How to protect yourself and company from social engineering and phishing emails
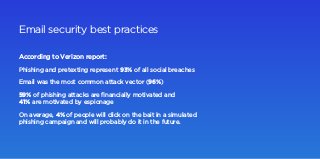
- 1. According to Verizon report: Email security best practices Phishing and pretexting represent 93% of all social breaches Email was the most common attack vector (96%) 59% of phishing attacks are financially motivated and 41% are motivated by espionage On average, 4% of people will click on the bait in a simulated phishing campaign and will probably do it in the future.
- 2. Phishing and pretexting explained Phishing is a common email attack that makes the receiver to click on a malicious link or open an attachment. Pretexting is the way of phishing when someone pretends to be another person. It usually contains more personal information like company name, date of birth or coworkers' names to gain your trust.
- 3. Don't trust the sender’s display name and email The sender’s email address is of someone you don’t usually communicate with. This is an unexpected or unusual email with an embedded hyperlink or an attachment from someone you haven’t communicated with recently. An email is from someone outside your organization and is not related to your job duties. An email was sent from someone inside the organization or from a customer, vendor, or partner but is very unusual. The sender’s email address is from a suspicious domain like apple-contact.com How to detect phishing email?
- 4. Keep an eye on the subject Be careful with attachments An email with a subject line that is irrelevant or does not match the message content An email message is a reply to something you never sent or requested The sender included an email attachment that you were not expecting or that makes no sense in relation to the email message. You see an attachment with a possibly dangerous file type. The only file type that is always safe to download and open is a .txt file.
- 5. Don’t believe everything you read The sender is asking you to click on a link or open an attachment to avoid a negative consequence or to gain something of value. The email is out of the ordinary, or it has bad grammar or spelling errors. The sender is asking you to click a link or open up an attachment that seems odd or illogical. You have an uncomfortable gut feeling about the sender’s request to open an attachment or click a link. The message is asking you to look at a compromising or embarrassing picture or info of yourself or someone you know. You are requested to share personal information like passwords and logins.
- 6. Look but don't click You hover your mouse over a hyperlink that’s displayed in the email message, but the link-to address is for a different website. You received an email that only has long hyperlinks with no further information, and the rest of the email is completely blank. You received an email with a hyperlink that is a misspelling of a known web site. For instance, — the “m” is really two characters — “r” and “n.”
- 7. Relevant Software provides cybersecurity services to identify security breaches and vulnerabilities, preventing data leaks through cloud platforms and making sure your product can hold cyberattacks. www.relevant.software Interested in strengthening your cybersecurity posture? Drop us a line to welcome@relevant.software We'll get back in the short run.
