SIEM Part II - External Threat Analysis Tool
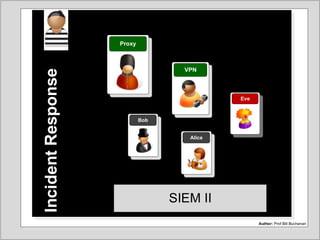
- 1. SIEM II Author: Prof Bill Buchanan IncidentResponse SIEM II Proxy VPN Eve Bob Alice
- 2. Author:BillBuchananAuthor:BillBuchanan StatefulfirewallNetworkSecurity Stateful firewall PIX/ASAConfigNetworkSecurity PIX/ASA Author: Prof Bill BuchananAuthor: Prof Bill Buchanan IncidentResponse Data Sources/Timeline
- 3. Author:BillBuchananAuthor:BillBuchanan StatefulfirewallNetworkSecurity Stateful firewall PIX/ASAConfigNetworkSecurity PIX/ASA Author: Prof Bill Buchanan IncidentsIntroduction Author: Prof Bill Buchanan Incidents During IncidentBefore Incident After Incident Intruder Intrusion Detection
- 4. Author:BillBuchananAuthor:BillBuchanan StatefulfirewallNetworkSecurity Stateful firewall PIX/ASAConfigNetworkSecurity PIX/ASA Author: Prof Bill Buchanan DatastatesInc.Response Data in-motion, data in-use and data at-rest Intrusion Detection System Intrusion Detection System Firewall Internet Switch Router Proxy server Email server Web server DMZ FTP server Firewall Domain name server Database server Bob Alice Eve Data in- motion Data at- rest Data in- use Data at- rest
- 5. Author:BillBuchananAuthor:BillBuchanan StatefulfirewallNetworkSecurity Stateful firewall PIX/ASAConfigNetworkSecurity PIX/ASA Author: Prof Bill Buchanan IncidentsIntroduction Author: Prof Bill Buchanan Incidents During IncidentBefore Incident After Incident Timeline Data At Rest Data In-Motion Data In-Process Files, Directories, File Rights, Domain Rights, etc. File changes, File CRUD (Create, Delete, Update, Delete), Thumbprints Network packet logs, Web logs, Security logs Network scanners, Intrusion Detection Systems, Firewall logs, etc Processes, Threads, Memory, etc. Security Log, Application Log, Registry, Domain Rights. Intruder
- 6. Author:BillBuchananAuthor:BillBuchanan StatefulfirewallNetworkSecurity Stateful firewall PIX/ASAConfigNetworkSecurity PIX/ASA Author: Prof Bill Buchanan IntroductionIncResponse Four Vs of Big Data Intrusion Detection System Firewall Router Proxy server Email server Web server FTP server Switch Alice Management report Sales analysis Targeted marketing Trending/Correlation V- Volume [Scale of data] V- Variety [Different forms of data] V- Velocity [Speed of data generation] V- Veracity [Trustworthiness] Incident Response Eve Bob
- 7. Author:BillBuchananAuthor:BillBuchanan StatefulfirewallNetworkSecurity Stateful firewall PIX/ASAConfigNetworkSecurity PIX/ASA Author: Prof Bill Buchanan IntroductionIncResponse Data Capture Web server IT Ops Nagios. NetApp. Cisco UCS. Apache. IIS. Web Services Firewall Router Proxy server Email server FTP server Switch Eve Bob Microsoft Infrastructure Active Directory. Exchange. SharePoint. Structured Data CSV. JSON. XML. Database Sys Oracle. My SQL. Microsoft SQL. Network/Security Syslog/SNMP. Cisco NetFlow. Snort. Intrusion Detection System Alice Cloud AWS Cloudtrail. Amazon S3. Azure. Application Serv Weblogic. WebSphere. Tomcat
- 8. Author:BillBuchananAuthor:BillBuchanan StatefulfirewallNetworkSecurity Stateful firewall PIX/ASAConfigNetworkSecurity PIX/ASA Author: Prof Bill Buchanan IntroductionIncResponse Investigation sources Web server Firewall Router Proxy server Email server FTP server Bob Eve Internal systems Cloud service providers Communication service providers Trusted partners
- 9. Author:BillBuchananAuthor:BillBuchanan StatefulfirewallNetworkSecurity Stateful firewall PIX/ASAConfigNetworkSecurity PIX/ASA Author: Prof Bill Buchanan IntroductionIncResponse Eve Eve Logs/alerts Bob SIEM Package (Splunk) News feeds Security alerts
- 10. Author:BillBuchananAuthor:BillBuchanan StatefulfirewallNetworkSecurity Stateful firewall PIX/ASAConfigNetworkSecurity PIX/ASA Author: Prof Bill BuchananAuthor: Prof Bill Buchanan IncidentResponse Threat Analysis Proxy VPN Eve Bob Alice
- 11. SIEMNetworkSecurity SIEM Data Fusion Semi-structured >10 million events Select shape and type text. Yellow handle adjusts line spacing. Data storage (2GB/day) Context Parsing/ Normalisation Processing Rule based correlation. Statistical correlation. Event priorization SIEM 10,000 alerts 1 incident Aggregation
- 16. SIEMNetworkSecurity SIEM Trent Micro Threat Analysis
- 18. SIEMNetworkSecurity SIEM State of the Internet
- 23. SIEM II Author: Prof Bill Buchanan IncidentResponse SIEM II Proxy VPN Eve Bob Alice
