Running head METHODS USED IN CYBER WARFARE1METHODS USED IN CYB.docx
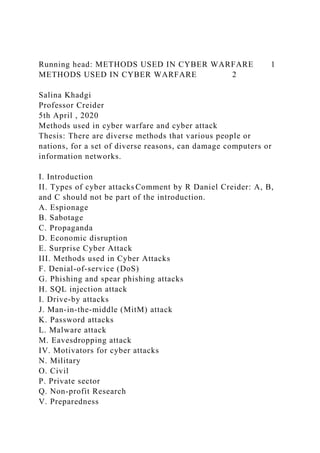
- 1. Running head: METHODS USED IN CYBER WARFARE 1 METHODS USED IN CYBER WARFARE 2 Salina Khadgi Professor Creider 5th April , 2020 Methods used in cyber warfare and cyber attack Thesis: There are diverse methods that various people or nations, for a set of diverse reasons, can damage computers or information networks. I. Introduction II. Types of cyber attacks Comment by R Daniel Creider: A, B, and C should not be part of the introduction. A. Espionage B. Sabotage C. Propaganda D. Economic disruption E. Surprise Cyber Attack III. Methods used in Cyber Attacks F. Denial-of-service (DoS) G. Phishing and spear phishing attacks H. SQL injection attack I. Drive-by attacks J. Man-in-the-middle (MitM) attack K. Password attacks L. Malware attack M. Eavesdropping attack IV. Motivators for cyber attacks N. Military O. Civil P. Private sector Q. Non-profit Research V. Preparedness
- 2. VI. Cyber counterintelligence Methods used in Cyber warfare and cyber attacks Just like other warfare, Cyber warfare is a digital war where computer viruses are sent instead of army and hacking into database with the aim to create damages and destruction. With the increasing use of computer and technology in almost every field obstruction of data can be a bigger war than an actual war. Acquiring sensitive data about a country, business, person or anything that relies in computational functions are in risk if the data is lost which can cause metamorphosis of a certain company that relies hugely on computer. There are diverse methods that various people or nations, for a set of diverse reasons, can damage computers or information network. Cyber- attack is a broad picture of cyber warfare, similar types of methods are used in cyber warfare and cyber-attack. When a nation’s database or the system of one of its branches is attacked for war reasons or for manipulation, the term cyber warfare is used. Comment by R Daniel Creider: Why is this text in bold? You need both an abstract and an introduction. You should have place holders in the draft to indicate that those sections of the paper have not been written. Cyberwarfare is, therefore, a long period of cyberattacks carried out now and then, and at some point, it includes traditional military actions between countries. The fact, however, is that to date, the actual act hasn't taken place. But many states have had an eye for an eye military-cyber action, and a good example is the cyber-attack launched by the US against the Iranian Weapons as retaliation for US drone Iranian shot down. This paper looks at the primary methods used in cyber warfare and cyber-attacks. The increasing technology is not causing mass destruction to business organizations, but to critical government agencies to. Cyberattacks and cyberwarfare are at the center of every threat
- 3. that information technology possesses to the government agencies. Those running the ICT sector as experts still have several debates as per the actual meaning/definition of cyberwarfare, some look at it as misnomer arguing that up-to today, no cyberattack qualifies as an act of war and those that have occurred is within the international relations domain. Although there is no clear definition or meaning of what cyber warfare and cyber-attacks are, the world's top super nations are in the race of running active operations as ways of an offensive and defensive mechanism There are diverse methods that various people or nations, for a set of diverse reasons, can damage computers or information networks. In a broad picture, espionage is one of the cyber- attacks, espionage in literal meaning refers to the practice of spying. Spying using a computer falls under cyber-attack. Another type is sabotage, sabotage is the act of destroying data. Changing the propaganda digitally is another type of cyber- attack. Disruption of economy is another huge concerned area of cyber-attack. Malware in commonly known as computer virus. “Malware is a term used to describe malicious software, including spyware, ransomware, viruses, and worms. Malware breaches a network through a vulnerability, typically when a user clicks a dangerous link or email attachment that then installs risky software”( . Malware is the most common and the most dangerous type of a cyber-attack. Malware can be of many types and they are sent by hackers intending to block and/or change network keys or settings, damage information from a computer or a network of computers, sabotage and most importantly disable a system. Types of cyber attacks Espionage: Many still think that Espionage is not an act of war, but the fact it causes tension among countries. It is a form of cyber-attack that involves abstaining confidential data without
- 4. the consent of the owner of the information (Kafol & Bregar, 2017). Examples of Espionage is the massive act of spying on other countries by the American government as an ICT hacker Edward Snowden revealed. Comment by R Daniel Creider: This should be a complete sentence and the first word of the sentence is capitalized. Sabotage: this form of cyber-attack involves using computer and satellites system to coordinate and run operations leading to a severe disruption of other networks, including the military systems like C4ISTAR that run and control communications. As a cyber-attack, Sabotage leads to the interception of crucial communication or malicious replacement of the intended transmission. Other things that get affected by a Sabotage attack are; water, transportation, power, and fuel infrastructures. Propaganda: a cyber-propaganda refers to efforts by one nation to control another nation's information in any way possible and use the information in managing the general public opinion (Goswami, 2018). To a high degree, cyber propaganda is psychological warfare; the only difference is that it uses websites that run fake news, social media platforms, and other internet platforms. Jowett & Donnell (2018) state that "propaganda is the deliberate, systematic attempt to shape perceptions, manipulate cognitions, and direct behavior to achieve a response that furthers the desired intent of the propagandist" (p. 7). Comment by R Daniel Creider: Page number is not needed. Comment by salina khadgi: Still working on the format Comment by salina khadgi: Economic disruption: this form of cyber-attack targets economic infrastructures such as manufacturing companies, processing industry, and other aspects of the economy. An excellent example of economic disruption is the Wanna-Cry attacks that affected Ukraine and UK, s N.H.S, Merck pharmaceuticals, Maersk shipping, and other organizations globally. Economic disruption is a cyber-crime and financial crime in particular. Surprise Cyber Attacks: this kind of attack involves using
- 5. malware such as antivirus to attack communications systems, information systems, and other software that is operated by a particular organization. Denial of service (DoS) and distributed denial of service (DDoS) is, as the name suggests, a type of cyber-attack that denies a user form getting into an online system or database. “A denial-of-service attack floods systems, servers, or networks with traffic to exhaust resources and bandwidth. As a result, the system is unable to fulfill legitimate requests. Attackers can also use multiple compromised devices to launch this attack” [1]. SQL injection is a type of cyber-attack where the attacker uses SQL code to acquire any sort of information from a computer. “A Structured Query Language (SQL) injection occurs when an attacker inserts malicious code into a server that uses SQL and forces the server to reveal information it normally would not. An attacker could carry out a SQL injection simply by submitting malicious code into a vulnerable website search box” [1]. Man-in-the-middle attack is the type of cyber-attack that interrupts or attacks a computational communication. An attacker inserts himself in a conversation between two parties, either personal communication or interaction between a user and an application making it appear like a normal conversation. “Man-in-the-middle (MitM) attacks, also known as eavesdropping attacks, occur when attackers insert themselves into a two-party transaction. Once the attackers interrupt the traffic, they can filter and steal data. Two common points of entry for MitM attacks: 1. On unsecure public Wi-Fi, attackers can insert themselves between a visitor’s device and the network. Without knowing, the visitor passes all information through the attacker. 2. Once malware has breached a device, an attacker can install
- 6. software to process all of the victim’s information” (Cisco) Phishing is the type of attack that is intended in stealing login credentials, credit card information or any other information that is saved in a browser or an application. According to CSO, “Phishing is a cyber-attack that uses disguised email as a weapon. The goal is to trick the email recipient into believing that the message is something they want or need — a request from their bank, for instance, or a note from someone in their company — and to click a link or download an attachment” (CSO) There could be a million reasons for a person or group of people to involve themselves in cyber warfare or cyber-attacks. Acquiring information about a country could ruin a country’s prestige and could allow power to the wrong people. As an example, many countries use electronic methods for voting, if a voting system is hacked power of that country can belong to anyone. There could be military reasons for cyber warfare, for two rival nations knowing the next move of your rival can play a vital role in a war situation. If communication system between the military and the government can be hacked that will put a whole country into threat. Manipulation of a country’s database can ruin the information that they have about their citizens. “Offensive cyber operations offer a large variety of cheap and risk-free options to weaken other countries and strengthen their own positions. Considered from a long-term, geostrategic perspective, cyber offensive operations can cripple whole economies, change political views, agitate conflicts within or among states, reduce their military efficiency and equalize the capacities of high-tech nations to that of low-tech nations, and use access to their critical infrastructures to blackmail them” (Wikipedia) Military in many countries have a department of cyber security,
- 7. they recruit people to save and/or attack different nations for military purposes. “Examples of cyberwarfare driven by political motivations can be found worldwide. In 2008, Russia began a cyber-attack on the Georgian government website, which was carried out along with Georgian military operations in South Ossetia. In 2008, Chinese 'nationalist hackers attacked CNN as it reported on Chinese repression on Tibet” [3]. There have been rumors of Russia attacking US presidential election held on 2016. “The Senate Intelligence Committee concluded Thursday that election systems in all 50 states were targeted by Russia in 2016, an effort more far-reaching than previously acknowledged and one largely undetected by the states and federal officials at the time” [4]. “The US Department of Justice has charged 12 Russian intelligence officers with hacking Democratic officials in the 2016 US elections” (BBC News). Countries attacking other countries digitally is not fresh news. There have been instances where powerful countries have used technological means to attack a rival country. There might be a lot of activities that never made it to the news channels. “Computers and satellites that coordinate other activities are vulnerable components of a system and could lead to the disruption of equipment Compromise of military systems, such as C4ISTAR components that are responsible for orders and communications could lead to their interception or malicious replacement. Power, water, fuel, communications, and transportation infrastructure all may be vulnerable to disruption” (Wikipedia). Preparedness The increase in cyber-attacks has driven countries into conducting activities that will increase their readiness and create new strategies. The preparedness mechanism runs as war games. Since 2010, CCDCE (Cooperative Cyber Defense Centre of Excellence) which is part of NATO, has conducted annual war game known as Locked Shield as part testing readiness and improving strategic techniques, skills, and the operation decision making for all the national organizations of the
- 8. participating nations. The 2019 war games brought together 1200 competitors from thirty nations who competed as Blue team vs Red team. The 2019 game was unique as it included Beryllia a fictional nation facing deteriorating cyber security situation. Cyber counterintelligence The cyber counterintelligence refers to measures of identifying, penetrating/neutralizing any form of foreign operation that runs through cyber operations as a primary threat control method. The process also includes neutralizing foreign intelligence by gauging the capabilities of cyber threats and motives. The U.S government invest millions of monies in cyber counterintelligence, since 2009, the federal government spends over $100 million in responding and repairing the network systems damaged by several cyber-attacks that target the country’s top security communication networks. The U.S lawmakers are also part of the support system in the war against cyber-attacks and they first showed in 2009 by pushing the White House to appoint a cyber-attack specialist as way of dramatically escalating the country’s defense system against any form of cyber threats, crafts proposals to empower the government in setting the best security mechanism to protect private industry. The US Department of Defense is also in the race of ensuring that the country develops counterattack system. in 2015, the department made public a memorandum that detailed several tactics that will ensure the country remains prepared to face the cyber-attack threats. One of the most challenging issue in cyber counterintelligence is attributing the problem to a parson or system of operation. It is almost impossible to figure the person behind any form of cyber-attack, although the defiance secretary of defense maintains that as a country, we have the best systems to trace an attack back to the source. As a country that runs some of the world’s top military system, the Pentagon has continuously prosed various ways of ensuring that the
- 9. country has the best including the prosed deployment of the country’s top ICT experts and hackers to military operation bases. Reference Comment by R Daniel Creider: You need a URL for every reference. Just the URL is not a complete reference. “Cyber Attack - What Are Common Cyberthreats?” Cisco, Cisco, 30 Mar. 2020, www.cisco.com/c/en/us/products/security/common- cyberattacks.html. Fruhlinger, Josh. “What Is Phishing? How This Cyber Attack Works and How to Prevent It.” CSO Online, CSO, 13 Feb. 2020, www.csoonline.com/article/2117843/what-is-phishing- how-this-cyber-attack-works-and-how-to-prevent-it.html. Sanger, David E., and Catie Edmondson. “Russia Targeted Election Systems in All 50 States, Report Finds.” The New York Times, The New York Times, 25 July 2019, www.nytimes.com/2019/07/25/us/politics/russian-hacking- elections.html. “Twelve Russians Charged with US 2016 Election Hack.” BBC News, BBC, 13 July 2018, www.bbc.com/news/world-us- canada-44825345. “Cyberwarfare.” Wikipedia, Wikimedia Foundation, 5 Apr. 2020, en.wikipedia.org/wiki/Cyberwarfare#Cyberwarfare_vs._Cyber_ War. Kafol, C., & Bregar, A. (January 01, 2017). Cybersecurity: Building sustainable protection. Dalam International Scientific Book, 2017, 81-90. Kafol, C., & Bregar, A. (January 01, 2017). Cybersecurity: Building sustainable protection. Dalam International Scientific Book, 2017, 81-90. Goswami, M. P. (2018). Fake News and Cyber Propaganda: A study of manipulation and abuses on Social Media. Jowett, G. S., & O'Donnell, V. (2018). Propaganda & persuasion. Sage Publications. Abawajy, J. (2014). User preference for cybersecurity
- 10. awareness delivery methods. Behavior & Information Technology, 33(3), 237-248. Thomas, T., Vijayaraghavan, A. P., & Emmanuel, S. (2020). Machine learning approaches in cybersecurity analytics. Singapore: Springer. Bordoff, S., Chen, Q., & Yan, Z. (January 01, 2019). Cyber Attacks, Contributing Factors, and Tackling Strategies.