The Most Innovative Cyber Security Leaders to Watch in 2023.pdf
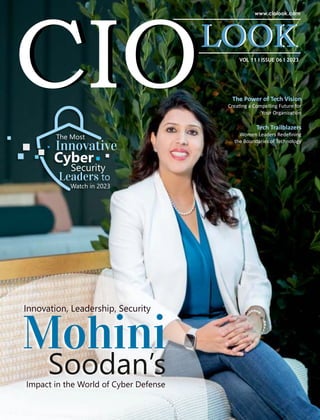
- 1. VOL 11 I ISSUE 06 I 2023 The Power of Tech Vision Crea ng a Compelling Future for Your Organiza on Innovation, Leadership, Security Mohini Soodan’s Impact in the World of Cyber Defense The Most Innovative Cyber Security Leaders to Watch in 2023 Tech Trailblazers Women Leaders Redefining the Boundaries of Technology
- 5. n the rapidly advancing digital age, where the stakes Iin cyberspace are higher than ever, our reliance on innovative cybersecurity solutions is paramount. As guardians of our interconnected world, cybersecurity leaders are not only tasked with protecting sensitive data but are also instrumental in shaping the future of technology. With a focus on these fundamentals, CIOLook presents a comprehensive exploration of “The Most Innovative Cybersecurity Leaders to Watch in 2023.” In an era where digital interconnectedness is both a blessing and a vulnerability, the individuals showcased here represent the front lines of defense against a myriad of cyber threats. Their commitment to innovation, coupled with their ability to adapt to an ever-changing threat landscape, positions them as leaders for today and the challenges that lie ahead. These leaders stand as beacons of inspiration, pushing the boundaries of what is possible in the cybersecurity domain. Their foresight, strategic thinking, and technical prowess are the driving forces behind the resilience of our digital infrastructure. In the following pages, you'll discover stories of tenacity, ingenious problem-solving, and a relentless pursuit of excellence. From disruptive startups to seasoned industry veterans, each profiled leader brings a unique perspective and skill set to cybersecurity. Their journeys and accomplishments will inform and inspire the next generation of cybersecurity professionals. The collaborative efforts and groundbreaking innovations showcased in this feature highlight the resilience of the cybersecurity community and its unwavering commitment to staying one step ahead of adversaries. CIOLook extends its gratitude to the featured leaders for sharing their experiences and expertise. May their stories serve as a source of motivation for all those dedicated to securing our digital future. Flip through the pages and have a delightful read! Impressive Traits in the Digital Business Arena Anishmiller
- 6. 17. Charles Henderson P r o fi l e s Filipi Pires A Leader Safeguarding the Digital Frontlines Olayinka Naa Dzama Wilson Kofhi Driving Informa on Security and Privacy in the Dynamic Industry A r t i c l e s 24. 32. 20. 28. Delivering Breakthrough Solu ons and Shaping the Future of IT The Power of Tech Vision Crea ng a Compelling Future for Your Organiza on Tech Trailblazers Women Leaders Redefining the Boundaries of Technology
- 7. 08 Story Innovation, Leadership, Security Mohini Soodan’s Impact in the World of Cyber Defense
- 9. Brief Company Name Filipi Pires Security Researcher/ Cybersecurity Advocate/ Advisor Filipi Pires has risen as a Cybersecurity Researcher, helping companies build sovereignty and security over access and privileged information. Charles Henderson Global Managing Partner and Head of X-Force With more than two decades of experience in the information security industry, Charles leads a global team of hackers, researchers, investigators and incident responders. IBM ibm.com Filipi Pires filipipires.com Ann Mennens Founding Member Ann Mennens is the Manager of the European Commission's Cyber Aware Programme, aimed at raising the cyber awareness of the whole Commission staff. Women4Cyber Belgium women4cyber.eu Mohini Soodan Sr. CyberSecurity Architect, Global Chair For Culture & Heritage G100 (Group of 100 Global Women Leaders) Mohini Soodan is an illustrious figure in the realm of cybersecurity whose accolades paint a vivid picture of her prowess and leadership. Microsoft microsoft.com Ericsson ericsson.com Olayinka Naa Dzama Wilson-Kofi is a dynamic leader and an Information Security and Privacy Specialist who has made significant contributions to this industry. Olayinka Wilson-Kofi Information Security and Privacy Specialist Featured Person The Most Innovative Cyber Security Leaders to Watch in 2023
- 10. Mohini Soodan Sr. CyberSecurity Architect @Microsoft, Global Chair For Culture & Heritage G100 (Group of 100 Global Women Leaders)
- 11. Innovation, Leadership, Security Mohini Soodan’s Impact in the World of Cyber Defense We guide and lead cybersecurity initiatives, partnering with CISOs and security stakeholders, designing strategies that see cybersecurity as a business risk, not just a technical concern.” “
- 12. ohini Soodan is an illustrious figure in the Mrealm of cybersecurity whose accolades paint a vivid picture of her prowess and leadership. As an award-winning Sr. Lead Cybersecurity Architect at Microsoft Global security Team and G100 Chairman in the USA, Mohini stands among the top 100 global leaders. Her influence reverberates internationally as a keynote speaker, researcher and security advocate. Mohini’s expertise transcends boundaries, as evidenced by her role in building Microsoft’s global security teams and her association with the prestigious National Security Team at Microsoft. Among her notable achievements, Mohini conducted a groundbreaking case study on the Colonial Pipeline ransomware attack, offering invaluable insights to combat future cyber threats. Her contributions extend to prestigious institutions like Harvard University, where she conducted impactful research on ransomware attacks. Mohini’s passion extends beyond her professional sphere—she mentors women from non-tech backgrounds, empowering them to excel in the cybersecurity domain. A Harvard Alumni with an executive degree in cybersecurity, Mohini is not only an advocate for women in tech but also a globe-trotter, a music enthusiast and a yoga practitioner. Her influence in the cybersecurity space resonates through her podcasts, keynote speeches and media coverage, making her a true luminary in the field. In her impactful role, Mohini shoulders the responsibility of shaping the cybersecurity landscape for Microsoft and its clients positioned as the Sr. Lead Cybersecurity Architect at Microsoft Global security Team of the Global Security Team. With a direct focus on managing a team comprising Cloud Security Architects (CSA’s) and Customer Engineers (CE’s), she orchestrates a strategic vision for security. Mohini manages a Team of Security Architects, Security Advisors, meticulously defining the roadmap for security. She crafts concrete architectures for Microsoft’s top global clients, emphasizing Authentication Best Practices and ensuring a secure digital environment. Working closely with CISOs, security executives, Executive Vice Presidents at Microsoft, and Sales Heads in the Midwest, Mohini forges collaborations. She pioneers core security management, championing security, data protection, and privacy features at the foundational level. Mohini’s leadership is evident in her approach to nurturing talent. She mentors new cloud architects, oversees the hiring process for security architects and establishes a dynamic team focused on security architecture and design solutions. Under her guidance, a new Application Security Team is born, collaborating with Global Black Belts Teams worldwide to fortify Microsoft’s security stance. Let’s explore and engage with Mohini’s insights, experience award-winning knowledge and how she is fortifying security against evolving threats! Bridging the Cyber Chasm Mohini is dedicated to fortifying the digital world against evolving threats. With unwavering determination, Mohini stands as a guardian, supporting global cybersecurity initiatives for Microsoft’s top partners, enterprise Federal Organizations, CISOs, and security stakeholders. Mohini’s mission is clear, “We empower them with proper security measures.” In her role, Mohini orchestrates essential conversations on the Future of Cybersecurity, emphasizing the importance of a robust security architecture. She champions the implementation of Zero Trust principles, offering guidance that protects individuals and businesses alike. Through end-to-end assessments, Mohini ensures the safety of valuable assets, preventing theft and damage. Her focus on innovation is evident, “Engaging with all top executives to defend against these threats and build security strategies and new approaches to cybersecurity improvement and innovation which is powered by AI.” Mohini’s efforts extend beyond the conventional, reaching into the realm of digital strategy. She crafts intricate security roadmaps, helping organizations globally fortify their digital states. In her hands, the future of cybersecurity is not just secure—it’s empowered. Forging Iron Bonds Mohini is an integral part of Microsoft’s Global Security
- 13. “We use sophisticated data analysis and AI algorithms to better understand and protect against digital threats against Future Cyber-criminal activity.”
- 14. Ransomware attacks are becoming more sophisticated, especially in regions like the Middle East, Africa and the UAE.” “
- 15. Team where she is reshaping the approach to digital defense. Mohini’s philosophy is clear, “We guide and lead cybersecurity initiatives, partnering with CISOs and security stakeholders, designing strategies that see cybersecurity as a business risk, not just a technical concern.” In the face of evolving threats, Mohini advocates a proactive stance, emphasizing the need for a culture of accountability, “Planning is everything, simulation exercises can help.” This approach fosters resilience, ensuring organizations can navigate the complexities of modern cyberattacks. Mohini believes in empowering IT teams, advocating for clear expectations, robust security policies and a deep understanding of security states. “We empower them with the right Cybersecurity measures, creating a strong cybersecurity culture in protecting IT infrastructures, devices, data, network, etc.” Collaboration is key, as Mohini works hand in hand with security executives, implementing the Zero Trust model effectively. To her, this isn’t just a job—it’s a responsibility, “We have a duty to protect the digital systems underpinning our modern society.” Strengthening Shields Mohini is a digital guardian who advocates a transformative approach, stating, “Our top approach is the implementation of the Zero Trust Framework, where we never trust, always verify.” Guided by this principle, her team challenges assumptions, assuming breach and meticulously verifying each asset. The corporate walls may stand, but behind them, a robust verification process is at play, ensuring safety and security at every turn. Embracing the power of technology, Mohini and her team delve deep into the digital realm, employing advanced data analysis and AI algorithms. In her words, “We use sophisticated data analysis and AI algorithms to better understand and protect against digital threats and future Cyber-criminal activity.” This isn’t just cybersecurity—it’s a proactive, intelligent defense strategy. With a keen eye on the future, Mohini fosters an environment where trust is earned, not assumed. Every digital interaction, every piece of data, is scrutinized and fortified and it’s about empowering a safer, more resilient digital tomorrow for all. Beyond Thunderclouds In the landscape of cybersecurity, Mohini is a trailblazer championing transformative strategies. “We must incorporate smart Cybersecurity policies, Modernize and simplify with Zero Trust,” she asserts, urging organizations to heed this call to action. In her vision: Ÿ Modernization through Zero Trust: Mohini emphasizes the urgent need for organizations to modernize security programs, simplifying the complex with Zero Trust principles. This approach ensures agile security, enabling swift adaptation to evolving threats. Ÿ Alignment of Security to Business + IT: To fortify digital fortresses, Mohini advocates aligning security with business and IT. This integration ensures security becomes an inherent part of organizational processes, securing what truly matters and avoiding wasted efforts on low-value assets. Ÿ Partnerships and Understanding: Building genuine partnerships and fostering a security-focused understanding of business priorities are pivotal. Mohini emphasizes the importance of collaboration, where security teams comprehend the nuances of future risks and align their efforts accordingly. Ÿ Embracing Innovation: To optimize resources, embracing new security and technology innovations is crucial. Mohini advocates avoiding wasteful manual tasks and ineffective efforts, steering security teams toward impactful strategies. Ÿ Accountability and Expertise: A key facet of success lies in distributing security risk accountability. Business owners shoulder security risks while security teams, as subject matter experts, manage and mitigate these risks effectively. Securing Boundaries, Bridging Regulations Mohini represents Microsoft’s unwavering commitment and asserts, “Privacy is a fundamental right
- 16. and GDPR is a crucial step forward.” Microsoft, under her guidance, is championing privacy rights. Here’s how: Ÿ Microsoft’s Commitment to GDPR: Microsoft not only believes in the essence of GDPR but also embodies it. Mohini ensures, “We are committed to our own compliance with the GDPR,” showcasing a dedication that goes beyond mere words. Ÿ Supporting Compliance Obligations: Microsoft doesn’t just comply—it empowers others to do so too. With an array of products and resources, Mohini states, “We provide products, features, documentation, and resources to support our customers in meeting their compliance obligations under the GDPR.” It’s a partnership, a collective endeavor. Ÿ The Zero Trust Framework: Mohini, as a proponent of the Zero Trust framework, sees it as more than just a security measure. It’s a vital component of a larger governance model. “Zero Trust serves as part of a larger governance model,” she affirms, acknowledging its role in establishing a hierarchy of requirements within organizations. Ÿ Diverse Approaches in Compliance: Mohini recognizes the complexity of compliance. In her view, “In the compliance and regulatory space, there can be many ways to achieve the same requirement or control.” She embraces diversity in strategies, understanding that flexibility and adaptability are key. Beyond the Firewall Amidst the digital challenges of 2023, Mohini navigates the intricate landscape of cybersecurity with resolute determination. She reflects on the evolving threat of ransomware, noting, “Ransomware attacks are becoming more sophisticated, especially in regions like the Middle East, Africa and the UAE.” In her vision, collaboration and innovation are paramount: Ÿ Facing Ransomware Head-On: Mohini acknowledges the harsh reality: ransomware attacks have become a critical challenge. The recent Microsoft-IDC research underscores this, revealing that organizations in the UAE and Qatar are grappling with a growing number of attacks. “It’s hardly surprising given the impact - 40 percent of UAE- based organizations forced to shut down, losing a total of $1.4 million,” she emphasizes, highlighting the urgency of the situation. Ÿ Learning and Sharing: Mohini champions collaboration, stating, “Microsoft works with our customers and industry organizations to both share our learnings and learn from them.” This exchange of knowledge and insights creates a collective shield, fortifying organizations against the onslaught of ransomware. Ÿ Investment in Defenses: Microsoft, under Mohini’s leadership, invests heavily in capabilities. These efforts are not just about defense—they are about empowerment. “We have heavily invested in capabilities to help organizations defeat attack techniques found in both everyday and sophisticated targeted attacks,” she affirms, indicating a proactive stance against evolving threats. Unite or Fall In the realm of evolving regulations, Mohini emphasizes, “To be really successful, we must have a solid cooperation with all of our varied stakeholders and practice transparency.” Microsoft Security, under her guidance, harnesses machine learning to navigate the influx of regulatory information. It’s not just about data—it’s about collaboration and openness. Through her approach, understanding complex regulations becomes not just a challenge but an opportunity for unity and progress. Shaping Future Cloud Custodians Mohini leads with purpose and underscores, “Communications and listening are the key to success.” Under her guidance, Microsoft fosters a nurturing atmosphere, blending technical mentorship with critical thinking. “We challenge and empower our team with solving real-world cyber-attacks,” she asserts, emphasizing the importance of hands-on problem- solving. The qualities sought in talent echo this ethos: Ÿ Passion for Learning and Success: A dedication to continuous learning and delivering success for all. Ÿ Problem-solving and Adaptability: Skills to tackle evolving cybersecurity threats with adaptability. Ÿ Hunger for Learning and Teamwork: An eagerness to learn new skills and a collaborative attitude. Keys to Every Lock At the helm of Microsoft’s global security team, Mohini champions a unifying ethos: “Leading regular conversations, coordinated structured workflows,
- 17. prioritizing inclusiveness values all our team internationally and preserves through the challenges.” Under her guidance, technology unites international projects and inclusivity prevails. Embracing cultural diversity, Microsoft ensures training opportunities for all, fostering a culture of continuous learning and open discussions. Through Mohini’s leadership, Microsoft not only manages security but nurtures a global community where diversity thrives and knowledge knows no bounds. Beyond Bits and Bytes Discussing the challenges of cybersecurity Mohini notes, “End-to- end visibility, increasing cyber threats and swift response are key.” These challenges echo across every industry. Ensuring visibility into complex cloud architectures is crucial, matched only by the rise in cyber threats. Equally vital is the ability to respond swiftly and implement robust security controls. Mohini’s insights reflect a universal truth—the need for vigilance and adaptability in the face of evolving digital threats, a mission embraced by cybersecurity leaders globally.
- 18. www.ciolook.com | November 2023 | 16
- 19. C ybersecurity consulting services providers help provide security assurance for business and government entities. They work with businesses to protect data and systems against cyberattacks, as well as provide solutions to help prevent and remedy data breach incidents. In the rapidly evolving landscape of information security, IBM Security X-Force stands out for its unwavering commitment to innovation, excellence and cutting-edge approach. With a global presence and a strong reputation for delivering results, this company has solidified its position as a leader in the industry. At the helm of this dynamic organization is Charles Henderson, a visionary leader, the Global Managing Partner and the Head of X-Force. With extensive experience and a deep understanding of the intricacies of the information security sector, he is playing a pivotal role in driving the company's success and shaping its future. Having navigated the ever-changing technological landscape, Charles has consistently demonstrated exceptional leadership, strategic thinking and a relentless pursuit of excellence. His ability to identify emerging trends and anticipate market demands has been instrumental in his success. IBM Security X-Force is a threat-centric team of hackers, responders, researchers, and analysts. The X- Force portfolio includes offensive and defensive products and services, fueled by a 360-degree view of threats We at CIOLook interviewed Charles on pushing boundaries, challenging conventions and delivering extraordinary results for clients. Let’s delve into the insights of the interview! Fail-Fast Culture In the realm of cybersecurity, where the stakes are high and failure can have dire consequences, X-Force stands out as an organization that champions a fail-fast culture of experimentation. The company understands the importance of finding acceptable ways to fail, recognizing that it is precisely these failures that breed innovation. Moreover, X-Force recognizes that constant fear of failure can contribute to employee exhaustion and burnout, two challenges already prevalent in the security industry. Prank Culture Within X-Force, a unique prank culture has taken root, fostering a sense of camaraderie and team-building. X- Force has dedicated internal communication channels to this "prank culture," playfully dubbed "parrots." Every year, during the Def Con event, team members engage in pranks, creating memorable experiences that serve not only as team-building exercises but also as training grounds for the company. Taking a Unique View Charles’ impact on the dynamic industry stems from a unique perspective. Throughout his career, he has always emphasized looking at everything through the lens of an attacker. Charles says explaining the same, “Too often in information security, we think of our own goals and not the goals of the attacker. To be truly successful, it’s important to turn that on its head and look at everything through the eyes of an attacker.” www.ciolook.com | November 2023 | 17
- 20. Charles adds, “Additionally, looking at the problems we have to solve in security, it's not just about having a solution, but having a solution that can be used on a large scale and replicated effectively.” Take Penetration (pen) Testing as an example. At one point, it could cover an organization’s entire environment, but as businesses and environments grew, traditional pen testing couldn't keep up. It became impractical for a human to evaluate an entire environment. So, the need to adapt and find new ways to make testing more meaningful and relevant This means taking existing products and find ways to work for new challenges. And that’s one of the main areas that Charles tends to focus on – looking at how tools and technology can be used to scale and create efficiencies. Sector's Next Change: Taking the Leap Contemplating the next significant change in the cybersecurity sector, Charles anticipates that artificial intelligence (AI) will play a crucial role in the coming decade. Charles shares, “AI will have a meaningful impact on our industry in the next decade. At X-Force, we’re exploring how AI can elevate offensive and defensive capabilities.” www.ciolook.com | November 2023 | 18
- 21. X-Force is focused on addressing critical areas that have been overlooked or remain unsolved, such as patching and detection engineering, considering this as an example. Charles believes that the industry has a flaw-fixing problem, not a flaw-identifying problem. Patching is extremely labor intensive and minor improvements, at this point, would be insignificant. However, by leveraging AI, it may be possible to substantially improve speed, and volume. Innovation and Research at Scale Charles embraced technological innovations as a means to enhance its solutions and address the pervasive skills shortage in the industry. The organization constantly seeks ways to extend the reach and impact of its personnel through technology. For Charles, scalability is paramount. Research and innovation serve as the building blocks of X-Force, and using technology to to disseminate research and innovation to a wider audience is crucial for success. Journey as a Leader: Building the Right Culture As a dynamic leader within the industry, the individual at the helm of X-Force has faced numerous obstacles along his career. Building teams and attracting talent have consistently been major challenges in the industry. He states, “This holds true even in my entrepreneurial days.” Charles recognizes this and believes that building a culture that promotes innovation and that the type of culture people want to come work for is so important. The cybersecurity industry itself presents a constant challenge of keeping up with ever-evolving threat actors. X-Force acknowledges that security innovations are often driven by the innovations of its adversaries. In this highly competitive environment, X-Force not only competes with other security firms but also with threat actors. Envisioning Future Growth Looking ahead, it’s clear that AI is going to significantly shape the future of the industry which is whyX-Force is focusing on innovative research and exploring the impact of AI on defenders and attackers. X-Force is actively preparing for the changes that threat actors will bring in the next decade, particularly around how they will exploit AI advancements. By understanding the possibilities, we can get ahead of what’s to come. Aiming to stay ahead of the curve, understanding the possibilities and implications that lie ahead. Advice for Entrepreneurs For budding entrepreneurs aspiring to venture into the dynamic cybersecurity industry, Charles offers valuable advice: be part of the solution. A lot of entrepreneurs create a solution and then go look for a problem. It’s a lot easier to come up with an idea than an application for that idea. Put in a little more work upfront to find a problem that you can solve. That’s where you can make a real impact. www.ciolook.com | November 2023 | 19
- 22. n today's fast-paced and technology-driven world, having a clear and compelling vision for your Iestablishment's future is essential. Technology always plays a vital role in shaping the business landscape and driving innovation. This article explores the power of tech vision and how it can enable leaders to create a compelling future for their organizations. By harnessing the potential of technology and envisioning its application strategically, leaders can chart a path for growth, adapt to changing environments, and stay ahead of the competition. Defining Tech Vision Tech vision refers to a forward-thinking and aspirational perspective that leaders develop regarding the role of technology within their organization. It involves envisioning how emerging technologies can transform processes, disrupt industries, and create new opportunities. A well- defined tech vision provides a roadmap for leveraging technology to drive innovation, enhance operational efficiency, and deliver value to customers. Anticipating Technological Trends To create a compelling future, leaders must stay abreast of emerging technological trends and their potential impact on their industry. This requires continuous monitoring of advancements in areas such as Artificial Intelligence, IoT, blockchain, cloud computing, and data analytics. By identifying relevant trends early on, leaders can proactively integrate technology into their strategic planning and capitalize on emerging opportunities. Aligning Tech Vision with Business Strategy A powerful tech vision aligns with the overall business strategy and goals of the organization. It is not about adopting technology for the sake of it, but rather integrating technology to enable and enhance core business objectives. Leaders should ensure that their tech vision supports key strategic pillars such as improving customer experience, driving operational efficiency, fostering innovation, and enabling sustainable growth. Inspiring and Communicating the Vision A compelling tech vision should inspire and motivate stakeholders within the organization. Leaders must effectively communicate the vision, articulating the benefits and opportunities that Creatinga Compelling Future for Your Organization www.ciolook.com | 202 | November 3 20
- 23. The Power of Tech Vision www.ciolook.com | November 2023 | 21
- 24. technology brings. By painting a vivid picture of the future and highlighting how technology can transform processes, create new business models, and drive competitive advantage, leaders can rally support and commitment from employees, partners, and investors. Fostering a Culture of Innovation Creating a compelling future requires fostering a culture of innovation within the organization. Leaders should encourage experimentation, risk-taking, and learning from failures. By providing resources, incentives, and a supportive environment, leaders empower their teams to explore and leverage technology to drive creative solutions and disruptive ideas. An innovation-driven culture is crucial for transforming the tech vision into tangible outcomes. Continuous Learning and Adaptation Technology is constantly evolving, and leaders must embrace continuous learning to adapt their tech vision accordingly. This involves staying connected with industry trends, networking with experts, and investing in ongoing training and development. By fostering a learning mindset and remaining agile, leaders can ensure that their tech vision remains relevant and adaptable in the face of advancing technological landscapes. Driving Collaboration and Cross-Functional Alignment A compelling tech vision fosters collaboration and cross-functional alignment within the organization. It brings together diverse teams from different departments and disciplines, encouraging them to work together towards a shared goal. By promoting a common understanding of the organization's tech vision, leaders break down silos and facilitate the exchange of ideas, expertise, and resources. This collaborative approach unlocks synergies, promotes innovation, and propels the organization forward. Customer-Centric Innovation Tech vision empowers organizations to deliver exceptional customer experiences through customer- centric innovation. By leveraging technology, leaders can gain deep insights into customer needs and preferences, enabling the development of personalized products, services, and experiences. Tech vision drives a customer-centric mindset across the organization, ensuring that innovation efforts are focused on creating value and addressing customer pain points, ultimately fostering customer loyalty and differentiation in the market. Embracing Ethical and Responsible Technology Practices A compelling tech vision emphasizes ethical and responsible technology practices. Leaders recognize the potential impact of technology on society, privacy, and the environment. They actively incorporate ethical considerations into their tech vision, championing principles such as data privacy, transparency, and fairness. By integrating ethical practices into their technological advancements, organizations build trust, mitigate risks, and contribute to the greater social good. Empowering Agility and Adaptability Tech vision enables organizations to cultivate a culture of agility and adaptability. By envisioning a future empowered by technology, leaders inspire their teams to embrace change, experiment with new ideas, and continuously learn. This culture of agility allows organizations to respond swiftly to market shifts, capitalize on emerging opportunities, and pivot their strategies as needed. Tech vision acts as a guiding compass, ensuring that the organization remains flexible and resilient in the face of uncertainty. The power of tech vision lies in its ability to shape the future of organizations. By anticipating disruption, enabling digital transformation, fostering agility, driving collaboration, focusing on customer-centric innovation, and embracing ethical technology practices, leaders can create a compelling vision that propels their organization forward. Tech vision serves as a roadmap, guiding organizations through the complexities of the digital age and positioning them for sustained growth and success. By harnessing the power of tech vision, leaders can create a compelling future for their organizations and seize the opportunities presented with the transforming technological landscape. www.ciolook.com | November 2023 | 22
- 26. n open-minded leader is someone who is ready Ato explore new technologies, methodologies, and best practices in the company. Such a leader encourages the team to stay updated on the latest advancements and is willing to implement innovative solutions to enhance security. These security threats are evolving rapidly, emerging to those challenges requires a dynamic, agile, innovative, and adaptable mindset. To this response Filipi Pires has risen as a Cybersecurity Researcher, helping companies build sovereignty and security over access and privileged information. Filipi’s dedication and effort has earned a place in CIOLook’s latest edition of The Most Innovative Cyber Security Leaders to Watch in 2023. Below are the highlights of the interview Brief our audience about your journey as a dynamic leader until your current position at your company. What challenges have you had to overcome to reach where you are today? My name is Filipi Pires; I’m Brazilian, married, a father of 4 children, Christian, a musician and a lover of information security, hacking and technology. I currently live in Portugal and have been working in recent years as a Security and Threat Researcher and Cybersecurity Advocate. One of the great teachings that I received was always looking for the bases, that is, understanding the bases, operating systems bases, the bases of networks, the bases of infrastructure, understanding how cloud architecture works and so on, it is an area that we have constant learning, I always had the challenge of proving that even coming from a commercial area, I could be a technically good person, I believe that many can face this challenge in their career when they make a different transition as was my case, but you never can give up, you need to apply yourself and always seek to study to the fullest, and never seek the path that "seems" easier. I have been working as a Cybersecurity Researcher and Advocate in several projects involving the Hacking communities and opensource projects, such as Hacking is Not a Crime and Snyk, among others, over the last few years, I have worked in some countries like Poland, Brazil and Portugal, working with Penetration Testing, RedTeam, BlueTeam and Application Security, implementing DevSecOps culture and some organizations where I worked or even when I worked as a consulting company. Senhasegura's primary goal is to expand its reach to the international market while simultaneously championing the cause of digital sovereignty for a global society. “ “ www.ciolook.com | November 2023 | 24
- 27. www.ciolook.com | November 2023 | 25
- 28. I’m one of the founders of a company, operating in Brazil and Europe, called Black & White Technology, and I currently work for senhasegura, a company with worldwide technology made in Brazil, which has the mission "To help organizations build sovereignty and security over access and privileged information." that has expanded its activities worldwide. Finally, I leave here my final thoughts; you always need to do your best in whatever area you choose to work with, with dedication and effort you will get there! Enlighten us on how you have been impacting the dynamic industry through your expertise in the market. I believe that my contribution is related to where I worked/work as a Professor in college, graduated and MBA courses, teaching Malware Analysis, Cloud Security, Offensive Security, Threat Hunting and Incident Response. Another collaboration for Industry is related to my participation in events of Information Security of new technologies, mainly in events in the European Union. And finally, I'm an active member of some hacking communities (US, Brazil and Europe), helping with presentations, building trails at conferences and sharing Opensource content for everyone through social networks and events. Describe in detail the values and culture that drive your organization. Currently, I have been working as an Information Security Researcher at senhasegura; We strive to ensure the sovereignty of companies over actions and privileged information. To this end, we work against data theft through the traceability of administrator actions on networks, servers, databases and a multitude of devices. In addition, we pursue compliance with auditing requirements and the most demanding standards, including PCI DSS, Sarbanes-Oxley, ISO 27001 and HIPAA. What we believe as senhasegura is that protection, access, and confidentiality of privileged information are fundamental rights of any organization and society as a whole; our mission, is to be the best privileged access management solution in the global market. And the Mission is "to help organizations build sovereignty and security over access and privileged information.” Undeniably, technology is playing a significant role in almost every sector. How are you advancing towards technological innovations to make your solutions resourceful? In recent years, there has been a lot of talk about digital transformation in many sectors of the industry; we see a growing daily development of solutions using AI (Artificial Intelligence), new technologies inside factories and much more, with the increase of new technologies, we also see a large increase and evolution of threats. As a Security and Threat Researcher, I have been looking to understand how each attack works within Cloud environments, analysing and understanding how each attacker uses cloud permissions to escalate privileges. What, according to you, could be the next significant change in your sector? How is your company preparing to be a part of that change? When we look at the last 5 years (2018 to 2023), we see many types of attacks repeating themselves since the famous WannaCry attack in 2017. Attacks using ransomware as an attack vector have continued to be a very successful model in recent years, and it continues to be a very effective business model. There is already an industry that has grown a lot, with tutorials and the www.ciolook.com | November 2023 | 26
- 29. search for new insiders to carry out the necessary attacks, in addition to RaaS attacks - Ransowmare as a Service. Comparing the past with the future, we were able to observe that attacks always seek an identity with a certain level of permission, for this attack to occur, that is, for the execution of Ransomware, the infected user needs to have permission to execute the even in your environment when an access key is leaked, this key needs to have a certain type of privilege in your environment, that is, everything is related to the type of privilege that this identity has. Here is some information that according to Gartner about future attacks in the coming years: Ÿ By the end of 2023, modern data privacy laws will cover the personal information of 75% of the world's population. Ÿ By 2024, organizations that adopt a cybersecurity network architecture will be able to reduce the financial costs of security incidents by an average of 90% Ÿ By 2024, 30% of enterprises will deploy cloud- based Secure Web Gateway (SWG), Cloud Access Security Brokers (CASB), Zero Trust Network Access (ZTNA), and Firewall as a Service (FWaaS), sourced from the same vendor Ÿ By 2025, 60% of organizations will use cybersecurity risk as the primary determinant in conducting third-party transactions and business relationships Ÿ By 2025, 40% of boards will have a dedicated cybersecurity committee overseen by a qualified board member Ÿ By 2025, 70% of CEOs will build a culture of corporate resilience to protect themselves from threats from cybercrime, severe weather events, social events, and political instability Ÿ By 2025, cyber-attackers will be able to use operational technology environments as weapons successfully enough to cause human casualties. The percentage of states that enact laws regulating ransomware payments, fines and negotiations will increase from less than 1% in 2021 to 30% by the end of 2025 A significant change could be the increased integration of artificial intelligence and machine learning in cybersecurity. AI-powered tools can help organizations detect and respond to threats more effectively by analyzing vast amounts of data and identifying patterns indicative of malicious activity. senhasegura might focus on enhancing its AI capabilities and developing solutions that leverage machine learning to offer proactive and adaptive defense mechanisms. Where do you envision yourself to be in the long run, and what are your future goals for the organization? I'm currently very happy doing one of my dreams as a Security Researcher and Cybersecurity Advocate, for the future what I’m looking for is to focus on being Threat Researcher, maybe creating a Threat Security Team to understand how APTs groups create their attacks, investigating their attacks and how this knowledge can help enterprise organizations to anticipate possible attacks. senhasegura's primary goal is to expand its reach to the international market while simultaneously championing the cause of digital sovereignty for global society. With a steadfast commitment to security and innovation, the company seeks to empower organizations worldwide with cutting-edge solutions that safeguard their critical assets and sensitive data. What would be your advice to budding entrepreneurs who aspire to venture into the dynamic industry? Keep your focus and determination, no matter what area you work in, you always need to do the best in whatever area you choose to work in; with dedication and effort, you'll get there! Remember that you are unique, and that's why your work is unique, don't be in a hurry to speed things up; to grow in any industry and especially in cybersecurity, you need to master the basics very well, so don't rush, solidify your knowledge well and step by step you will evolve. www.ciolook.com | November 2023 | 27
- 30. WomenLeaders Redening the Boundariesof Technology WomenLeaders Redening the Boundariesof Technology n an era of unprecedented technological advancements, women are increasingly Iplaying a pivotal role in reshaping the landscape of the tech industry. With their relentless determination, unwavering passion and exceptional skills, women leaders are breaking down barriers and redefining the boundaries of technology. Women leaders in technology are rewriting the narrative, redefining the boundaries of what is possible, and driving innovation across industries. In this article, we will explore the remarkable achievements and contributions of these trailblazers, who not only inspire but also pave the way for a more inclusive and innovative future. Challenging Norms: Overcoming Obstacles in a Male-Dominated Industry Shattering Stereotypes Women leaders in technology have overcome countless obstacles to make their mark in what has historically been a male-dominated industry. They have shattered stereotypes, debunking the notion that certain fields are exclusively meant for men. By excelling in technical roles and leadership positions, they prove that gender is not a barrier to success in the tech world. Inspiring the Next Generation The accomplishments of women leaders in technology serve as an inspiration for young girls and women who aspire to pursue careers in this field. By sharing their stories and serving as role models, these trailblazers motivate and empower future generations to believe in their abilities and pursue their passion for technology, thereby creating a more diverse and inclusive industry. Driving Innovation: Embracing Diversity and Creativity Diverse Perspectives Women leaders bring a wealth of diverse perspectives to the tech industry. Their unique experiences, insights and approaches to problem-solving drive innovation and foster www.ciolook.com | 202 | November 3 28
- 31. Tech Trailblazers www.ciolook.com | November 2023 | 29
- 32. creativity. By embracing diversity, companies gain a competitive edge, as these trailblazers offer fresh insights and solutions that stem from their distinct backgrounds and perspectives. User-Centric Design Women leaders excel in designing user-centric products and services that cater to a wide range of individuals. Their deep understanding of user needs and empathy enables them to develop innovative solutions that enhance user experiences. By prioritizing inclusivity and accessibility, these leaders ensure that technology benefits everyone and leaves no one behind. Navigating Challenges: Breaking Barriers and Advocating for Change Overcoming Bias Women leaders in technology face inherent biases and systemic challenges. However, their resilience and determination enable them to overcome these hurdles. By showcasing their expertise and skills, they challenge preconceived notions and pave the way for more equitable opportunities for women in the tech industry. Advocacy and Mentorship Trailblazing women leaders understand the importance of advocacy and mentorship. They actively promote and support other women in the field, offering guidance, mentorship and opportunities for growth. Through their advocacy and mentorship efforts, they create a supportive ecosystem that nurtures talent and fosters the success of women in technology. Transforming Industries: Impacting Various Sectors Tech Entrepreneurship Women leaders are making significant strides in tech entrepreneurship, founding and leading successful startups that disrupt industries and drive innovation. Their entrepreneurial ventures not only create economic opportunities but also inspire others to follow in their footsteps and challenge the status quo. Artificial Intelligence and Data Science In the realm of artificial intelligence and data science, women leaders are making groundbreaking contributions. From developing advanced algorithms to ensuring ethical and responsible use of AI, these trailblazers are shaping the future of these emerging fields and making them more inclusive and equitable. Future Prospects: Paving the Way for Progress Increasing Representation The future holds great promise for women leaders in technology as organizations increasingly recognize the value of diversity and inclusion. Efforts are being made to create more opportunities and eliminate gender biases, leading to increased representation of women in technical roles and leadership positions. Collaboration and Networking Collaboration and networking are essential for women leaders to thrive in the tech industry. Building strong networks and fostering collaborations will enable them to share knowledge, exchange ideas and support each other's growth, resulting in a more cohesive and supportive community of women in technology. Through their remarkable achievements, they inspire future generations and create a more inclusive and diverse tech ecosystem. In the future, we can expect to witness a continued rise of women leaders in the technology industry as organizations recognize the importance of diversity and inclusion. These trailblazers will continue to redefine the boundaries of technology by bringing their unique perspectives and innovative ideas to the forefront. They will play a crucial role in shaping emerging fields such as artificial intelligence, blockchain and quantum computing while driving advancements in areas such as cybersecurity, data analytics and digital transformation. Additionally, women leaders will continue to advocate for equal opportunities, mentorship programs and initiatives that promote gender equality in the tech sector. Their unwavering determination and contributions will pave the way for a future where women's leadership in technology is not only celebrated but becomes the norm, fostering a truly inclusive and thriving tech industry. The trail they blaze today will pave the way for a brighter and more equitable future in the world of technology. www.ciolook.com | November 2023 | 30
- 34. Driving Information Security and Privacy in the Dynamic Industry he field of information security and privacy is a Trapidly evolving sector driven by the increasing reliance on technology and the rising threats of cyberattacks. Cybersecurity is now a global priority as cybercrime and digital threats grow in frequency and complexity. The role of an information security professional is to identify security risks before hackers do, and then develop and implement new preventative security controls for defending against cyberattacks. The cybersecurity workforce shortage and lack of new professionals funneling into this industry are one of the major obstacles to preventing cybercrime. Olayinka Naa Dzama Wilson-Kofi is a dynamic leader and an Information Security and Privacy Specialist who has made significant contributions to this industry. With her expertise and passion for cybersecurity, she has become a driving force in ensuring the confidentiality, integrity and availability of critical information systems. Currently associated with Ericsson (Middle East & Africa) and serving as the President of the Women in Cybersecurity (WiCyS) West Africa Affiliate, Olayinka continues to make a profound impact in the industry. She is overcoming challenges and making significant contributions to the dynamic industry of cybersecurity. With her leadership, expertise and commitment to continuous learning, Olayinka is driving advancements in technology, promoting ethical conduct and ensuring the security of critical information systems. As she continues to empower and mentor others, Olayinka envisions a future where organizations prioritize cybersecurity and privacy, safeguarding their data and ensuring a secure digital landscape. Let’s delve into Olayinka’s approach to leading the dynamic sector of information and security! Journey as a Dynamic Leader Olayinka’s journey began with an internship at Odade Publishers in Lagos, Nigeria, where she worked as an Assistant Virtual Librarian. Afterwards, she served at the Ghana Highway Authority as an IT Support personnel as part of National Service. Her roles included resolving network issues and training staff on IT system usage. Building on this foundation, Olayinka joined the National Lottery Authority (NLA), Accra, Ghana as Customer Service & Helpdesk Support, where she not only set up daily lotto games but also provided technical support to customers. With determination to excel in a male-dominated industry, Olayinka decided to pursue a career in Cyber and Information Security. Her motivation stemmed from the desire to secure the information technology infrastructure of the National Lottery Authority through the principles of Confidentiality, Integrity and Availability (CIA) Triad. She played a pivotal role in initiating an information security program and establishing a security sub-unit within the IT department. Olayinka was appointed as the information security and assurance officer, responsible for enhancing the CIA of IT systems, conducting risk assessments and ensuring system resilience for uninterrupted customer access. Olayinka’s journey also included a senior consulting role at Innovare Africa, where she implemented and managed ISO 27001 (Information Security) and ISO 22301 (Business Continuity) for various organizations, including IT Consortium and FinTech companies in Ghana. She shares, “As a go-getter, I was hungry to grow and hone my skills in emerging technology, security frameworks and its applicability in global companies.” Subsequently, she transitioned to eProcess www.ciolook.com | November 2023 | 32
- 35. O Olayinka Naa Dzama Wilson-Kofi Informa on Security and Privacy Specialist Ericsson (Middle East & Africa), Women in Cybersecurity (WiCyS) West Africa Affiliate www.ciolook.com | November 2023 | 33
- 36. International S.A. as the Business Security Manager within the Cybersecurity Department. She says, “From my experience with E-Council CCISO, it has helped with my leadership drive. Thanks to the knowledge and skills obtained from the CCISO training.” She also adds, “It has helped me grow personally and professionally, and there’s been a huge growth in the West Africa Affiliate, making it very attractive for other affiliates to collaborate. As a result, I have been able to help setup the Nigeria affiliate and student chapters both in Ghana and Rwanda.” In addition to her professional endeavors, Olayinka started the Women in Cybersecurity (WiCyS) West Africa Affiliate with other ladies and currently serves as its President. Through this initiative, she aims to empower and guide young women aspiring to enter the cybersecurity field. Olayinka is also an active participant in ISACA Accra Chapter and serves as a WiCyS Global Mentor and Mentee, providing guidance and sharing her experiences with others. She is also a member of Internet Security Forum (ISF) and the Organization for Women in Science for the Developing World (OWSD). Impact on the Dynamic Industry Olayinka’s expertise in cybersecurity has had a profound impact on the industry. Throughout her career, she has assisted businesses in implementing security frameworks, leveraging cutting-edge technologies such as Artificial Intelligence (AI) and Machine Learning (ML) to enhance threat detection and response. Her emphasis on ethical conduct and integrity has ensured adherence to legal and regulatory requirements, promoting honesty, professionalism and transparency within organizations. Olayinka’s leadership approach is characterized by a security-first mindset, prioritizing the consideration of security in every aspect of operations. She actively promotes continuous learning and adapts to emerging technologies and practices by pursuing a Ph.D. in Cybersecurity and obtaining relevant professional certifications. Her commitment to knowledge sharing and collaboration fosters an environment of teamwork and innovation. Olayinka also implements risk-based approaches, ensuring robust risk management frameworks and holding individuals accountable throughout the risk management process. Thought Leadership Olayinka actively contributes to the cybersecurity community by sharing her knowledge and insights through blog posts, articles and speaking engagements at industry conferences. Her thought leadership helps raise awareness about emerging threats, best practices and the importance of information security and privacy. Advocacy for Diversity and Inclusion Olayinka is a strong advocate for diversity and inclusion in the cybersecurity industry. She actively works towards bridging the gender gap and encourages more women to pursue careers in cybersecurity. Through her involvement in organizations like WiCyS, she promotes diversity and provides mentorship opportunities to aspiring female cybersecurity professionals. She shares, “During my early career stages, I lacked the mentor–mentee opportunity for career guidance, hence the motivation to give back. I am ready to make every opportunity worth it as it appears.” Incentivizing Challenges Throughout her journey, Olayinka encountered various challenges, including rapidly evolving cyber threats and the need to stay up to date with the latest security practices. She shares, “I had the challenge of not having a female mentor; I had a mentor, Mr. C.K. Bruce, CEO of Innovare Africa, who is my solid foundation to date.” However, these challenges pushed Olayinka to enhance her knowledge and skills by continuously investing in herself. Staying in Sync As an Information Security and Privacy Specialist, Olayinka recognizes the importance of staying in sync with the dynamic nature of the sector. She stays updated on evolving privacy regulations, participating in privacy-focused communities, webinars, conferences and workshops. By collaborating with other privacy specialists, she develops robust privacy frameworks that align with emerging requirements. www.ciolook.com | November 2023 | 34
- 37. With a determination to excel in a male- dominated industry, Olayinka decided to pursue a career in Cyber and Information Security. Her motivation stemmed from the desire to secure the information technology infrastructure of the Ghana National Lottery Authority through the principles of Confidentiality, Integrity, and Availability (CIA) Triad. “ “ Advancing Technological Innovations Recognizing the significance of technological advancements, Olayinka is committed to harnessing the power in the cybersecurity domain. She embraces AI and ML to improve threat detection and response capabilities, automating routine security processes to enhance efficiency. With the rapid adoption of cloud computing, Olayinka focuses on developing and implementing robust privacy measures to ensure the safety of cloud-based infrastructure, applications and data. Future Goals Olayinka envisions herself as the future CEO of an information security consulting firm that specializes in ISO 27001 and ISO 22301 implementation and management, security awareness training, policy development and cybersecurity strategy formulation. She aims to provide organizations with comprehensive security solutions tailored to their unique needs. Advice to Budding Entrepreneurs Olayinka offers valuable advice to aspiring entrepreneurs entering the dynamic industry of cybersecurity. She emphasizes the importance of gaining a strong foundation in cybersecurity, identifying a niche within the industry, building a strong network, maintaining ethical conduct, and emphasizing trust and confidentiality. Olayinka encourages continuous learning and collaboration with others to tackle complex cybersecurity challenges and stresses the importance of staying updated on emerging threats and security technologies. She highlights it in a few pointers, which include: Ÿ Gain a Strong Foundation in Cybersecurity: Start by acquiring a solid foundation in cybersecurity. Understand the various domains of cybersecurity, including network security, application security, incident response and risk management. Pursue relevant education and professional certifications to develop your knowledge and expertise. Ÿ Identify a Niche and understand the Business Landscape: Consider specializing in a specific area within cybersecurity. By focusing on a niche, you can develop thorough expertise and differentiate yourself from competitors. Gain an understanding of the business landscape in which you will want to operate. Ÿ Build a Strong Network: Networking is crucial in the cybersecurity industry. Connect with professionals, industry experts and potential clients through conferences, meetups and online communities such as LinkedIn. Engage in knowledge sharing, seek mentorship and build relationships that can provide guidance and opportunities. Ÿ Stay Ethical and Compliant: Maintain a strong ethical foundation in your cybersecurity ventures. Emphasize the importance of ethical hacking and responsible disclosure practices. Adhere to legal and regulatory requirements and promote a culture of compliance within your organization. Ÿ Emphasize Trust and Confidentiality: Cybersecurity is built on trust. Ensure that your client’s data and privacy are safeguarded with the utmost care. Develop strong security measures to protect sensitive information and communicate your commitment to confidentiality and trust to your clients. Ÿ Collaborate with Others: Cybersecurity challenges are often complex and multifaceted. Collaborate with other experts, organizations and researchers to tackle common problems. Share threat intelligence, contribute to open-source projects and participate in coordinated vulnerability disclosure programs. Ÿ Continuously Learn and Evolve: Cybersecurity is an ever-evolving field, so commit to continuous learning. Invest in ongoing training and professional development to ensure you stay at the forefront of the industry. www.ciolook.com | November 2023 | 35
- 39. Security in every byte: Women shaping the cybersecurity landscape Security in every byte: Women shaping the cybersecurity landscape
- 40. www.ciolook.com