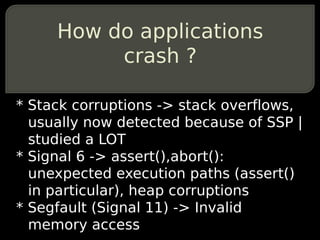
In this presentation, we introduce a new exploitation methodology of invalid memory reads and writes, based on dataflow analysis after a memory corruption bug has occured inside a running process.
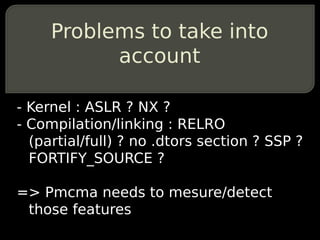
We will expose a methodology which shall help writting a reliable exploit out of a PoC triggering an invalid memory write, in presence of security defense mechanisme such as compiler enchancements (full RELRO, SSP...), or kernel anti exploitation features (ASLR, NX...).
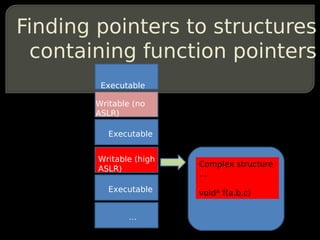
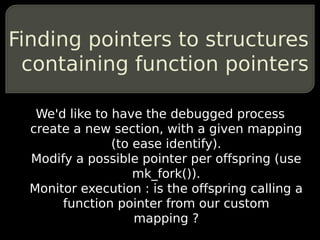
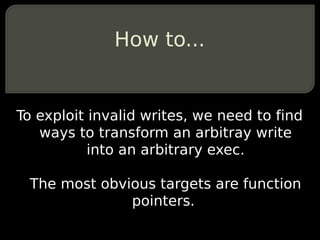
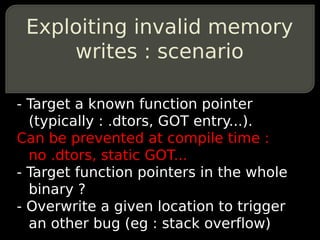
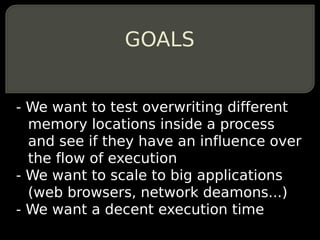
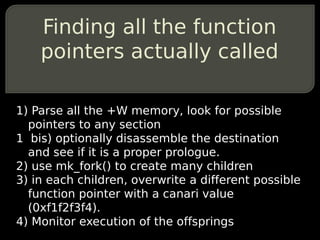
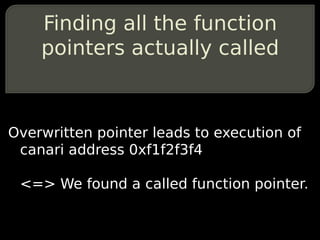
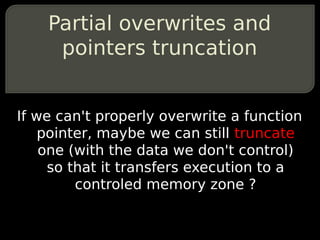
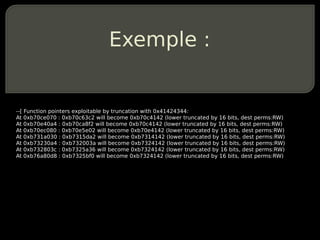
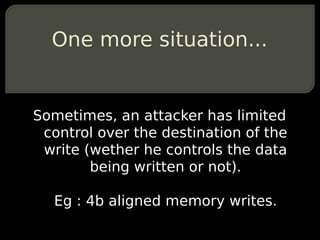
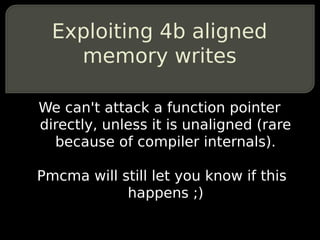
We will demonstrate how to:find all the function pointers inside a running process, how to determine which ones would have been dereferenced after the crash, which ones are truncable (in particular with 0x00000000). In case all of the above fail, how to test for specific locations overwrites in order to indirectly trigger a second vulnerability allowing greater control and eventually control flow hijacking. All of the above without source code, indeed ;)
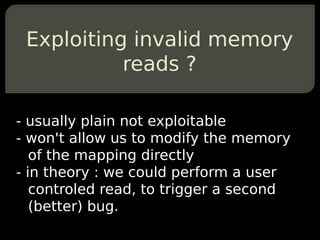
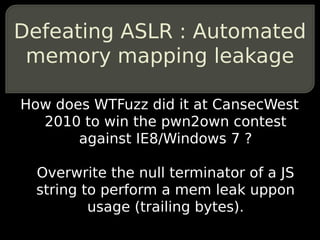
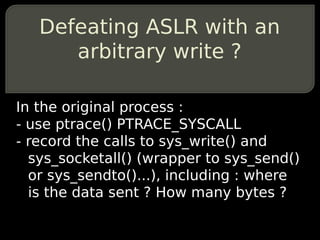
In the case of invalid memory reads, we will exemplify how indirectly influence the control flow of execution by reading arbitary values, how to trace all the unaligned memory access and how to test if an invalid read can be turned into an invalid write or used to infere the mapping of the binary.
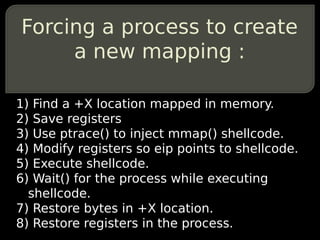
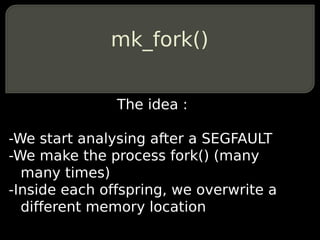
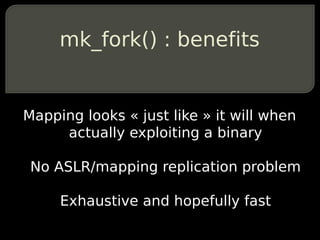
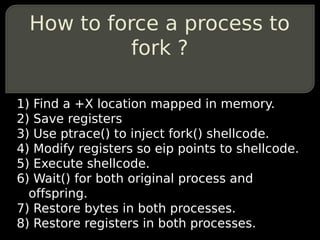
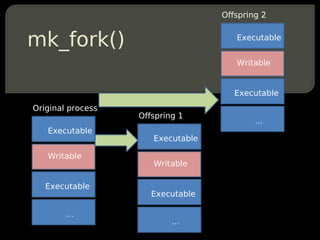
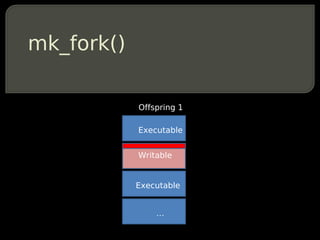
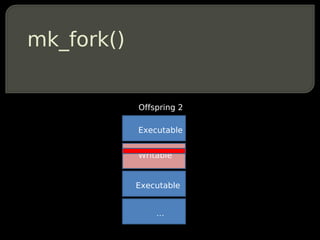
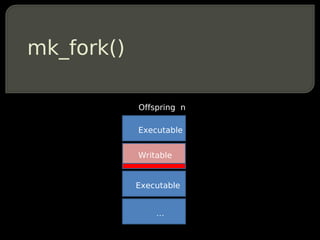
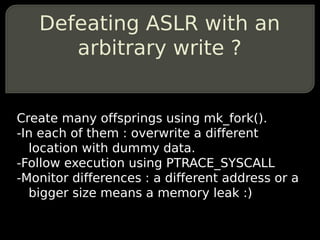
We will also introduce a new debugging technique which allows for very effective testing of all of the above by forcing the debugged process to fork(). Automatically. And with a rating of the best read/write location based on probabilities of mapping addresses (because of ASLR).
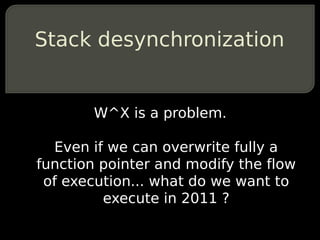
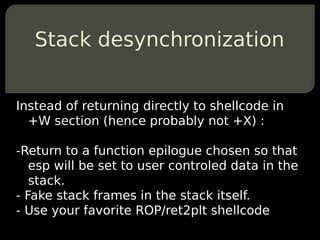
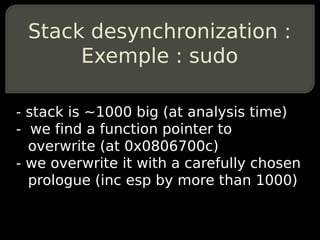
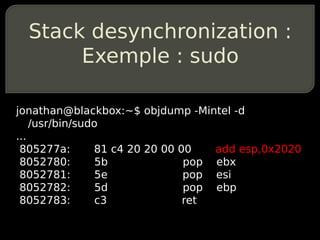
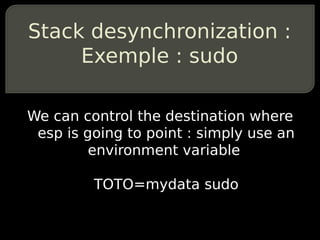
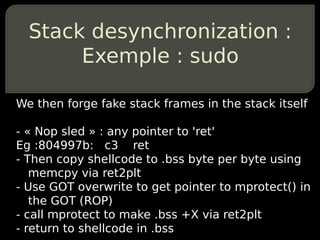
Finally, since overwriting function pointers doesn't allow direct shellcode execution because of W^X mappings, we introduce a new exploitation technique which works even in the most hardcore kernels such as grsecurity. IT is called "stack desynchronization" and allows frame faking inside the stack itself.
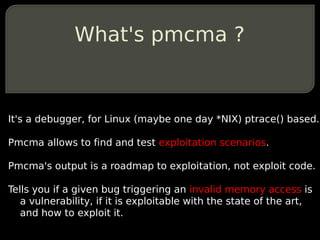
Those techniques are implemented in the form of a proof of concept tool running under x86 GNU/Linux to be released during the conference : pmcma.

![Invalid memory reads (1/2)
Eg :
CVE-2011-0761 (Perl)
cmp BYTE PTR [ebx+0x8],0x9](https://image.slidesharecdn.com/bhus2011brossard-110912094902-phpapp01/85/Blackhat-US-2011-Post-Memory-Corruption-Memory-Analysis-13-320.jpg)
![Invalid memory reads (2/2)
Eg :
CVE-2011-0764 (t1lib)
fld QWORD PTR [eax+0x8]](https://image.slidesharecdn.com/bhus2011brossard-110912094902-phpapp01/85/Blackhat-US-2011-Post-Memory-Corruption-Memory-Analysis-14-320.jpg)
![Invalid memory writes
Eg :
CVE-2011-1824 (Opera)
mov DWORD PTR [ebx+edx*1],eax](https://image.slidesharecdn.com/bhus2011brossard-110912094902-phpapp01/85/Blackhat-US-2011-Post-Memory-Corruption-Memory-Analysis-16-320.jpg)


![Means of modifying the
flow of execution without
function pointers
Call tables.
Calling [Offset+register]
=> This is also already performed
automatically using pmcma.](https://image.slidesharecdn.com/bhus2011brossard-110912094902-phpapp01/85/Blackhat-US-2011-Post-Memory-Corruption-Memory-Analysis-67-320.jpg)