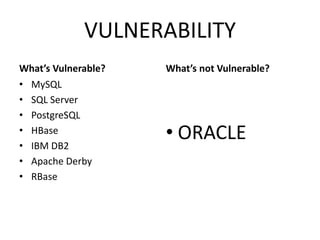
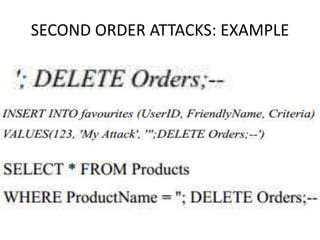
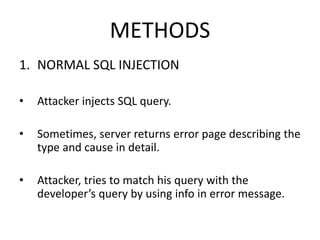
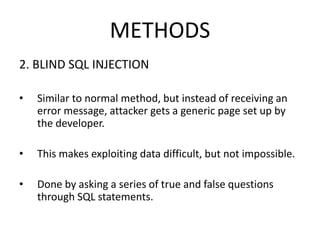
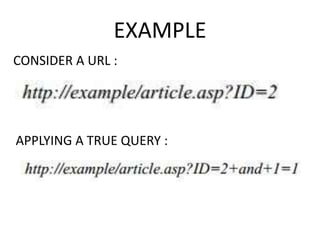
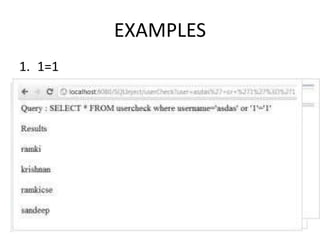
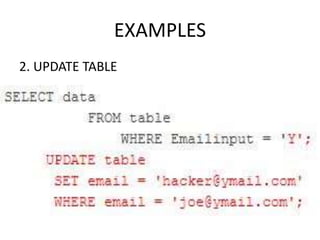
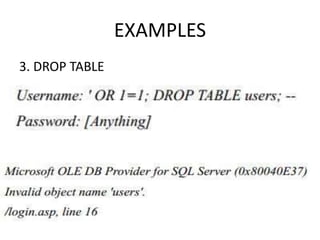
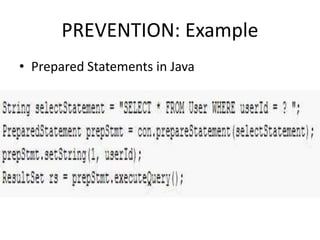
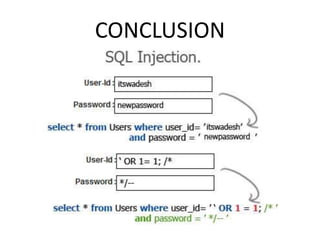
The document discusses SQL injection techniques used to hack databases by injecting malicious commands through applications, specifically highlighting vulnerable systems like MySQL and PostgreSQL. It distinguishes between first order and second order attacks, illustrating different types of SQL injections such as normal and blind methods, along with their respective examples. Prevention strategies such as using bind variables and validating inputs are emphasized to mitigate such attacks.