Embed presentation
Download as ODP, PPTX

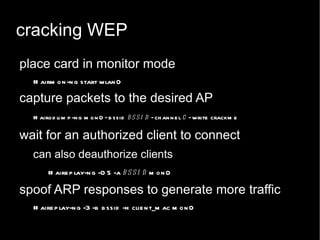
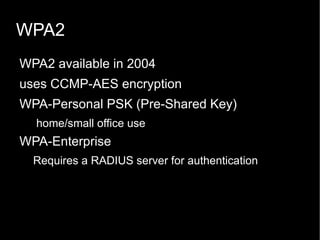
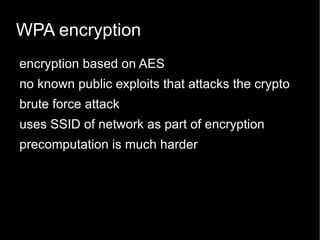

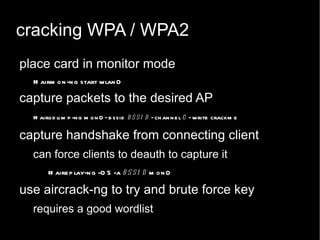
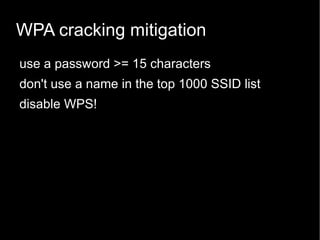
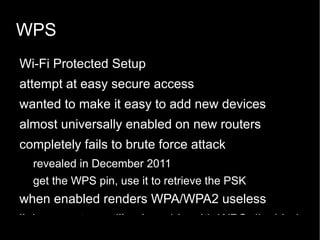
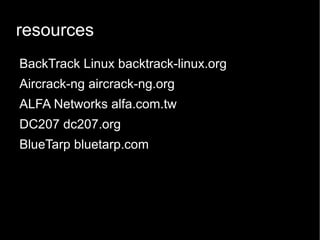

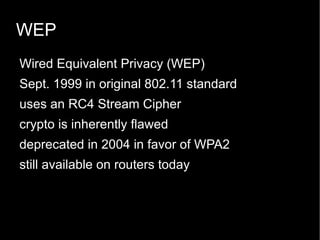
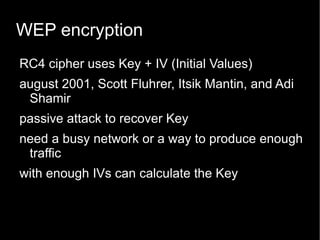
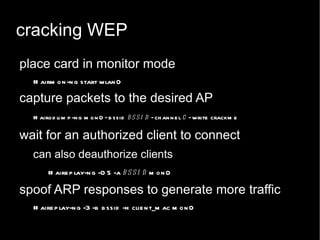
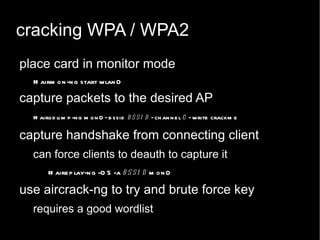
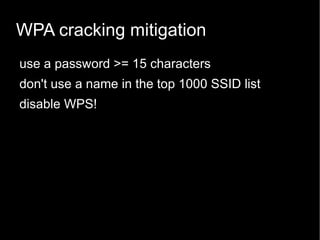
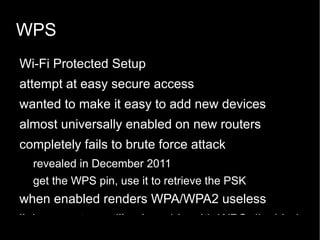
The document presents a tutorial by Casey DC207 on wireless security cracking, covering how to retrieve WEP and WPA/WPA2 passwords using the Aircrack-ng suite. It discusses the vulnerabilities of WEP encryption and the more secure WPA/WPA2 protocols, as well as mitigation strategies to enhance security. The session emphasizes the ease of exploiting WPS vulnerabilities and provides practical commands for cracking these protocols.