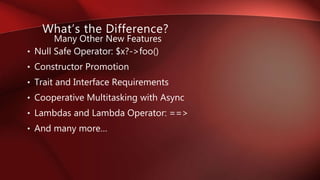
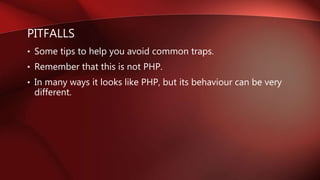
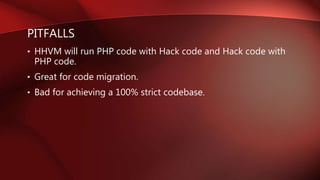
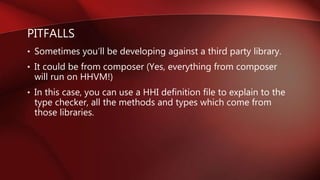
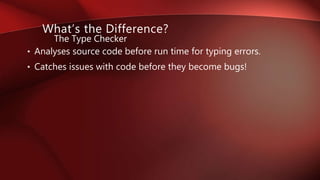
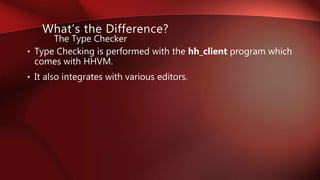
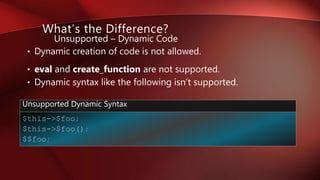
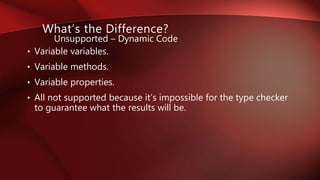
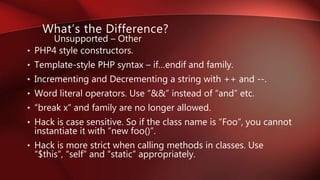
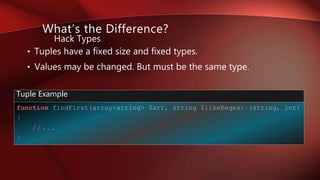
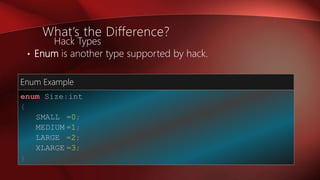
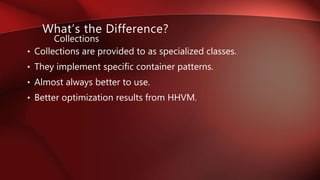
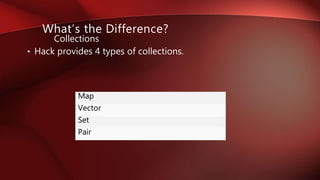
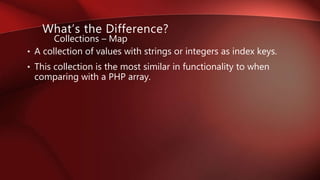
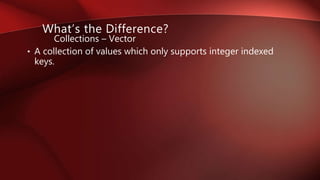
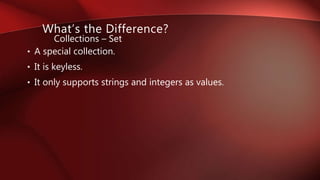
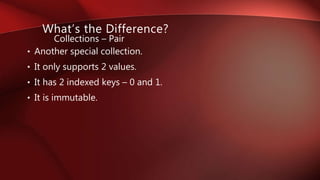
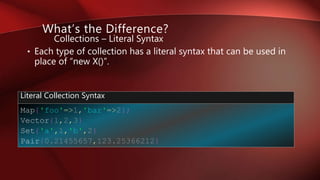
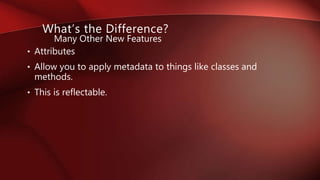
This document provides an introduction to the Hack programming language. It discusses how Hack originated from HHVM and PHP and was open sourced by Facebook in 2015. Key differences between Hack and PHP are described, such as Hack being stricter and type oriented. The document outlines type checking in Hack and various data types supported. It also covers collections, attributes and other new features of Hack. Potential pitfalls of Hack are mentioned along with tips for getting started, installation, learning resources, and frameworks.






![The Type Checker
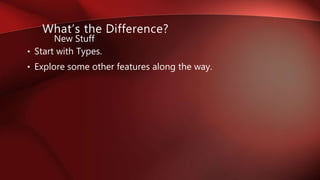
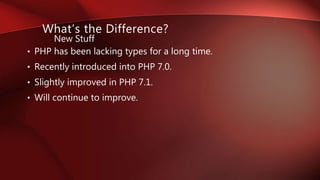
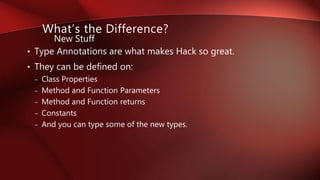
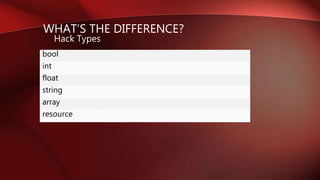
What’s the Difference?
<?hh //strict
class App
{
public function exec():void
{
$this->run(['bar']);
}
public function run(array<string,mixed> $array):void
{
var_dump($array);
}
}
Top Level Code Example](https://image.slidesharecdn.com/welcometohack-161013062537/85/Welcome-to-hack-13-320.jpg)



![WHAT’S THE DIFFERENCE?
<?php
class DB
{
public function upsert($record,$condition=[],$options=[])
{
//...
}
}
Basic PHP Example
• Consider the following example:
• An imaginary method.
• Can insert or update a record in a database.](https://image.slidesharecdn.com/welcometohack-161013062537/85/Welcome-to-hack-32-320.jpg)
![WHAT’S THE DIFFERENCE?
<?php
class DB
{
public function upsert(Array $record, Array $condition=[],$options=[])
{
//...
}
}
PHP 5 Example](https://image.slidesharecdn.com/welcometohack-161013062537/85/Welcome-to-hack-33-320.jpg)
![WHAT’S THE DIFFERENCE?
<?php
declare(strict_types=1);
class DB
{
public function upsert
(
array $record,
array $condition=[],
array $options=[]
):array
{
//...
}
}
PHP 7.0 Example](https://image.slidesharecdn.com/welcometohack-161013062537/85/Welcome-to-hack-34-320.jpg)
![WHAT’S THE DIFFERENCE?
<?php
declare(strict_types=1);
class DB
{
public function upsert
(
array $record,
array $condition=[],
array $options=[]
):?array
{
//...
}
}
PHP 7.1 Example](https://image.slidesharecdn.com/welcometohack-161013062537/85/Welcome-to-hack-35-320.jpg)
![WHAT’S THE DIFFERENCE?
<?hh //strict
class DB
{
public function upsert
(
array<string,mixed> $record,
array<string,mixed> $condition=[],
array<string,mixed> $options=[]
):?array<string,mixed>
{
//...
}
}
Hack Example](https://image.slidesharecdn.com/welcometohack-161013062537/85/Welcome-to-hack-36-320.jpg)
![WHAT’S THE DIFFERENCE?
<?hh //strict
type CommonStringKeyArray=array<string,mixed>;
class DB
{
public function upsert
(
CommonStringKeyArray $record,
CommonStringKeyArray $condition=[],
CommonStringKeyArray $options=[]
):?CommonStringKeyArray
{
//...
}
}
Hack Aliases Example](https://image.slidesharecdn.com/welcometohack-161013062537/85/Welcome-to-hack-37-320.jpg)
![WHAT’S THE DIFFERENCE?
<?hh //strict
type CommonStringKeyArray =array<string,mixed>;
type DBRecord =CommonStringKeyArray;
type DBQuery =CommonStringKeyArray;
type DBQueryOptions =CommonStringKeyArray;
class DB
{
public function upsert
(
DBRecord $record,
DBQuery $condition=[],
DBQueryOptions $options=[]
):?DBRecord
{
//...
}
}
Hack Aliasing Alias Example](https://image.slidesharecdn.com/welcometohack-161013062537/85/Welcome-to-hack-38-320.jpg)
![WHAT’S THE DIFFERENCE?
<?hh //strict
type CommonStringKeyArray =array<string,mixed>;
type DBRecord =CommonStringKeyArray;
type DBQuery =CommonStringKeyArray;
type DBQueryOptions =shape
(
'order' =>int,
'limit' =>int,
'offset‘ =>int
);
class DB
{
public function upsert
(
DBRecord $record,
DBQuery $condition=[],
DBQueryOptions $options=[]
):?DBRecord
{
//...
}
}
Hack Shape Example](https://image.slidesharecdn.com/welcometohack-161013062537/85/Welcome-to-hack-39-320.jpg)
![WHAT’S THE DIFFERENCE?
<?hh //strict
require_once('types.hh');
class DB
{
private ?DBConnection $connection;
private bool $connected=false;
private DBQuery $lastQuery;
public function upsert
(
DBRecord $record,
DBQuery $condition=[],
DBQueryOptions $options=[]
):?DBRecord
{
//...
}
}
Hack Typed Properties Example](https://image.slidesharecdn.com/welcometohack-161013062537/85/Welcome-to-hack-40-320.jpg)

![Many Other New Features
What’s the Difference?
<<
command('encryptString'),
arguments
(
[
['--input','-i'],
'The string to encrypt.'
]
)
>>
public function encryptString(Command $command){}
Attributes](https://image.slidesharecdn.com/welcometohack-161013062537/85/Welcome-to-hack-58-320.jpg)