What are the Top Five Cyber Security Certifications?
•
0 likes•19 views
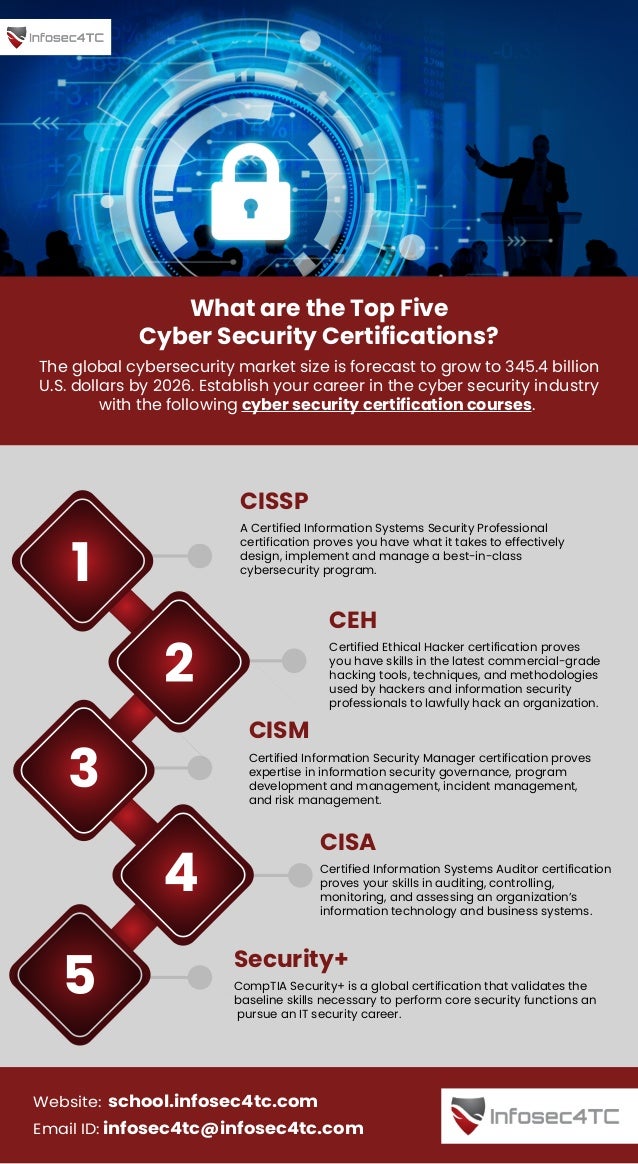
The global cybersecurity market size is forecast to grow to 345.4 billion U.S. dollars by 2026. Establish your career in the cyber security industry with the following cyber security certification courses.
Report
Share
Report
Share
Download to read offline
Recommended
Selecting the ideal cybersecurity certification for newcomers involves considering your individual career aspirations and preferences. Investigating the current job market needs and emerging trends aids in identifying sought-after certifications. Additionally, picking the appropriate cybersecurity course is crucial for certification success. Lastly, assessing the legitimacy and pertinence of certifications guarantees that you dedicate your resources to credentials esteemed within the industry. For top-notch cybersecurity training certificates, ACS Networks and Technologies Pvt. Ltd. stands out as a reliable choice.
For more information click on the given link : https://medium.com/@acs.shivanimishra/cyber-security-training-certification-for-beginners-45bfa5338ba0Best Cyber Security Training Certification | ACS Networks and Technologies Pv...

Best Cyber Security Training Certification | ACS Networks and Technologies Pv...ACS Networks and Technologies Pvt. Ltd.
Recommended
Selecting the ideal cybersecurity certification for newcomers involves considering your individual career aspirations and preferences. Investigating the current job market needs and emerging trends aids in identifying sought-after certifications. Additionally, picking the appropriate cybersecurity course is crucial for certification success. Lastly, assessing the legitimacy and pertinence of certifications guarantees that you dedicate your resources to credentials esteemed within the industry. For top-notch cybersecurity training certificates, ACS Networks and Technologies Pvt. Ltd. stands out as a reliable choice.
For more information click on the given link : https://medium.com/@acs.shivanimishra/cyber-security-training-certification-for-beginners-45bfa5338ba0Best Cyber Security Training Certification | ACS Networks and Technologies Pv...

Best Cyber Security Training Certification | ACS Networks and Technologies Pv...ACS Networks and Technologies Pvt. Ltd.
Here are the Top 12 Certifications to Boost Your Career in 2023: 1. Google Certified Professional 2. AWS Certified Solutions Architect 3. Certified Information Security Manager 4. Project Management ProfessionalBoost Your Career in 2023: 12 Best Certifications For It | Future Education M...

Boost Your Career in 2023: 12 Best Certifications For It | Future Education M...Future Education Magazine
More Related Content
Similar to What are the Top Five Cyber Security Certifications?
Here are the Top 12 Certifications to Boost Your Career in 2023: 1. Google Certified Professional 2. AWS Certified Solutions Architect 3. Certified Information Security Manager 4. Project Management ProfessionalBoost Your Career in 2023: 12 Best Certifications For It | Future Education M...

Boost Your Career in 2023: 12 Best Certifications For It | Future Education M...Future Education Magazine
Similar to What are the Top Five Cyber Security Certifications? (20)
7 Ultimate Benefits Of Ethical Hacking Course To Boost Your IT Career.pptx

7 Ultimate Benefits Of Ethical Hacking Course To Boost Your IT Career.pptx
The Ultimate Guide To Cyber Security Certifications

The Ultimate Guide To Cyber Security Certifications
Cyber Security Course in Hyderabad February 2024.pptx

Cyber Security Course in Hyderabad February 2024.pptx
Boost Your Career in 2023: 12 Best Certifications For It | Future Education M...

Boost Your Career in 2023: 12 Best Certifications For It | Future Education M...
Recently uploaded
Recently uploaded (20)
Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood

Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood
Navigating Identity and Access Management in the Modern Enterprise

Navigating Identity and Access Management in the Modern Enterprise
"I see eyes in my soup": How Delivery Hero implemented the safety system for ...

"I see eyes in my soup": How Delivery Hero implemented the safety system for ...
AI+A11Y 11MAY2024 HYDERBAD GAAD 2024 - HelloA11Y (11 May 2024)

AI+A11Y 11MAY2024 HYDERBAD GAAD 2024 - HelloA11Y (11 May 2024)
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
Vector Search -An Introduction in Oracle Database 23ai.pptx

Vector Search -An Introduction in Oracle Database 23ai.pptx
TrustArc Webinar - Unified Trust Center for Privacy, Security, Compliance, an...

TrustArc Webinar - Unified Trust Center for Privacy, Security, Compliance, an...
Decarbonising Commercial Real Estate: The Role of Operational Performance

Decarbonising Commercial Real Estate: The Role of Operational Performance
Six Myths about Ontologies: The Basics of Formal Ontology

Six Myths about Ontologies: The Basics of Formal Ontology
Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024

Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024
JavaScript Usage Statistics 2024 - The Ultimate Guide

JavaScript Usage Statistics 2024 - The Ultimate Guide
Design and Development of a Provenance Capture Platform for Data Science

Design and Development of a Provenance Capture Platform for Data Science
What are the Top Five Cyber Security Certifications?
- 1. What are the Top Five Cyber Security Certifications? https://school.infosec4tc.com The global cybersecurity market size is forecast to grow to 345.4 billion U.S. dollars by 2026. Establish your career in the cyber security industry with the following cyber security certification courses. 1 2 3 4 5 CISSP A Certified Information Systems Security Professional certification proves you have what it takes to effectively design, implement and manage a best-in-class cybersecurity program. CEH Certified Ethical Hacker certification proves you have skills in the latest commercial-grade hacking tools, techniques, and methodologies used by hackers and information security professionals to lawfully hack an organization. CISM Certified Information Security Manager certification proves expertise in information security governance, program development and management, incident management, and risk management. CISA Certified Information Systems Auditor certification proves your skills in auditing, controlling, monitoring, and assessing an organization’s information technology and business systems. Security+ CompTIA Security+ is a global certification that validates the baseline skills necessary to perform core security functions an pursue an IT security career. https://school.infosec4tc.com Email ID: infosec4tc@infosec4tc.com Website: school.infosec4tc.com
