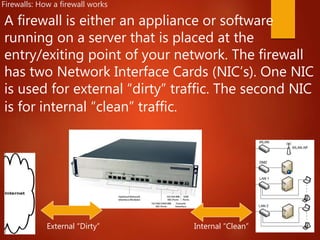
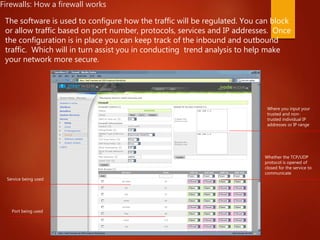
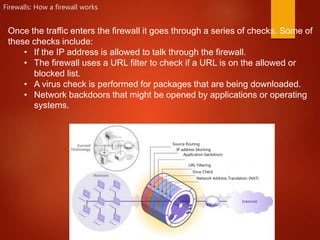
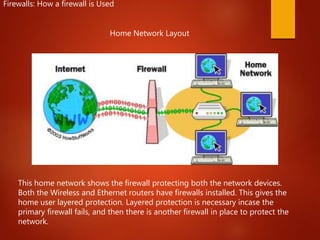
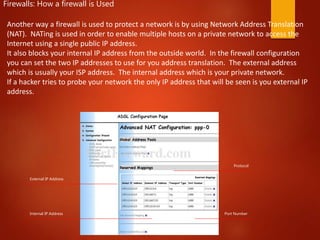
Firewalls are hardware or software solutions that enforce security policies and protect networks. They work by regulating inbound and outbound network traffic through configured rules. A firewall typically has two network interfaces - one for the internal network and one for the external network. Traffic is checked according to port numbers, protocols, IP addresses, and other criteria before being allowed to pass through. Firewalls can protect both home and enterprise networks from threats by blocking unauthorized access and malware while allowing legitimate communications. They perform functions like network address translation, virus scanning, and application controls to secure network integrity.