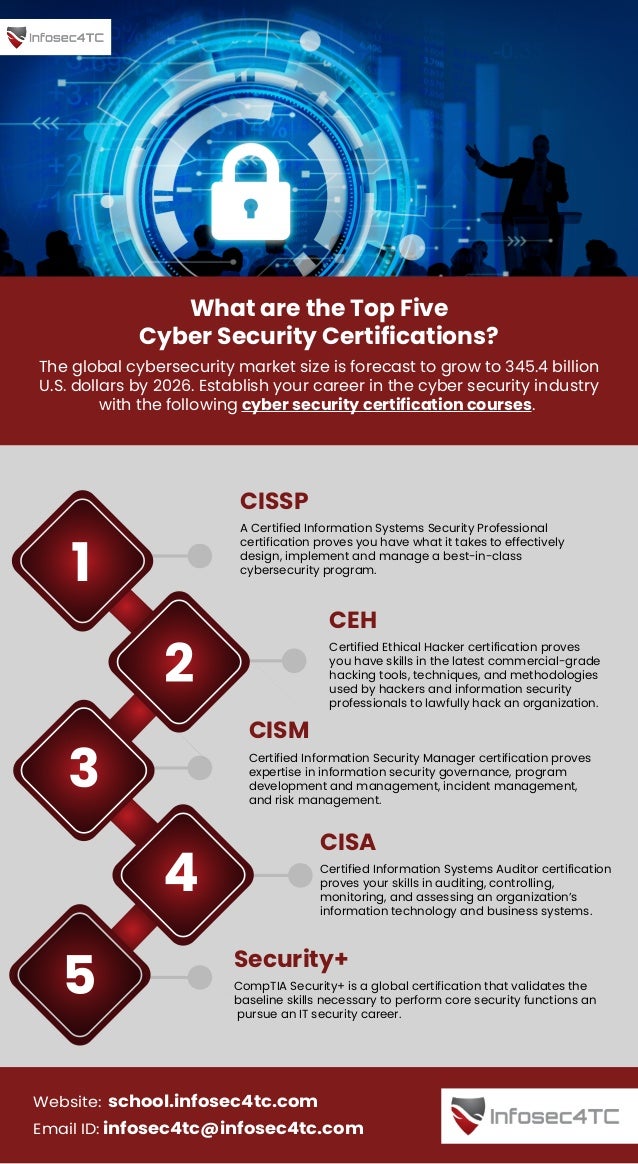
The document outlines the top five cybersecurity certifications that can enhance career opportunities in the growing cybersecurity market, projected to reach $345.4 billion by 2026. The certifications listed are CISSP, CEH, CISM, CISA, and CompTIA Security+, each validating different expert skills in cybersecurity management, ethical hacking, information governance, auditing, and security functions. For more information, visit the provided link or contact via email.