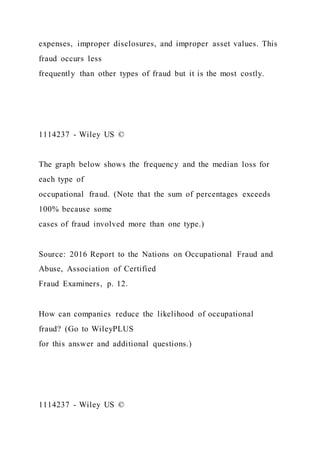
This chapter discusses the importance of internal controls in preventing fraud, with a focus on cash management at Barriques coffeehouse. It explains key principles of internal control, such as segregation of duties and establishment of responsibility, to minimize fraud opportunities. Additionally, it highlights the Sarbanes-Oxley Act's requirements for public companies to ensure effective internal control systems.