week6
•
0 likes•121 views
Y
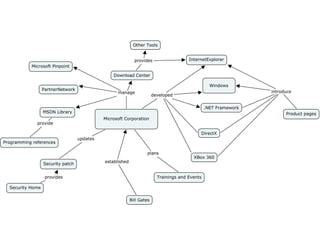
ymWindows 7 was designed to simplify tasks, work the way users want, and enable new capabilities. Microsoft provides many security upgrades for Windows. Technologies are described in detail in the MSDN Library for developers.
Report
Share
Report
Share
Download to read offline
Recommended
Acronis True Image 3rd Party Speed & Ransomware Tests, Apr 2017 from MRG Effitas

Acronis True Image 2017 provides several new features that set it apart from other backup software. An independent lab tested its performance, usability, ransomware protection, and features. The lab found that only Acronis True Image 2017 was able to protect backups from every ransomware family tested. It also won the majority of performance tests and provided the fastest cloud backup speeds. Additionally, Acronis True Image 2017 includes Active Protection technology that shields backup files from ransomware infections to prevent data loss.
Securing a great Developer Experience - v1.3

In the software engineering world, change is the only constant. And in the course of the last decades, the frequency of that change has exploded. What Agile has brought to software teams, DevOps is now bringing to the entire organization. And the results speak for themselves. The DevOps high-performers are killing it. Insane deploy frequencies of features, high reliability of applications, and high productivity of cross-functional teams have amplified the speed at which ideas become a reality.
In parallel, Application Security was doing its own thing and to a large part remained oblivious to all the impressive improvements that were happening in software engineering. Because breaking an application doesn’t need any knowledge of how it was created in the first place.
This talk will cover anti-patterns that are preventing application security from being adopted by development teams, such as:
* Issues Overload
* Acronym Overuse
* Sales team Wall
Install Linux CentOS 6 x86_64 - minimum installation

Installing Linux in 3 steps: download the CentOS 6.4 x86_64 ISO file, burn it to a CD or USB drive, then boot from the disc and select the "Minimum installation" option to quickly install the basic Linux system files and utilities.
Accelerating Incident Response in Organizations of Any Size

This document discusses accelerating incident response for organizations of any size. It describes how current security infrastructure, like antivirus and firewalls, are overwhelmed by constant alerts. It then outlines the typical incident response workflow of investigating incidents, recovering from attacks, improving defenses, and reducing future vulnerabilities. The presentation will demonstrate how Cisco's security products can integrate to provide automated hunting of recorded network activity over 30 days to accelerate incident response. These products include Email Security, Cisco ISE, ThreatGrid, Umbrella, AMP, and Cisco Talos.
Developing a Rugged Dev Ops Approach to Cloud Security (Updated)

DevSecOps is propelling forward-thinking organizations by doing something simple – fostering collaboration of seemingly contradictory teams to align their disparate goals into a singular effort.
Don’t WannaCry? Here’s How to Stop Those Ransomware Blues

This document discusses the WannaCry ransomware attack of May 2017. It provides an overview of how WannaCry worked, including that it infected over 300,000 Windows machines worldwide by encrypting their contents until a ransom was paid in bitcoin. It spread using vulnerabilities in Microsoft SMB and EternalBlue/DoublePulsar exploits. The document advocates for securing networks and applications to manage risks from these types of attacks and focuses on quality and security practices across the software development lifecycle.
Virus part1

DDoS programs are created by attackers to overwhelm web servers with traffic and deny legitimate users access to services. DDoS stands for Distributed Denial of Service. There are different types of viruses including DOS, Windows, script, macro, and boot viruses. Boot viruses infect the hard disk during system startup while DOS viruses attach to the end of files and modify headers to gain control during execution. Windows viruses commonly infect executable files and modify system files and processes. Macro viruses spread through document templates and startup folders in programs like Word and Excel. Script viruses can utilize scripting capabilities in browsers to spread via webpages and emails. Safe computing practices like disabling scripting hosts, hiding file extensions, updating security software, and
The Open Sourcing of Infrastructure

This document discusses the history and future of open sourcing infrastructure. It describes how Linux and open source software grew from being seen as "cheap Unix" to becoming ubiquitous. Factors like the LAMP stack, concerns around vendor lock-in, and a need for greater automation drove more organizations to use open source options. Now open source powers much of modern infrastructure through tools like Docker, Kubernetes, and DC/OS. Going forward, the document advocates open sourcing entire infrastructure stacks to avoid vendor lock-in and allow for community ownership and contributions from anywhere.
Recommended
Acronis True Image 3rd Party Speed & Ransomware Tests, Apr 2017 from MRG Effitas

Acronis True Image 2017 provides several new features that set it apart from other backup software. An independent lab tested its performance, usability, ransomware protection, and features. The lab found that only Acronis True Image 2017 was able to protect backups from every ransomware family tested. It also won the majority of performance tests and provided the fastest cloud backup speeds. Additionally, Acronis True Image 2017 includes Active Protection technology that shields backup files from ransomware infections to prevent data loss.
Securing a great Developer Experience - v1.3

In the software engineering world, change is the only constant. And in the course of the last decades, the frequency of that change has exploded. What Agile has brought to software teams, DevOps is now bringing to the entire organization. And the results speak for themselves. The DevOps high-performers are killing it. Insane deploy frequencies of features, high reliability of applications, and high productivity of cross-functional teams have amplified the speed at which ideas become a reality.
In parallel, Application Security was doing its own thing and to a large part remained oblivious to all the impressive improvements that were happening in software engineering. Because breaking an application doesn’t need any knowledge of how it was created in the first place.
This talk will cover anti-patterns that are preventing application security from being adopted by development teams, such as:
* Issues Overload
* Acronym Overuse
* Sales team Wall
Install Linux CentOS 6 x86_64 - minimum installation

Installing Linux in 3 steps: download the CentOS 6.4 x86_64 ISO file, burn it to a CD or USB drive, then boot from the disc and select the "Minimum installation" option to quickly install the basic Linux system files and utilities.
Accelerating Incident Response in Organizations of Any Size

This document discusses accelerating incident response for organizations of any size. It describes how current security infrastructure, like antivirus and firewalls, are overwhelmed by constant alerts. It then outlines the typical incident response workflow of investigating incidents, recovering from attacks, improving defenses, and reducing future vulnerabilities. The presentation will demonstrate how Cisco's security products can integrate to provide automated hunting of recorded network activity over 30 days to accelerate incident response. These products include Email Security, Cisco ISE, ThreatGrid, Umbrella, AMP, and Cisco Talos.
Developing a Rugged Dev Ops Approach to Cloud Security (Updated)

DevSecOps is propelling forward-thinking organizations by doing something simple – fostering collaboration of seemingly contradictory teams to align their disparate goals into a singular effort.
Don’t WannaCry? Here’s How to Stop Those Ransomware Blues

This document discusses the WannaCry ransomware attack of May 2017. It provides an overview of how WannaCry worked, including that it infected over 300,000 Windows machines worldwide by encrypting their contents until a ransom was paid in bitcoin. It spread using vulnerabilities in Microsoft SMB and EternalBlue/DoublePulsar exploits. The document advocates for securing networks and applications to manage risks from these types of attacks and focuses on quality and security practices across the software development lifecycle.
Virus part1

DDoS programs are created by attackers to overwhelm web servers with traffic and deny legitimate users access to services. DDoS stands for Distributed Denial of Service. There are different types of viruses including DOS, Windows, script, macro, and boot viruses. Boot viruses infect the hard disk during system startup while DOS viruses attach to the end of files and modify headers to gain control during execution. Windows viruses commonly infect executable files and modify system files and processes. Macro viruses spread through document templates and startup folders in programs like Word and Excel. Script viruses can utilize scripting capabilities in browsers to spread via webpages and emails. Safe computing practices like disabling scripting hosts, hiding file extensions, updating security software, and
The Open Sourcing of Infrastructure

This document discusses the history and future of open sourcing infrastructure. It describes how Linux and open source software grew from being seen as "cheap Unix" to becoming ubiquitous. Factors like the LAMP stack, concerns around vendor lock-in, and a need for greater automation drove more organizations to use open source options. Now open source powers much of modern infrastructure through tools like Docker, Kubernetes, and DC/OS. Going forward, the document advocates open sourcing entire infrastructure stacks to avoid vendor lock-in and allow for community ownership and contributions from anywhere.
Open security group launching a new language to link security tools - extent ...

According to OCA, the adoption of OpenDXL Ontology would construct a stronger, united front to safeguard and shield across all kinds of security tools, while reducing the load of stage integrations between separate products.The group asserts the new language will snip the demand for custom integrations between each of the products which utilize it.
Meanwhile, the OCA has also supported the creation of a new steering committee, that can combine leaders from associates IBM Security, McAfee, Tripwire, AT&T, and Packet Clearinghouse to fortify the technical advancement and management of the human body.
Install Linux CentOS 7.0

This document provides instructions for installing Linux CentOS 7.0 in 3 steps. It is authored by Sayyed Mehdi Poustchi Amin, a network administrator and founder of Iran's honeynet project. Amin has several IT certifications and provides his contact information.
VMware Server 2

VMware Installation & Configuration document discusses VMware Server 2 for both Windows and Linux versions. It provides information on VMware Server software and is presented by Sayyed Mehdi Poustchi Amin, a network administrator and founder of Iran's honeynet project who works at Azad University of Mashhad and SICSR.
Install Windows Server 2012 Step-by-Step

This document provides a step-by-step guide to installing Windows Server 2012. It was written by Mehdi Poustchi Amin, a network administrator and founder of Iran's honeynet project, and presented in India in October 2013. The guide outlines the installation process and is intended to assist administrators with deploying Windows Server 2012.
VMware Workstation 7

VMware Workstation 7.1 is virtualization software that allows users to run multiple operating systems on a single computer. It has a 30-day trial version available for download from VMware.com for $189. The document was presented by Mehdi Poustchi Amin, a network administrator and founder of Iran's honeynet project who was giving a presentation on VMware Workstation virtualization.
Install Windows Server 2008 Step-by-Step

This document provides a step-by-step guide to installing Windows Server 2008. It was written by Mehdi Poustchi Amin, a network administrator and founder of Iran's honeynet project, and presents the installation process.
VMware ESX 3.5

This document provides information on installing and configuring VMware ESX Server 3.5 and VMware Infrastructure Client 2.5. It was presented by Sayyed Mehdi Poustchi Amin, who has several IT certifications and works as a network administrator and research assistant. The presentation covers VMware's network virtualization technology using ESX Server and how to manage the virtual infrastructure with the Infrastructure Client software.
Install windows 8.1 Pro

To install Windows 8.1 Pro, download the installation files, run the setup.exe file to begin installation, and follow the on-screen instructions to accept license terms, select a custom or upgrade installation, and enter your product key. The installation will then format your hard drive, copy files, configure settings, and install updates so you have a functional Windows 8.1 Pro system.
Evident io Continuous Compliance - Mar 2017

Continuous Compliance is achievable, provided you leverage the cloud infrastructure APIs and applying Continuous Monitoring to your deployed resources. Here's how Evident.io is doing cloud security right.
Micro segmentation – a perfect fit for microservices

Microsegmentation, which groups network entities into segments and applies security policies to control traffic, is a perfect fit for securing microservices architectures. It allows for network-independent security policies to be defined and centrally managed at a fine-grained level, enabling policies to adapt to the dynamic and elastic nature of microservices. Major networking and security platforms like VMware NSX, Cisco ACI, and Docker's libnetwork support microsegmentation capabilities that are well-suited for microservices security through isolation, segmentation, and distributed policy enforcement.
Presentation on the topic of Windows and its difference.

Microsoft Windows was developed by Microsoft and introduced in 1985. It has since overtaken other operating systems with a 90% market share. The presentation discusses the history and versions of Windows, from Windows 1.0 to the current Windows 10. It also covers specifications of Windows, comparing it to Linux and Mac in terms of installation, support, security, performance, and user interface. In conclusion, the presentation provides different perspectives on Windows according to the audience.
How Search is Accelerating the Growth of Video in the Enterprise

Video has had a significant impact in the consumer world. A similar trend is underway in the enterprise. In enterprises video is increasingly used for business meetings, user to user messaging, training, customer care, corporate events, corporate communications, safety and security. In many cases video must also be recorded. This explosion of video creates two challenges: finding and consuming them.
This talk examines why video is becoming more prevalent in the enterprise and promising new technology to find and consume them. It also addresses the role of speech and search technology, as well as the role of network infrastructure.
Windows 8 Preso

Windows 8 provides a unified interface across all devices with a focus on touch, apps, and the cloud. It includes a reimagined browser and is designed for business use, while Windows XP reaches end of support presenting security and compatibility risks. A demo is then shown highlighting these features.
Sonatype storybook go fast_be secure

The document tells a story about the long-standing conflict between development teams wanting to move fast and security teams wanting to ensure safety. It describes how the rise of component-based development made it even harder to secure applications. The story says that after much reflection, the two sides realized they could achieve both speed and security by building intelligence and governance into components from the start using the tools developers already use. This new approach came to be called the CLM (Component Lifecycle Management) model and allowed developers to move fast while keeping applications secure.
Brian P Milstead resume

Brian Milstead is an experienced security analyst and network technician seeking a new position that utilizes his skills. He has over 10 years of experience in information technology, including positions at Staples Promotional Products where he performed security audits, patched systems, administered encryption and antivirus software, and monitored security and firewall systems. He is proficient with Windows, Mac OS, and security certifications.
1e operating sysytem4 bicar

Windows Vista is Microsoft's successor to Windows XP and offers improved performance, reliability, security and organization capabilities compared to previous versions. It is available in five editions for different users, from basic home users to enterprise businesses. Other major operating systems include Mac OS X, UNIX, Linux, and network operating systems like Windows Server, UNIX, Linux, Solaris and NetWare which are designed to support larger networks and provide file/resource sharing and security features.
Object Storage Updates - Juno Edition 

John Dickinson, Object Storage PTL, outlines the changes made in the Icehouse release as well as upcoming updates for Juno.
Learn more about Object Storage (Swift) here: https://wiki.openstack.org/wiki/Swift
Cisco Security Training | Qos Networking | Implementing Cisco Network Security

QoS Networking provides approved Cisco Security Training include ccna security, ccnp security, implementing cisco network security, ccna Certification.
The Cyber Protection Revolution

Today’s reliance on data is creating a variety of new challenges for businesses and individuals alike. We use data in more places on more devices, creating more opportunities for data loss. At the same time, cybercriminals are using huge amounts of computing power and cutting-edge AI to make their attacks more effective and damaging – and they are producing new strains of ransomware faster than traditional anti-virus can keep up.
We’ll look at the emerging IT trends that are making traditional approaches obsolete, and how the new discipline of cyber protection is more effective in safeguarding critical data, applications and systems.
Massachusetts u.s. attorney’s office framework for countering violent extremism

The document presents a framework for countering violent extremism developed by a collaborative in the Greater Boston region. It identifies seven problem areas, including young people feeling isolated and alienated, making them vulnerable to recruitment. For this problem, the framework suggests goals like reducing isolation and improving access to services. Sample solutions include skills development programs through schools and community organizations, as well as awareness/education initiatives like training for parents and organizations on supporting youth. The framework is intended to increase capacity to protect individuals from extremism through prevention and intervention approaches.
aaaaaaaaaaa

This document discusses 4 main points: a) aaaaaaaaaaa, b) bbbbbbbbbbbb, c) ccccccc, and d) dddddddddd.
Ejercicios de fisica

El documento presenta ecuaciones y cálculos relacionados con la cinemática de objetos en movimiento horizontal y en caída libre. Incluye ecuaciones para velocidad inicial, velocidad final, aceleración, distancia recorrida, tiempo de vuelo y ángulo de lanzamiento para proyectiles y objetos en caída libre considerando la gravedad.
More Related Content
What's hot
Open security group launching a new language to link security tools - extent ...

According to OCA, the adoption of OpenDXL Ontology would construct a stronger, united front to safeguard and shield across all kinds of security tools, while reducing the load of stage integrations between separate products.The group asserts the new language will snip the demand for custom integrations between each of the products which utilize it.
Meanwhile, the OCA has also supported the creation of a new steering committee, that can combine leaders from associates IBM Security, McAfee, Tripwire, AT&T, and Packet Clearinghouse to fortify the technical advancement and management of the human body.
Install Linux CentOS 7.0

This document provides instructions for installing Linux CentOS 7.0 in 3 steps. It is authored by Sayyed Mehdi Poustchi Amin, a network administrator and founder of Iran's honeynet project. Amin has several IT certifications and provides his contact information.
VMware Server 2

VMware Installation & Configuration document discusses VMware Server 2 for both Windows and Linux versions. It provides information on VMware Server software and is presented by Sayyed Mehdi Poustchi Amin, a network administrator and founder of Iran's honeynet project who works at Azad University of Mashhad and SICSR.
Install Windows Server 2012 Step-by-Step

This document provides a step-by-step guide to installing Windows Server 2012. It was written by Mehdi Poustchi Amin, a network administrator and founder of Iran's honeynet project, and presented in India in October 2013. The guide outlines the installation process and is intended to assist administrators with deploying Windows Server 2012.
VMware Workstation 7

VMware Workstation 7.1 is virtualization software that allows users to run multiple operating systems on a single computer. It has a 30-day trial version available for download from VMware.com for $189. The document was presented by Mehdi Poustchi Amin, a network administrator and founder of Iran's honeynet project who was giving a presentation on VMware Workstation virtualization.
Install Windows Server 2008 Step-by-Step

This document provides a step-by-step guide to installing Windows Server 2008. It was written by Mehdi Poustchi Amin, a network administrator and founder of Iran's honeynet project, and presents the installation process.
VMware ESX 3.5

This document provides information on installing and configuring VMware ESX Server 3.5 and VMware Infrastructure Client 2.5. It was presented by Sayyed Mehdi Poustchi Amin, who has several IT certifications and works as a network administrator and research assistant. The presentation covers VMware's network virtualization technology using ESX Server and how to manage the virtual infrastructure with the Infrastructure Client software.
Install windows 8.1 Pro

To install Windows 8.1 Pro, download the installation files, run the setup.exe file to begin installation, and follow the on-screen instructions to accept license terms, select a custom or upgrade installation, and enter your product key. The installation will then format your hard drive, copy files, configure settings, and install updates so you have a functional Windows 8.1 Pro system.
Evident io Continuous Compliance - Mar 2017

Continuous Compliance is achievable, provided you leverage the cloud infrastructure APIs and applying Continuous Monitoring to your deployed resources. Here's how Evident.io is doing cloud security right.
Micro segmentation – a perfect fit for microservices

Microsegmentation, which groups network entities into segments and applies security policies to control traffic, is a perfect fit for securing microservices architectures. It allows for network-independent security policies to be defined and centrally managed at a fine-grained level, enabling policies to adapt to the dynamic and elastic nature of microservices. Major networking and security platforms like VMware NSX, Cisco ACI, and Docker's libnetwork support microsegmentation capabilities that are well-suited for microservices security through isolation, segmentation, and distributed policy enforcement.
Presentation on the topic of Windows and its difference.

Microsoft Windows was developed by Microsoft and introduced in 1985. It has since overtaken other operating systems with a 90% market share. The presentation discusses the history and versions of Windows, from Windows 1.0 to the current Windows 10. It also covers specifications of Windows, comparing it to Linux and Mac in terms of installation, support, security, performance, and user interface. In conclusion, the presentation provides different perspectives on Windows according to the audience.
How Search is Accelerating the Growth of Video in the Enterprise

Video has had a significant impact in the consumer world. A similar trend is underway in the enterprise. In enterprises video is increasingly used for business meetings, user to user messaging, training, customer care, corporate events, corporate communications, safety and security. In many cases video must also be recorded. This explosion of video creates two challenges: finding and consuming them.
This talk examines why video is becoming more prevalent in the enterprise and promising new technology to find and consume them. It also addresses the role of speech and search technology, as well as the role of network infrastructure.
Windows 8 Preso

Windows 8 provides a unified interface across all devices with a focus on touch, apps, and the cloud. It includes a reimagined browser and is designed for business use, while Windows XP reaches end of support presenting security and compatibility risks. A demo is then shown highlighting these features.
Sonatype storybook go fast_be secure

The document tells a story about the long-standing conflict between development teams wanting to move fast and security teams wanting to ensure safety. It describes how the rise of component-based development made it even harder to secure applications. The story says that after much reflection, the two sides realized they could achieve both speed and security by building intelligence and governance into components from the start using the tools developers already use. This new approach came to be called the CLM (Component Lifecycle Management) model and allowed developers to move fast while keeping applications secure.
Brian P Milstead resume

Brian Milstead is an experienced security analyst and network technician seeking a new position that utilizes his skills. He has over 10 years of experience in information technology, including positions at Staples Promotional Products where he performed security audits, patched systems, administered encryption and antivirus software, and monitored security and firewall systems. He is proficient with Windows, Mac OS, and security certifications.
1e operating sysytem4 bicar

Windows Vista is Microsoft's successor to Windows XP and offers improved performance, reliability, security and organization capabilities compared to previous versions. It is available in five editions for different users, from basic home users to enterprise businesses. Other major operating systems include Mac OS X, UNIX, Linux, and network operating systems like Windows Server, UNIX, Linux, Solaris and NetWare which are designed to support larger networks and provide file/resource sharing and security features.
Object Storage Updates - Juno Edition 

John Dickinson, Object Storage PTL, outlines the changes made in the Icehouse release as well as upcoming updates for Juno.
Learn more about Object Storage (Swift) here: https://wiki.openstack.org/wiki/Swift
Cisco Security Training | Qos Networking | Implementing Cisco Network Security

QoS Networking provides approved Cisco Security Training include ccna security, ccnp security, implementing cisco network security, ccna Certification.
The Cyber Protection Revolution

Today’s reliance on data is creating a variety of new challenges for businesses and individuals alike. We use data in more places on more devices, creating more opportunities for data loss. At the same time, cybercriminals are using huge amounts of computing power and cutting-edge AI to make their attacks more effective and damaging – and they are producing new strains of ransomware faster than traditional anti-virus can keep up.
We’ll look at the emerging IT trends that are making traditional approaches obsolete, and how the new discipline of cyber protection is more effective in safeguarding critical data, applications and systems.
What's hot (19)
Open security group launching a new language to link security tools - extent ...

Open security group launching a new language to link security tools - extent ...
Micro segmentation – a perfect fit for microservices

Micro segmentation – a perfect fit for microservices
Presentation on the topic of Windows and its difference.

Presentation on the topic of Windows and its difference.
How Search is Accelerating the Growth of Video in the Enterprise

How Search is Accelerating the Growth of Video in the Enterprise
Cisco Security Training | Qos Networking | Implementing Cisco Network Security

Cisco Security Training | Qos Networking | Implementing Cisco Network Security
Viewers also liked
Massachusetts u.s. attorney’s office framework for countering violent extremism

The document presents a framework for countering violent extremism developed by a collaborative in the Greater Boston region. It identifies seven problem areas, including young people feeling isolated and alienated, making them vulnerable to recruitment. For this problem, the framework suggests goals like reducing isolation and improving access to services. Sample solutions include skills development programs through schools and community organizations, as well as awareness/education initiatives like training for parents and organizations on supporting youth. The framework is intended to increase capacity to protect individuals from extremism through prevention and intervention approaches.
aaaaaaaaaaa

This document discusses 4 main points: a) aaaaaaaaaaa, b) bbbbbbbbbbbb, c) ccccccc, and d) dddddddddd.
Ejercicios de fisica

El documento presenta ecuaciones y cálculos relacionados con la cinemática de objetos en movimiento horizontal y en caída libre. Incluye ecuaciones para velocidad inicial, velocidad final, aceleración, distancia recorrida, tiempo de vuelo y ángulo de lanzamiento para proyectiles y objetos en caída libre considerando la gravedad.
The Root Of All Fears

1) Israel fears that an Iranian nuclear weapon could undermine Israel's military superiority and ability to defeat its enemies decisively in war.
2) It could also encourage proliferation of nuclear weapons in the Middle East by countries like Egypt and Saudi Arabia.
3) This nuclearization would threaten Israel's security by reducing incentives for Arab states to make peace, since they would no longer fear catastrophic defeat by Israel.
K%26s

K&S provides general cleaning services such as window washing, power washing, and general home maintenance. They are fully insured and can be contacted by phone, fax, cell, or through their website for support. K&S offers cleaning and maintenance services for both residential and commercial customers.
Puertos

Este documento describe diferentes tipos de puertos en una computadora. Explica que los puertos son conectores que permiten conectar dispositivos periféricos o de almacenamiento a la computadora para compartir información. Luego describe específicamente los puertos PCI, VGA, USB, paralelo, PS/2, de audio, serie y de red, explicando sus funciones y los tipos de dispositivos que se pueden conectar a cada uno.
New Training Program for Bullying Prevention in Youth Sports

The National Alliance for Youth Sports (NAYS) recently created the first bullying awareness and prevention training program specifically for youth sports participants. The free training helps coaches and parents prevent, identify, and respond to bullying. Over 2,000 youth coaches and parents have already completed the training. NAYS emphasizes the importance of bullying prevention in youth sports by citing data that children's experiences with bullying increase when participating in recreational sports, and hopes the training will help ensure a safe and fun environment for youth sports participants.
Uso de la alternativa mientras

El documento describe un programa que utiliza una estructura de control "mientras" para imprimir los números del 1 al 100. El programa inicializa un contador en 1 y, mientras el contador sea menor que 100, imprime el valor del contador y luego lo incrementa en 1. Esto se repite hasta que el contador alcance el valor de 100.
Ερμηνείες για το εκλογικό αποτέλεσμα της 17ης Ιουνίου

Ερμηνείες
για το εκλογικό
αποτέλεσμα
της 17ης Ιουνίου
Mike Mokhtar

This document discusses why finance is needed for businesses and how to obtain financing. It notes that finance is needed to start new businesses, expand existing businesses, or purchase other businesses or assets. Some options for financing mentioned include bank loans, government grants, private loans, and funding from family and friends. However, the document states that for most options besides family/friends, a business plan is required. The business plan demonstrates an understanding of the business, its vision, and how it will adapt to economic changes. The document provides examples of industries that have successfully obtained financing. It also discusses considerations for buying, selling, and succession planning for a business, as well as establishing power of attorney and wills.
Cliclo celular

El ciclo celular consta de la interfase y la fase M. La interfase incluye las fases G1, S y G2 donde la célula crece y replica su ADN. La fase M es cuando la célula se divide a través de la mitosis o meiosis. La mitosis produce dos células hijas idénticas mientras que la meiosis da como resultado cuatro células hijas con la mitad de la información genética de la célula original. El ciclo celular permite el crecimiento y replicación controlada de las células a través de
Chalaneru(2)

El documento habla nostálgicamente de la inocencia perdida de la Arcadia del autor. Expresa que aunque era un valle escondido y lejano, fue descubierto por hombres sedientos de riqueza que destruyeron su belleza natural. Finalmente, invita al viajero a dejar una rama de madreselva sobre la tumba del poeta Armando Palacio si alguna vez visita las montañas de Asturias.
7 carf us

CARF manages growing demand for accreditation with Pivotal CRM solution. CARF needed a more efficient system to manage large volumes of accreditation data as demand grew. Their previous paper-based system was time-intensive. With Pivotal CRM, CARF can streamline the accreditation application process online and improve surveyor productivity and customer satisfaction. Over 3,700 providers across North America and Europe have earned CARF accreditation. Pivotal CRM provides a unified system for effective communication between staff, customers, and surveyors to manage the accreditation process.
[Northern Ireland] Winter, K., Connolly, P., Bell, I., & Ferguson, J. (2012)....![[Northern Ireland] Winter, K., Connolly, P., Bell, I., & Ferguson, J. (2012)....](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Northern Ireland] Winter, K., Connolly, P., Bell, I., & Ferguson, J. (2012)....](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Northern Ireland] Winter, K., Connolly, P., Bell, I., & Ferguson, J. (2012)....Linkedin Education of Children in Care Network
The document summarizes a presentation on evaluating the effectiveness of the Letterbox Club in improving educational outcomes for children aged 7-11 in foster care in Northern Ireland. It found that children who received Letterbox Club packs showed improvements in reading accuracy, reading comprehension, and number skills based on pre and post testing. However, a controlled trial is still needed to conclusively determine how much of the improvement is directly due to the Letterbox Club intervention. Recommendations include expanding the number games in packs, conducting a rigorous controlled trial, and considering additional outcomes like enjoyment and confidence.Viewers also liked (17)
Massachusetts u.s. attorney’s office framework for countering violent extremism

Massachusetts u.s. attorney’s office framework for countering violent extremism
New Training Program for Bullying Prevention in Youth Sports

New Training Program for Bullying Prevention in Youth Sports
Ερμηνείες για το εκλογικό αποτέλεσμα της 17ης Ιουνίου

Ερμηνείες για το εκλογικό αποτέλεσμα της 17ης Ιουνίου
[Northern Ireland] Winter, K., Connolly, P., Bell, I., & Ferguson, J. (2012)....![[Northern Ireland] Winter, K., Connolly, P., Bell, I., & Ferguson, J. (2012)....](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Northern Ireland] Winter, K., Connolly, P., Bell, I., & Ferguson, J. (2012)....](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Northern Ireland] Winter, K., Connolly, P., Bell, I., & Ferguson, J. (2012)....
Recently uploaded
Skybuffer SAM4U tool for SAP license adoption

Manage and optimize your license adoption and consumption with SAM4U, an SAP free customer software asset management tool.
SAM4U, an SAP complimentary software asset management tool for customers, delivers a detailed and well-structured overview of license inventory and usage with a user-friendly interface. We offer a hosted, cost-effective, and performance-optimized SAM4U setup in the Skybuffer Cloud environment. You retain ownership of the system and data, while we manage the ABAP 7.58 infrastructure, ensuring fixed Total Cost of Ownership (TCO) and exceptional services through the SAP Fiori interface.
GraphRAG for Life Science to increase LLM accuracy

GraphRAG for life science domain, where you retriever information from biomedical knowledge graphs using LLMs to increase the accuracy and performance of generated answers
AWS Cloud Cost Optimization Presentation.pptx

This presentation provides valuable insights into effective cost-saving techniques on AWS. Learn how to optimize your AWS resources by rightsizing, increasing elasticity, picking the right storage class, and choosing the best pricing model. Additionally, discover essential governance mechanisms to ensure continuous cost efficiency. Whether you are new to AWS or an experienced user, this presentation provides clear and practical tips to help you reduce your cloud costs and get the most out of your budget.
Operating System Used by Users in day-to-day life.pptx

Dive into the realm of operating systems (OS) with Pravash Chandra Das, a seasoned Digital Forensic Analyst, as your guide. 🚀 This comprehensive presentation illuminates the core concepts, types, and evolution of OS, essential for understanding modern computing landscapes.
Beginning with the foundational definition, Das clarifies the pivotal role of OS as system software orchestrating hardware resources, software applications, and user interactions. Through succinct descriptions, he delineates the diverse types of OS, from single-user, single-task environments like early MS-DOS iterations, to multi-user, multi-tasking systems exemplified by modern Linux distributions.
Crucial components like the kernel and shell are dissected, highlighting their indispensable functions in resource management and user interface interaction. Das elucidates how the kernel acts as the central nervous system, orchestrating process scheduling, memory allocation, and device management. Meanwhile, the shell serves as the gateway for user commands, bridging the gap between human input and machine execution. 💻
The narrative then shifts to a captivating exploration of prominent desktop OSs, Windows, macOS, and Linux. Windows, with its globally ubiquitous presence and user-friendly interface, emerges as a cornerstone in personal computing history. macOS, lauded for its sleek design and seamless integration with Apple's ecosystem, stands as a beacon of stability and creativity. Linux, an open-source marvel, offers unparalleled flexibility and security, revolutionizing the computing landscape. 🖥️
Moving to the realm of mobile devices, Das unravels the dominance of Android and iOS. Android's open-source ethos fosters a vibrant ecosystem of customization and innovation, while iOS boasts a seamless user experience and robust security infrastructure. Meanwhile, discontinued platforms like Symbian and Palm OS evoke nostalgia for their pioneering roles in the smartphone revolution.
The journey concludes with a reflection on the ever-evolving landscape of OS, underscored by the emergence of real-time operating systems (RTOS) and the persistent quest for innovation and efficiency. As technology continues to shape our world, understanding the foundations and evolution of operating systems remains paramount. Join Pravash Chandra Das on this illuminating journey through the heart of computing. 🌟
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
Main news related to the CCS TSI 2023 (2023/1695)

An English 🇬🇧 translation of a presentation to the speech I gave about the main changes brought by CCS TSI 2023 at the biggest Czech conference on Communications and signalling systems on Railways, which was held in Clarion Hotel Olomouc from 7th to 9th November 2023 (konferenceszt.cz). Attended by around 500 participants and 200 on-line followers.
The original Czech 🇨🇿 version of the presentation can be found here: https://www.slideshare.net/slideshow/hlavni-novinky-souvisejici-s-ccs-tsi-2023-2023-1695/269688092 .
The videorecording (in Czech) from the presentation is available here: https://youtu.be/WzjJWm4IyPk?si=SImb06tuXGb30BEH .
Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...

Skybuffer AI, built on the robust SAP Business Technology Platform (SAP BTP), is the latest and most advanced version of our AI development, reaffirming our commitment to delivering top-tier AI solutions. Skybuffer AI harnesses all the innovative capabilities of the SAP BTP in the AI domain, from Conversational AI to cutting-edge Generative AI and Retrieval-Augmented Generation (RAG). It also helps SAP customers safeguard their investments into SAP Conversational AI and ensure a seamless, one-click transition to SAP Business AI.
With Skybuffer AI, various AI models can be integrated into a single communication channel such as Microsoft Teams. This integration empowers business users with insights drawn from SAP backend systems, enterprise documents, and the expansive knowledge of Generative AI. And the best part of it is that it is all managed through our intuitive no-code Action Server interface, requiring no extensive coding knowledge and making the advanced AI accessible to more users.
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
A Comprehensive Guide to DeFi Development Services in 2024

DeFi represents a paradigm shift in the financial industry. Instead of relying on traditional, centralized institutions like banks, DeFi leverages blockchain technology to create a decentralized network of financial services. This means that financial transactions can occur directly between parties, without intermediaries, using smart contracts on platforms like Ethereum.
In 2024, we are witnessing an explosion of new DeFi projects and protocols, each pushing the boundaries of what’s possible in finance.
In summary, DeFi in 2024 is not just a trend; it’s a revolution that democratizes finance, enhances security and transparency, and fosters continuous innovation. As we proceed through this presentation, we'll explore the various components and services of DeFi in detail, shedding light on how they are transforming the financial landscape.
At Intelisync, we specialize in providing comprehensive DeFi development services tailored to meet the unique needs of our clients. From smart contract development to dApp creation and security audits, we ensure that your DeFi project is built with innovation, security, and scalability in mind. Trust Intelisync to guide you through the intricate landscape of decentralized finance and unlock the full potential of blockchain technology.
Ready to take your DeFi project to the next level? Partner with Intelisync for expert DeFi development services today!
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Are you ready to revolutionize how you handle data? Join us for a webinar where we’ll bring you up to speed with the latest advancements in Generative AI technology and discover how leveraging FME with tools from giants like Google Gemini, Amazon, and Microsoft OpenAI can supercharge your workflow efficiency.
During the hour, we’ll take you through:
Guest Speaker Segment with Hannah Barrington: Dive into the world of dynamic real estate marketing with Hannah, the Marketing Manager at Workspace Group. Hear firsthand how their team generates engaging descriptions for thousands of office units by integrating diverse data sources—from PDF floorplans to web pages—using FME transformers, like OpenAIVisionConnector and AnthropicVisionConnector. This use case will show you how GenAI can streamline content creation for marketing across the board.
Ollama Use Case: Learn how Scenario Specialist Dmitri Bagh has utilized Ollama within FME to input data, create custom models, and enhance security protocols. This segment will include demos to illustrate the full capabilities of FME in AI-driven processes.
Custom AI Models: Discover how to leverage FME to build personalized AI models using your data. Whether it’s populating a model with local data for added security or integrating public AI tools, find out how FME facilitates a versatile and secure approach to AI.
We’ll wrap up with a live Q&A session where you can engage with our experts on your specific use cases, and learn more about optimizing your data workflows with AI.
This webinar is ideal for professionals seeking to harness the power of AI within their data management systems while ensuring high levels of customization and security. Whether you're a novice or an expert, gain actionable insights and strategies to elevate your data processes. Join us to see how FME and AI can revolutionize how you work with data!
dbms calicut university B. sc Cs 4th sem.pdf

Its a seminar ppt on database management system using sql
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Presentation of the OECD Artificial Intelligence Review of Germany

Consult the full report at https://www.oecd.org/digital/oecd-artificial-intelligence-review-of-germany-609808d6-en.htm
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-und-domino-lizenzkostenreduzierung-in-der-welt-von-dlau/
DLAU und die Lizenzen nach dem CCB- und CCX-Modell sind für viele in der HCL-Community seit letztem Jahr ein heißes Thema. Als Notes- oder Domino-Kunde haben Sie vielleicht mit unerwartet hohen Benutzerzahlen und Lizenzgebühren zu kämpfen. Sie fragen sich vielleicht, wie diese neue Art der Lizenzierung funktioniert und welchen Nutzen sie Ihnen bringt. Vor allem wollen Sie sicherlich Ihr Budget einhalten und Kosten sparen, wo immer möglich. Das verstehen wir und wir möchten Ihnen dabei helfen!
Wir erklären Ihnen, wie Sie häufige Konfigurationsprobleme lösen können, die dazu führen können, dass mehr Benutzer gezählt werden als nötig, und wie Sie überflüssige oder ungenutzte Konten identifizieren und entfernen können, um Geld zu sparen. Es gibt auch einige Ansätze, die zu unnötigen Ausgaben führen können, z. B. wenn ein Personendokument anstelle eines Mail-Ins für geteilte Mailboxen verwendet wird. Wir zeigen Ihnen solche Fälle und deren Lösungen. Und natürlich erklären wir Ihnen das neue Lizenzmodell.
Nehmen Sie an diesem Webinar teil, bei dem HCL-Ambassador Marc Thomas und Gastredner Franz Walder Ihnen diese neue Welt näherbringen. Es vermittelt Ihnen die Tools und das Know-how, um den Überblick zu bewahren. Sie werden in der Lage sein, Ihre Kosten durch eine optimierte Domino-Konfiguration zu reduzieren und auch in Zukunft gering zu halten.
Diese Themen werden behandelt
- Reduzierung der Lizenzkosten durch Auffinden und Beheben von Fehlkonfigurationen und überflüssigen Konten
- Wie funktionieren CCB- und CCX-Lizenzen wirklich?
- Verstehen des DLAU-Tools und wie man es am besten nutzt
- Tipps für häufige Problembereiche, wie z. B. Team-Postfächer, Funktions-/Testbenutzer usw.
- Praxisbeispiele und Best Practices zum sofortigen Umsetzen
leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...

Predictive maintenance is a proactive approach that anticipates equipment failures before they happen. At the forefront of this innovative strategy is Artificial Intelligence (AI), which brings unprecedented precision and efficiency. AI in predictive maintenance is transforming industries by reducing downtime, minimizing costs, and enhancing productivity.
Recently uploaded (20)
GraphRAG for Life Science to increase LLM accuracy

GraphRAG for Life Science to increase LLM accuracy
WeTestAthens: Postman's AI & Automation Techniques

WeTestAthens: Postman's AI & Automation Techniques
Operating System Used by Users in day-to-day life.pptx

Operating System Used by Users in day-to-day life.pptx
Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...

Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...

Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...
A Comprehensive Guide to DeFi Development Services in 2024

A Comprehensive Guide to DeFi Development Services in 2024
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Driving Business Innovation: Latest Generative AI Advancements & Success Story
Presentation of the OECD Artificial Intelligence Review of Germany

Presentation of the OECD Artificial Intelligence Review of Germany
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU
leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...

leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...
week6
- 2. Sentences “We designed Windows 7 to simplify your everyday tasks, work the way you want, and make new things possible.” Microsoft provides many upgrades for Windows security. Technologies are described their details in MSDN Library for developers.
- 3. 5 Keywords and definitions Microsoft A computer software corporation established by Bill Gates and Paul Allen. It is global company. Windows A very famous operating system for personal computers developed by Microsoft. .NET Framework A environment for application develop and running developed by Microsoft Security “the department of a large company or organization that deals with the protection of its buildings, equipment and staff” - Oxford Internet Explorer A famous web browser developed by Microsoft and used all over the world.