Running head SECURITY ANALYSIS REPORT1SECURITY ANALYSIS REPO.docx
- 1. Running head: SECURITY ANALYSIS REPORT 1 SECURITY ANALYSIS REPORT 13 Project 3: Security Analysis Report on Factors that are Likely to Affect Ombank’s Organizational Information Systems Infrastructure Aisha Tate UMUC August 26, 2019 Aisha 2nd Submission – Does not meet requirements – one more submission allowed. Please review the checklist and review both submissions. Read the project requirements and share an action plan before you work and submit the last revision. Thanks for your continued efforts. Here is what you have done well · You have focused on an organization and you have tried to apply the knowledge, skills and abilities you have gained · You have continued to improve your research skills. · You have done a good job with your APA formatting Skills I feel that you did not go through this checklist below. Avoid using generic graphics from literature especially if they are not
- 2. directly pertinent to the discussion. You did a good job with RAR report. You put much effort with your lab. Leverage Project 2 and Project 3 lab information in this SAR report. Please work on the quality of your references – especially in your RAR and SAR report Dr K Student Name: Aisha Tate Date:6-Sep-2019 This form provides the same classroom instructions in a checklist form to help students and professors quickly evaluate a submission Project 3: Requires the Following THREE Pieces Areas to Improve 1. Security Assessment Report (including relevant findings from Lab) See detailed comments below 2. Risk Assessment Report Meets Requirements – revise When you update SAR 3. Lab Experience Report with Screenshots Continue to improve Revise and connect with SAR 1. Security Assessment Report Enterprise Network Diagram You will propose a local area network (LAN) and Please research organizations For network information s a wide area network (WAN)
- 3. define the systems environment, Meets expectations incorporate this information in a network diagram. Discuss the security benefits of your chosen network design. Needs improvement Threats Define threat intelligence and explain what kind of threat intelligence is known about the OPM breach. Please find papers and share Common organizational challenges differentiate between the external threats to the system and the insider threats. ????? entify where these threats can occur in the previously created diagrams. Relate the OPM threat intelligence to your organization. How likely is it that a similar attack will occur at your organization? Good effort Identifying Security Issues Provide an analysis of the strength of passwords used by the employees in your organization. Tie in lab results Are weak passwords a security issue for your organization? ???? Firewalls and Encryption Determine the role of firewalls and encryption, and auditing ??? RDBMS that could assist in protecting information and monitoring the confidentiality, integrity, and availability of the information in the information systems. Research and share
- 4. Threat Identification Identify the potential hacking actors of these threat attacks on vulnerabilities in networks and information systems and the types of remediation and mitigation techniques available in your industry, and for your organization. Any research? Identify the purpose and function of firewalls for organization network systems, and how they address the threats and vulnerabilities you have identified. Update Also discuss the value of using access control, database transaction and firewall log files. Meets expectations Identify the purpose and function of encryption, as it relates to files and databases and other information assets on the organization's networks. No mention of encryption 2. Risk Assessment Report Risk and Remediation Please use more peer-reviewed and scho And scholarly references in your RAR What is the risk and what is the remediation? Good overview What is the security exploitation? Meets expectations Revise after SAR report is done 3. Lab Experience Report Summarizes the Lab Experience and Findings Continue to improve Responds to the Questions Tie lab observations to SAR report
- 5. Provides Screenshots of Key Results Yes Lab Experience Report Feedback Table of Contents Introduction 3 Purpose 3 Organization 4 Scope 5 Methodology 6 Data 8 Results 10 Findings 12 References 13 Introduction Organizational information is the key to success in modern business environments. In this project, Ombank – a hypothetical financial organization has been used to demonstrate key security issues likely to face organizations, as well as the preparation of a security assessment report. Ombank is a financial services organization offering financial support to customers through online assistance and physical consultancy. The organization is tasked with managing financial resources for customers who in turn pay for these services. For instance, customers who seek to find out how feasible their business ideas are for start-ups, they provide this information to Ombank, who are going to recommend the best course of action to take as far as investments, capital, and expenditure are concerned. On-site financial consultants provide services to customers who chose to physically acquire help or services from the organization. An online helper service facilitates remote consultancy for customers who need assistance but they are
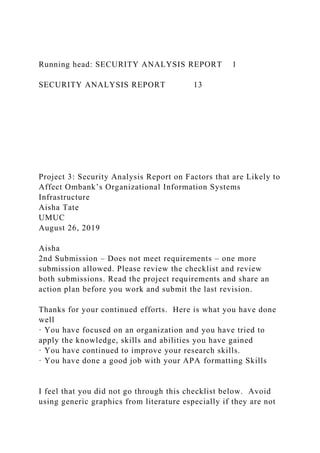
- 6. physically constrained. The customers who prefer online access are presented by a means of inputting their financial information, which may be in form of assets or personal finances. In this Security Analysis Document, we will be finding out the crucial security risks and vulnerabilities in the OmBank Organization.Purpose The purpose of this Security Assessment Analysis is to come up with possible security concerns for the organization as well as outlining possible threats to Ombank’s organizational infrastructure as far as information systems are concerned. Various I.T infrastructure will be assessed, outlining threats, to the organizational network, underlying security issues and overall enterprise threats. Information security is crucial to an organization’s business viability in accordance with its predefined goals (Bishop, 2003). Therefore, in this report, the factors which are likely to undermine the overall business viability and stability of the organization will be described and the possible factors which may lead to this unpleasant situation assessed. Organization Ombank, is structured in a way that every department is connected to a local area network. This infrastructure is meant to offer seamless management policies which improves the overall business organization, whilst providing a framework for customer and employee interaction with the information systems’ infrastructure. The local area network is connected to the internet through one router and three access points. The company makes use of technologies such as cloud computing. This means that the organization makes use of an online cloud database as opposed to local storage . Customer information is processed either locally or remotely. The following is a visual representation of the network architecture (???? Connect with literature for similar real-life organization) Ombank’s network is connected in the form of local and wide
- 7. area networks. The local area network provides access to the organizational resources such as servers – which may be application or network servers, and, at the same time providing a framework for information sharing, data management, and traffic congestion management (Fowler et al., 1991). The organizational architecture is shown below: Scope The analysis covers assessment of the infrastructure in the [company] organization. I.T infrastructure to be checked for security assessment include: 1) the enterprise network layout or infrastructure. Several concepts of networking have been applied in the organizational infrastructure. Issues arising from platform usage, cloud computing, centralized and distributed computing as well as programming designs used are investigated to find flaws, irregularities and vulnerabilities which may be costly if manipulated. ???? Networking hardware also needs to be subjected to security tests to affirm that there are no inconsistencies, leakages in hardware functionality. Network hardware tested include routers, switches and firewalls. Hardware in network configurations is often manipulated to gain unauthorized entry into organizational networks, which may prove costly in terms of financial losses and data breaches which may affect an organization’s reputation as well as business credibility (Hoo, 2000). To make sure that these factors are not manipulated, Ombank requires a full hardware audit and assessment to exhaustively analyze risks attached to all network hardware. Moreover, human organization in the organization???? also needs to be carefully scrutinized to ensure consistency, security and access in a manner that does not compromise the information security or pose a threat to the organization. Nonetheless, organizational policies are also scrutinized to ensure that no loopholes can be present which may be manipulated by attacks to compromise data security.
- 8. Software applications making use of organizational information such as databases and network communication too needed to be probed for loopholes and vulnerabilities. Ernest and Lin (2007) clearly illustrate that employee behavior is a factor that mandates for enactment and implementation of organizational control policies in an aim to protect information systems. Methodology Analysis was conducted over a period of six months. The investigation was conducted on governance policies, human resource and computer infrastructure. Physical security of computer components and overall organizational structure was handled first. This was to ensure that compromise to the information system infrastructure would not come from physical external contact, or, unauthorized internal contact (What standards are appropriate?). This also curbs the problem of vandalism or breakage. When physical security is out of question, analysis was done on authorization access. ????Maintaining the property of physical security, the organization access policies to hardware was also scrutinized. This means that only users with particular levels of access privileges would access to certain components. For instance, access to network servers and application servers in the distributed computing environment needs to be restricted only to the respective administrators. The level of privileges among all employees was recommended ascertaining that databases and applications would not be subject to any manipulation by unauthorized personnel. Moreover, this would help delegate responsibility to specific people who would answerable in case of incidents. (Very vague – find case studies / scholarly reports for classification of data/access) Network hardware under investigation was also identified, each component being give emphasis as a vulnerability would mean a loophole with heavy risks. The organization uses local area networks in wireless and wired forms. Both of these technologies are however connected to similar access points. The wireless local area network needed to be protected using
- 9. the WPA or WPA2 encryption methods. These forms of password protection are hard to crack or hack as opposed to WEP encryption. Wi-Fi access points with WEP encryption were noted down for replacement. The wired network is connected to the routers through wired access points. These are in form of switches and hubs. The wired network is made possible through the use of Ethernet cables, connected to switches and access points. Due to the increasingly large size of Ombank’s organizational layout, local area network access points are heavily distributed across the organizational premises. During the assessment, it was crucial to establish whether the Ethernet access is protected against unauthorized access too, and the level of privileges set for computers connected to the Ethernet. Ombanks’s network still makes use of hubs despite being a little overtaken by time. Hubs do not allow control of traffic as opposed to switches. These components are becoming obsolete since one cannot control information being transferred within the organization. Therefore, employees with malicious intentions may use this loophole to transmit uncensored information outside the organization. Marianov et al., (1999) claim that the use of toxic hubs???? may prompt computer users into network manipulation to share malicious information due to lack of network monitoring capabilities. (Please find more recent papers on network security) Moreover, the organization makes use of cloud computing. This means that organizational information is stored in databases provided by cloud computing service providers as opposed to local storage. As much as this technology offers security due to non-interference, study needed to be conducted to ensure how information is transmitted, whether there is a possibility for database manipulation by different employee levels. Programming designs used for software around the organization also needed inspection to ascertain security of applications and bugs which may lead to inconsistencies. Object-oriented approaches are best suitable for security designs due to factors
- 10. such as data encapsulation, inheritance and abstraction. Object oriented designs therefore are important because they are easier to debug and troubleshoot problems.Data Data is crucial in a security analysis situation as it helps define the areas which are susceptible to compromise, and makes troubleshooting easier. This information provides an overview of the current organization in question and flaws in any parts of the data may lead to threats to information security. Data collected for this assessment was in the following form. 1. I.T Infrastructure information I. Networks Network components such as routers, switches and firewalls. II. Application software Details about the software used by the organization, including programming principles used.???? Do you mean secure coding practices? III. Database Information about the organizational database, local and cloud- based. IV. Application servers This information pertains the location of servers, authorized personnel who access and the security protocols employed. 2. User Information in the organization I. Authentication policies Information about password policies, level of authentication and password management. What are the differences between Authentication, Authorization and Accounting? Why are these three important to this organization? II. Employee information. Details about all employees in the organization, including names, salaries and disciplinary reports. III. Personal identifiable information. This is information about all people related with the organization, clients, managers or general employees. This information includes Identification numbers, phone numbers, and addresses.
- 11. 3. Physical layout information I. Physical security information. These are all the details pertaining physical security including number of security personnel, locks and gate passes. II. Disaster precaution information????. This includes information relating to how the security is prepared against calamities such as fires. This includes fire extinguishers and smoke detection information. Results Major threats to the organizational information system was realized in transaction handling and overall management. Threats arising from poor infrastructural organizations were also indicated. These threats are categorized according to the type; those that may arise from organizational personnel and those that could be manipulated by external attackers with malicious intents. Scenarios of the findings are indicated as follows: Lack of proper physical security. The organization has employed security guards for physical security. However, the infrastructural components could still be accessed by a majority of employees, including those without proper authorization. Server rooms need enhanced protection. Organizational policies not exhaustive. Access Control Polices (ACP) are not clearly defined and enacted. Majority of the users use the shared network. However, there are not clearly defined laws (do you mean policies and procedures?) restricting network usage access. Access to administrative privileges have been realized amongst standard users. This is dangerous as it could easily provoke employees with more knowledge of information technology systems to manipulate the systems to gain access to sensitive information. Incident reporting mechanisms in the organization have also been undermined. Working in such an organization requires a fast means of giving feedback to the responsible personnel of even the slightest malfunction in the computer systems. With this kind of feedback, system administrators can troubleshoot problems even when they are
- 12. far-coming. ???? Furthermore, with the organization access to the internet, it is easy for employees to take work home, and submit it remotely to the servers. The Remote Access Policy has not been clearly defined. This policy requires an organization to set acceptable standards for connecting to an organization’s network remotely. The communication policy is partially defined. While it is clear to employees about the implications of sharing company sensitive information with outside parties, rules governing the use of corporate communication services have not been set. An instance was realized when an employee received an email, through the corporate means, from an unknown source and still accessed it from their workstations. Attackers normally use unsuspecting employees to spread viruses, backdoors and Trojans through such means. Use of outdated technologies. Technology, be it hardware or software becomes obsolete when issues arise pertaining their usage and security. It was therefore horrifying to find out that the company still uses outdated technologies such as hubs for local area connections. Use of hubs poses serious challenges to administrators as there is no possible way of monitoring or filtering information being relayed around the organization and the outside world. Furthermore, some Wi-Fi access points were found to be using the obsolete WEP encryption method. The WEP encryption method poses serious dangers of unauthorized access given how easy it is to crack passwords encrypted with this technology. No tie-in with the lab report – Project 2, Project 3 Lab work?Findings Threats to overall security were categorized according to the nature and the impact that would be realized in case of employment of the vulnerabilities. These included natural threats, human threats, environmental factors, and threats to physical security. Natural threats arise due to unintended environmental factors in the organizational structure. These
- 13. may include fire and water damage. An assessment of the organization showed that the premises is well equipped to handle such conditions. Fires started intentionally or unintentionally pose a risk to damage of equipment resulting in loss of information and cost inflation to the organization. Human threats in the organization include espionage and sabotage. The organization hosts a minimum of 200 employees.??? Should be at the start of the report? Discontentment, dissatisfaction and feuds with management may pose a risk of sabotage where disgruntled employees may result in causing intentional damage or compromising organizational information (Shaw et al., 1998). Human threats furthermore include vandalism, theft hacking and social engineering. It was identified that the organization’s employees are not competent with social engineering schemes. These include malicious emails which may be used to capture personal information by hackers. Moreover, organizational data integrity is prone to being compromised attributing to the fact that employees have a tendency of taking work away from the office. Environmental and physical threats identified include program errors, unauthorized entry and power outages. The organization lacks infrastructural uninterrupted power supply systems. Instead, these devices are located for majority of the workstations. This however does not rule out the fact that short- life UPSs are susceptible to malfunction or failure if power outages prolong for long periods of time. References Bishop, M. (2003). What is computer security?. IEEE Security & Privacy, 1(1), 67-69. Fowler, H. J., Leland, W. E., & Bellcore, B. (1991). Local area network traffic characteristics, with implications for broadband network congestion management. IEEE Journal on Selected Areas in Communications, 9(7), 1139-1149. Hoo, K. J. S. (2000). How much is enough? A risk management
- 14. approach to computer security. Stanford: Stanford University. Ernest Chang, S., & Lin, C. S. (2007). Exploring organizational culture for information security management. Industrial Management & Data Systems, 107(3), 438-458. Marianov, V., Serra, D., & ReVelle, C. (1999). Location of hubs in a competitive environment. European Journal of Operational Research, 114(2), 363-371. Shaw, E. D., Ruby, K. G., & Post, J. M. (1998). The insider threat to information systems. Security Awareness Bulletin, 2(98), 1-10. Cloud ServicesInternetApplication serverWorkstationWorkstationWorkstation Cloud Services Internet Application server Ethernet Workstation Workstation Workstation HubWireless Access PointWireless Access pointSwitchWork StationWork StationWork StationWork StationWork StationWork StationPDA/SmartphonesServerFirewallRouter Hub Wireless Access Point Wireless Access point Switch
- 15. Work Station Work Station Work Station Work Station Work Station Work Station PDA/Smartphones Server Firewall Router Adjust your audio This is a narrated slide show. Please adjust your audio so you can hear the lecture. If you have problems hearing the narration on any slide show please let me know. 1 Chapter 1 The Information Systems Strategy Triangle
- 16. 2 Kaiser Permanente (KP) Opening Case What was KP’s business strategy in 2015? On what were bonuses to doctors based under the “fix me” system? What would the new idea be called instead of a “fix me” system? What is the new basis for end-of-year bonuses? What goal alignment has helped KP’s success? What IS components are part of this? Could only the IS components be changed to achieve their success? Could only the strategy be changed to achieve their success? © 2016 John Wiley & Sons, Inc. 3 To promote better health care at lower cost Billings Proactive health system Improved health of patients Alignment between business strategy, organizational design, and information systems strategy Fast communication with patients outside of face-to-face appointments; automatic email reminders to patients for
- 17. exercise or medications No, the business strategy must be aligned with the IS, in addition to incentives No, without the new incentives and new IS, employees would not wish to cooperate, nor would they be able to do so. 3 4 The Information Systems Strategy Triangle These need to be balanced. Business Strategy Organizational Strategy Information Strategy © 2016 John Wiley & Sons, Inc. 4 What is a “Strategy?” Coordinated set of actions to fulfill objectives, purposes, or goals It sets limits on what the organization seeks to accomplish Starts with a missionCompanyMission StatementZappos To provide the best customer service possible. Internally we call this our WOW philosophy.Amazon We seek to be Earth’s most customer-centric company for three primary customer sets: consumer customers, seller customers and developer customers.L.L. Bean Sell good merchandise at a reasonable profit, treat your customers like human beings and they will
- 18. always come back for more. © 2016 John Wiley & Sons, Inc. 5 What is a business strategy? It is where a business seeks to go and how it expects to get there It is not a business model, although it includes business models as one component of a business strategy Business models include subscriptions, advertising, licenses, etc. Business models do not include where the business seeks to go, and only the revenue portion of how it expects to get there © 2016 John Wiley & Sons, Inc. 6 Generic Strategies Framework Michael Porter: How businesses can build a competitive advantage Three primary strategies for achieving competitive advantage: Cost leadership – lowest-cost producer. Differentiation – product is unique. Focus – limited scope – can accomplish this via cost leadership
- 19. or differentiation within the segment 7 © 2016 John Wiley & Sons, Inc. 7 Three Strategies for Achieving Competitive AdvantageStrategic AdvantageStrategic TargetUniqueness Perceived by CustomerLow Cost PositionIndustry WideDifferentiationCost LeadershipParticular Segment OnlyFocus © 2016 John Wiley & Sons, Inc. 8 Three Strategies for Achieving Competitive Advantage ExamplesStrategic AdvantageStrategic TargetUniqueness Perceived by CustomerLow Cost PositionIndustry WideDifferentiationCost LeadershipParticular Segment OnlyFocus Apple Wal-Mart Marriott
- 20. Ritz Carlton © 2016 John Wiley & Sons, Inc. 9 Dynamic Strategies Beware of Hypercompetition Can lead to a “red ocean” environment Cutthroat competition – zero sum game Every advantage is eroded—becoming a cost. Sustaining an advantage can be a deadly distraction from creating new ones. D’Avenis says: Goal of advantage should be disruption, not sustainability Initiatives are achieved through series of small steps. Get new advantage before old one erodes. Better to adopt a “blue ocean” strategy Change the industry; create new segments/products 10 © 2016 John Wiley & Sons, Inc. 10 Creative Destruction
- 21. GE’s Approach under Jack Welch Ask people to imagine how to destroy and grow your business DYB: Imagine how competitors would want to destroy your business. GYB: Counteract that by growing the business in some way to: Reach new customers/markets Better serve existing customers © 2016 John Wiley & Sons, Inc. 11 SummaryStrategic ApproachKey IdeaApplication to Information SystemsPorter’s generic strategiesFirms achieve competitive advantage through cost leadership, differentiation, or focus.Understanding which strategy is chosen by a firm is critical to choosing IS to complement the strategy.Dynamic environment strategiesSpeed, agility, and aggressive moves and countermoves by a firm create competitive advantage.The speed of change is too fast for manual response making IS critical to achieving business goals. © 2016 John Wiley & Sons, Inc. 12 Organizational Strategy What is organizational strategy?
- 22. Organizational design and Choices about work processes How do you manage organizational, control, and cultural variables? Managerial Levers 13 © 2016 John Wiley & Sons, Inc. 13 14 Managerial Levers © 2016 John Wiley & Sons, Inc. 14 IS Strategy What is an IS Strategy? - The plan an organization uses in providing information services. Four key IS infrastructure components
- 23. 15 © 2016 John Wiley & Sons, Inc. 15 16 Information systems strategy matrix.WhatWhoWhereHardwareThe physical devices of the systemSystem users and managersPhysical location of devices (cloud, datacenter, etc.)SoftwareThe programs, applications, and utilities System users and managersThe hardware it resides on and physical location of that hardwareNetworkingThe way hardware is connected to other hardware, to the Internet and to other outside networks.System users and managers; company that provides the serviceWhere the nodes, wires, and other transport media areDataBits of information stored in the systemOwners of data; data administratorsWhere the information resides © 2016 John Wiley & Sons, Inc. Click to edit Master text styles Second level Third level Fourth level Fifth level
- 24. 16 WhatWhoWhereHardwareLaptops, servers to store info and back up laptopsConsultants have laptops, managed by the IS Dept.Laptops are mobile; servers are centralizedSoftwareOffice suite; collaboration toolsSoftware is on consultants’ laptops but managed centrallyMuch resides on laptops; some only resides on serversNetworkingInternet; hard wired connections in office; remote lines from home, satellite, or client officesISP offers service; Internal IS group provides servers and accessGlobal access is needed; Nodes are managed by ISPsDataWork done for clients; personnel dataData owned by firm but made available to consultants as neededResides on cloud and copies “pulled” into laptops as needed. 17 Illustration in a Consulting Firm © 2016 John Wiley & Sons, Inc. Click to edit Master text styles Second level Third level Fourth level Fifth level 17 One IS Strategy: Social Strategy Collaboration
- 25. Extend the reach of stakeholders to find and connect with one- another Engagement Involve stakeholders in the business via blogs; communities Innovation Identify, describe, prioritize new ideas © 2016 John Wiley & Sons, Inc. 18 Summary After you have listened to this lecture and read Chapter 1 of your text Go to Discussion Board 2 and answer the discussion prompt Finally complete Quiz 1 © 2016 John Wiley & Sons, Inc. 19