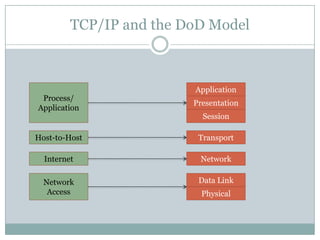
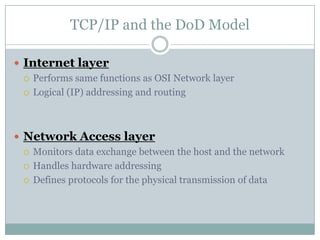
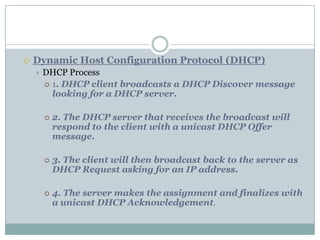
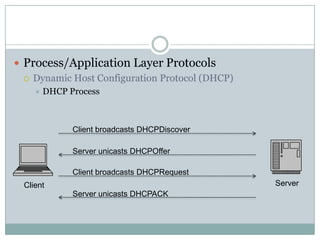
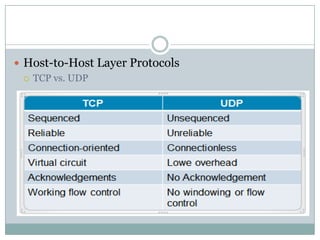
The document discusses the TCP/IP and DoD models. It explains that the DoD model has 4 layers instead of the 7 layers in the OSI model. The 4 layers are the Process/Application layer, Host-to-Host layer, Internet layer, and Network Access layer. It then provides details on protocols that operate at each of these layers, such as TCP and UDP at the Host-to-Host layer, and IP at the Internet layer.