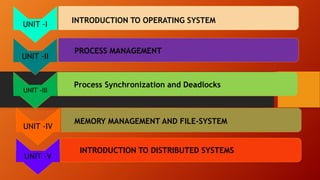
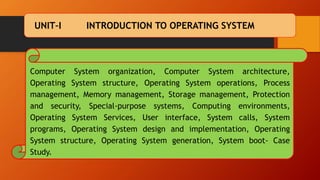
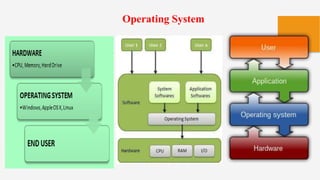
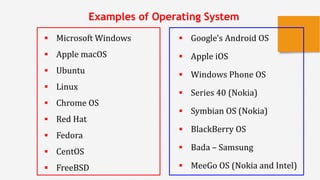
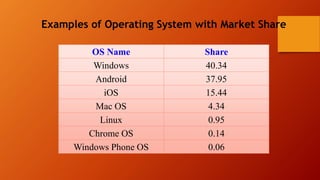
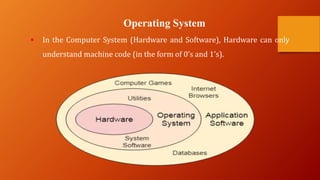
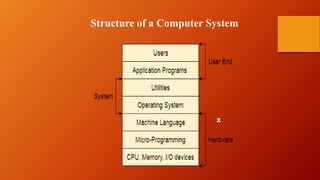
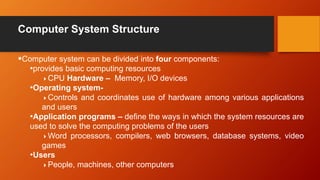
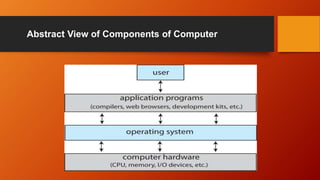
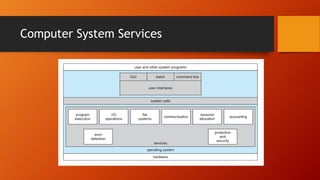
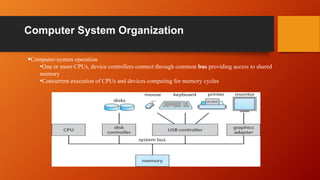
This document outlines the structure and content of a course on operating system principles. It is divided into 5 units that cover topics like process management, memory management, distributed systems, and synchronization. The introduction defines key parts of a computer system like the operating system, hardware, and users. It describes the role of the operating system in allocating resources and controlling devices and programs. Examples are given of popular desktop, mobile, and server operating systems.