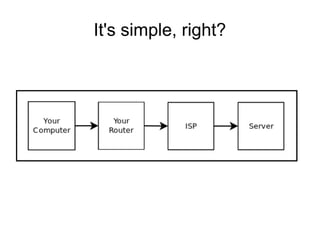
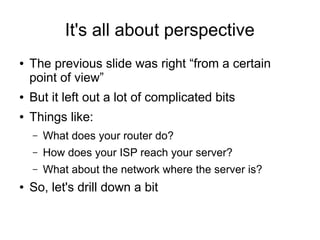
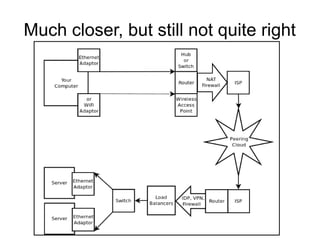
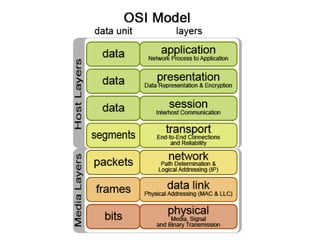
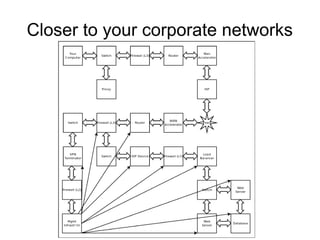
The document provides an overview of how the internet works by discussing various networking concepts and components involved in connecting devices and routing traffic from local networks to external networks and servers. It explains protocols like TCP, UDP, and IP and networking devices like routers, switches, firewalls, proxies, load balancers and VPNs and how they facilitate communication and security. The document is intended to help understand error logs and troubleshoot network issues by providing context on the underlying infrastructure.