10_Steps_To_Cyber_Security__1657691326.pdf
•
0 likes•1 view
Cybersecurity
Report
Share
Report
Share
Download to read offline
Recommended
More Related Content
Similar to 10_Steps_To_Cyber_Security__1657691326.pdf
Similar to 10_Steps_To_Cyber_Security__1657691326.pdf (20)
10 Most Important Strategies for Cybersecurity Risk Mitigation.pdf

10 Most Important Strategies for Cybersecurity Risk Mitigation.pdf
Top 10 Measure to Mitigate Insider Security Threats.pptx

Top 10 Measure to Mitigate Insider Security Threats.pptx
Microsoft Security adoptionguide for the enterprise

Microsoft Security adoptionguide for the enterprise
Building and implementing a successful information security policy

Building and implementing a successful information security policy
Protecting the Portals - Strengthening Data Security.pdf

Protecting the Portals - Strengthening Data Security.pdf
Do You Know About Cyber Security? | Secninjaz Technologies LLP 

Do You Know About Cyber Security? | Secninjaz Technologies LLP
Crucial Steps to Cyber Resilience: Understanding the Role of Security Services

Crucial Steps to Cyber Resilience: Understanding the Role of Security Services
The 10 most trusted cyber threat solution providers

The 10 most trusted cyber threat solution providers
Recently uploaded
Organic Name Reactions for the students and aspirants of Chemistry12th.pptx

Organic Name Reactions for the students and aspirants of Chemistry12th.pptxVS Mahajan Coaching Centre
“Oh GOSH! Reflecting on Hackteria's Collaborative Practices in a Global Do-It...

“Oh GOSH! Reflecting on Hackteria's Collaborative Practices in a Global Do-It...Marc Dusseiller Dusjagr
Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"

Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"National Information Standards Organization (NISO)
Recently uploaded (20)
18-04-UA_REPORT_MEDIALITERAСY_INDEX-DM_23-1-final-eng.pdf

18-04-UA_REPORT_MEDIALITERAСY_INDEX-DM_23-1-final-eng.pdf
Organic Name Reactions for the students and aspirants of Chemistry12th.pptx

Organic Name Reactions for the students and aspirants of Chemistry12th.pptx
Hybridoma Technology ( Production , Purification , and Application ) 

Hybridoma Technology ( Production , Purification , and Application )
A Critique of the Proposed National Education Policy Reform

A Critique of the Proposed National Education Policy Reform
Kisan Call Centre - To harness potential of ICT in Agriculture by answer farm...

Kisan Call Centre - To harness potential of ICT in Agriculture by answer farm...
Introduction to ArtificiaI Intelligence in Higher Education

Introduction to ArtificiaI Intelligence in Higher Education
“Oh GOSH! Reflecting on Hackteria's Collaborative Practices in a Global Do-It...

“Oh GOSH! Reflecting on Hackteria's Collaborative Practices in a Global Do-It...
Separation of Lanthanides/ Lanthanides and Actinides

Separation of Lanthanides/ Lanthanides and Actinides
Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"

Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"
Measures of Central Tendency: Mean, Median and Mode

Measures of Central Tendency: Mean, Median and Mode
Web & Social Media Analytics Previous Year Question Paper.pdf

Web & Social Media Analytics Previous Year Question Paper.pdf
10_Steps_To_Cyber_Security__1657691326.pdf
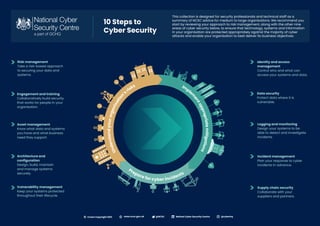
- 1. Identity and access management Control who and what can access your systems and data. Data security Protect data where it is vulnerable. Logging and monitoring Design your systems to be able to detect and investigate incidents. This collection is designed for security professionals and technical staff as a summary of NCSC advice for medium to large organisations. We recommend you start by reviewing your approach to risk management, along with the other nine areas of cyber security below, to ensure that technology, systems and information in your organisation are protected appropriately against the majority of cyber attacks and enable your organisation to best deliver its business objectives. 10 Steps to Cyber Security Risk management Take a risk-based approach to securing your data and systems. Engagement and training Collaboratively build security that works for people in your organisation. Asset management Know what data and systems you have and what business need they support. Architecture and configuration Design, build, maintain and manage systems securely. Vulnerability management Keep your systems protected throughout their lifecycle. Incident management Plan your response to cyber incidents in advance. Supply chain security Collaborate with your suppliers and partners. Produce su p p o r t i n g r i s k m a n a g e m e n t p o l i c i e s U n d e r s t a n d y o u r o r g a n i s a t i o n ’s risks Im ple m e n t a p p r o p r i a t e m i t i g a t i o n s Prepare for cyber incidents @NCSC Natinal Cyber Security Centre @cyberhq www.ncsc.gov.uk Crown Copyright 2021 ©