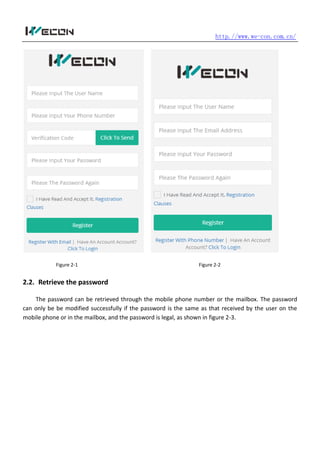
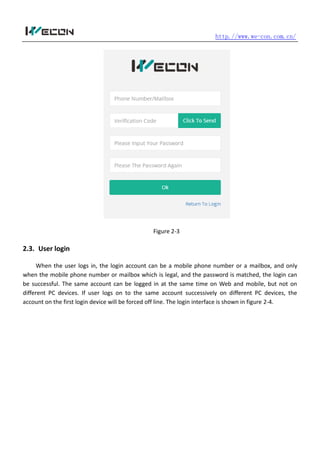
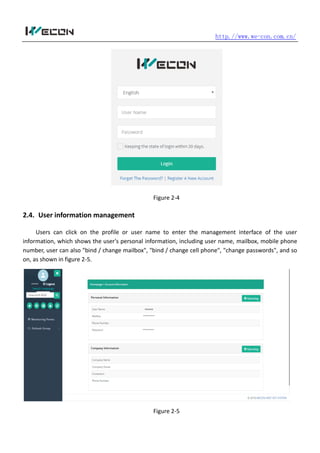
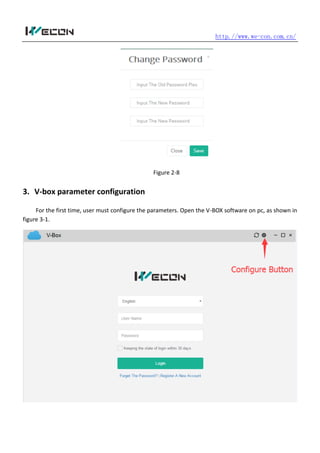
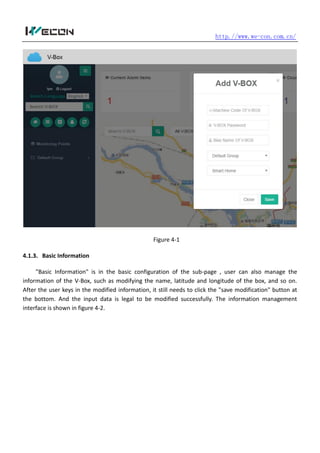
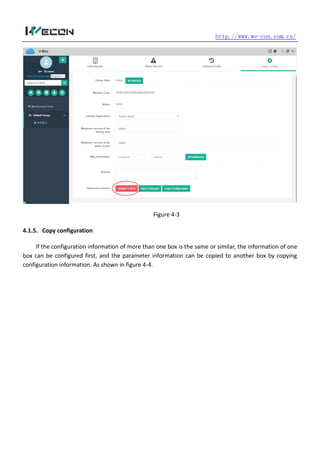
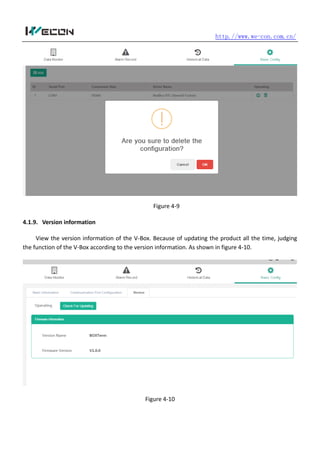
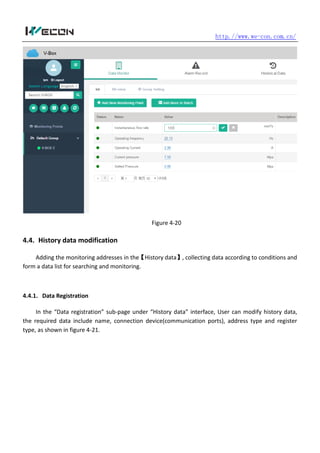
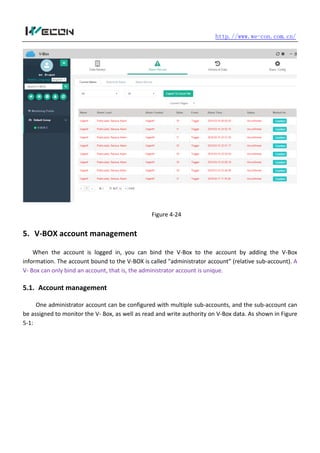
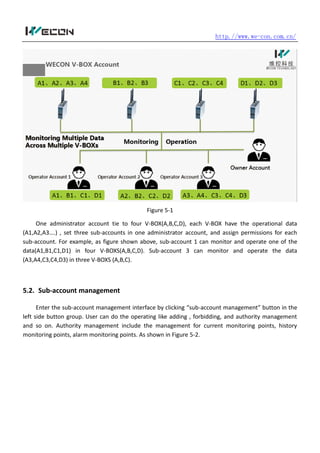
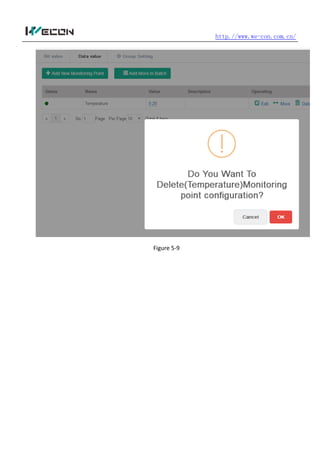
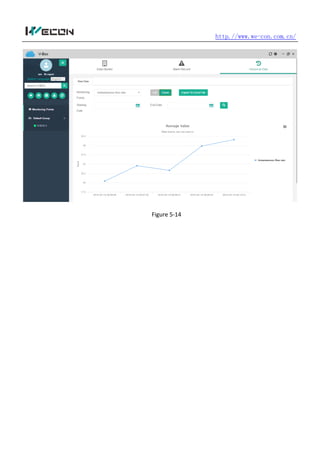
The document provides instructions for using the V-BOX Web application. It describes the basic functions and configuration of the application. The basic functions include user registration, password retrieval, and login. It also explains how to configure V-BOX parameters such as access password, connection settings, and update time. Additionally, it outlines how to add and manage V-BOX devices, communication ports, monitoring points, user accounts and alarm settings within the V-BOX Web interface.