SeverityNegligiblesmallunimportant;not likely to have.docx
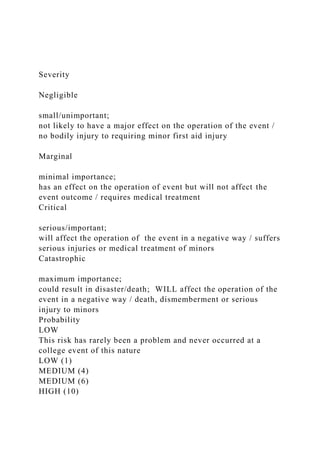
- 1. Severity Negligible small/unimportant; not likely to have a major effect on the operation of the event / no bodily injury to requiring minor first aid injury Marginal minimal importance; has an effect on the operation of event but will not affect the event outcome / requires medical treatment Critical serious/important; will affect the operation of the event in a negative way / suffers serious injuries or medical treatment of minors Catastrophic maximum importance; could result in disaster/death; WILL affect the operation of the event in a negative way / death, dismemberment or serious injury to minors Probability LOW This risk has rarely been a problem and never occurred at a college event of this nature LOW (1) MEDIUM (4) MEDIUM (6) HIGH (10)
- 2. MEDIUM This risk will MOST LIKELY occur at this event LOW (2) MEDIUM (5) HIGH (8) EXTREME (11) HIGH This risk WILL occur at this event, possibly multiple times, and has occurred in the past MEDIUM (3) HIGH (7) HIGH (9) EXTREME (12) Risk Matrix ISOL536 DR. CHARLES DESASSURE UNIV. OF THE CUMBERLANDS SUMMER 2019 TYPE THE NAME OR YOUR COLLEGE OR UNIVERISTY HERE. TYPE ALL TEAM MEMBERS NAME. Explanation of Risk Ranking LOW MEDIUM If the consequences to this event/activity are LOW / MEDIUM, your group should be OK to proceed with this event/activity. It is advised that if the activity is MEDIUM, risk mitigation efforts should be made. HIGH If the consequences to this event/activity are HIGH, it is advised that you seek additional event planning support.
- 3. EXTREME If the consequences to this event/activity are EXTREME, it is advised that you do not hold this event without prior consultation with Risk Management Risk Assessment Table (Sample). Do not complete. List All Activities Your activity name Associated Risk(s) Risk(s) associated with the activity Severity Level of impact on the trip and students Probability The chances of that risk happening Risk Score Risk score, found by combining impact and probability on the risk matrix Method(s) to Manage the Risk A list of methods you will use to minimize the chances of the risk happening and/or the resulting damages of the risk Playing Chess in Classroom A 1. Damaging College property 2. Competition sparks fighting among participants 1. Negligible 2. Negligible 1. Low 2. Low 1. Low (1) 2. Low (1) Hiking on Unsteady Terrain with Elderly participants 1. Bodily Injury to participants
- 4. 1. Critical 1. Low 1. Medium (6) 1. Educate participants regarding conditions of activity, appropriate footwear and caution against risk of bodily injury due to uneven terrain. Traveling to Boston with students for a conference 1. Auto Accident 1. Catastrophic 1. Low 1. High (10) 1. Ensure Drivers are credentialed, use a College vehicle to ensure it is properly insured, educate passengers on vehicle safety Note: YOUR TEAM WILL NEED TO COMPLETE THIS
- 5. SECTION. FIVE DIFFERENT THRETS ARE REQUIRED. Risk Assessment Table List All Activities Your activity name Associated Risk(s) Risk(s) associated with the activity Severity Level of impact on the trip and students Probability The chances of that risk happening Risk Score Risk score, found by combining impact and probability on the risk matrix Method(s) to Manage the Risk A list of methods you will use to minimize the chances of the risk happening and/or the resulting damages of the risk
- 6. Risk Assessment Table List All Activities Your activity name Associated Risk(s) Risk(s) associated with the activity Severity Level of impact on the trip and students Probability The chances of that risk happening Risk Score Risk score, found by combining impact and probability on the risk matrix Method(s) to Manage the Risk A list of methods you will use to minimize the chances of the risk happening and/or the resulting damages of the risk
- 8. Team System Design Group Project Instructions Overview The purpose of this activity is for your team to put everything that we have learned thus far into one system. Your group will design a large-scale grading system for college or university from scratch. Setup This activity is a group project. Each group should have at least three students. We may have to adjust the team because some students dropped the course or did not attend the Dallas Residency. Activity 1. For this project, your team is in charge of designing and planning the development of a secure system for storing student’s records at a college or university of about 15,000 students. Think of this as a real- world implementation project. If you have questions about the functionality of
- 9. the system please ask the instructor. Some basic requirements are below: A. Instructors should be able to view the grades of the students. B. School admins should be able to view the grades of any student and up-date grade with an Approved Grade Change Form. C. Students may view only their own grades. D. The system should be a web-based system. E. The system should account for user management. F. Student’s grades I emailed, and physically mail at the conclusion of the course. Tasks 1. Use the template (s) located on the course website to help your group complete this project. 2. Think of recommendations on how your group can improve the basic requirements of this system.
- 10. <college or university Name>team system Plan Course: ISOL536 – Security Architecture and Design Dr. Charles DeSassure, Adjunct Professor Graduate Computer Science Program University of the Cumberlands Type the Group Number Type the current date Team System Project using MS Access Page 10 of 11 OVERVIEW College or University Name: <Make up an imaginary name.> Overview: <Provide an overview or the group college or university. You may include some information from the instructions. Delete this line.> ROLE AND RESPONSIBILITIES Name/Role/Responsibilities Member Picture Type team member name Role on this Project Insert a quality head picure of yourself. Adjust photo so it can appear professionally. Add additional rows if required, an
- 11. delete empty rows. <Delete these instructions> SYSTEM REQUIREMENTS (Tables) Include the name of all table tables that will exist within your system. Provide a brief overview of each table, two or three lines will be fine. Include only the table information on this page. Single space with a double line space between tables. <Delete these instructions>. No Table Name Purpose SYSTEM REQUIREMENTS (Relationships) Indicate which table will have relationships to what type and
- 12. explain why <Delete these instructions> No Table Name Which Field Index Field/Key SYSTEM REQUIREMENTS (Reports) Indicate the type of reports that will be generated by the system. Five different types of reports are required. Provide the purpose of each report <Delete these instructions> No Report Name Purpose SECURE SYSTEM REQUIREMENTS What is the group recommendation on what is required for this
- 13. sysem inorder for it to be a secure system? <Delete these instructions> No Requirement Purpose 1 2 3 4 5 MS ACCESS SYSTEM DESIGN – THREAT MODELING Now that your team has the system design completed, a team member will need to create a Threat Modeling Design (drawing) of the system. Use only the symbols that we have used in this class. Embed the system design into this report on this page. <Delete these instructions>. MS ACCESS SYSTEM DESIGN Now that your team has the system design completed, a team member needs to create each TABLE, each RELATIONSHIP, and each REPORT within MS Access. Input five records within
- 14. each table. <Delete these instructions>. Nothing should be on this page except the TITLE and the statement below. MS Access file uploaded to Blackboard. SYSTEM PROTECTION <Using MS Access Protection/System>. Password protect the file. Include the password for this file on this page before uploading to the professor. Test and test the system to ensure that the password is working. If not, the professor will not be able to review the group MS Access file. RECOMMENDATIONS Provide recommendations on how the group may enhance this system in the future.