Report
Share
Download to read offline
Recommended
Recommended
More Related Content
What's hot
What's hot (19)
Vendor Management for PCI DSS; EI3PA; HIPAA and FFIEC

Vendor Management for PCI DSS; EI3PA; HIPAA and FFIEC
Log Monitoring and File Integrity Monitoring for PCI DSS, EI3PA and ISO 27001

Log Monitoring and File Integrity Monitoring for PCI DSS, EI3PA and ISO 27001
Continual Compliance Monitoring– PCI DSS, HIPAA, FERC/NERC, EI3PA, ISO 27001 ...

Continual Compliance Monitoring– PCI DSS, HIPAA, FERC/NERC, EI3PA, ISO 27001 ...
Vendor Management for PCI DSS; EI3PA; HIPAA and FFIEC

Vendor Management for PCI DSS; EI3PA; HIPAA and FFIEC
Similar to Q radar pci-v2-matrix
Similar to Q radar pci-v2-matrix (20)
Information Security Management. Security solutions copy

Information Security Management. Security solutions copy
Towards Secure and Dependable Authentication and Authorization Infrastructures

Towards Secure and Dependable Authentication and Authorization Infrastructures
Pci standards, from participation to implementation and review

Pci standards, from participation to implementation and review
Data protection on premises, and in public and private clouds

Data protection on premises, and in public and private clouds
Get Real-Time Cyber Threat Protection with Risk Management and SIEM

Get Real-Time Cyber Threat Protection with Risk Management and SIEM
Infragard atlanta ulf mattsson - cloud security - regulations and data prot...

Infragard atlanta ulf mattsson - cloud security - regulations and data prot...
Enterprise Data Protection - Understanding Your Options and Strategies

Enterprise Data Protection - Understanding Your Options and Strategies
Private and Secured data Transmission and Analysis for Wireless Ad-hoc Network

Private and Secured data Transmission and Analysis for Wireless Ad-hoc Network
Security Information Event Management Security Information Event Management

Security Information Event Management Security Information Event Management
More from CMR WORLD TECH
More from CMR WORLD TECH (20)
Cyber Security for Everyone Course - Final Project Presentation

Cyber Security for Everyone Course - Final Project Presentation
Delivery readness for pick season and higth volume

Delivery readness for pick season and higth volume
Why digital-will-become-the-primary-channel-for-b2 b-engagement

Why digital-will-become-the-primary-channel-for-b2 b-engagement
Rep consumer experience_in_the_retail_renaissance_en_28_mar18_final_dm_

Rep consumer experience_in_the_retail_renaissance_en_28_mar18_final_dm_
Recently uploaded
Recently uploaded (20)
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
Swan(sea) Song – personal research during my six years at Swansea ... and bey...

Swan(sea) Song – personal research during my six years at Swansea ... and bey...
FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi

FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
The Codex of Business Writing Software for Real-World Solutions 2.pptx

The Codex of Business Writing Software for Real-World Solutions 2.pptx
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
SQL Database Design For Developers at php[tek] 2024![SQL Database Design For Developers at php[tek] 2024](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![SQL Database Design For Developers at php[tek] 2024](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
SQL Database Design For Developers at php[tek] 2024
Breaking the Kubernetes Kill Chain: Host Path Mount

Breaking the Kubernetes Kill Chain: Host Path Mount
Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365

Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Automating Business Process via MuleSoft Composer | Bangalore MuleSoft Meetup...

Automating Business Process via MuleSoft Composer | Bangalore MuleSoft Meetup...
Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...

Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...
Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation

Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
How to Remove Document Management Hurdles with X-Docs?

How to Remove Document Management Hurdles with X-Docs?
Q radar pci-v2-matrix
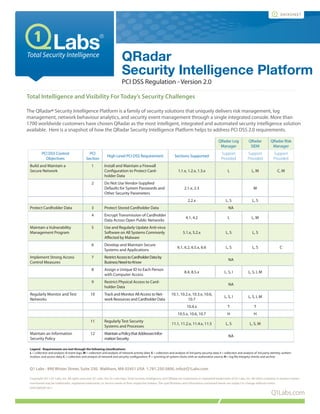
- 1. Total Intelligence and Visibility For Today’s Security Challenges The QRadar® Security Intelligence Platform is a family of security solutions that uniquely delivers risk management, log management, network behaviour analytics, and security event management through a single integrated console. More than 1700 worldwide customers have chosen QRadar as the most intelligent, integrated and automated security intelligence solution available. Here is a snapshot of how the QRadar Security Intelligence Platform helps to address PCI DSS 2.0 requirements. Q1Labs.com datasheet QRadar Security Intelligence Platform PCI DSS Regulation - Version 2.0 QRadar Log Manager QRadar SIEM QRadar Risk Manager PCI DSS Control Objectives PCI Section High Level PCI DSS Requirement Sections Supported Support Provided Support Provided Support Provided Build and Maintain a Secure Network 1 Install and Maintain a Firewall Configuration to Protect Card- holder Data 1.1.x, 1.2.x, 1.3.x L L, M C, M 2 Do Not Use Vendor-Supplied Defaults for System Passwords and Other Security Parameters 2.1.x, 2.3 M 2.2.x L, S L, S Protect Cardholder Data 3 Protect Stored Cardholder Data NA 4 Encrypt Transmission of Cardholder Data Across Open Public Networks 4.1, 4.2 L L, M Maintain a Vulnerability Management Program 5 Use and Regularly Update Anti-virus Software on All Systems Commonly Affected by Malware 5.1.x, 5.2.x L, S L, S 6 Develop and Maintain Secure Systems and Applications 6.1, 6.2, 6.5.x, 6.6 L, S L, S C Implement Strong Access Control Measures 7 RestrictAccesstoCardholderDataby BusinessNeed-to-Know NA 8 Assign a Unique ID to Each Person with Computer Access 8.4, 8.5.x L, S, I L, S, I, M 9 Restrict Physical Access to Card- holder Data NA Regularly Monitor and Test Networks 10 Track and Monitor All Access to Net- work Resources and Cardholder Data 10.1, 10.2.x, 10.3.x, 10.6, 10.7 L, S, I L, S, I, M 10.4.x T T 10.5.x, 10.6, 10.7 H H 11 Regularly Test Security Systems and Processes 11.1, 11.2.x, 11.4.x, 11.5 L, S L, S, M Maintain an Information Security Policy 12 MaintainaPolicythatAddressesInfor- mationSecurity NA Legend - Requirements are met through the following classifications: L = collection and analysis of event logs; M = collection and analysis of network activity data; S = collection and analysis of 3rd party security data; I = collection and analysis of 3rd party identity, authen- tication, and access data; C = collection and analysis of network and security configuration; T = synching of system clocks with an authorative source; H = log file integrity checks and archive Q1 Labs - 890 Winter Street, Suite 230, Waltham, MA 02451 USA 1.781.250.5800, info@Q1Labs.com Copyright 2011 Q1 Labs, Inc. All rights reserved. Q1 Labs, the Q1 Labs logo, Total Security Intelligence, and QRadar are trademarks or registered trademarks of Q1 Labs, Inc. All other company or product names mentioned may be trademarks, registered trademarks, or service marks of their respective holders. The specifications and information contained herein are subject to change without notice. DSPCIMXSIP1011
