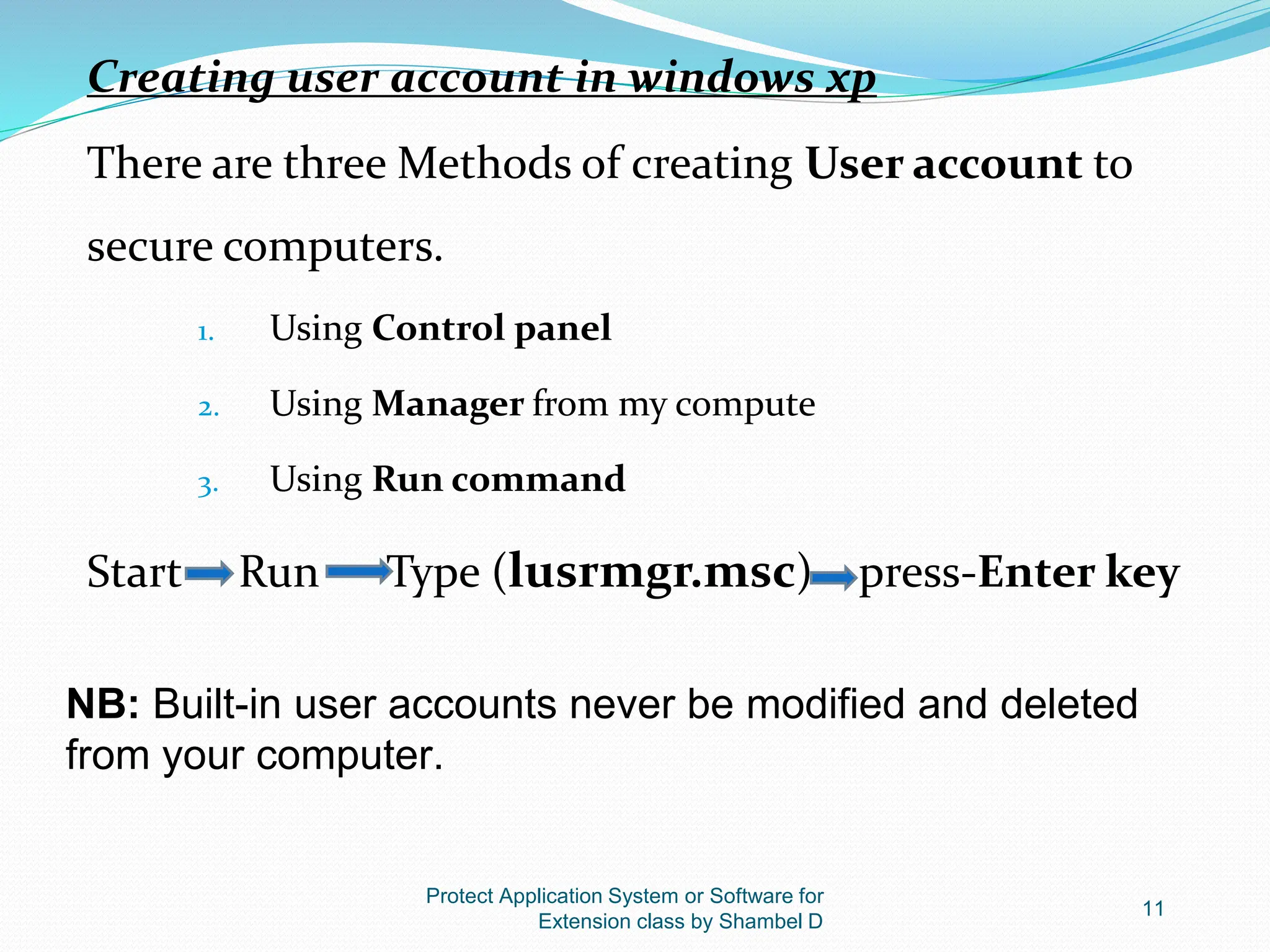
The document outlines competencies related to securing application systems and software, focusing on user account management, types of user accounts, and protective measures against malicious software. It details various types of destructive software, including viruses, worms, and Trojans, and provides guidelines on creating secure user accounts and strong passwords. Additionally, it emphasizes the importance of installing antivirus software and regularly updating security settings to prevent infections.
![Protect Application System or Software for
Extension class by Shambel D
12
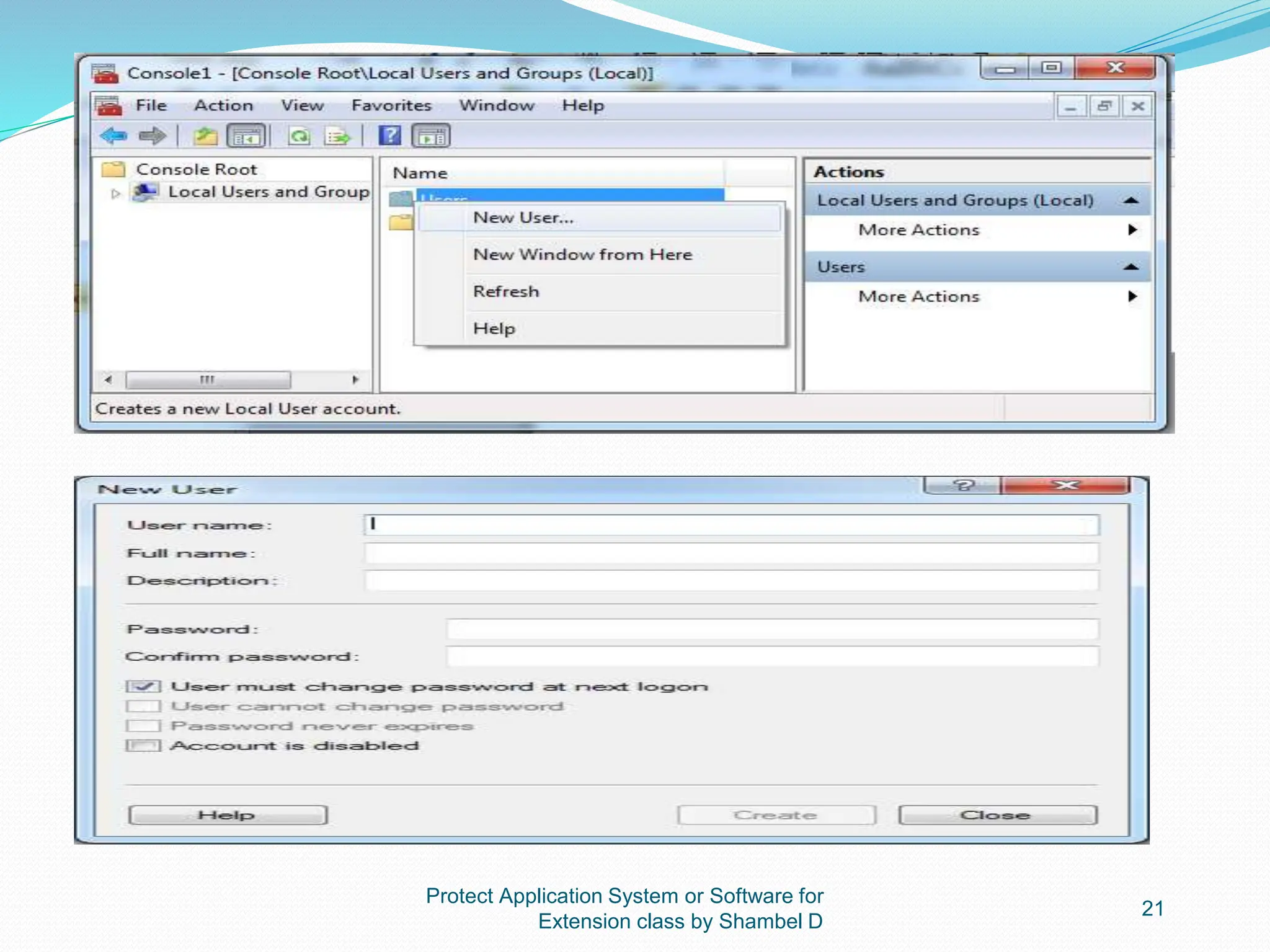
Rules for Creating User Account
- User account Name must be unique when you create user
account.
- Local user account name must be unique when you
create local user account on the computer.
- User logon name can contain up to 20 uppercase and
lowercase characters except special characters like “/
[]:,;!=+*?<>”](https://image.slidesharecdn.com/5protect-application-or-system-software2-240520075816-37dd4f26/75/5-Protect-Application-or-System-Software-2-pptx-12-2048.jpg)