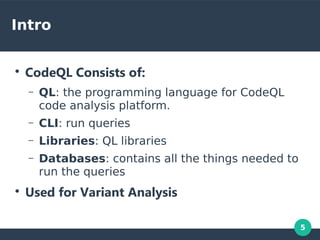
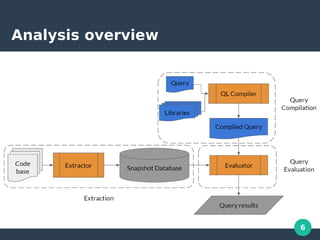
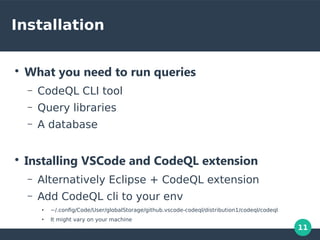
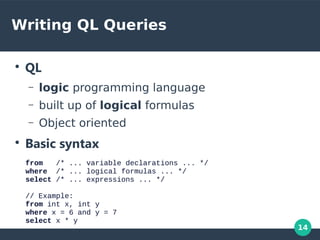
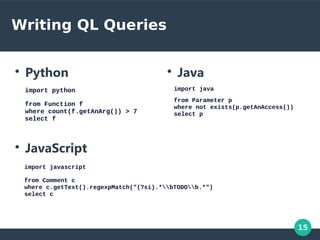
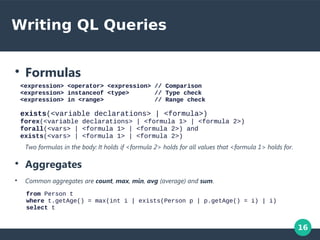
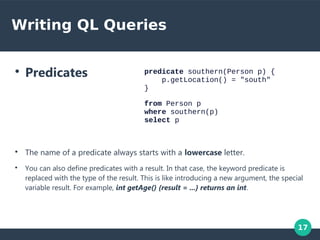
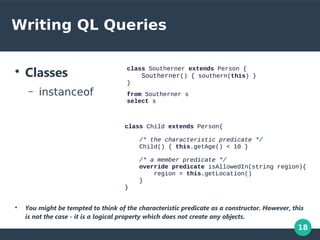
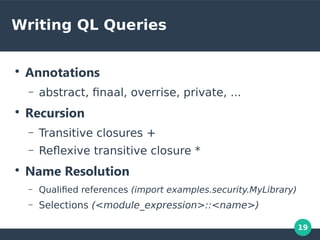
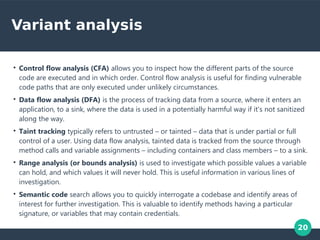
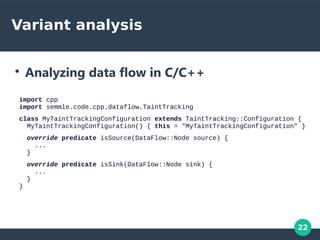
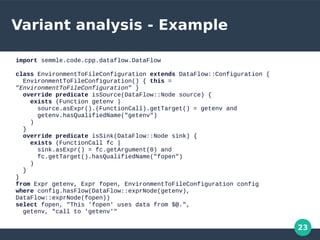
CodeQL is a code analysis platform that consists of the QL programming language, a CLI, libraries, and databases. It is used to analyze code for vulnerabilities and defects through queries written in QL. The document discusses installing CodeQL and the CLI, writing QL queries using logical formulas and predicates, and performing variant analysis through data and taint flow tracking to find issues. It provides an example query to find flows from environment variables to file openings.

![3
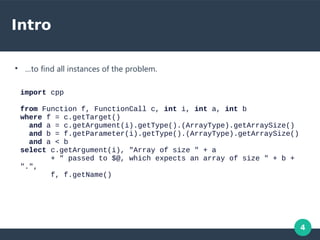
Intro
void fire_thrusters(double
vectors[12]) {
for (int i = 0; i < 12 i++) {
... vectors[i] ...
}
}
double thruster[3] = ... ;
fire_thrusters(thruster);
●
In C, array types of parameters degrade to pointer types.
●
The size is ignored!
●
No protection from passing a mismatched array.](https://image.slidesharecdn.com/codeql-presentation-191223183232/85/Semmle-Codeql-3-320.jpg)