2client
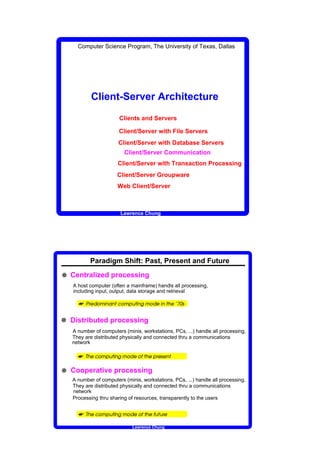
- 1. Computer Science Program, The University of Texas, Dallas Client-Server Architecture Clients and Servers Client/Server with File Servers Client/Server with Database Servers Client/Server Communication Client/Server with Transaction Processing Client/Server Groupware Web Client/Server Lawrence Chung Paradigm Shift: Past, Present and Future W Centralized processing A host computer (often a mainframe) handls all processing, including input, output, data storage and retrieval ¡ ¢ £ ¤ ¥ ¦ § ¨ § © ¤ ¥ © ¦ § ¥ ¤ £ ¢ ¦ § © ¢ W Distributed processing A number of computers (minis, workstations, PCs, ...) handle all processing, They are distributed physically and connected thru a communications network ¢ ¤ ¥ © ¦ § ¥ ¤ £ ¢ ¤ © ¢ ¡ ¢ ¢ § © W Cooperative processing A number of computers (minis, workstations, PCs, ...) handle all processing, They are distributed physically and connected thru a communications network Processing thru sharing of resources, transparently to the users ¢ ¤ ¥ © ¦ § ¥ ¤ £ ¢ ¤ © ¢ © ¡ ¢ Lawrence Chung
- 2. Clients and Servers v Basic Definition 3 Client: requests for services 3 Server: provides services 2 Service: any resource (e.g., data, type defn, file, control, object, CPU time, display device, etc.) v Typical Properties u A service request is about what is needed, and it often made abstractly It is up to the server to determine how to get the job done - the notion of module (cf. MILs, ADTs --- Larch, Z) u The ideal client/server software is independent of hardware or OS platform u The location of clients and servers are usually transparent to the user u A client may become a server; a server may become a client u A client/server system can be scaled horizontally, i.e., by adding/removing client workstations with only a slight performance impact vertically, i.e., by migrating to a larger and faster server machines or multiservers Lawrence Chung Client/Server with File Servers Client Client Client Application Application Application Centralized File Server 3 The client passes requests to the file server (software) for file records 3 Clients can reside in the same machine or separate machines (typically PCs) 3 Requests can be either local or over a network 3 Indispensable for documents, images, drawings, and other large data objects Client Client Client Application Application Application Distributed Network File Server File Server Lawrence Chung
- 3. Client/Server with Database Servers Client Client Client Application Application Application insert/update/delete Network tuple(s) Database Server 3 At present the majority of existing client/server-based software is to be found in the area of databases, and it is here that the greatest challenge to any corporation currently lies. [Richard Finkelstein, President, Performance Computing] 3 Events (violation of integrity constraints, temporal conditions, errors) trigger event handlers - implicit invocation, blackboards, events 3 A DBMS also offers features for recovery and concurrency control ! # $ % # 5 6 7 # ' ( ) 0 ( ' 1 2 3 4 ' 1 2 8 ( ' 9 @ A B ' C C C Lawrence Chung Client/Server Communication Sockets - RPCs - MOMs and ORBs Sockets 3 introduced in 1981 as the Unix BSD 4.2 generic interface 3 provide Unix-to-Unix communications over networks 3 The Windows socket API (Winsock): based on the Unix BSD 4.2 sockets interface Net_id.Host_id Internet Address Port Address 6 D E 6 G 5 % 6 % H 6 G 6 # % # Q @ 2 @ B F ' @ B A 4 ( B F ' I 4 B ( P 2 B ) A 4 2 B ( B 4 A A 2 ( 4 2 4 ( B R q 3 Principal transport service calls d ` X Y ` X T U V p ` Y S T T U V Socket (addr format, type: connection-oriented/connectionless, protocol:TCP/IP/...) W X Y ` X a S T V W W a X b ` Y U X c d ` e W U f T g h V d ` X Y ` i T U V p ` Y q d ` X Y Bind(...) ` X r f ` f ` s U d T Y U d W a t W a V U b W a t V U a a ` V Y W U a d ` r f ` T Y T u v g U V p W a t w a U a x v g U V p W a t y € ` b U Listen(...) e ` X V U a a ` V Y W U a d ` r f ` T Y s d U b Y ` r f ` f ` U d ‚ X W Y s U d U a ` u v g U V p W a t w a U a x y ƒ a W Y W X Accept(...) Y ` X V U a a ` V Y W U a ‚ W Y X d ` b U Y ` T U V p ` Y „ ` d b Connect(local_socket, remote_socket) W a X Y ` Y ` V U a a ` V Y W U a U a X T U V p ` Y … ` a i Shutdown(local_socket, remote_socket) X b ` T T X t ` Y d f X t U e ` a T U V p ` Y € ` V ` Send(local_socket, remote_socket, buffer, bytes) W e ` X b ` T T X t ` Y d f X t U e ` a T U V p ` Y q ` V Recv(local_socket, remote_socket, buffer, bytes) p X T ` Y U s T U V p ` Y T Y U T ` ` W s X a h V X a v ` d ` X i U d ‚ d W Y Y ` a u v g U V p W a t y Select(...) Lawrence Chung
- 4. Client/Server Communication Sockets - RPCs - MOMs and ORBs ¤ RPCs (Remote Procedure Calls) 3 a transparent mechanism to give the client procedure the illusion that it is making a direct call on the distant server procedure 3 stubs: local procedures (e.g., read(file_id, buffer, count)) hiding details of network comm. 3 10 steps to execute a RPC Client prog/proc Server prog/proc 10. result 5. parameter 6. server proc unmarshalling unmarshalling returns 1. stub call (unpack the msg (unpack the msg into result) into parameters); server proc call Client stub Server stub 2. parameter 4. pass the msg 7. result marshalling 9. pass the msg marshalling (collect pack (pack the result the parameters into a msg); into a msg); a sys call a sys call 3. send the call msg Transport entity Transport entity 8. send the return msg Lawrence Chung Client/Server Communication Sockets - RPCs - MOMs and ORBs u MOM (Message-Oriented Middleware) Every DAD (Distributed Application Development) needs a MOM u v u ¤ RPC ¤ MOM 3 Many-to-many messaging via queues Server Client Server Client post office-like asynchronous no fixed sequence Server Client a single queue sharable Lawrence Chung
- 5. Client/Server with Transaction Processing Client Client Client Application Application Application transactions (banking, Network reservation,...) TP Monitor Database Server 3 Transaction changeAddress (p: String, newAddress: Address) begin oldAddress - retrieve address from Person where name = p if oldAddress = newAddress then return error1 else update Person where p = name with address - newAddress end 3 Transaction increaseSalary (increment: Dollar) begin ... end Lawrence Chung Client/Server with Transaction Processing 3 Transactions are a way to make ACID operations a general commodity [Transaction Processing Concepts and Techniques, Jim Gray and Andreas Reuter, 1993] Ë Atomicity t a transaction is an indivisible unit of work t an all-or-nothing proposition t all updates to a database, displays on the clients’ screens, message queues t e.g., salary increase for all 1 million employees or none Ë Consistency t a transaction is an indivisible unit of work t S - [T | abort] - S t integrity constraints (e.g., mgr.salaray salary) Ë Isolation t a transaction’s behavior not affected by other transactions running concurrently t e.g., reserve a seat t serialization techniques Ë Durability t persistence t a transaction’s effects are permanent after it commits. † ‡ ˆ ‰ ‘ ’ “ ” • – — ˜ ” ™ ˜ – – d e f d e g g ’ ” g ” h ˆ — i ‘ f ” j ” ‘ ‘ e ™ k l e f d k – m j e f i — ˜ e n ” — – – • m j ˜ – o — h p q r ” f – m s ˜ g ™ ” e j ˜ f s h Lawrence Chung
- 6. Client/Server with Transaction Processing v Two-Phase Commit Protocol 3 To synchronize updates on different machines so that they either all fail or all succeed 3 centralize the decision to commit but giving each participant the right of veto 3 like a Christian marriage Commit Coordinator Subordinate Subordinate (Root) Node Node Prepare-to-commit Prepare-to-commit Prepare-to-commit Phase 1 Record in Log Ready-to-commit Ready-to-commit Commit Commit Commit Phase 2 Complete Complete Complete t If the subordinates have spawned pieces of the transaction on other nodes, they must propagate the prepare-to-commit-command in the first phase - a transaction tree t If any of the participants returns a transaction failure, the root node tells all its subordinates to perform a rollback Lawrence Chung Client/Server Groupware 3 Why? support for business reengineering: bcfh - maximize profit change the way people communicate with each other helps manage (and track) the product thru its various phases computer-supported cooperative work (CSCW) collaborative/workgroup computing return on investment: 16% to 1666% on a median investment of $100K [a study of 65 Notes users in 1994] 3 Five foundation technologies t u v w x y z y z { | } u ~ z v v { y } € z ‚ u ƒ } | y z { z } „ € … z } ƒ { … t „ › ‘ ‘ š ‹ œ ” ™ ™ ‡ • š ” “ œ “ – ” ” “ œ from electronic imaging (scanning, digitization, display, storage and retrieval) to document (component types: text, image, graphics, faxes, mail, voice clips, BBs) „ † ‡ ˆ ‰ Š ‹ ‡ Œ „ Ž ‘ ‹ „ ‘ ‡ “ Š ” ˆ ” “ • “ – ’ thru microphones, video windows, electronic whiteboards, controlled access to shared document „ ‘ — • ˜ ” ™ š ‹ “ – electronic scheduling of meetings, sharing calendars and to do lists, triggering events e Why not just DBMS? DBMS: highly structured data Groupware: highly unstructured data document database e Why not just TP Monitors? TP Monitors: transaction processes Groupware: (currently) not transaction-oriented in the ACID sense Lawrence Chung
- 7. Client/Server Groupware „ † ‡ ˆ ‰ Š ‹ ‡ Œ S c c d U e X g ž Ÿ ¡ Ÿ ¢ £ ¤ ¥ ¤ ¡ ¥ ¦ ¦ § ¨ © ¥ £ ¨ Ÿ ª « U X a q d ` i W Y S a T ‚ ` d S c c d X W T X g € ` r f ` T Y S a X g h T W T q f T Y U b ` d Form DB e-mail fax spreadsheet Processing query to accountg conferencing d Many office workers spend a high percentage of their time processing documents d The workflow river carries the flow of work from port to port, value being added along the way d The workflow definition must take into consideration: h Routes along which the object moves h Rules about what information is routed and when E.g., If the loan is over $100, 000, send it to the supervisor within the next hour or else send it to the next hop h Roles define job functions independently of the people who do it E.g., the supervisor role can be handled by users Adam and Eve Lawrence Chung Web Client/Server „ ¬ ‘ “ œ ” ˆ • œ ‡ “ „ ® « 1 Page 2 3 Object 4 Internet 6 TCP/IP HTML 5 Documents ¯ ¡ ° ± ¢ Ÿ ² ³ ¡ ¢ ¯ ¡ ° º ¡ ¢ » ¡ ¢ ¼ · ½ ¾ · ½ ´ µ ¶ · ¸ ¹ You select a target URL (Univeral Resource Locator - platform-independent naming scheme) 1 http ://www.utdallas.edu :80 :~ttsx19c/java/toys.html Protocol Server Address Port Number Target Resource Path 2 Brower takes the URL, embeds it inside an HTTP request, and sends it to the server h HTTP (HyperText Transfer Protocol), a stateless RPC, is used to retrieve URL-named resources 1) establishes a client/server connection, 2) transmits and receives parameters including a returned file, and 3) breaks the client/server connection STATELESS: a new connection for each user request - simple but inefficient 3 The HTTP server receives the reqest on the port, makes a socket connection, 4 The server finds the requested HTML file (Page Object) and concatenates it with status info d HTML (HyperText Markup Language) describes the structure of a Web document, provide font and graphics info, and define hyperlinks to other Web pages Internet resources) 5 The server ships back the file, and closes the connection 6 The Browser interprets the HTML command and displays the page content and invokes a helper application (e.g., xview, audiotool) Lawrence Chung
- 8. Web Client/Server „ ¿ À Á  À À Á Ä ‘ ‘ ‘ Å ‘ ‡ ˆ ™ œ ” š à ™ œ ” à ˆ œ ” Æ ” ‹ ” • œ ˆ ‡ “ • • ‡ ” ˆ • ” Ç W È È X 3 Env. Var. 1 2 É d i ` d Ê U d b 5 Internet HTTP 4 Srvr CGI TCP/IP Prog 9 6 ¯ ¡ ° ± ¢ Ÿ ² ³ ¡ ¢ 7 ´ µ ¶ · ¸ ¹ 8 ¯ ¡ ° º ¡ ¢ » ¡ ¢ ¼ · ½ ¾ · ½ You click on the form’s submit button 1 The Web browser collects the data within the form, assembles it into a string of name/value pairs, specifies a POST method, the URL of the target program in the cgi-bin directory 2 The HTTP server receives the method invocation via a socket connection 3 The server parses the message to discover that it’s a POST for the cgi-bin program - start a CGI interaction: The HTTP server sets up the environment variable (e.g., content_length), in a blackboard 4 The HTTP server starts a CGI program 5 The CGI program reads the environment variables 6 The CGI program receives the message body via the input pipe 7 The CGI program does some work, typically by interacting with a DBMS, TP Monitor 8 The CGI program returns the results via the output pipe 9 The HTTP server returns the results to the Web brower Lawrence Chung Web Client/Server „ ¿ ‘ À Ë œ ‹ ” “ œ ’ Java Applet Bytecode Verifier Class Loader 4 Java Compiler Java Just-in-Time Run-time Compiler Interpreter Applet 1 Bytecode 2 Internet 5 TCP/IP 3 ¯ ¡ ° ± ¢ Ÿ ² ³ ¡ ¢ ¯ ¡ ° º ¡ ¢ » ¡ ¢ ´ µ ¶ · ¸ ¹ ¼ · ½ ¾ · ½ 1 A Web browser requests a Java applet The Browser initiates a separate TCP/IP session to download each applet within a Web page 2 The server retrieves the requested applet 3 The server sends the applet 4 The browser loads the applet into the client’s memory and executes it A poor man’s compound document architecture The applet’s region does NOT visually integrate with the rest of the page 5 The browser deletes the applet from memory when it exits the Web page Lawrence Chung