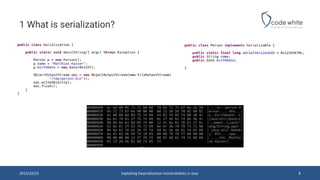
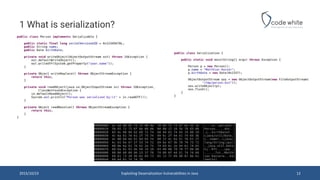
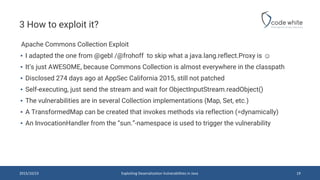
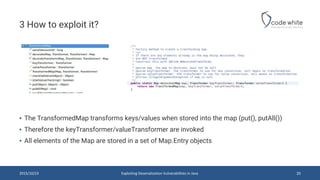
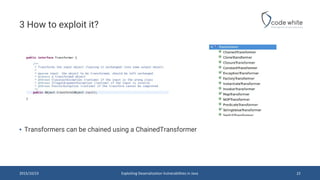
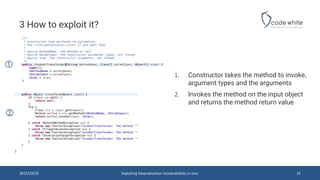
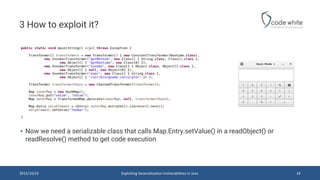
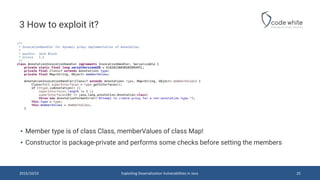
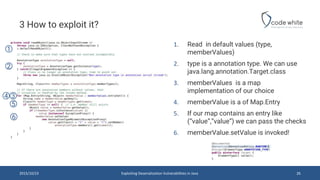
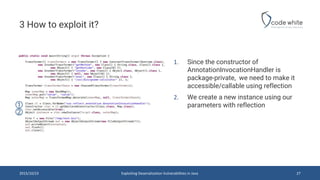
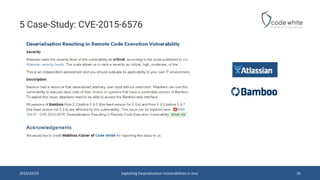
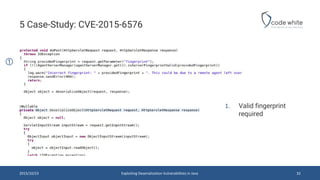
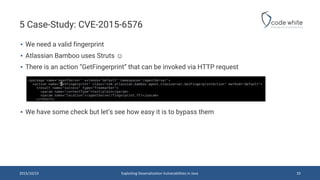
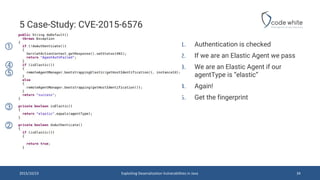
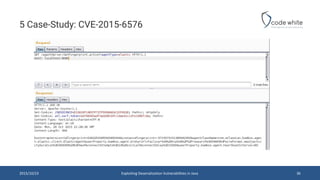
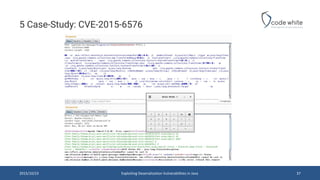
The document discusses deserialization vulnerabilities in Java, highlighting their relative obscurity compared to PHP unserialize vulnerabilities. It outlines the risks associated with deserialization, particularly focusing on how certain classes can lead to remote code execution if exploited correctly. Various exploitation techniques and case studies, including specific vulnerabilities like CVE-2015-6576, are presented to illustrate the topic's significance in the context of Java security research.