Blockchain Workshop
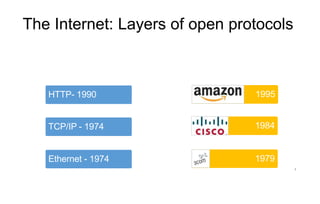
- 1. The Internet: Layers of open protocols Ethernet - 1974 TCP/IP - 1974 HTTP- 1990 1979 1984 1995 1
- 2. ‘The Net’ opening scene 1995 5 © Columbia Pictures. All rights reserved. This content is excluded from our Creative Commons license. For more information, see https://ocw.mit.edu/help/faq-fair-use/ Sandra Bullo 5 ck
- 3. First online sale: Pizza Hut in 1994 But money changed hands with delivery © Pizza Hut. All rights reserved. This content is excluded from our Creative Commons license. For more information, see https://ocw.mit.edu/help/faq-fair-use/ 6
- 4. Cryptography: Communications in the presence of adversaries Scytale Cipher Enigma Machine Asymmetric Cryptography Ancient Times 1920s - WWII 1976 to today Image is in the public domain via Wikipedia. © Luringen on Wikimedia Commons. License CC BY-SA. All Image by CIA and in the public domain via Wikimedia Commons. rights reserved. This content is excluded from our Creative Commons license. For more information, see https://ocw.mit.edu/help/faq-fair-use/ 7
- 5. 5 Early Cryptographic Digital Currencies Failed • DigiCash (David Chaum) – 1989 • Mondex (National Westminster Bank) - 1993 • CyberCash (Lynch, Melton, Crocker & Wilson) – 1994
- 6. The Internet: Cryptographic protocols Ethernet - 1974 TCP/IP - 1974 HTTP- 1990 SSL / TLS – 1996 1979 1984 1994 1998 6
- 7. 7 Further Cryptographic Digital Currencies Failed • DigiCash (David Chaum) – 1989 • Mondex (National Westminster Bank) - 1993 • CyberCash (Lynch, Melton, Crocker & Wilson) – 1994 • E-gold (Gold & Silver Reserve) – 1996 • Hashcash (Adam Back) – 1997 • Bit Gold (Nick Szabo) – 1998 • B-Money (Wei Dai) - 1998 • Lucre (Ben Laurie) – 1999
- 8. Digital Payments Innovation, though, Continued 2003 8 2007
- 9. Role of Money © Source Unknown. All rights reserved. This content is excluded from our Creative Commons license. For more information, see https://ocw.mit.edu/help/faq-fair-use/ Medium of Exchange Image by Rob Pongsajapan on flickr. CC BY. Store of Value Image by ajalfaro on flickr. CC BY-NC-SA Unit of Account 25
- 10. Non Metal Money Image in the public domain by Gary Todd. Image by Bertramz on Wikimedia. Licesne: CC BY Salt Bars - Ethiopia Cowrie Shells - Nigeria Image by Sandsteinon Wikimedia.License CC-BY Image by Yusuke Kawasaki on Wikimedia. License: CC BY Tally Sticks - England Rai Stones - Yap 8
- 11. Metal Money Bronze Aes Rude - Rome © Chuy1530on Wikipedia. All rights reserved. This content is excluded from our Creative Commons license. For more information, see https://ocw.mit.edu/help/faq-fair-use/. Bronze Spade - China Image by Mary Harrsch on flickr. License CC BY-NC-SA Cooper Plate - Sweden © StAnselm on Wikipedia. All rights reserved. This content is excluded from our Creative Commons license. For more information, see https://ocw.mit.edu/help/faq-fair-use/ 9
- 12. Minted Money Image by Daderot on Wikimedia. License: CC0. Image is in the public domain. Image by Scott Semans World Coins. License: CC BY. Bronze Yuan - China Silver Dekadrachm - Greece Gold Aureus - Rome 10
- 13. Paper Money Jiaozi Promissory Note - China I 5 Pound Note - England Continental Note – U.S. Images are in the public domain. 11
- 14. Private Bank Notes United States Australia Canada England Images are in the public domain. 12
- 15. Ledgers Principal Recordings of Accounts Proto Cuneiform Uruk, ca 3000 B.C Personal Ledger George Washington 1747 Images are in the public domain. 13
- 16. Ledgers Principal Recordings of Accounts: Economic Activity Financial Relationships Types of Ledgers: Transaction vs. Balance General vs. Supporting or Sub Single Entry vs. Double Entry 14
- 17. Characteristics of Good Ledgers • Immutable, Consistency • Timestamped • Ownership • Accuracy • Description of Transaction • Comprehensive 15
- 18. Deposits & Negotiable Orders 17 Images are in the public domain.
- 19. Fiat Currency • Social & Economic Consensus Image by epSos.de on Wikimedia. License CC BY. • Represented by Central Bank Liabilities & Commercial Bank Deposits • Relies upon System of Ledgers Integrated into Fractional Banking System • Accepted for Taxes • Notes & Coins are Legal Tender for All Debts Public & Private • Unique Tax Treatment 19
- 20. Credit Cards First General Merchant Card American Express Bank of America Diners’ Club First Plastic Card First General Purpose 1949 1959 Credit Card 1966 © Diner's Club, American Express, Bank of America. All rights reserved. This content is excluded from our Creative Commons license. For more information, see https://ocw.mit.edu/help/faq-fair-use/ 23
- 21. Central Banking, Money & Ledgers Image by Richard Gendal Brown from "Thoughts on the Future of Finance." Used with permission. 20
- 22. 26 Characteristics of Money • Durable • Portable • Divisible • Uniform/Fungible (Crawfurd v. Royal Bank 1749) • Acceptable • Stable - Limited supply - Hard to Counterfeit
- 23. 27 Design of Money • Token vs. Account Based • Physical vs. Digital • Private Sector vs. Central Bank • Widely Accessible vs. Wholesale
- 24. 29 Early Cryptographic Digital Currencies … All Failed • DigiCash (David Chaum) – 1989 • Mondex (National Westminster Bank) - 1993 • CyberCash (Lynch, Melton, Crocker & Wilson) – 1994 • E-gold (Gold & Silver Reserve) – 1996 • Hashcash (Adam Back) – 1997 • Bit Gold (Nick Szabo) – 1998 • B-Money (Wei Dai) - 1998 • Lucre (Ben Laurie) – 1999
- 25. 30 Why did Early Digital Currencies Fail? • Merchant adoption • Centralization • Double spending • Consensus
- 26. 32 The Riddle Remained How to move value peer-to-peer without any trusted central intermediary
- 27. 33 Bitcoin: A Peer-to-Peer Electronic Cash System •From: Satoshi Nakamoto <satoshi <at> vistomail.com> Subject: Bitcoin P2P e-cash paper Newsgroups: gmane.comp.encryption.general Date: Friday 31st October 2008 18:10:00 UTC •“I've been working on a new electronic cash system that's fully peer-to-peer, with no trusted third party.”
- 28. A new layer?: Programmable transactions - 2009 ??? Ethernet - 1974 TCP/IP - 1974 HTTP- 1990 SSL / TLS - 1996 1979 1984 1995 1998 34
- 29. Blockchain Technology timestamped append-only log auditable database network consensus protocol Secured via cryptography • Hash functions for tamper resistance and integrity • Digital signatures for consent Consensus for agreement Addresses ‘cost of trust’ (Byzantine Generals problem) • Permissioned • Permissionless 7
- 30. 30 Blockchain Technology • Verifiably moves ‘data’ on a decentralized network • The ‘data’ can represent value or computer code • Thus it goes directly to the plumbing of the financial sector and money • Broad adoption rests on addressing technical, commercial and public policy hurdles • It can be a catalyst for change in the world of finance and money
- 31. Purpose of Blockchain The purpose of a blockchain is to have a network of computers agree upon a common state of data. Plain and simple. Any person or organization should be able to participate in this process. No person or organization should be able to control this process. With a blockchain we can decentralize where code runs and agree on the output. There is no single owner of the code's execution The code always runs as programmed. The code is transparently verifiable
- 32. Pizza for bitcoins? May 18, 2010, 12:35:20 AM • “I'll pay 10,000 bitcoins for a couple of pizzas.. like maybe 2 large ones so I have some left over for the next day. I like having left over pizza to nibble on later. You can make the pizza yourself and bring it to my house or order it for me from a delivery place, but what I'm aiming for is getting food delivered in exchange for bitcoins where I don't have to order or prepare it myself, kind of like ordering a 'breakfast platter' at a hotel or something, they just bring you something to eat and you're happy! • I like things like onions, peppers, sausage, mushrooms, tomatoes, pepperoni, etc.. just standard stuff no weird fish topping or anything like that. I also like regular cheese pizzas which may be cheaper to prepare or otherwise acquire. • If you're interested please let me know and we can work out a deal. • Thanks, Laszlo” 16
- 33. 33 Re: Pizza for bitcoins? May 21, 2010, 07:06:58 PM • “So nobody wants to buy me pizza? Is the bitcoin amount I'm offering too low?”
- 34. 34 Re: Pizza for bitcoins? May 22, 2010, 07:17:26 PM • “I just want to report that I successfully traded 10,000 bitcoins for pizza. Pictures: http://heliacal.net/~solar/bitcoin/pizza/ Thanks jercos!”
- 35. 35 Medium of Exchange: 10,000 Bitcoins for 2 Pizzas • Value: • May 22, 2010 - $41 • $20.50 per pizza • September 23, 2023 – Rs. 22,09,75,36,390 (220 crores) • Rs.110 crores per pizza
- 36. 8 Bitcoin – Technical Features • Cryptographic Hash Functions • Timestamped Append-only Logs (Blocks) • Block Headers & Merkle Trees • Asymmetric Cryptography & Digital Signatures • Addresses • Consensus through Proof of Work • Network of Nodes • Native Currency • Transaction Inputs & Outputs • Unspent Transaction Output (UTXO) • Scripting language
- 37. NODES IN BLOCKCHAIN “On the most basic level, a node is simply a device running the software of a specific blockchain.” “Nodes are the source of source of truth for a a blockchain.”
- 39. Timestamped Append-only Log - Blockchain Image is in the public domain by National Institute of Standards and Technology. 13
- 40. Merkle Tree – Binary Data Tree with Hashes 15 Image is in the public domain by National Institute Standards and Technology.
- 41. We will Explore a Range of Perspectives Bitcoin Minimalist Smart Contract Minimalist Blockchain Minimalist Bitcoin Maximalist Smart Contract Maximalist Blockchain Maximalist But Anchor our Discussion in the Middle 41
- 42. Blockchain – Proof of Work Innovation – Chained Proof of Work for Distributed Network Consensus & Timestamping © Cryptographics.info. All rights reserved. This content is excluded from our Creative Commons license. For more information, see https://ocw.mit.edu/help/faq-fair-use/ 16
- 43. Blockchain – Proof of Work Image by Anders Brownworth. Used with permission. 17
- 44. Blockchain – Proof of Work Image by Anders Brownworth. Used with permission. 18
- 45. Cryptography Cryptography is the science and practice of securing communication and data by converting information into an unreadable format, which can only be deciphered by authorized individuals . The primary goal of cryptography is to ensure the confidentiality, integrity, and authenticity of information.
- 47. Types of Cryptography 1) Symmetric Key Encryption (Eg-AES 256)
- 48. 2) Asymmetric Key Encryption
- 49. A cryptographic hash function is a mathematical algorithm that takes an input (or message) and produces a fixed-size string of characters, which is typically a hexadecimal number. The key properties of a cryptographic hash function are: SHA-256 (Secure Hash Algorithm 256-bit) is a cryptographic hash function that is commonly used in blockchain technology, including in popular cryptocurrencies like Bitcoin. It plays a critical role in ensuring the security and integrity of blockchain data. Here's an explanation of how SHA-256 works and its role in blockchain: 3) Cryptographic Hash Functions • Deterministic: The same input will always produce the same hash value. • Fast to Compute: It's computationally efficient to calculate the hash value for any given input. • Irreversible: It should be nearly impossible to reverse the process and derive the original input from the hash value. • Avalanche Effect: A small change in the input should result in a significantly different hash value.
- 50. Cryptography in Blockchain Cryptography plays a fundamental role in blockchain technology: • Securing Transactions: In blockchain, cryptography is used to secure transactions. Each transaction is encrypted to ensure that only the intended parties can access the details, making it highly secure and tamper-resistant. • Digital Signatures: Blockchain users have public and private keys. Public keys are like usernames, and private keys are secret passwords. When someone wants to make a transaction, they use their private key to create a digital signature. Others can use their public key to verify that the transaction is valid and came from the right person. • Mining and Consensus: Cryptography is used in the mining process, where miners solve complex cryptographic puzzles to validate and add new blocks to the blockchain. This process ensures the integrity and security of the blockchain's transaction history.
- 51. How Cryptography makes Cryptocurrency Secure ?
- 52. Types of Blockchain 1) Public 2) Private 3) Hybrid 4) Consortium
- 55. BenefitsofBlockchain Security Transparency Immutability Faster Transactions
- 56. SECURITY In the digital age, security is paramount. Our personal information, financial assets, and even the integrity of our systems are constantly under threat from malicious actors. This is where blockchain comes in as a game-changer. When a transaction is added to the blockchain, it is stored in a block that is linked to the previous one using complex mathematical algorithms. Traditional centralized systems have single points of failure. In contrast, blockchain is decentralized, meaning data is distributed across a network of computers. There is no single vulnerable point for attackers to exploit. Even if one node is compromised, the rest of the network remains secure. Once data is recorded on the blockchain, it cannot be altered or deleted.
- 57. Transparency
- 58. Immutability immutability refers to the quality of being unchangeable or unalterable. In the context of technology and data, it means that once information is recorded or stored, it cannot be modified or deleted.
- 59. Blockchain – Consensus supports Longest Chain 19 Image by Meek Mark on Wikipedia . CC BY.
- 60. 20 Bitcoin Proof of Work Difficulty • Targets 10 minute average block generation time • Defined by the # of leading zeros Hash output requires to solve proof of work • Adjusts every 2016 blocks - about every two weeks • Currently, > 18 leading zeros (out of 64 hexadecimal characters) • Block 541974 (9/18/18)- 18 leading zeros 0000000000000000001104a863046dfbad1a2941128815669623ff93c2a3945f • Genesis Block (1/3/09) – 10 leading zeros, though only required 8 000000000019d6689c085ae165831e934ff763ae46a2a6c172b3f1b60a8ce26f
- 61. Bitcoin Mining Difficulty 21 Courtesy of Blockchain Luxembourg S.A. Used with permission. Source: Blockchain.com
- 62. Bitcoin Mining Evolution Application Specific Integrated Circuit (ASICs) 2013 – 2018 4 – 16 TH/S Image by InstagramFOTOGRAFIN on Pixabay. Graphics Processing Units (GPUs) 2010 – 2013 20 - 300 MH/S Image is in the public domain. Central Processing Units (CPUs) 2009 – 2010 2 - 20 MH/S Image by MiNE on flickr. CC BY Modern Mining Factory Image by Axel Castillo. CC0 Public Domain. 23
- 64. Native Currency Economic Incentive System ‘Monetary Policies’ vary widely • Bitcoin - BTC • Created through Coinbase Transaction in each block • ‘Monetary Policy’ preset in Bitcoin Core • Creation originally 50 Bitcoin per block • Reward halves (1/2s) every 210,000 blocks • Currently 12.5 BTCs created per block – thus ‘inflation’ 4.1% • Currently 17.3 million BTC; capping at 21 million BTC in 2040 • Market based transaction fee mechanism also provided for in Bitcoin Core • Ethereum • Currently 3 ETH per block – thus ‘inflation’ 7.4% • Recent proposal to decline to 2 ETH per block in 11/18 • Fees paid in Gas (109 Gas per ETH) fo 25r computation are credited to miners
- 65. Bitcoin vs Ethereum Design • Founder: Satoshi Nakamoto • Genesis: January 2009 • Code: Non Turing (Script) • Ledger: UTXO – Transaction • Merkle Trees: Transactions • Block Time: 10 minutes • Consensus: Proof of Work • Hash Function: SHA 256 Vatalik Buterin July 2015 Turing Complete (Solidity, Serpent, LLL or Mutan) State - Account Based Transactions, State, Storage, Receipts (w/nonces) 14 seconds Proof of Work Ethash
- 66. Bitcoin – Technical Features • Cryptography & Timestamped Logs • Cryptographic Hash Functions • Timestamped Append-only Logs (Blocks) • Block Headers & Merkle Trees • Asymmetric Cryptography & Digital Signatures • Addresses • Decentralized Network Consensus • Proof of Work • Native Currency • Network • Transaction Script & UTXO • Transaction Inputs & Outputs • Unspent Transaction Output (UTXO) set Ethereum? Yes ✔ ✔ ✔ ✔ ✔ ✔ Yes ✔ ✔ ✔ No State Transitions Account Based 7 languages • Script language 7
- 67. Smart Contracts • “A set of promises, • specified in digital form, • including protocols • within which the parties perform on these promises.” Nick Szabo, 1996 However …. • Smart Contracts may not be ‘Smart’ • Smart Contracts may not be ‘Con 6 tracts’
- 68. Bitcoin vs Ethereum Design • Currency: Bitcoin • Mining: ASIC • Hashrate: 54 Exahash/S • Pre-sale: None • Rewards: 12.5 BTC/block • Monetary Policy: 1/2s every 210,000 blocks (4 yrs) • Fees: Voluntary ETH GPU 260 Terahash/S ICO & prerelease of 72 m ETH 3 ETH/block Fixed, but changes by updates (was 5/block; proposal to 2) Needed & market based 9
- 69. 11 Smart Contract Potential Use Cases • Digital Identity • Securities • Derivatives • Mortgages • Supply Chain • Clinical Trials Records Trade Finance Financial Data Land Title Auto Insurance Cancer Research
- 70. 10 Smart Contract Platforms • Ethereum (2015) - $22 b current market value • EOS (2018) - $5 b – completed $4.2 b year long ICO in July • NEO (2016) – $1.1 b - China; delegated BFT; supports wider range of code • Ethereum Classic (2016) – $1.1 b - Created from the ‘DAO’ hard fork • LISK (2016) – $360 m - code in Java; uses side chains • Stratis (2017) - $150 m
- 73. What is the Role of Finance? Moving, Allocating & Pricing: Money Image by thomasjphotos on flickr. CC BY-NC-SA Throughout the Economy Image by Jamie on flickr. CC BY. Risk Image by Marco Verch. License CC BY 73
- 74. Financial Sector Challenges => Blockchain Potential Opportunities • Repeated crises and instability • Fiat currency instabilities associated with unsound policies • Centralized intermediaries’ concentrate risks & economic rents • Central Bank legacy payment systems • Clearing & settlement costs & counterparty risks • Financial inclusion • Payment system costs: ½ - 1 % of Global GDP • Financial sector costs: 7 ½ % of U.S. GDP 23
- 75. Challenges with Blockchain Technology • Performance, Scalability, & Efficiency • Privacy & Security • Interoperability • Governance & Collective Action • Commercial Use Cases • Public Policy & Legal Frameworks 9 9
- 76. Privacy & Security • Contradictory Tensions of Pseudonymous Addresses • Law Enforcement & Regulators want more Transparency • Financial Institutions, Regulators & Some Users want less Public Transparency • Concerns about Privacy Coins & Mechanisms Fostering Illicit Activities • Coins: Dash, Monero, Zcash • Mechanisms: Mixers or Tumblers • Cybersecurity Challenges of Private Key Custody, Generation & Storage • Significant Losses due to Hacks, Mismanagement and Thefts • Possible Solutions involve a) Zero Knowledge Proofs & b) Pedersen Commitments • Cryptographic Primitives that: a) lets Someone Prove a Statement is True without Revealing the Details of Exactly why that Statement is True & b) commit to data (like hash) but can 1 a 5 lso combine commitments