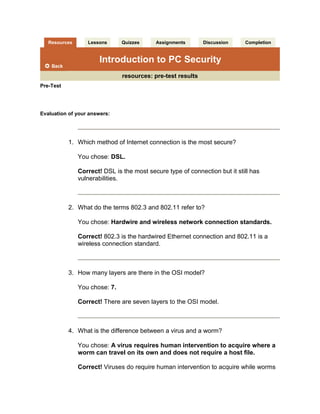
Pre Test Results Introduction To Pc Security
- 1. Resources Lessons Quizzes Assignments Discussion Completion Introduction to PC Securityresources: pre-test results Pre-TestEvaluation of your answers:Which method of Internet connection is the most secure?You chose: DSL.Correct! DSL is the most secure type of connection but it still has vulnerabilities.What do the terms 802.3 and 802.11 refer to?You chose: Hardwire and wireless network connection standards.Correct! 802.3 is the hardwired Ethernet connection and 802.11 is a wireless connection standard. How many layers are there in the OSI model?You chose: 7.Correct! There are seven layers to the OSI model.What is the difference between a virus and a worm?You chose: A virus requires human intervention to acquire where a worm can travel on its own and does not require a host file.Correct! Viruses do require human intervention to acquire while worms can move on their own and do not require a host file. Which scumware, malware, adware, or spyware lies to the computer that what it's seeing doesn't really exist?You chose: A rootkit program.Correct! A rootkit program hides from the computer by lying to it and telling the PC that the program it sees doesn't really exist. What is a universal vulnerability?You chose: A vulnerability that creates a known flaw in the security of a PC system or network.Correct! A vulnerability is universal when an operating system, software application, or some other programming code creates a known flaw in the security of a PC system or network.What is a SYN Flood attack?You chose: A method of flooding a computer with packets containing the address, port and information for communications.Correct! A SYN flood attack sends a flood of synchronized (SYN) packets containing the address, port, and other information necessary to communicate with the computer. What is the best protection for network security?You chose: A router with a built-in firewall and a software firewall.Correct! A router with built-in firewall can stop the packets from entering the network completely, while a software firewall will provide additional protection to individual PCs from spoofed packets slipping past the routers built-in firewall.In business, why do you need to worry about providing effective security for your network?You chose: Because of new laws governing the safe storage of personally identifying information.Correct! New legislation is appearing all the time that governs the safe storage of credit card information and personally identifying information. Failure to do so, could result in a business being liable for the financial loss to the customer.What do you call the new technology used in laptop engineering and design?You chose: Mobile.Correct! Mobile technology is the term used for the concept of designing lighter weight laptops with extended life batteries and wireless access. In computing terms, what does the term 'virtual' mean?You chose: Being in essence or effect, but not in fact.Correct! The term 'virtual' in computing has taken on the meaning from Webster's dictionary, which means being in essence or effect, but not fact. Why should you verify that antivirus software definitions have been updated when you do a security check?You chose: It verifies that nothing has interrupted the proper operation of the software.Correct! If the virus definitions are outdated and the auto-update is still enabled, it may indicate a virus is blocking the normal function of the software. Your score: 100% (out of 100%). Excellent job!Pre-TestDate submitted: 10/23/2008Please print this evaluation for your records.resources | lessons | quizzes | assignments | discussion | completion Course content © 1997-2008 by Debbie Mahler. All rights reserved. Reproduction or redistribution of any course material without prior written permission is prohibited.
