Embed presentation
Downloaded 30 times

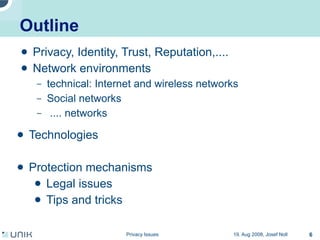
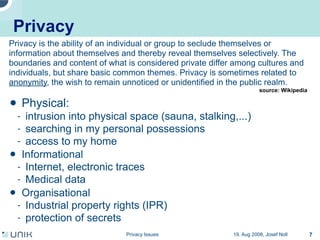

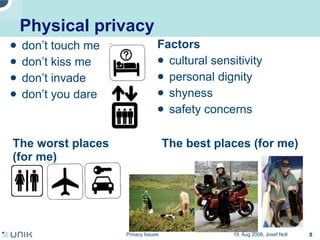
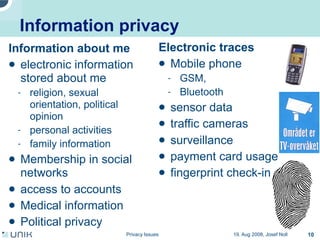


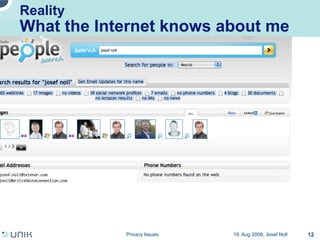
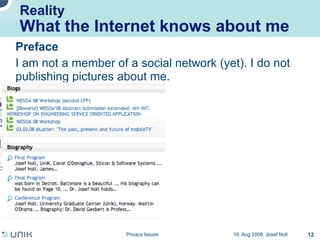
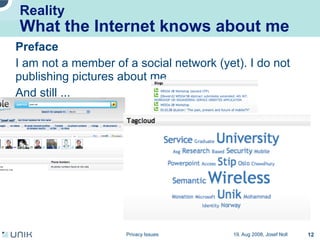
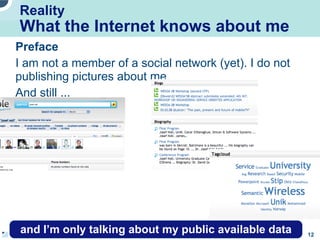
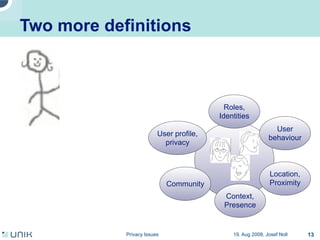
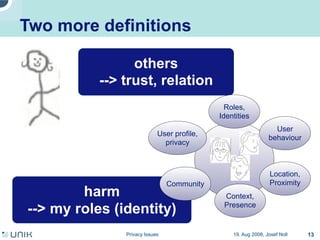
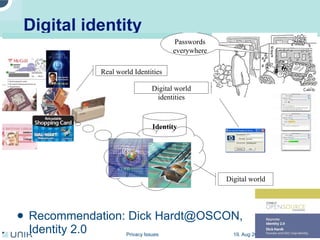
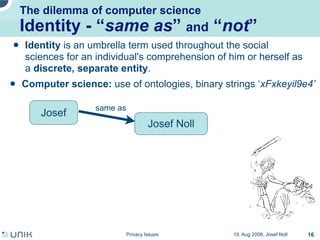
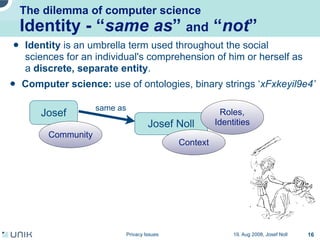
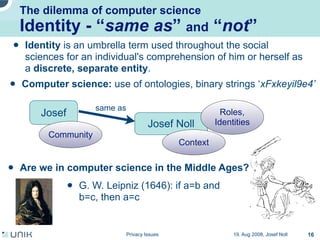
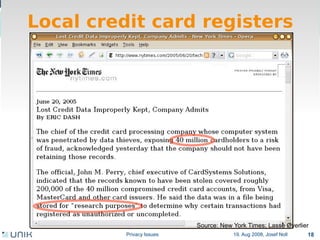
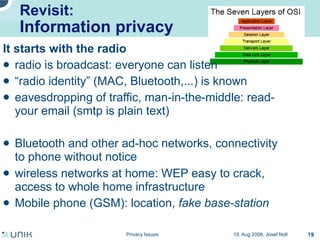

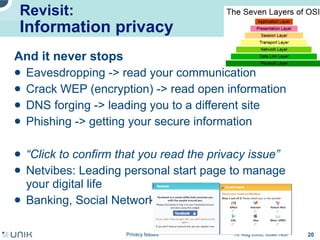
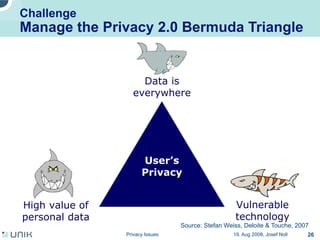
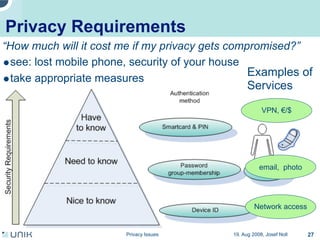
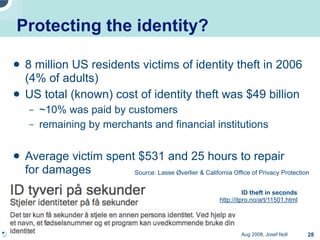
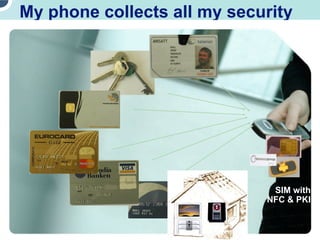
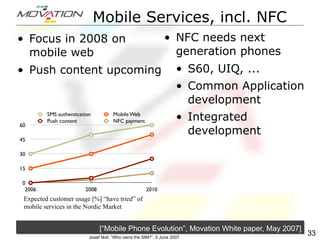

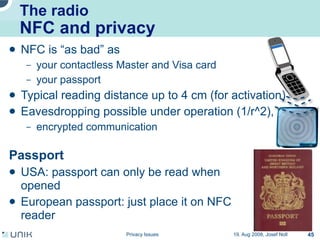
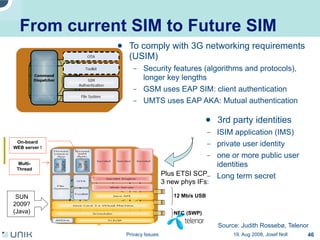
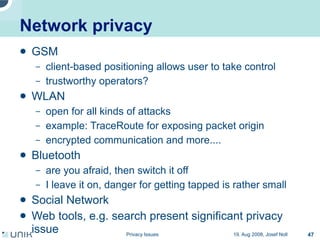
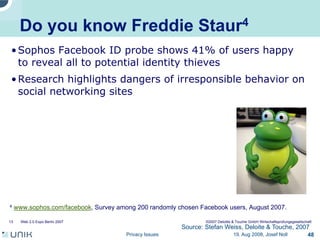
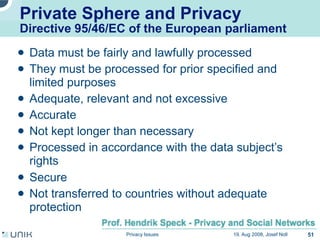
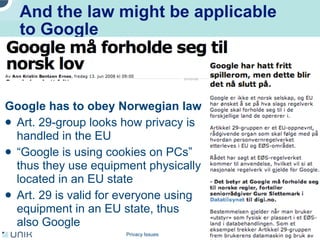


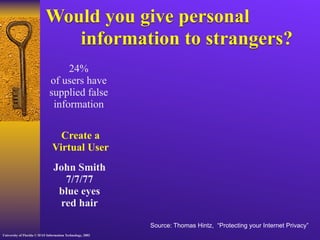
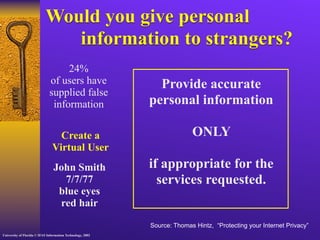
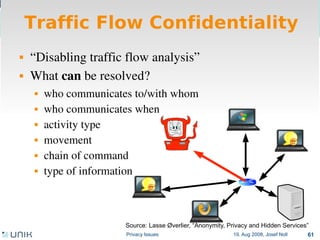
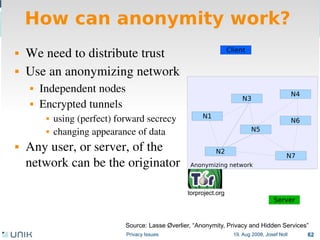
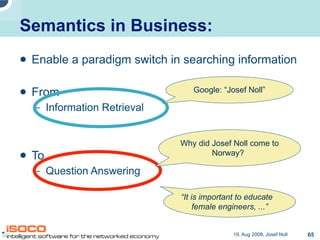

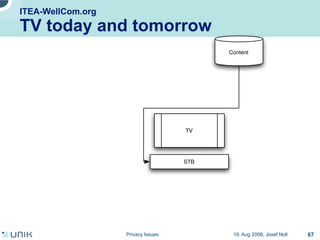
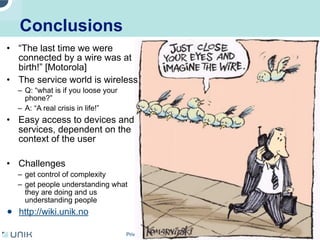

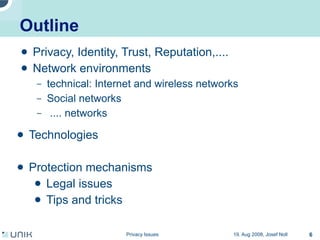
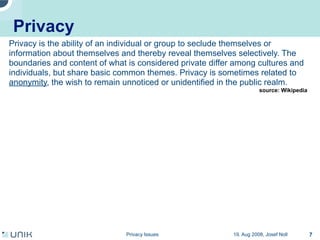
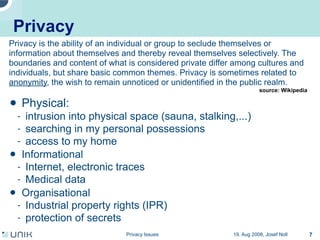
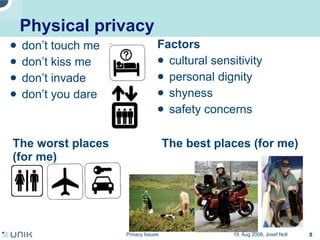
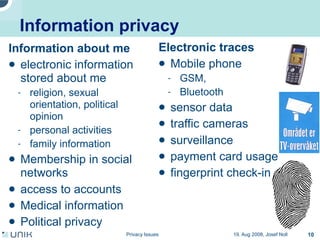
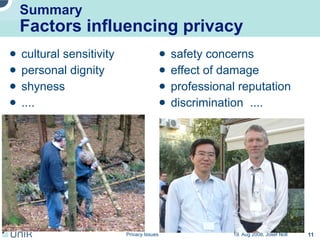
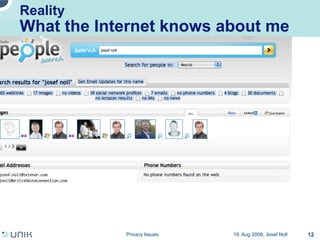
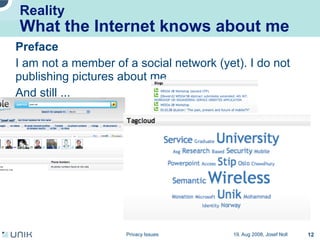
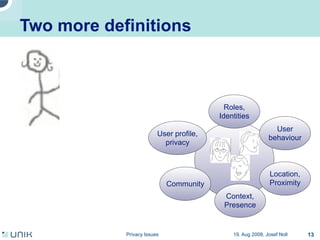
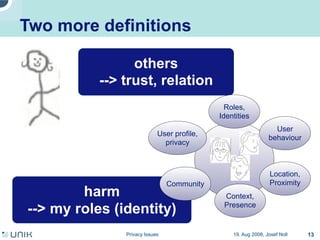
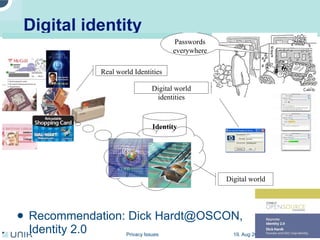
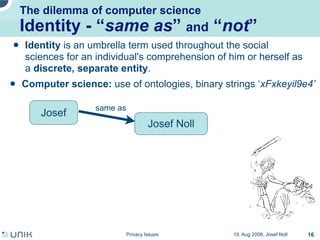
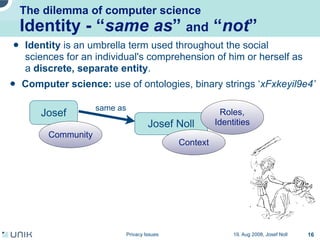
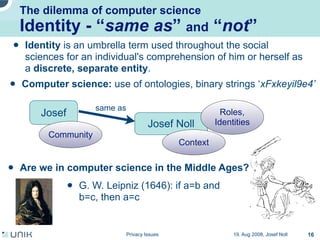
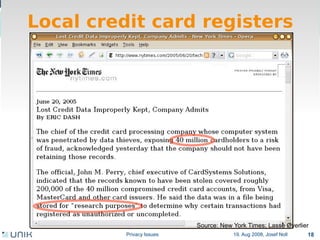
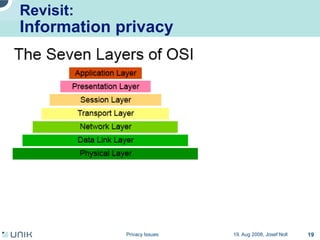
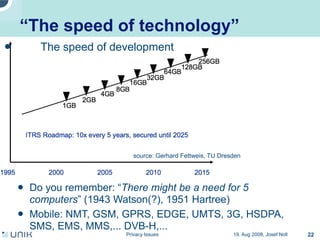
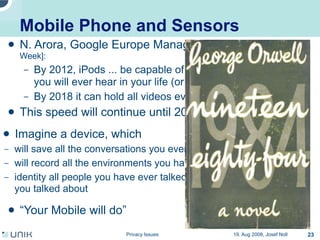
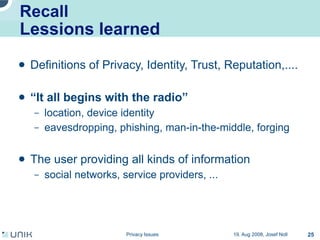
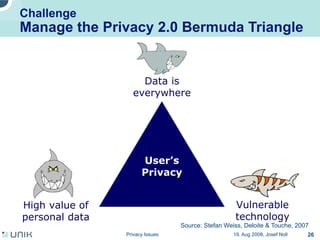
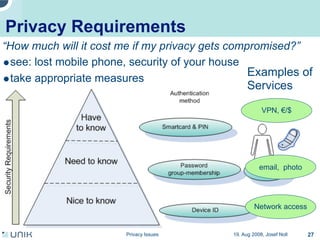
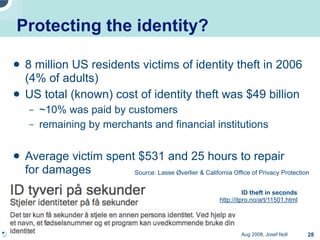
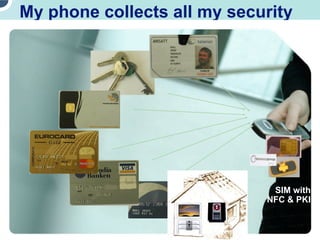
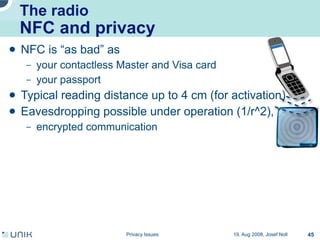
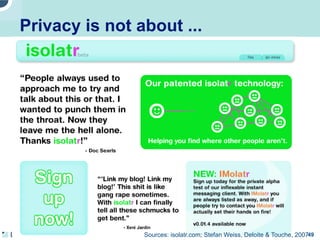
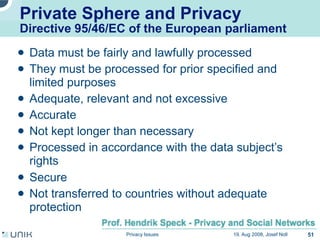
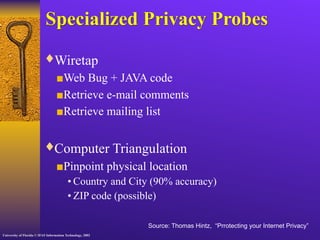
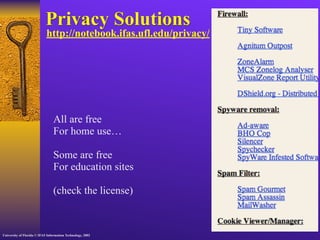
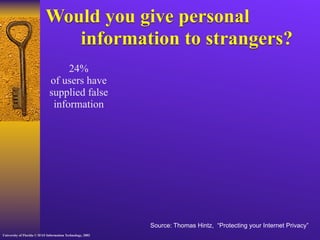
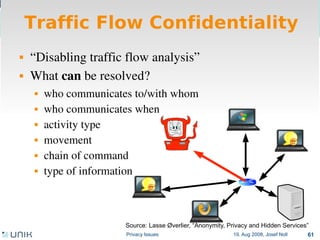
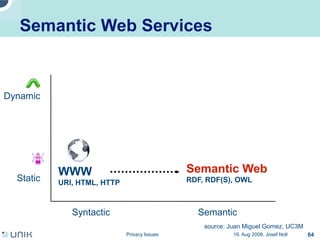
The document discusses various factors that influence privacy such as cultural sensitivity, personal dignity, and safety concerns. It examines different types of privacy including physical, informational, and organizational privacy. Additionally, it explores related concepts like identity, reputation, and trust in the digital world and how information about individuals is exposed through electronic traces online.