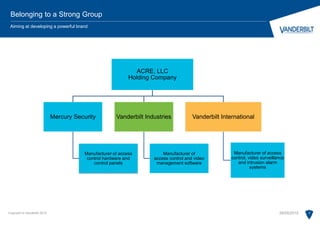
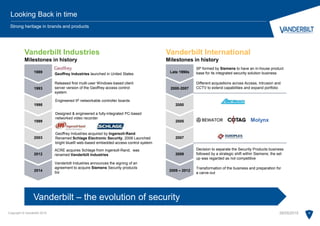
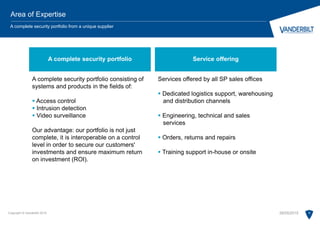
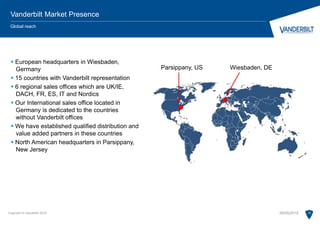
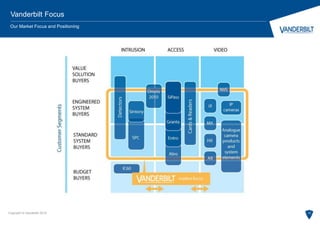
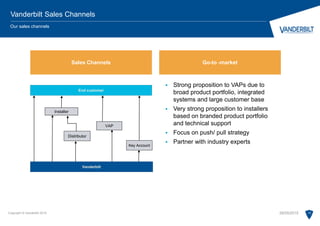
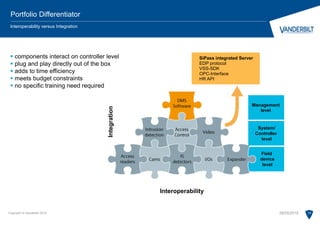
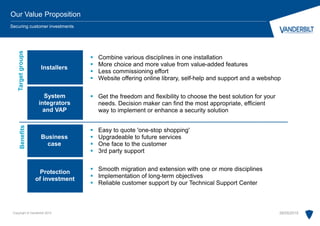
Vanderbilt is an independent security business with over 30 years of global presence, specializing in innovative security systems across various industries such as energy, healthcare, and finance. It focuses on access control, video management, and intrusion alarm systems, operating 16 locations worldwide, with its North American office in New Jersey. Vanderbilt aims to be the largest independent security products provider and prioritizes customer relationships through a multi-channel market approach, emphasizing agility, flexibility, and comprehensive technical support.